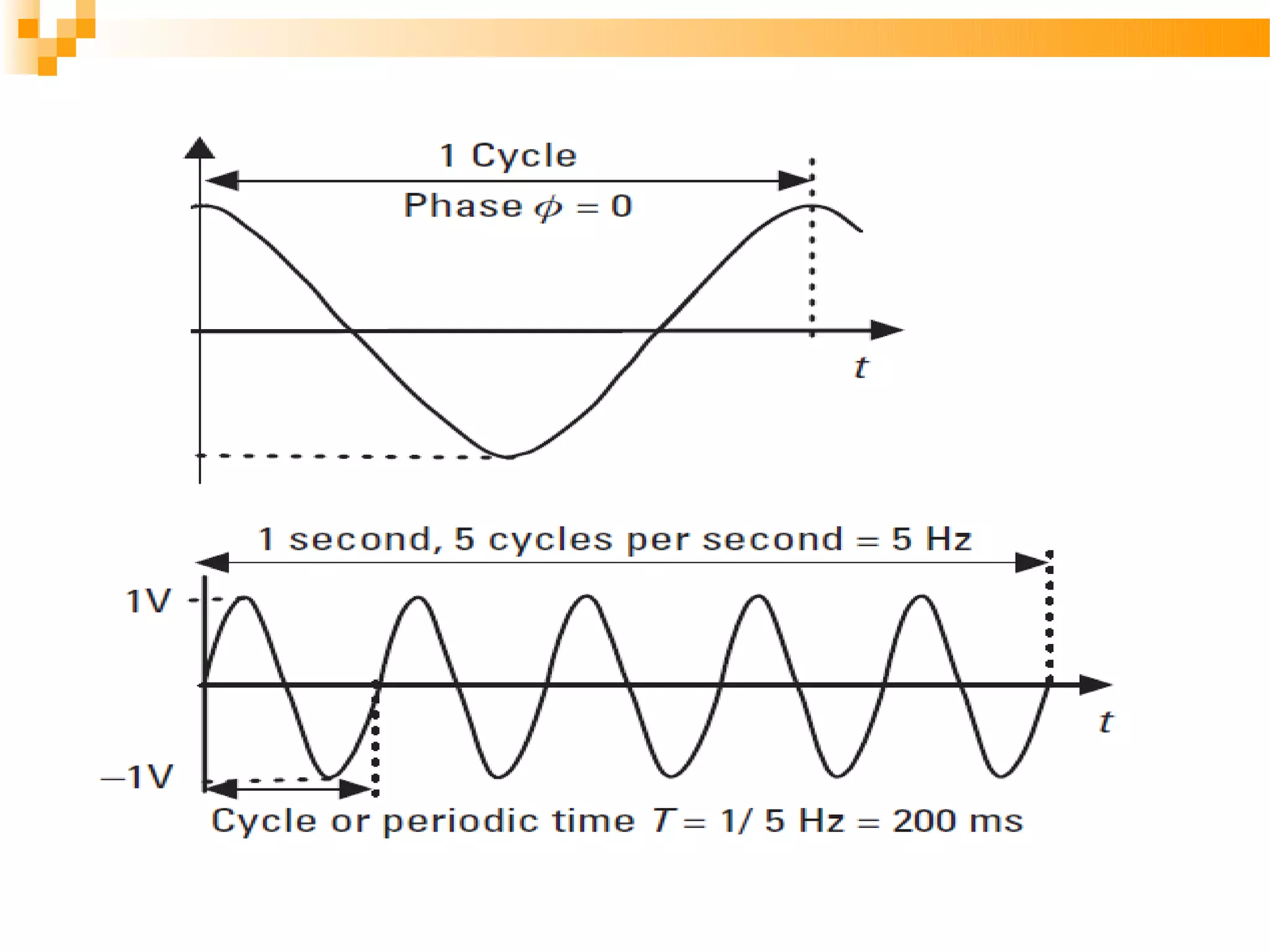
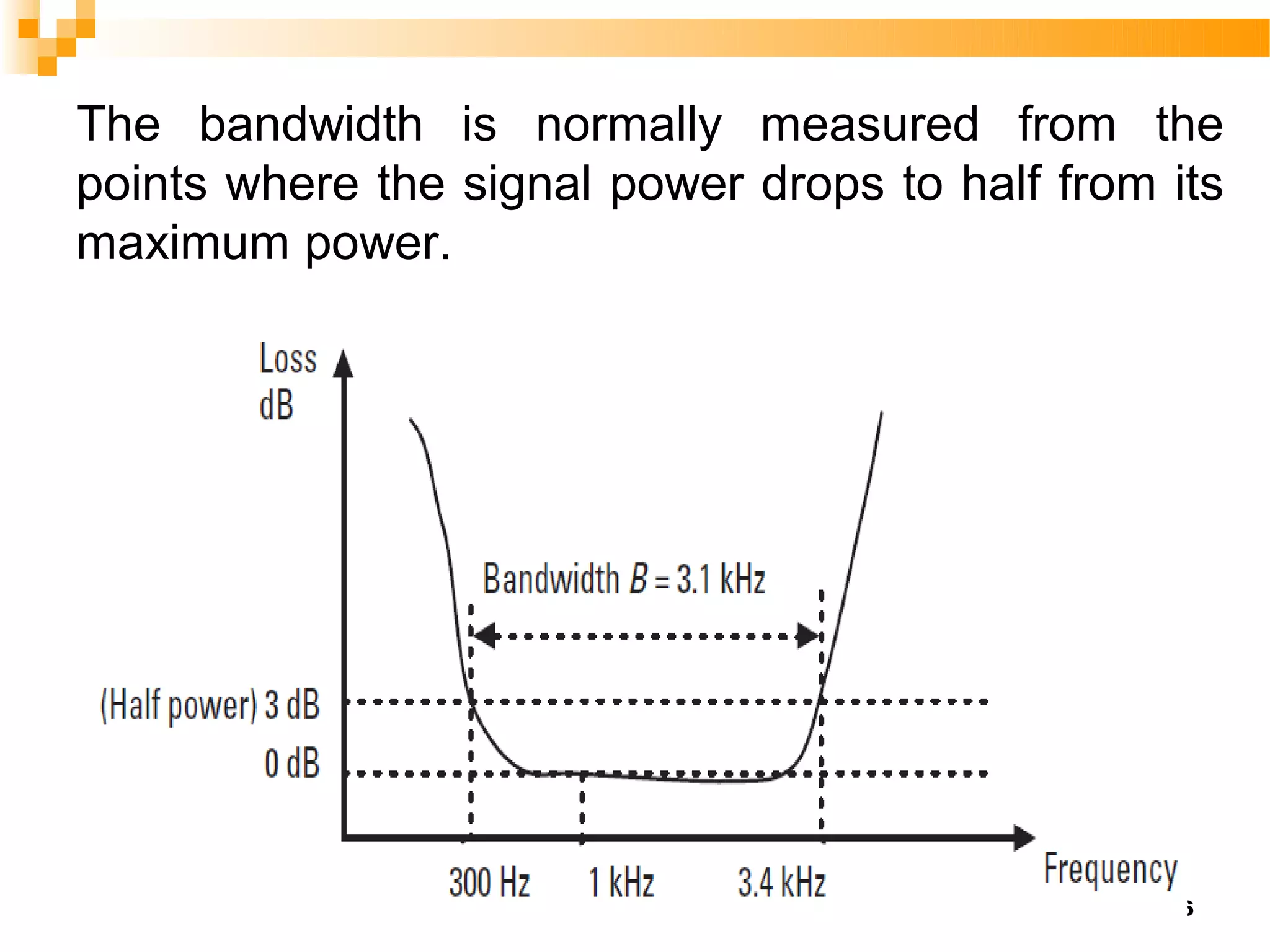
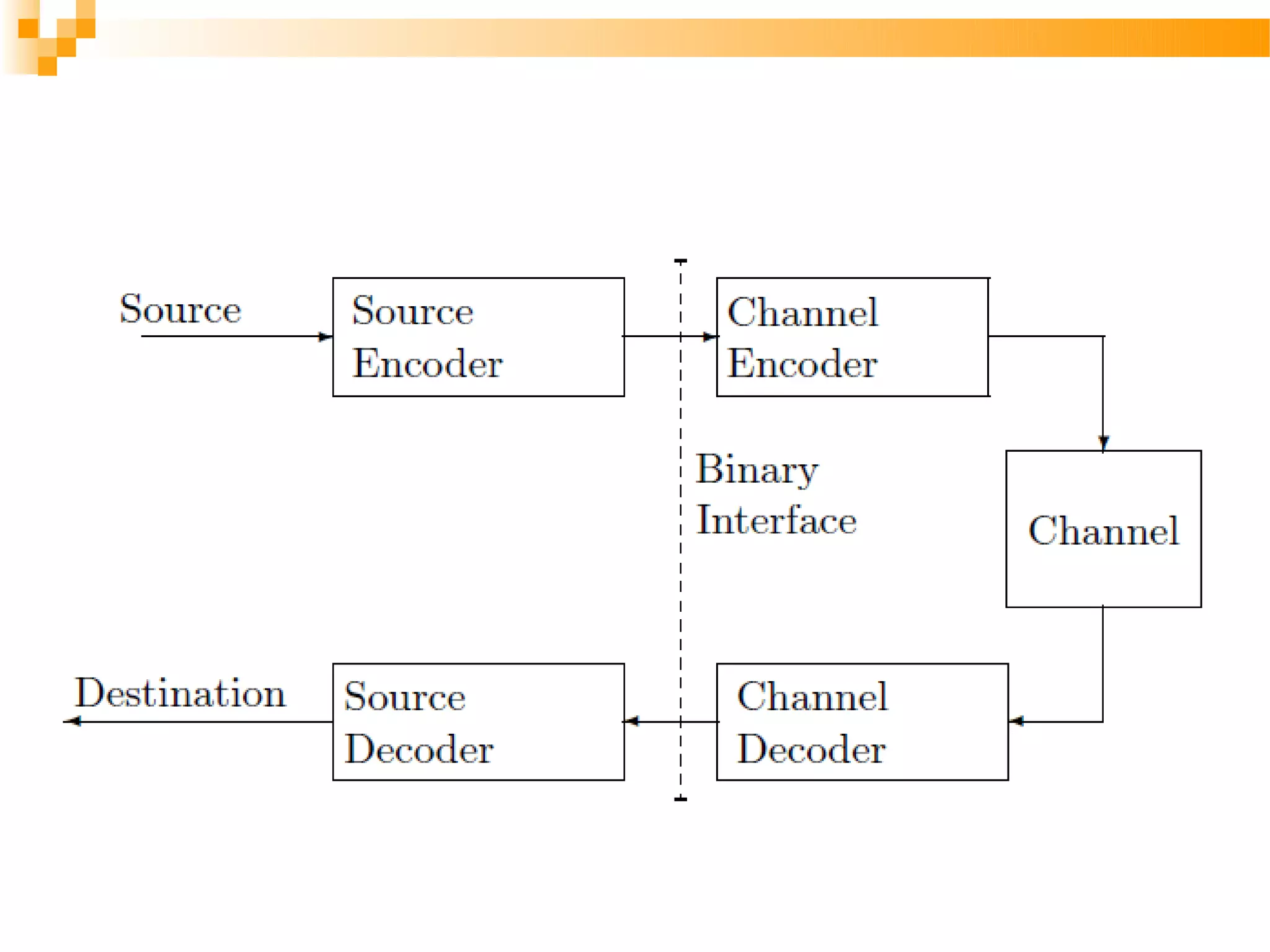
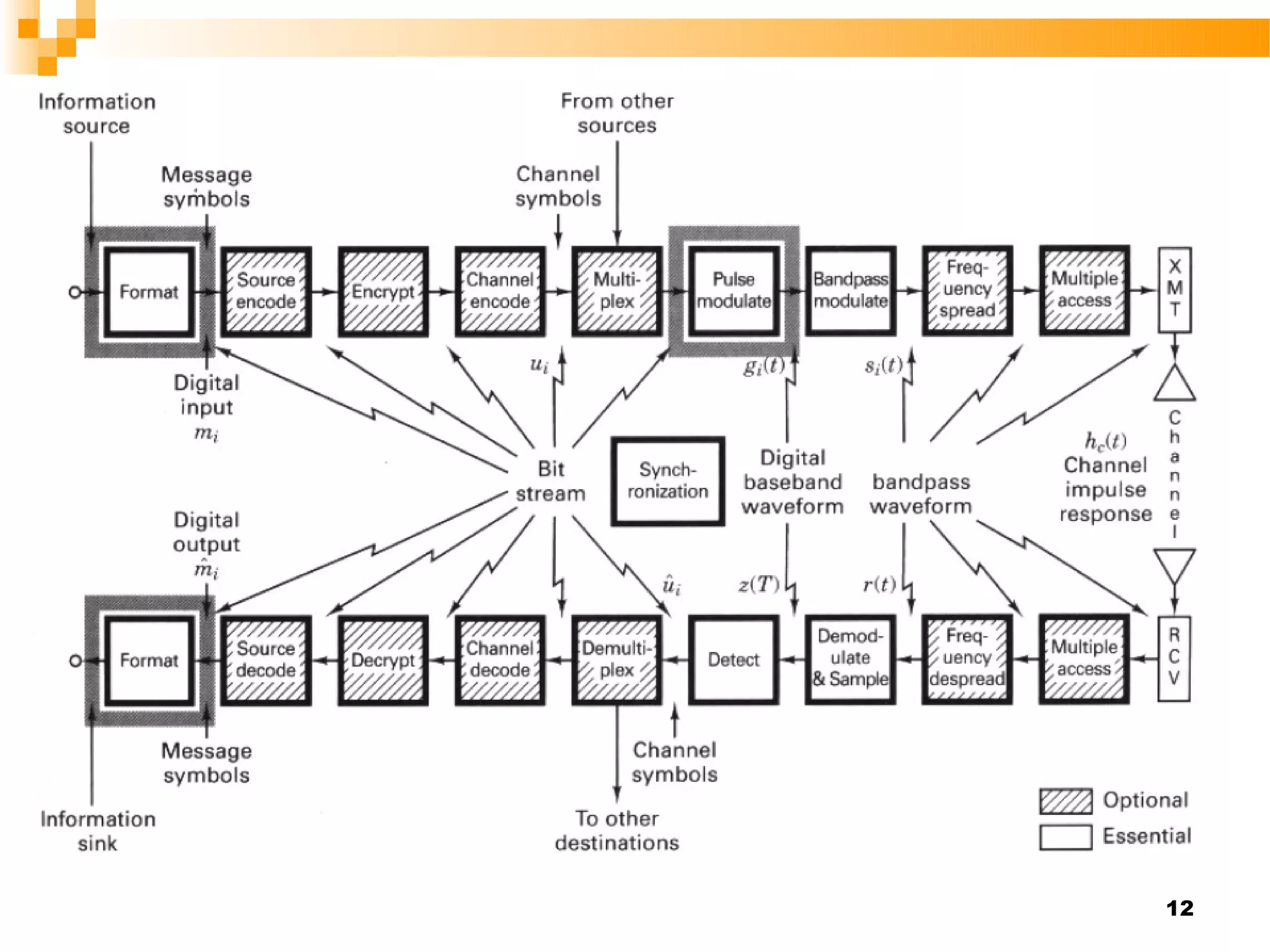
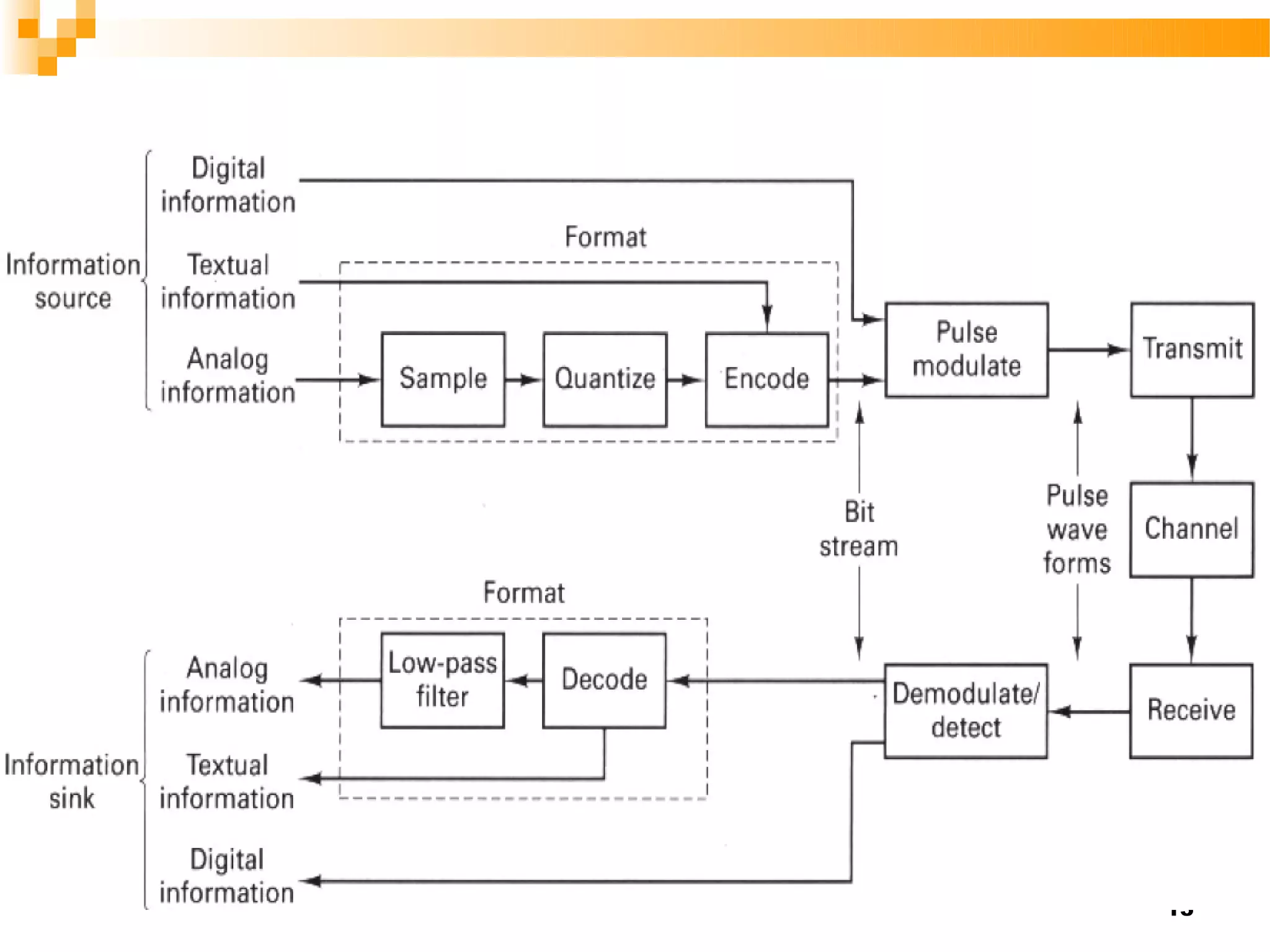
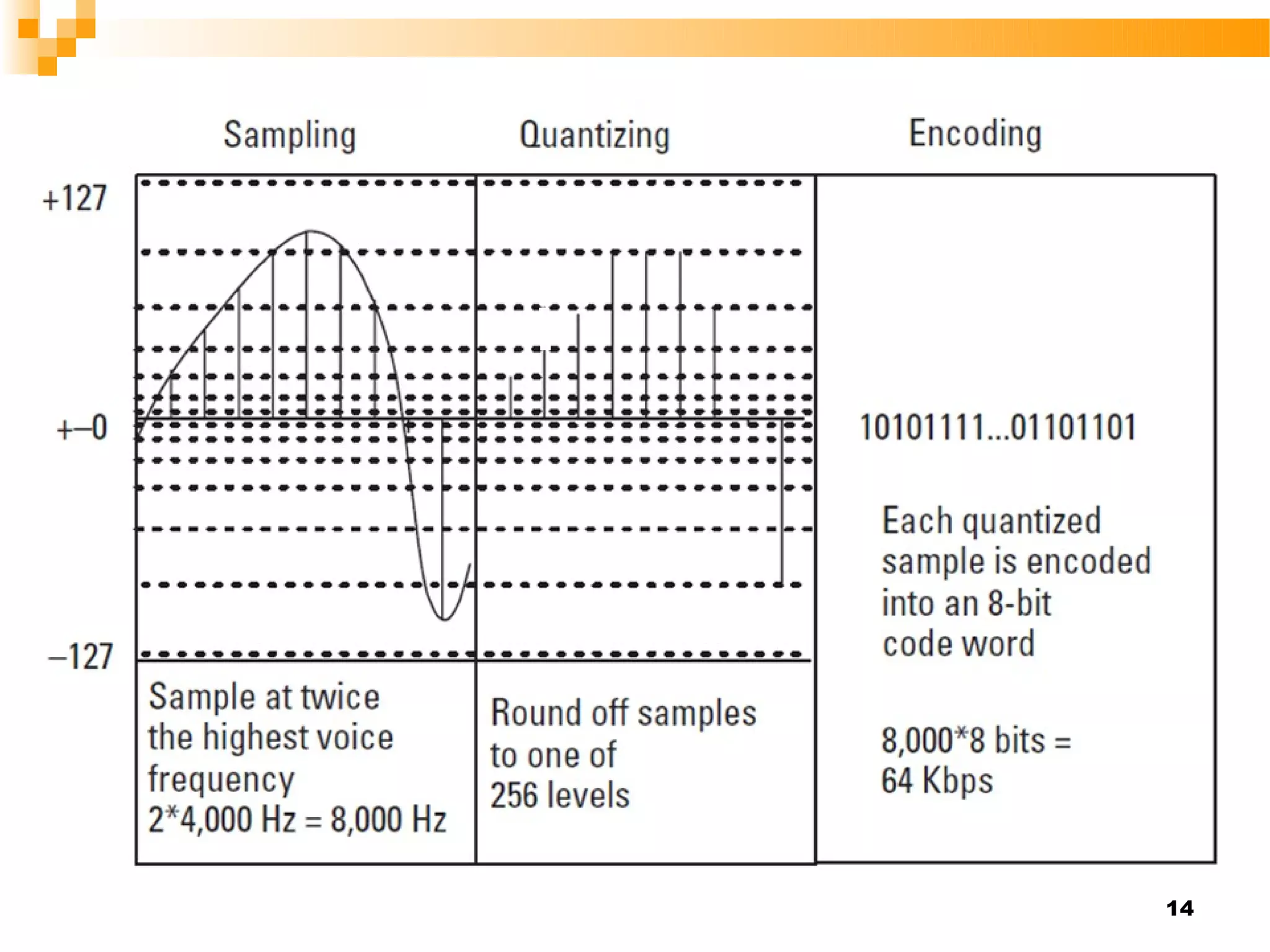
