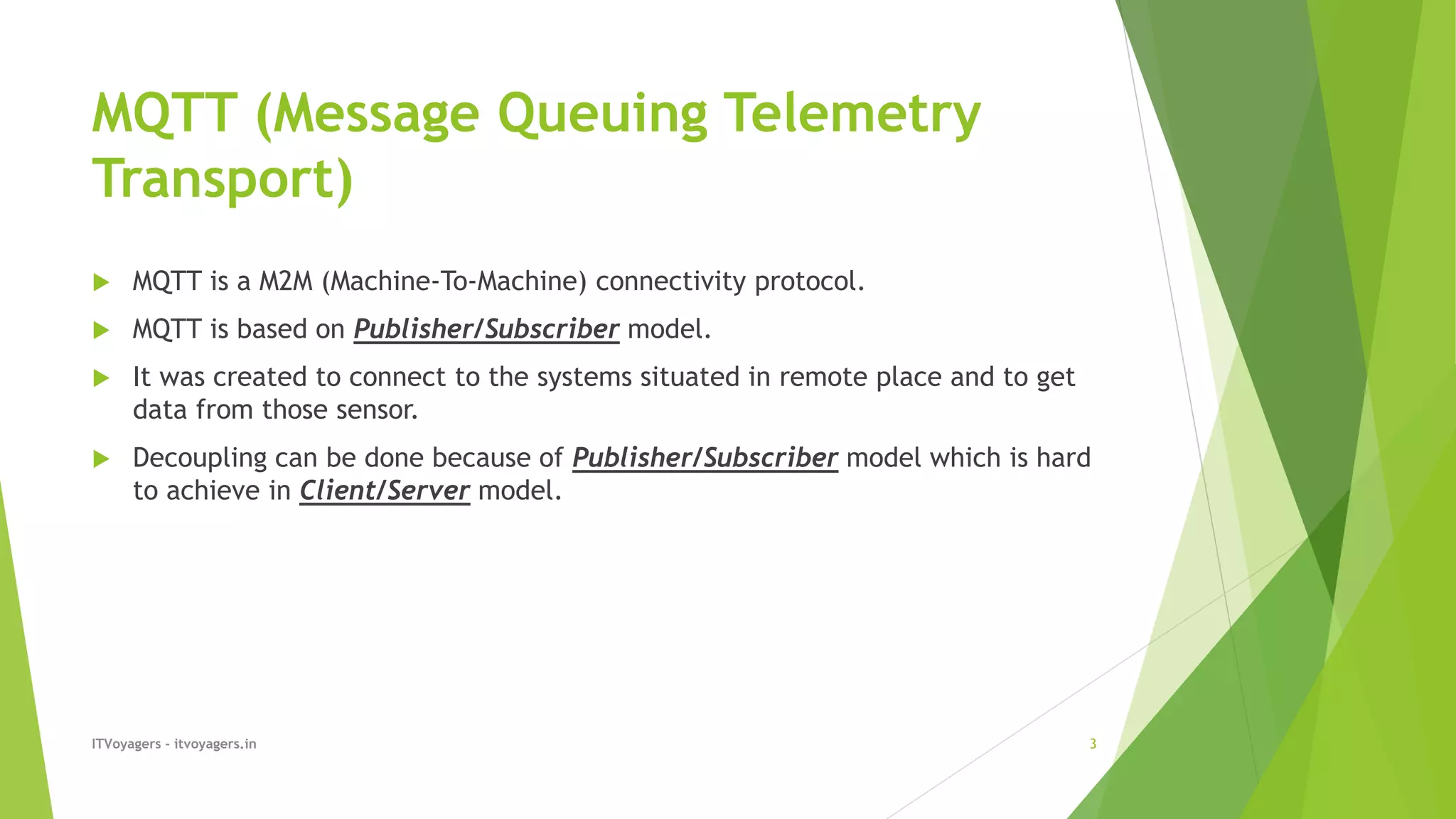
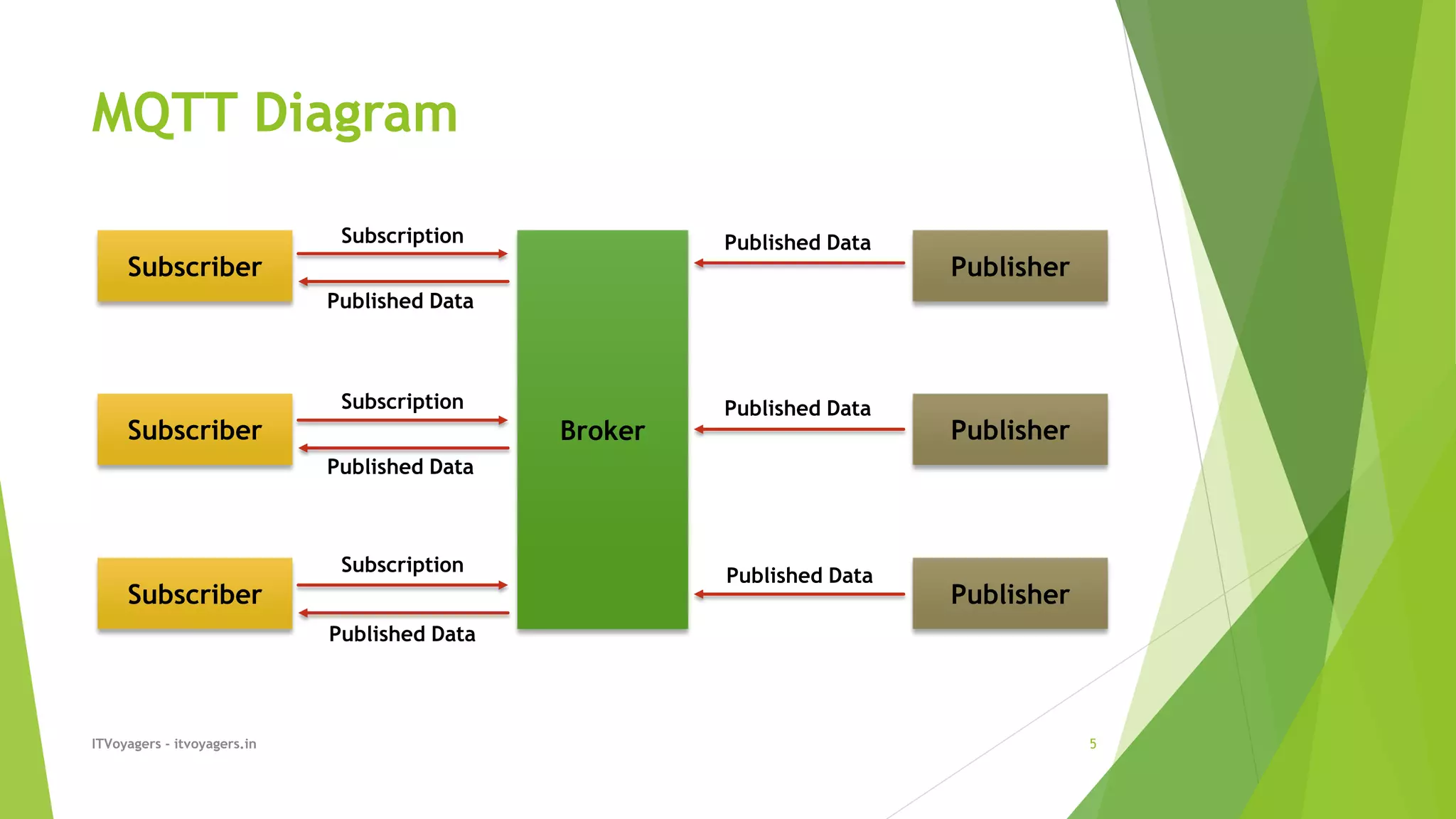
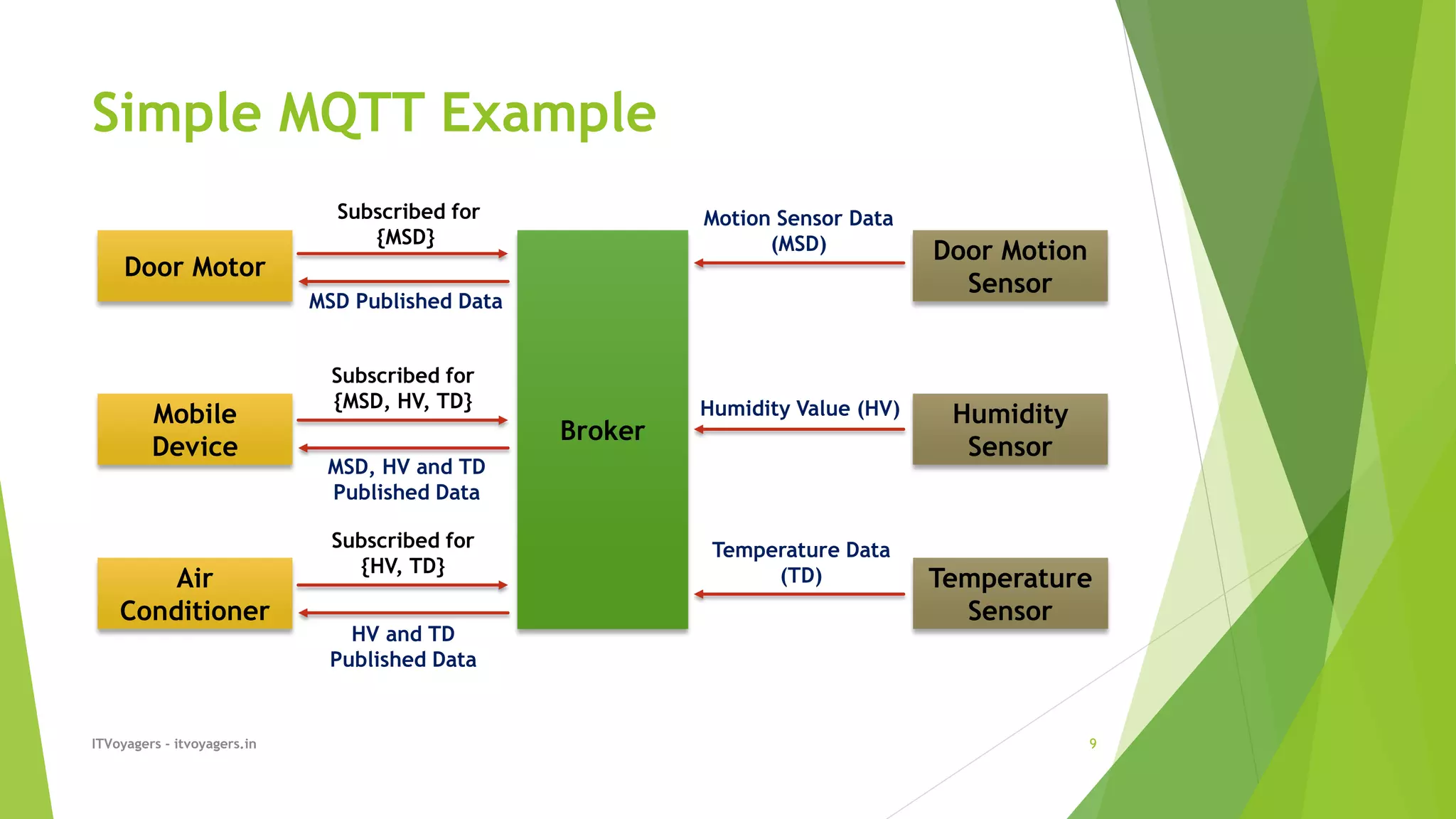
The document compares two protocols for machine-to-machine communication, MQTT and CoAP. MQTT operates on a publisher/subscriber model, allowing for efficient decoupling between data publishers and subscribers, while CoAP uses a client/server approach suitable for constrained networks. CoAP is designed for low power devices and supports features like UDP transmission and optimizations for data handling.






