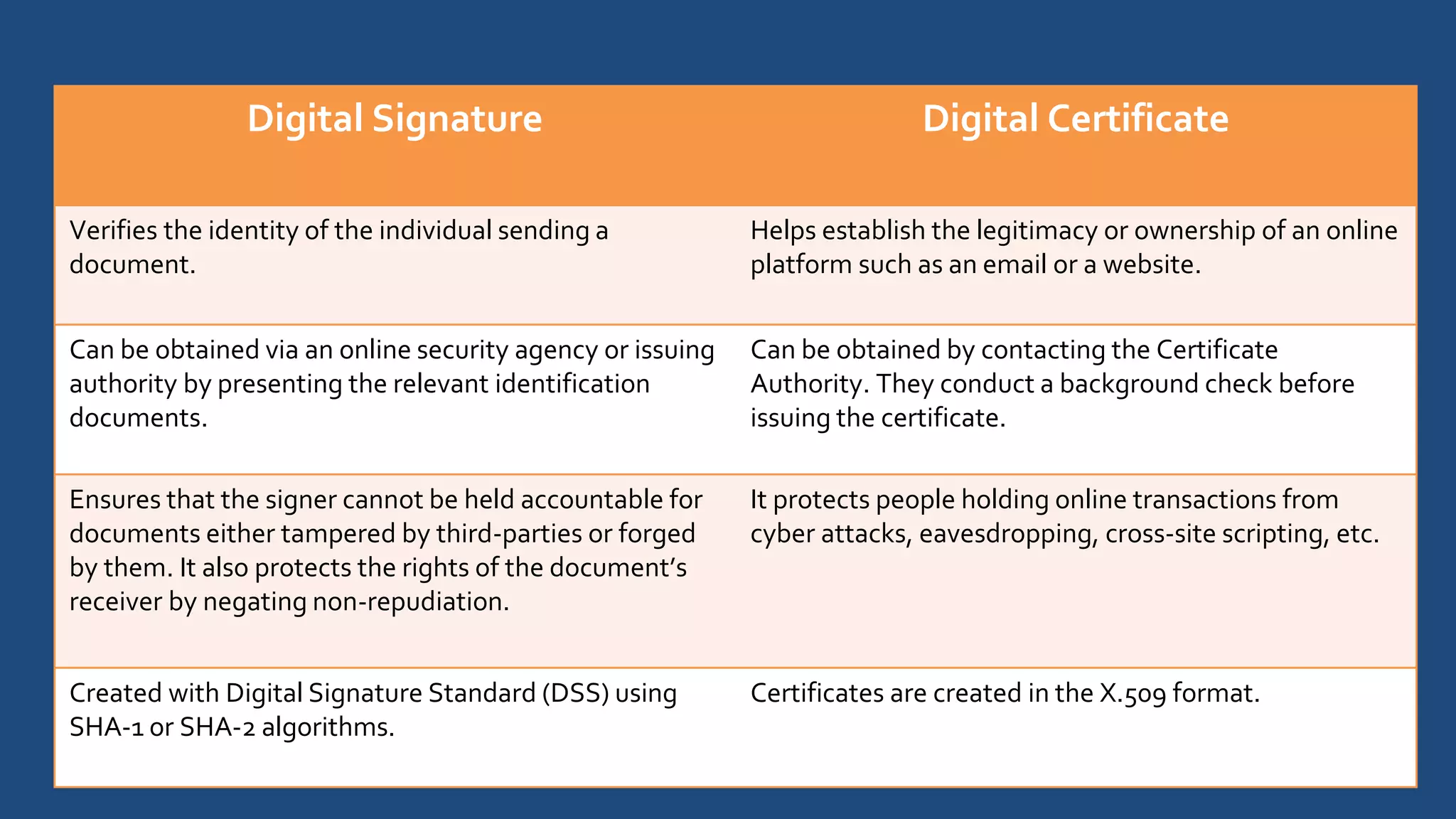
The document explains the differences between digital signatures and digital certificates, outlining the purpose and functionality of each. Digital signatures ensure the authenticity and integrity of documents, while digital certificates serve as identification cards issued by authorities to verify an individual's identity. Both play crucial roles in securing online transactions and protecting against fraud and tampering.