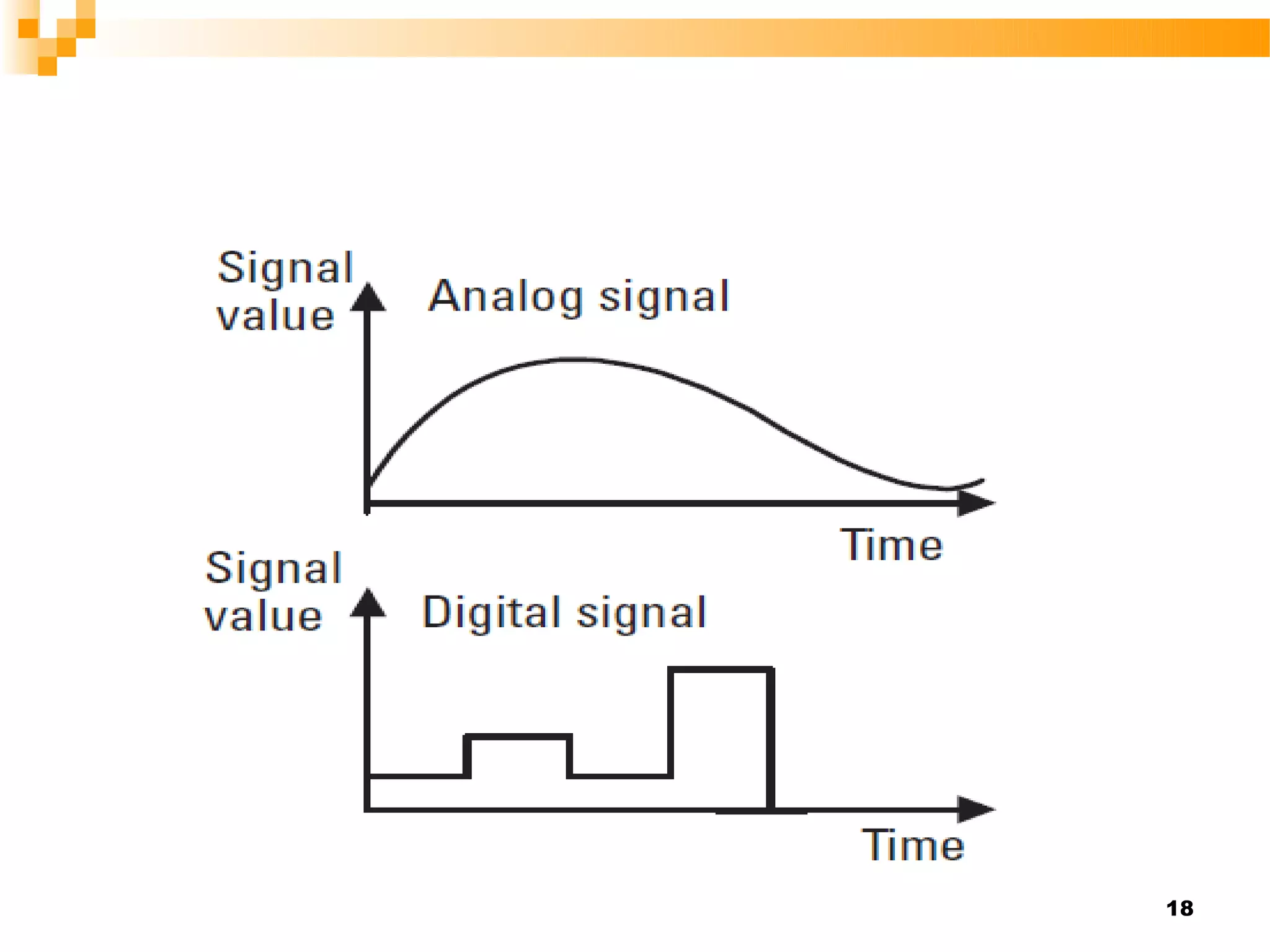
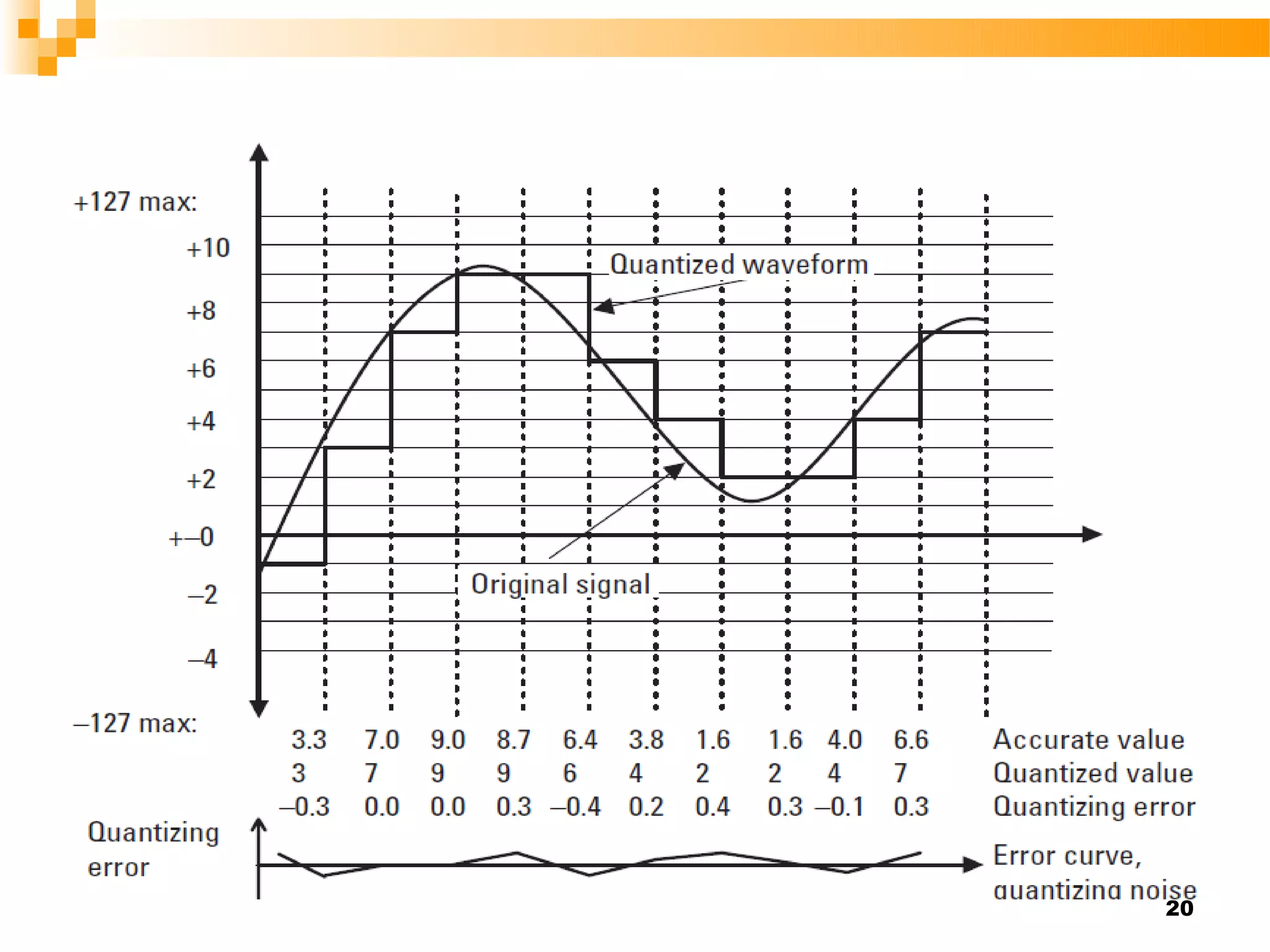
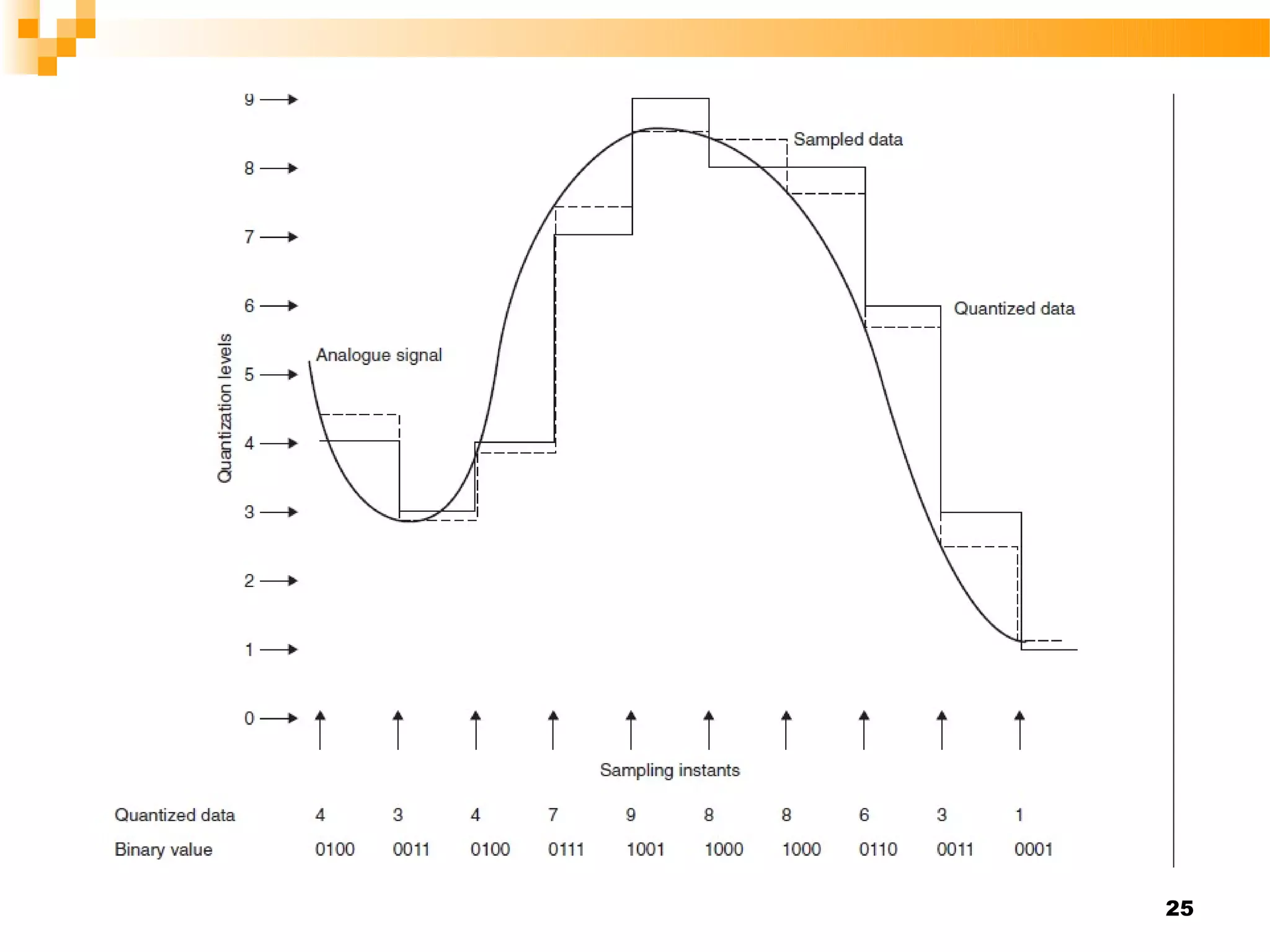
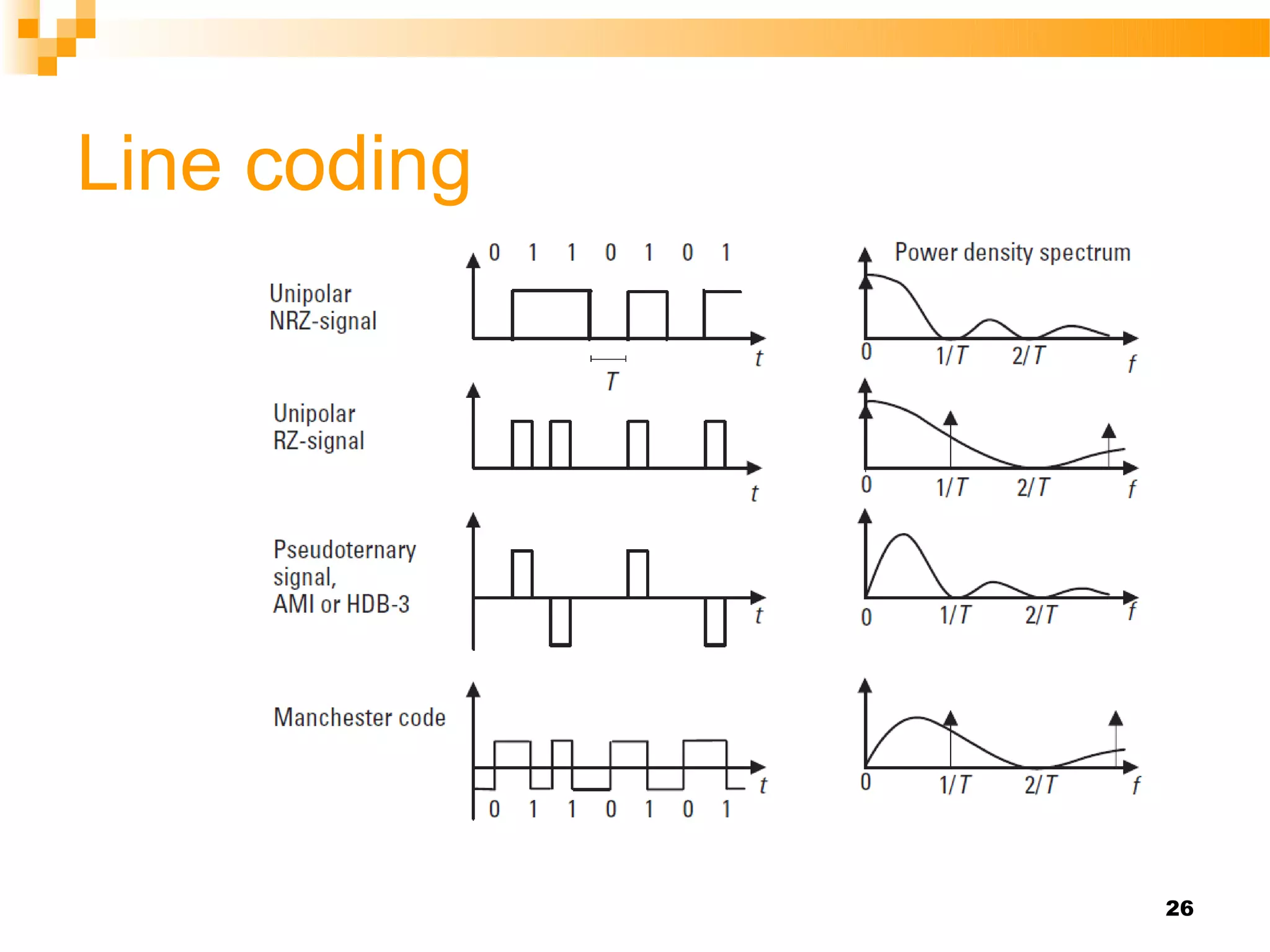
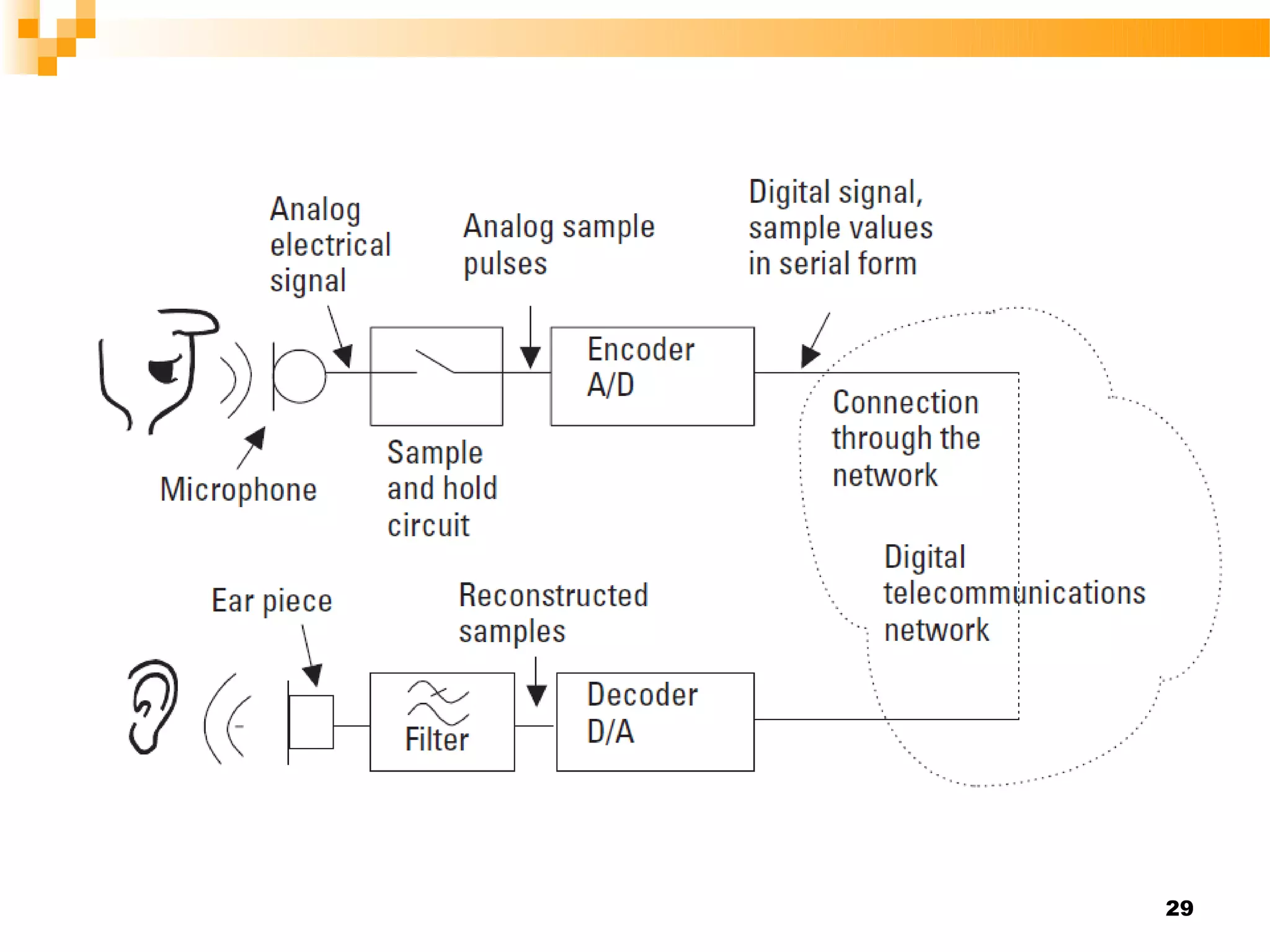
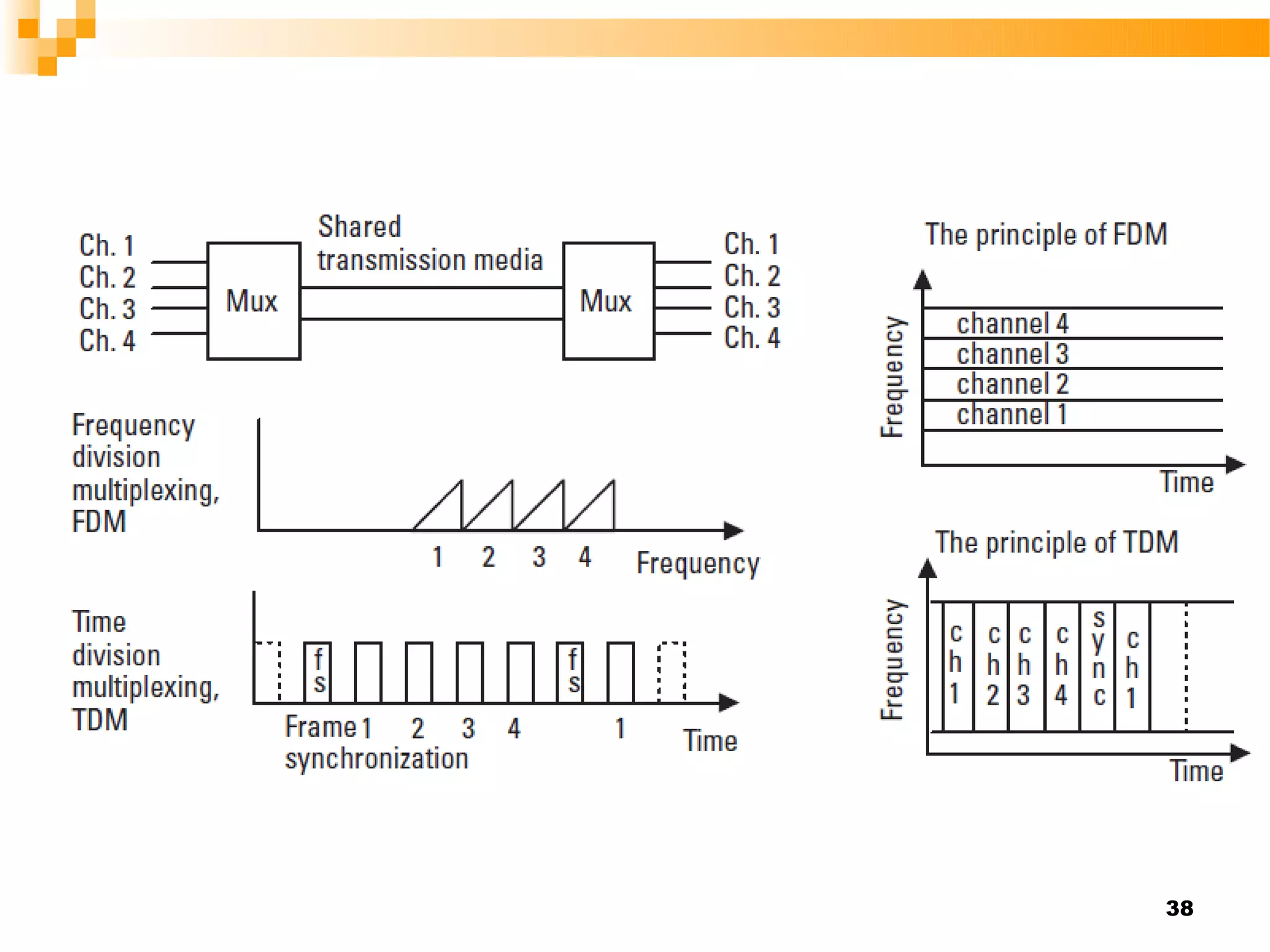