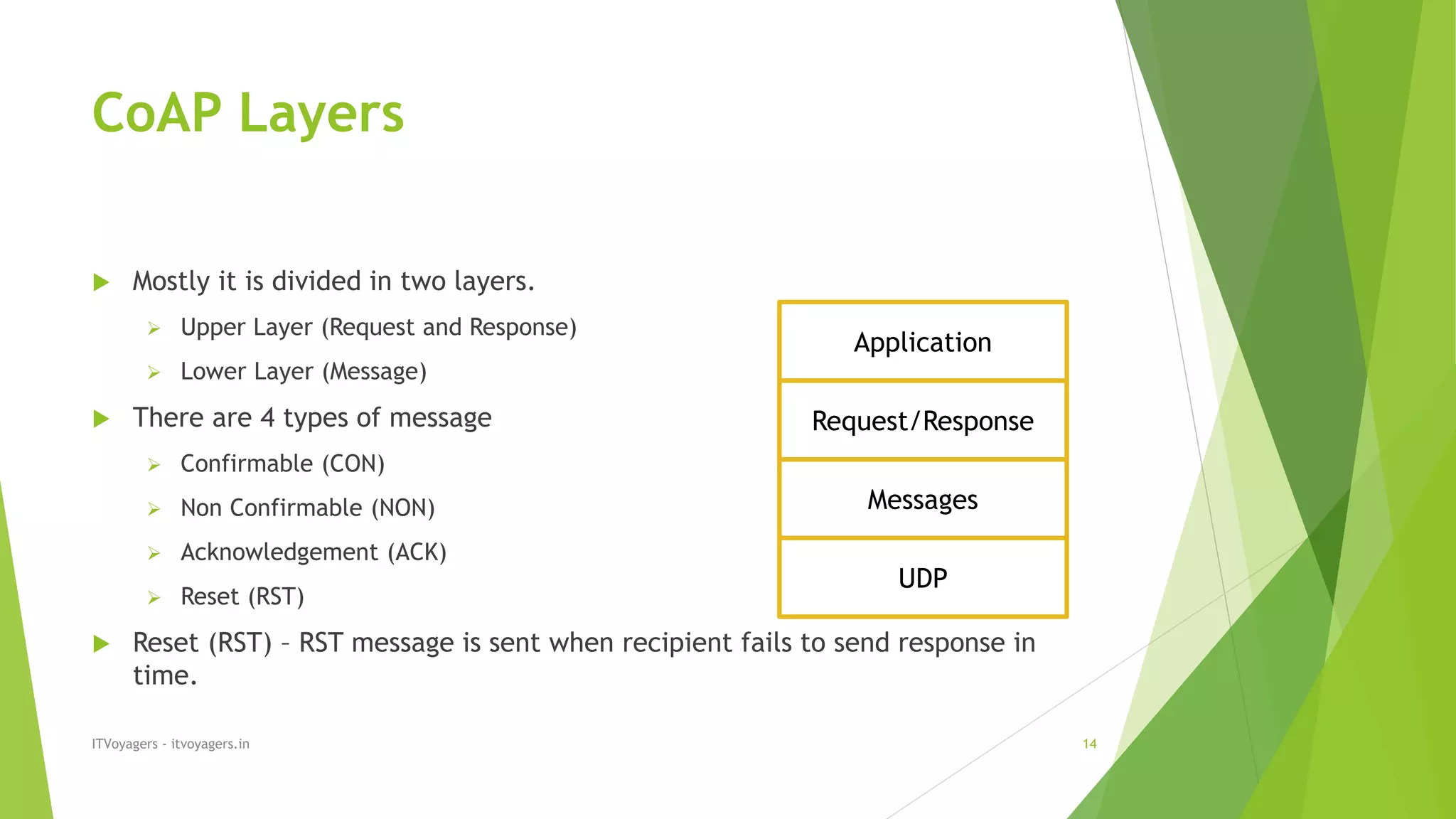

![COAP Header
ITVoyagers - itvoyagers.in 16
Credits : Wikipedia
VER (2 bits) – CoAP version.
Type (2 bits) – Type of messages [CON (0), NON (1), ACK (2), RST (3)]
Token Length (4 bits) – Indicates the length of variable
CoAP Request/Response Code (8 bits) – It has Request/Response code.
Message ID (16 bits) – Stores message ID which is use to detect message
duplication.](https://image.slidesharecdn.com/mqttandcoap-191001122353/75/MQTT-and-CoAP-16-2048.jpg)
