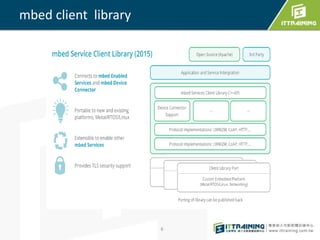
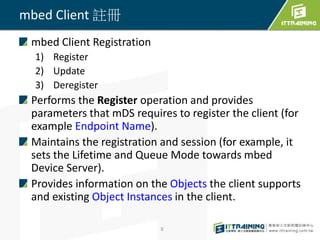
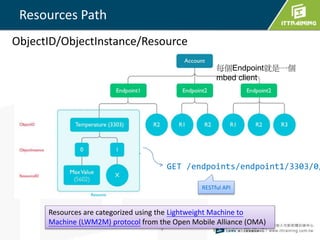
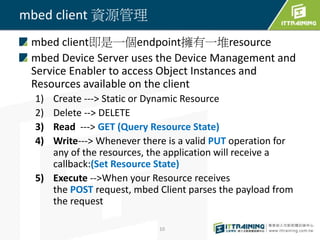
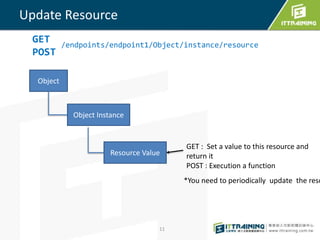
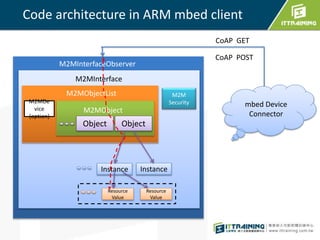
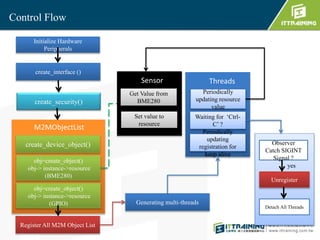
The document outlines the mbed Device Connector and its benefits, including compatibility with mbed OS and the LwM2M protocol, facilitating energy-efficient data communication and device management. It details the functionality of the mbed client library, which supports constrained networks and performs operations such as registration, resource management, and communication via CoAP. Additionally, it provides instructions for building and running mbed client applications using Yotta.




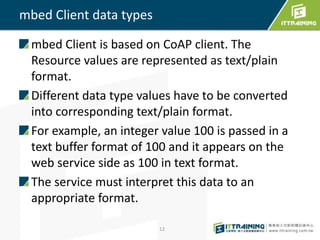
![HTTP 都是字串 text
13
int value = 1;
M2MResource* instance = objinst->create_dynamic_resource(“D",
“IntegerType“,M2MResourceInstance::INTEGER, true);
char buffer[20];
int size = sprintf(buffer,"%d",value);
instance->set_value((const uint8_t*)buffer, size);
float value = 1.023; --> FLOAT
bool value = true; --> BOOLEAN
char *str; --->STRING](https://image.slidesharecdn.com/2mbedcloud-160730054715/85/Deploy-mbed-IoT-cloud-13-320.jpg)
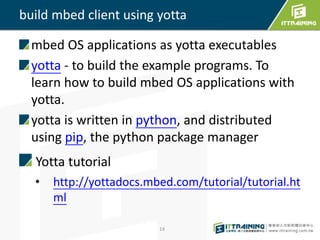

![編譯 mbed client
課程Sample Code
Install yotta tools
安裝說明 : http://blog.ittraining.com.tw/2016/06/raspberry-
pi-mbed-client.html
編譯mbed client
1) cd iot_demo/mbed-client-pi/mbed-linux/
2) change source/security.h
須登入 https://connector.mbed.com/ 產生security.h
[Security credentials]
3) yotta build
4) 執行程式:
build/arm-linux-native/source/mbed-client-
linux-example
18](https://image.slidesharecdn.com/2mbedcloud-160730054715/85/Deploy-mbed-IoT-cloud-18-320.jpg)