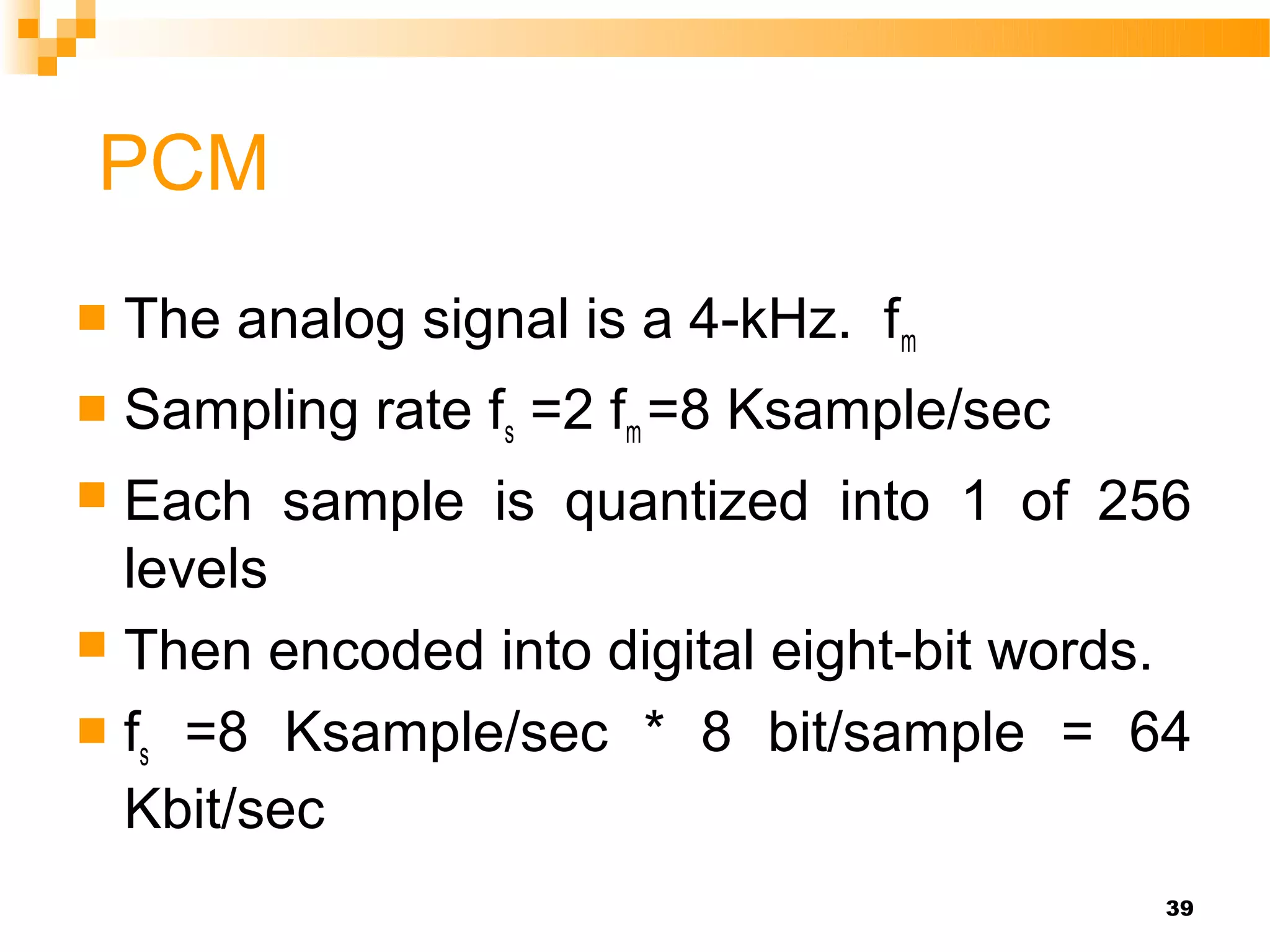
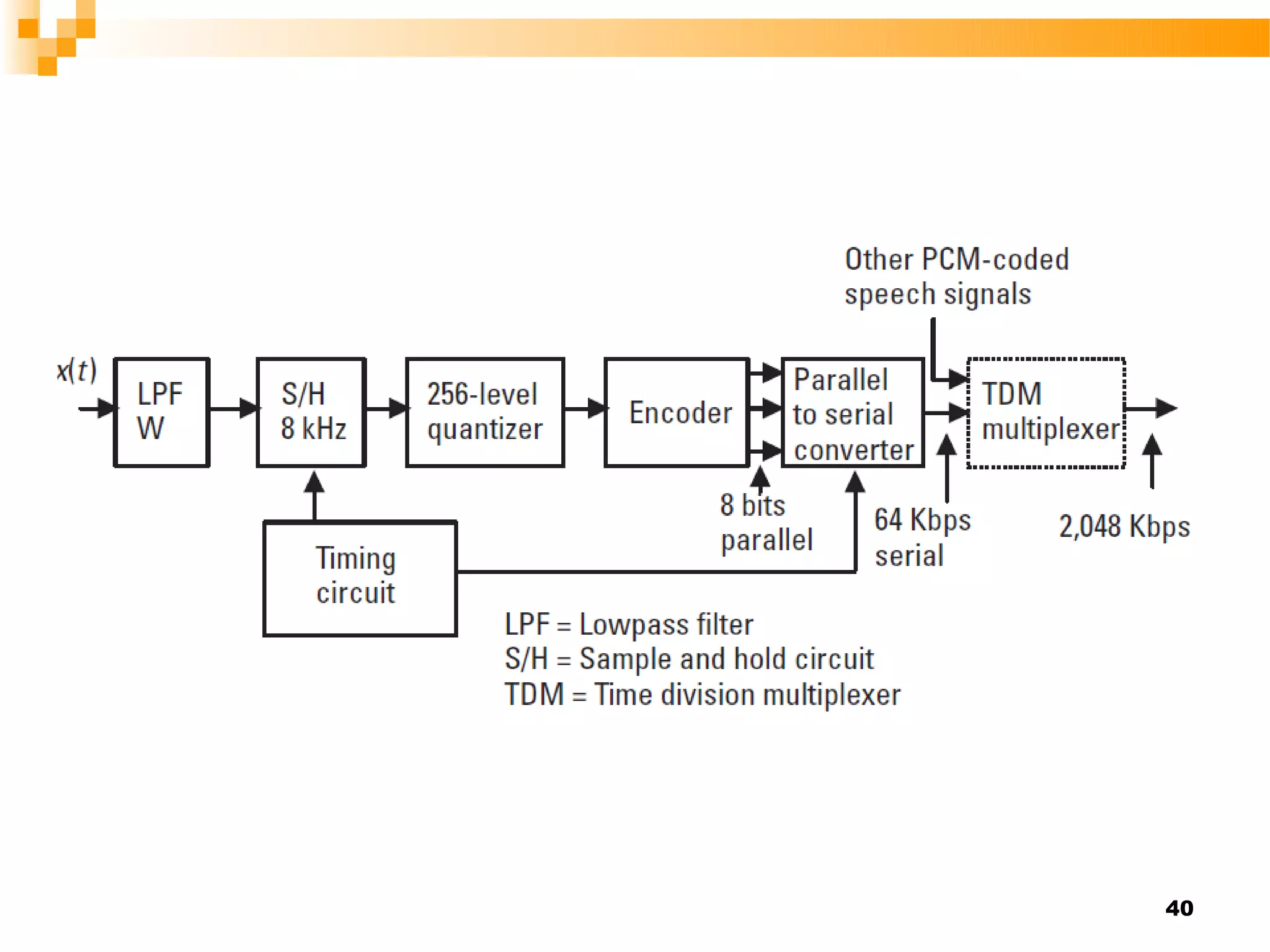
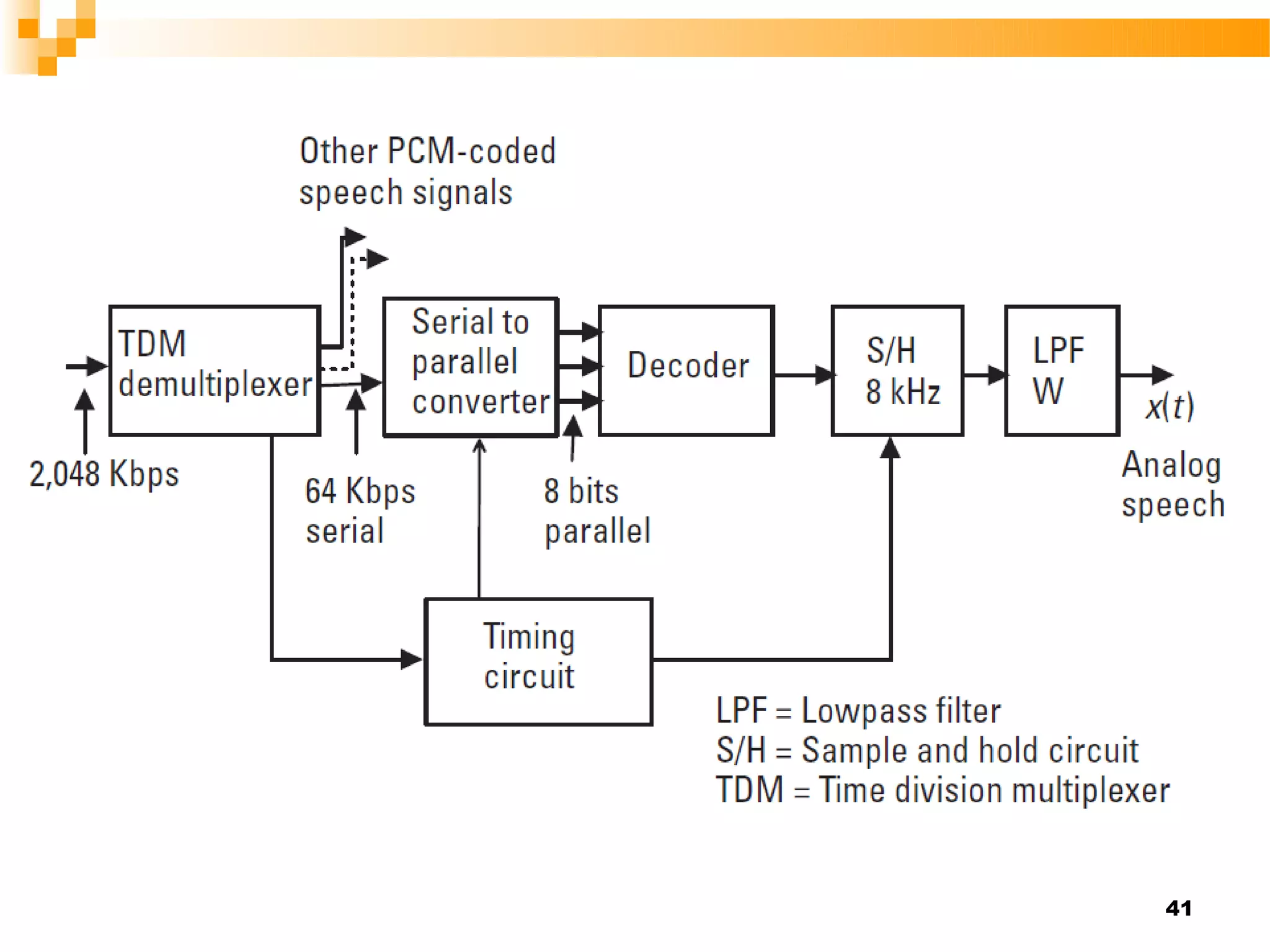
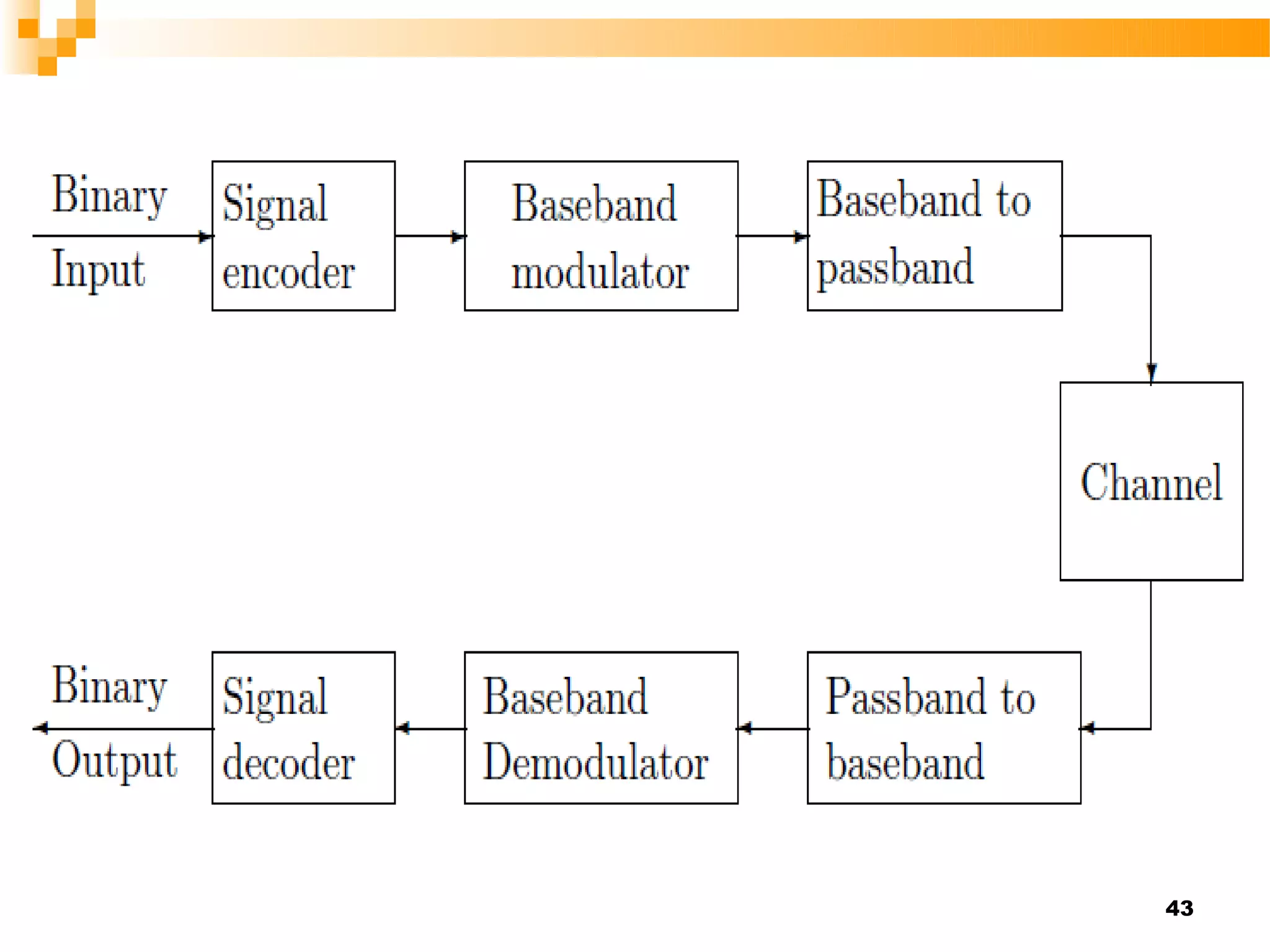
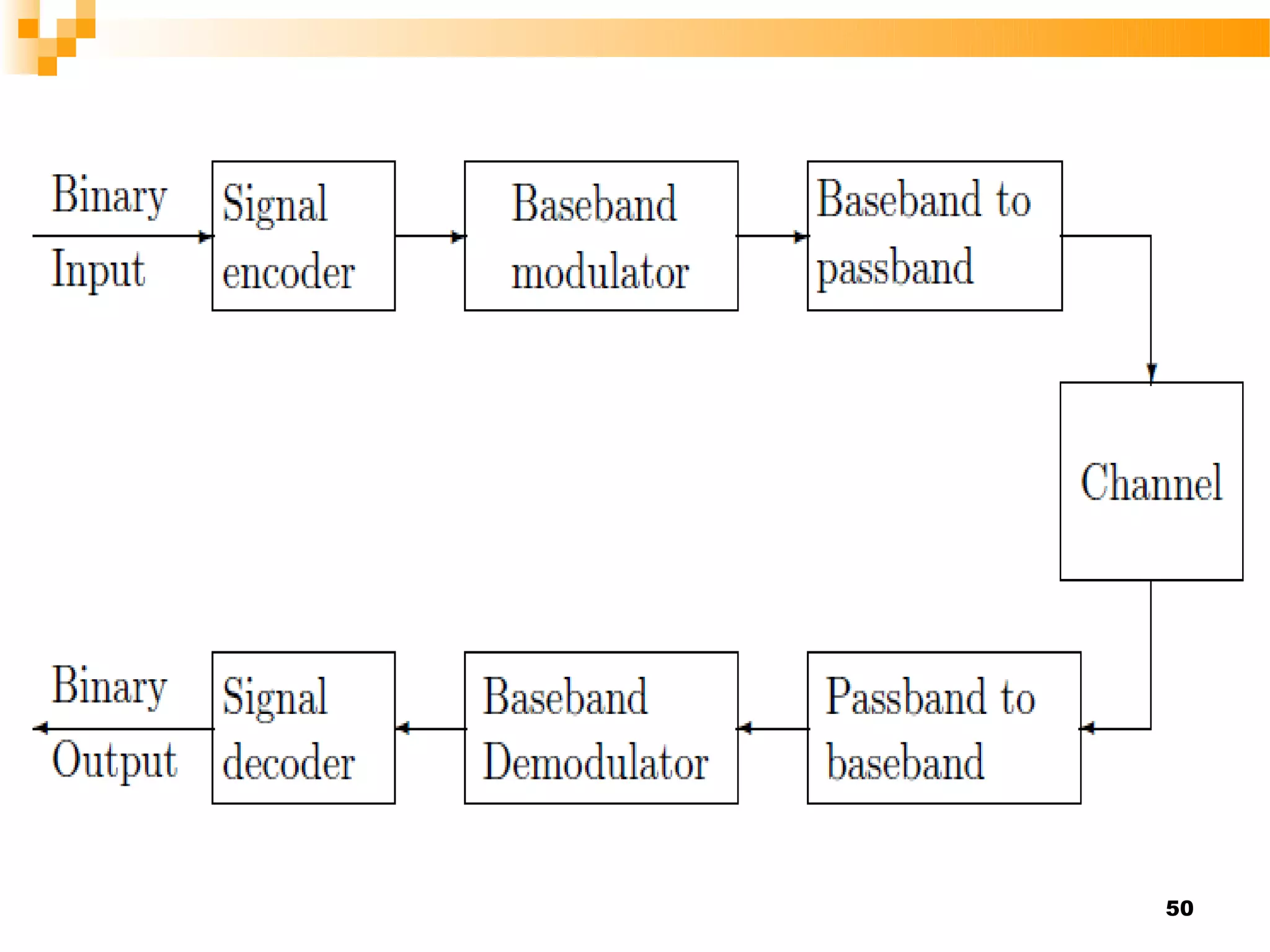
