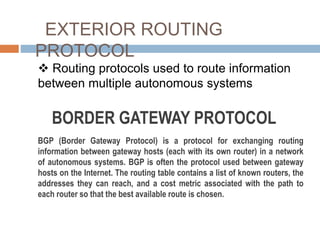
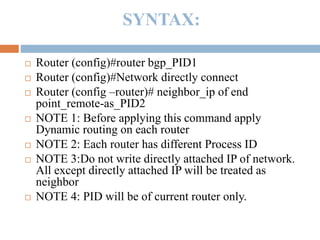
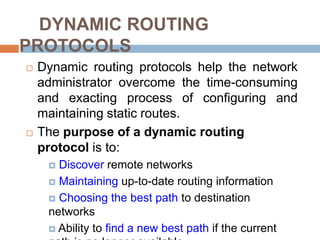
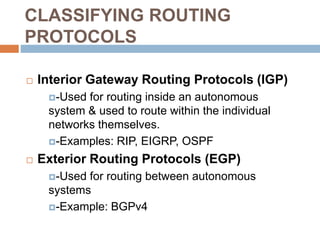
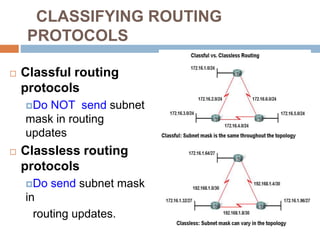
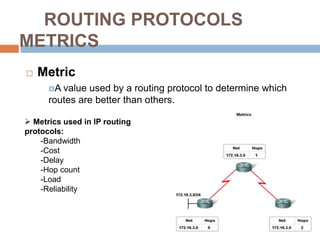
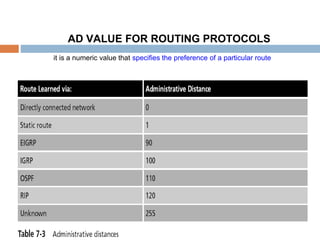
Dynamic routing protocols are used to automatically discover remote networks, maintain up-to-date routing information, and choose the best path to destination networks. There are two main types - interior gateway protocols (IGPs) like RIP, OSPF, and EIGRP that are used within an autonomous system, and exterior protocols like BGP that route between autonomous systems. IGPs use metrics like hop count or bandwidth to determine the best path. OSPF is a link-state protocol that floods link information, while EIGRP uses DUAL algorithm and maintains topology tables for fast convergence.

![Functional Requirements(contd.)
Routing Hierarchy
support large routing domains
Separate internal and external routes
Support of flexible subnetting schemes
route to arbitrary [address,mask]
combinations using VLSMs
Security
Type of Service Routing](https://image.slidesharecdn.com/pptonroutingprotocols622rg1312038622rg1312039-160514050323/85/Dynamic-routing-protocols-CCNA-20-320.jpg)