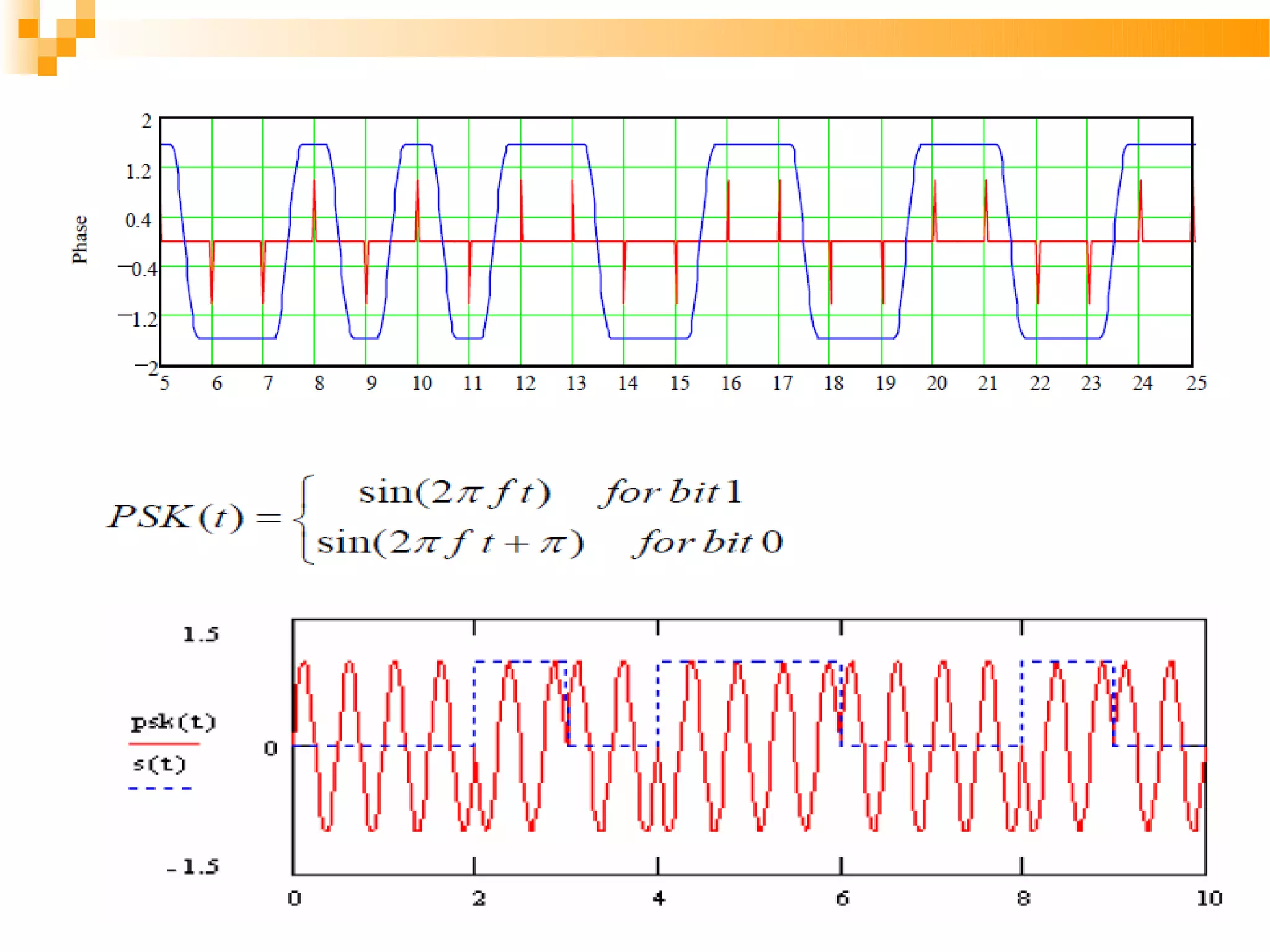
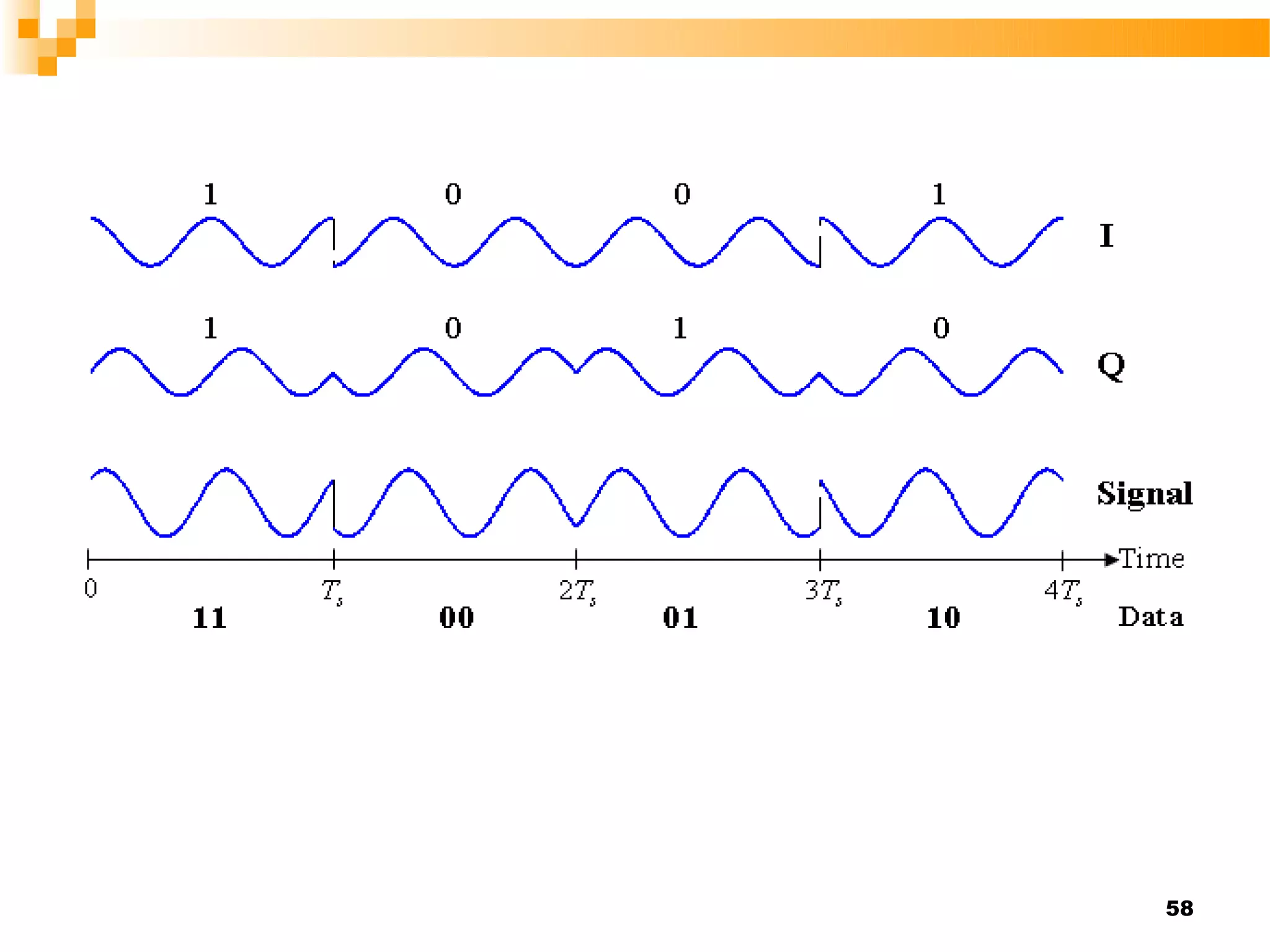
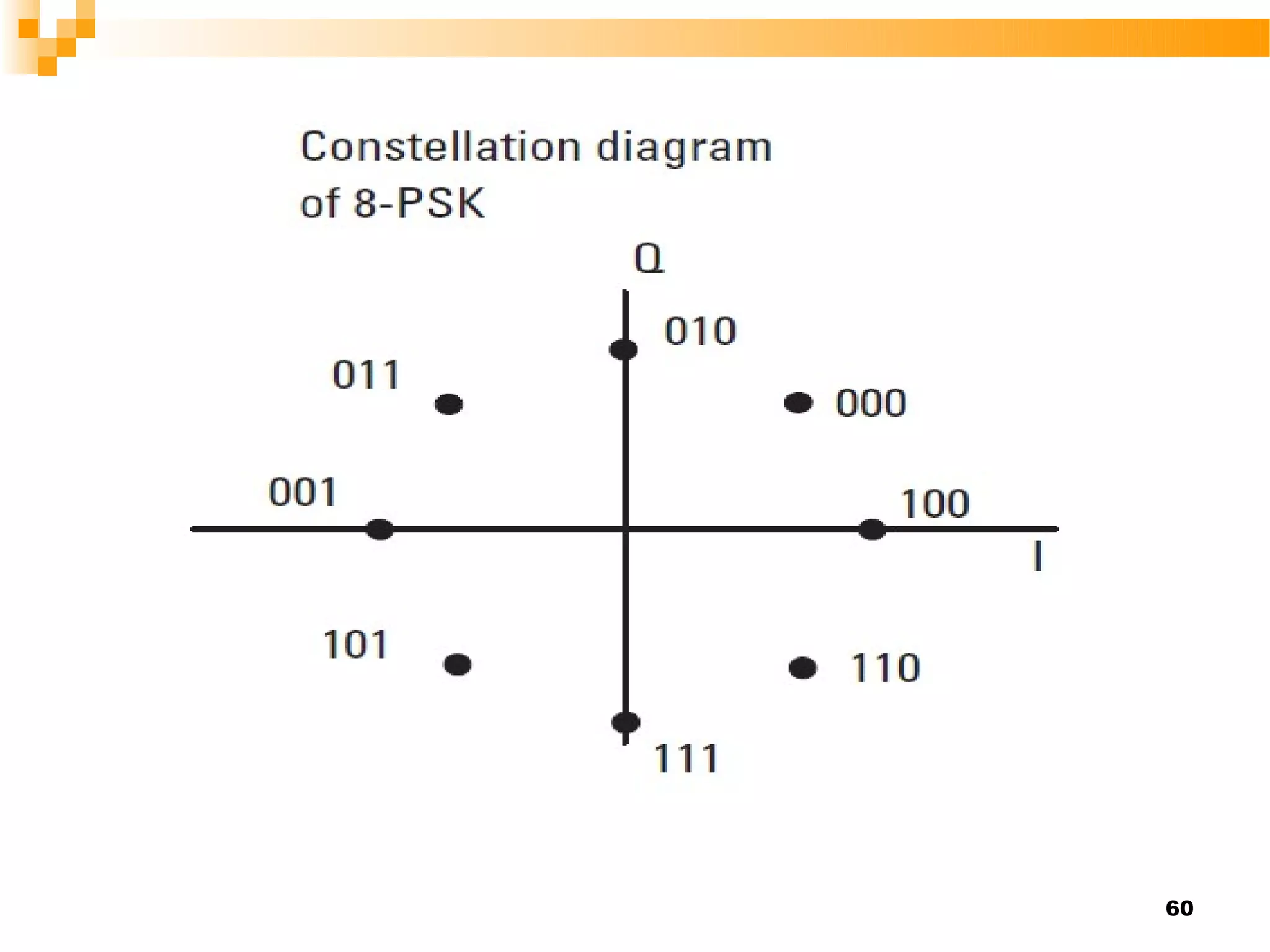
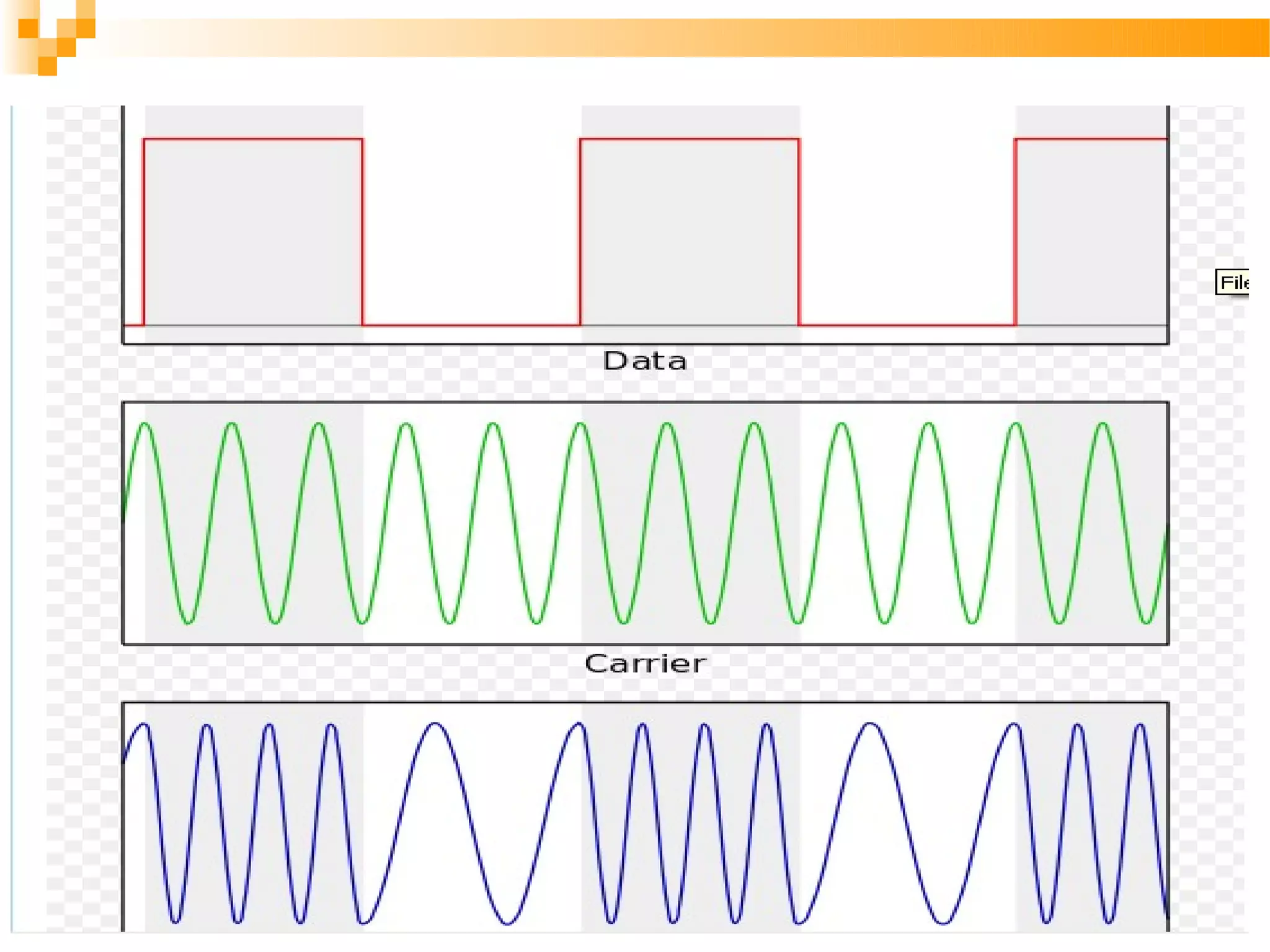
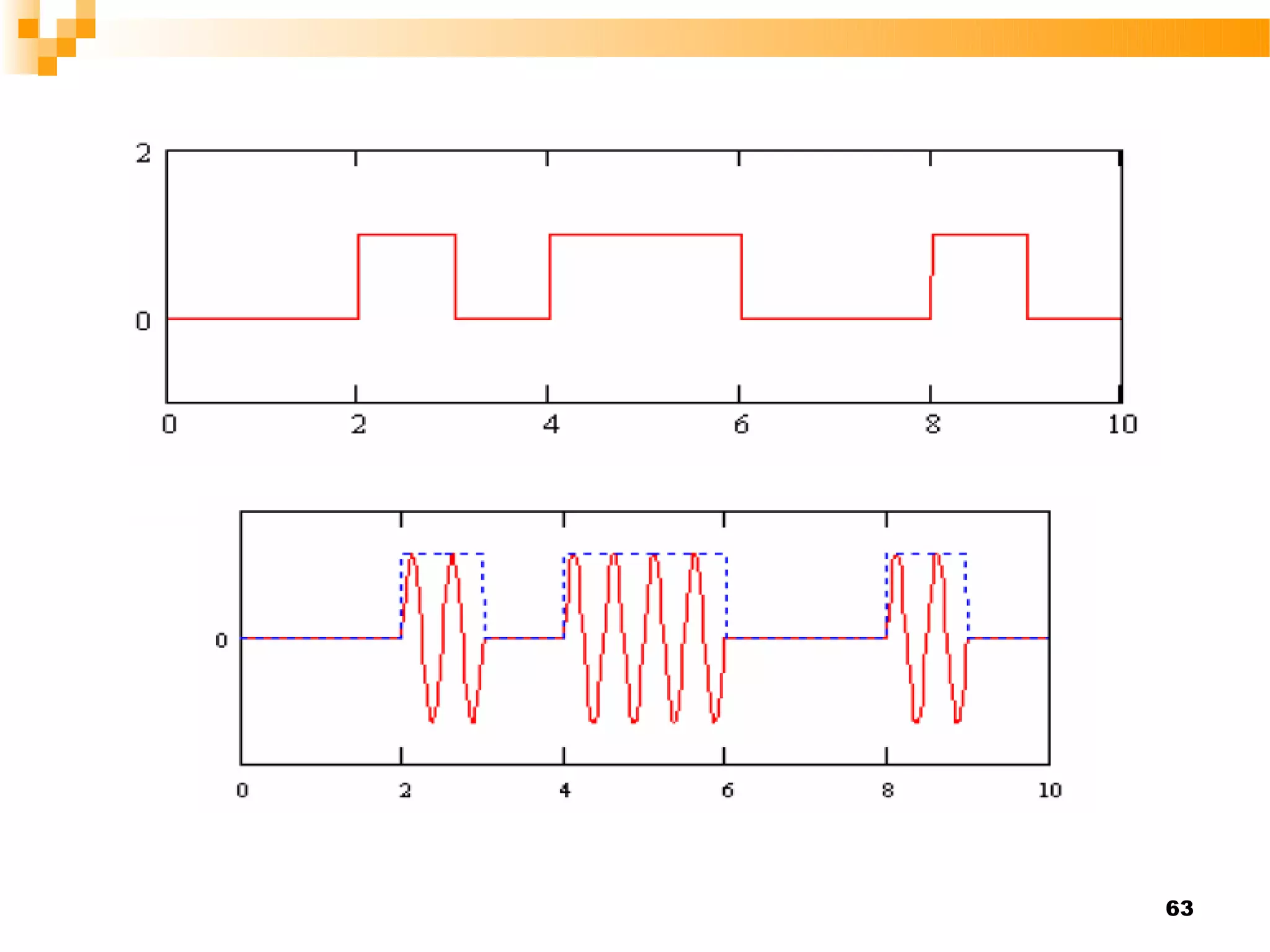
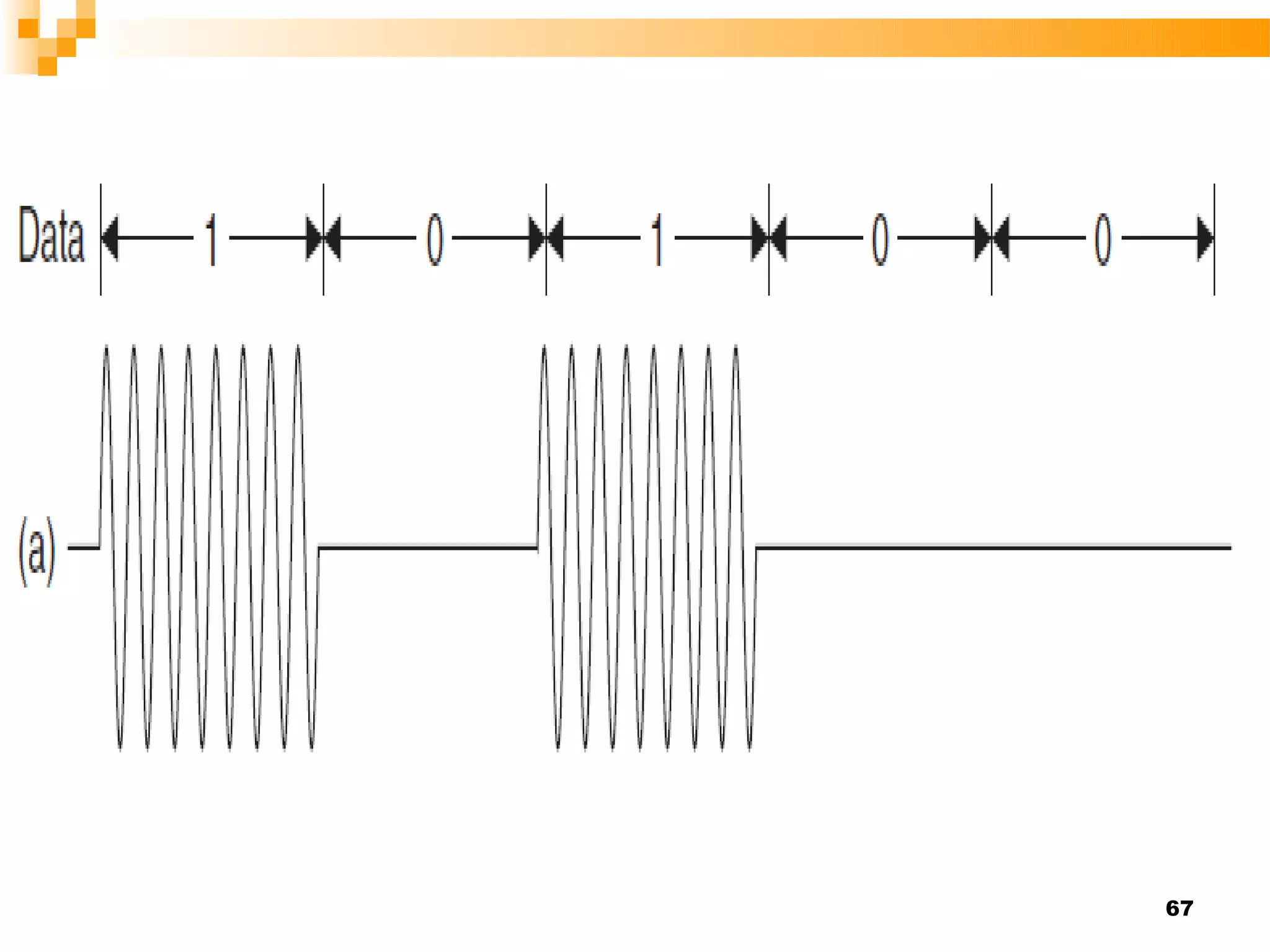
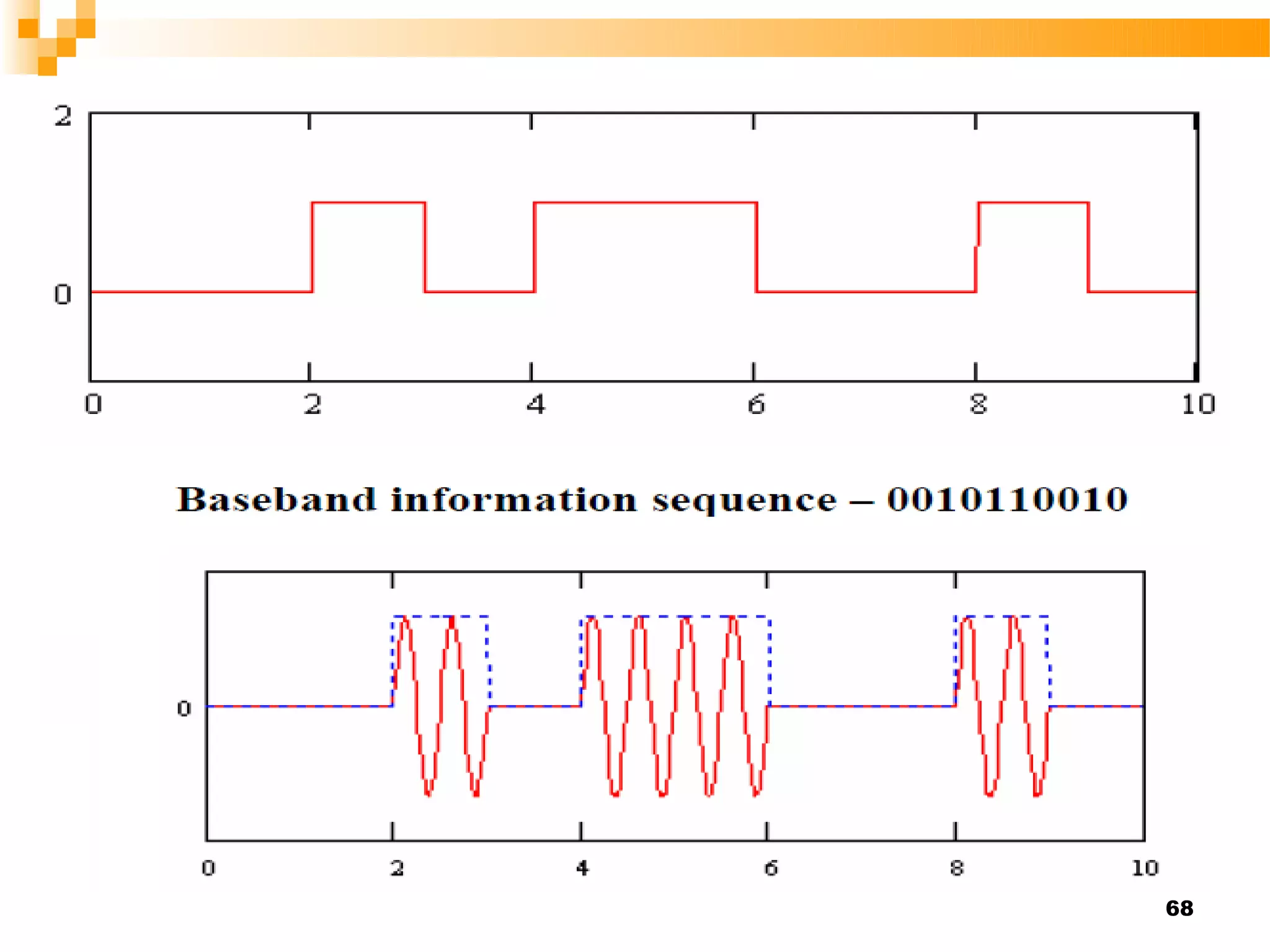
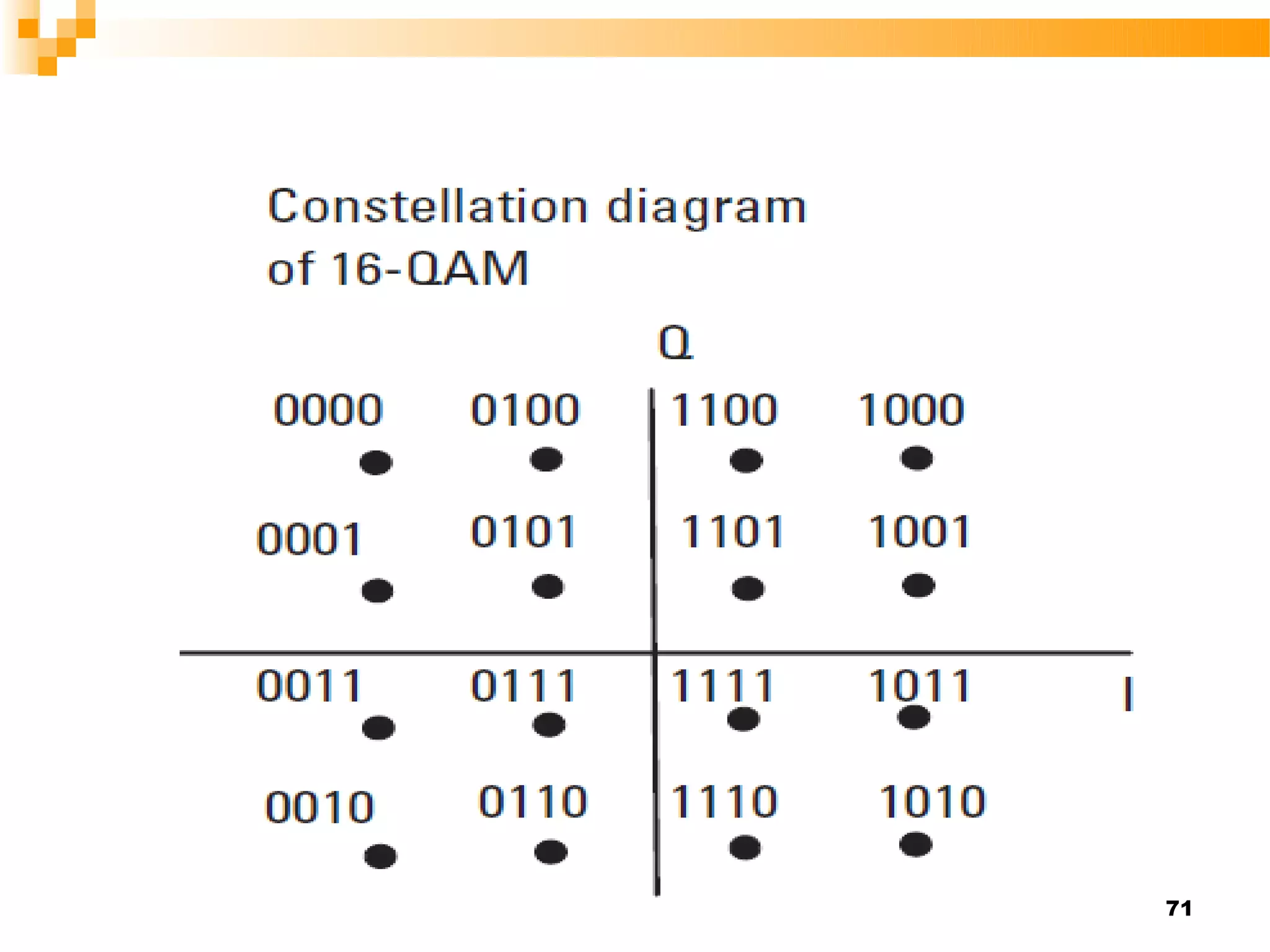
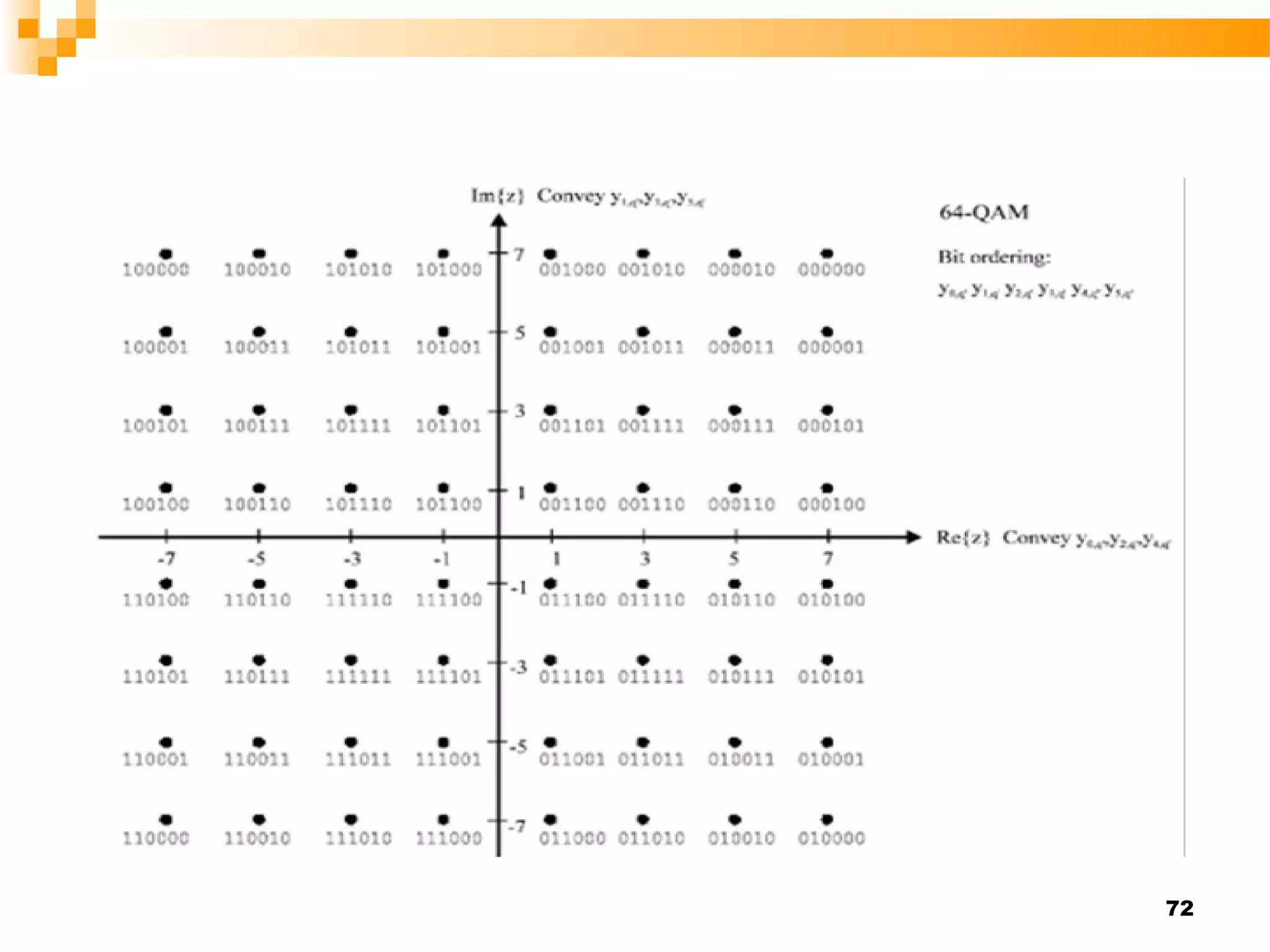
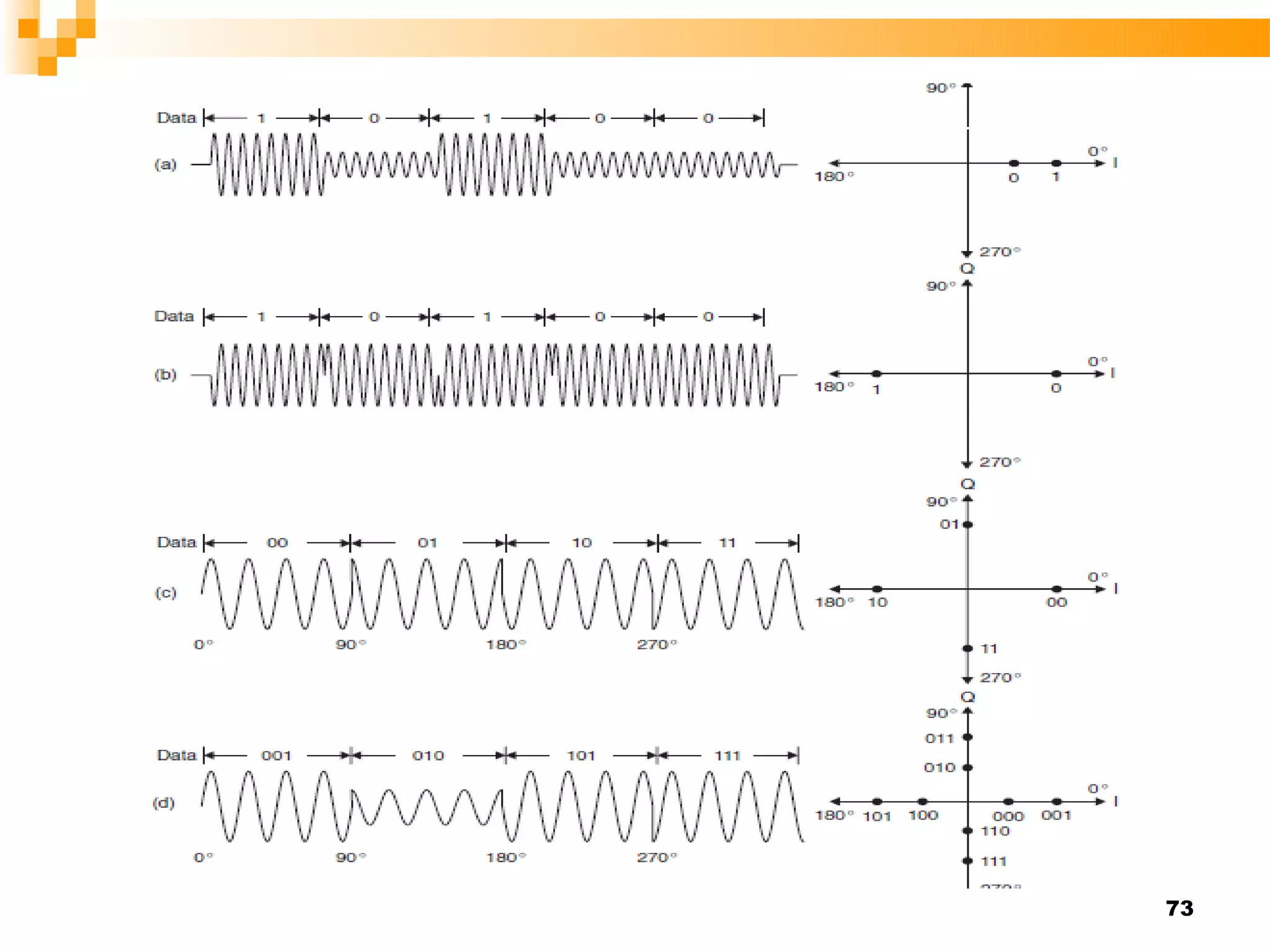
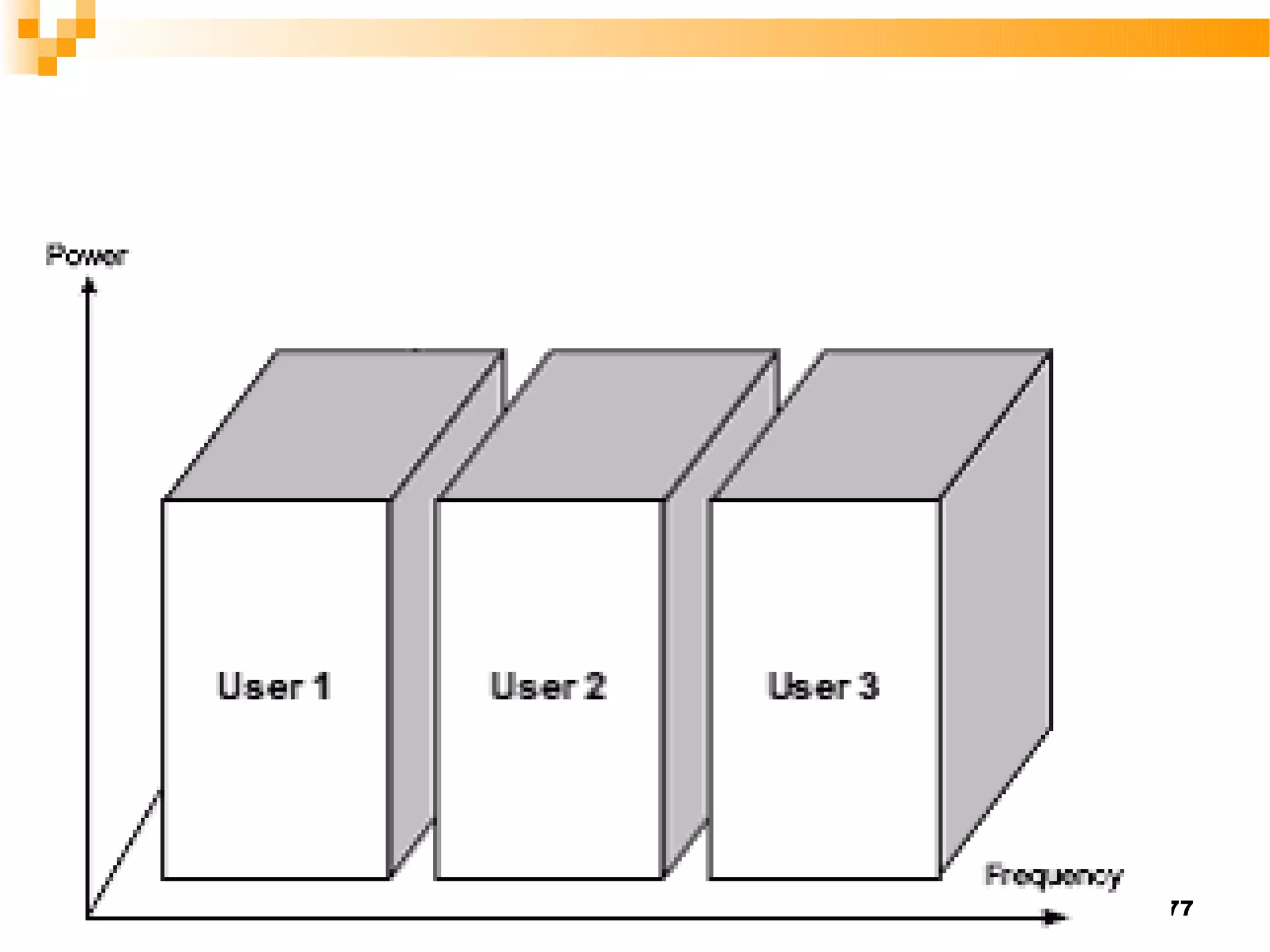
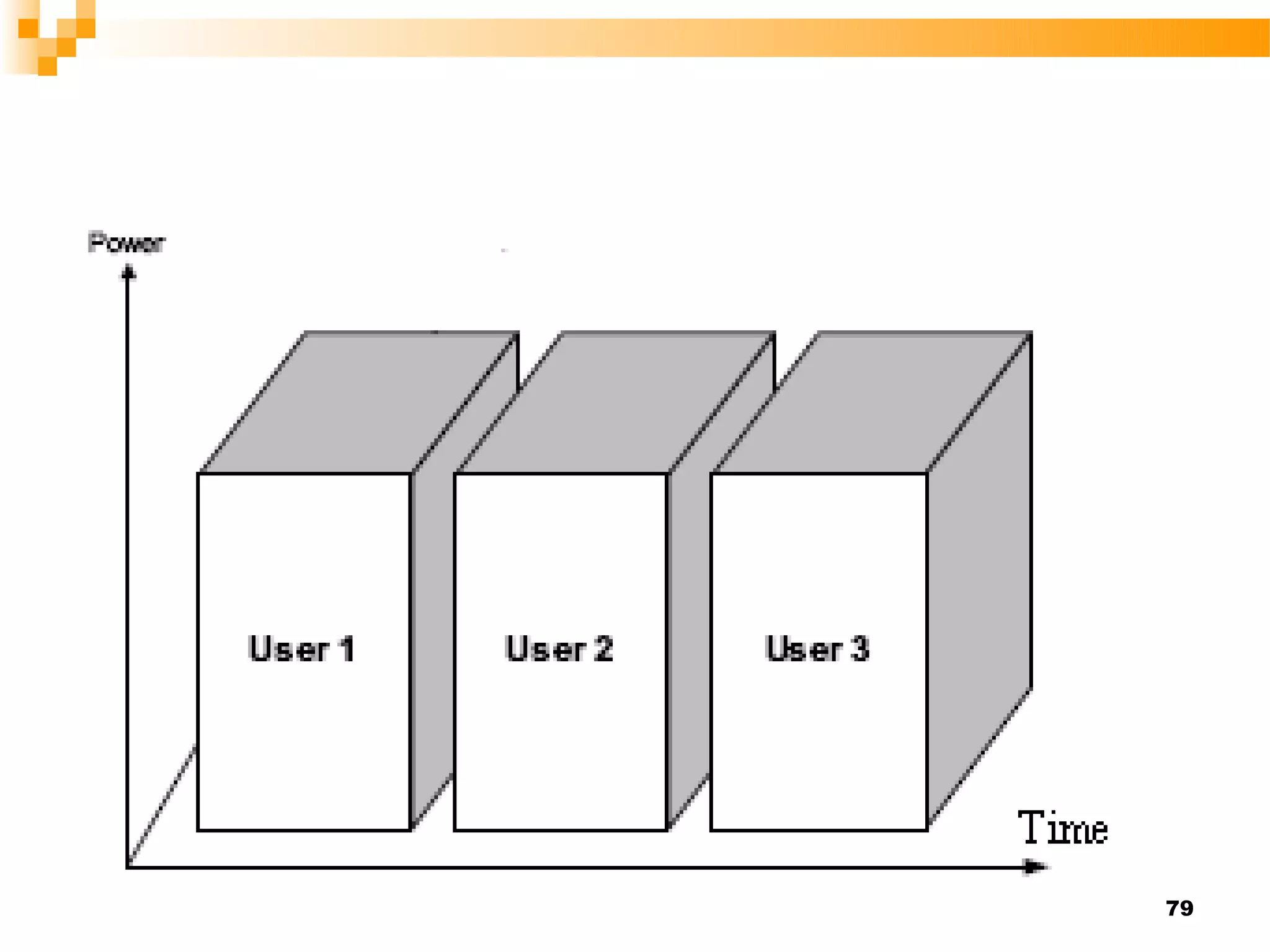
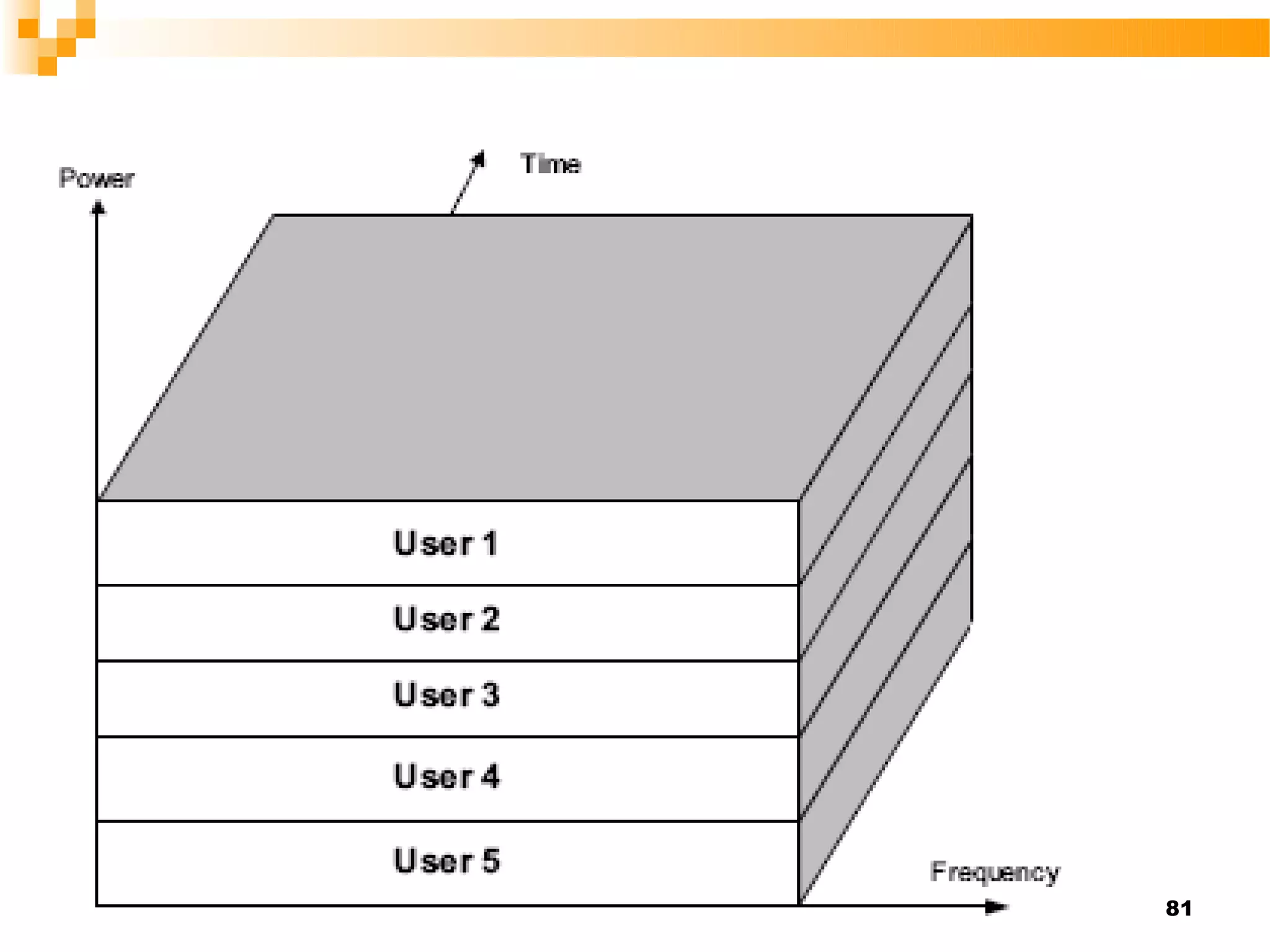
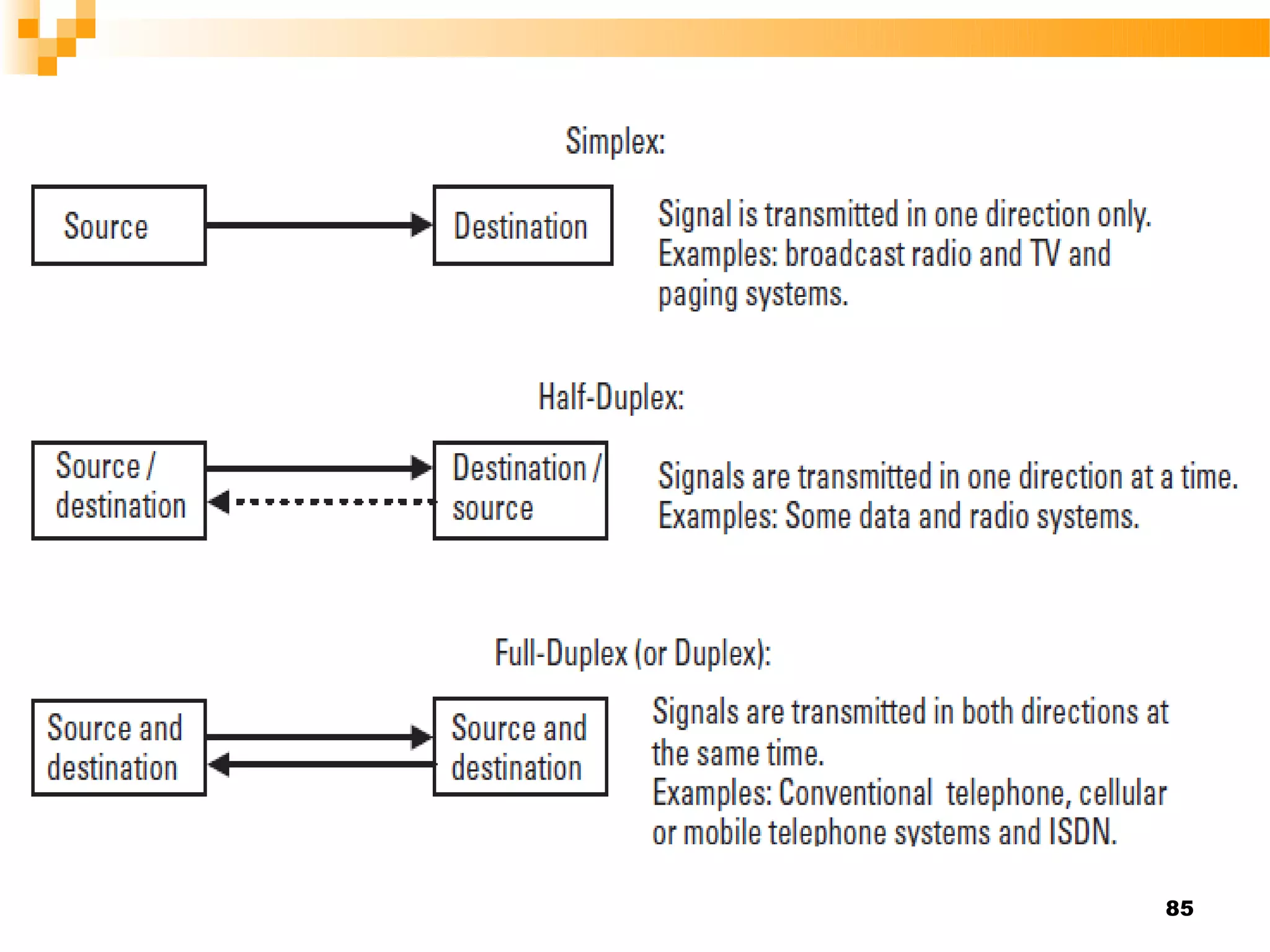
Digital communication systems allow transmission of information in digital form from one point to another. They involve source encoding, channel encoding/modulation, transmission over the channel, and decoding/demodulation at the receiver. Key concepts include frequency, bandwidth, sampling, quantization, line coding, multiplexing, channel coding, and digital modulation techniques like PSK, FSK, ASK, and QAM. Multiple access methods like FDMA, TDMA, and CDMA are used to enable multiple users to access the channel simultaneously. Duplex systems can be simplex, half-duplex, or full-duplex depending on the direction of transmission.