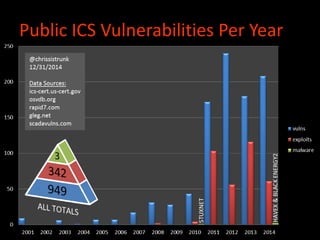
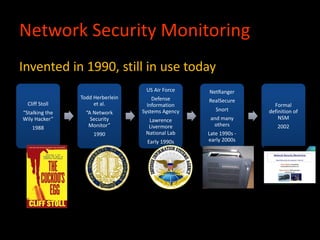
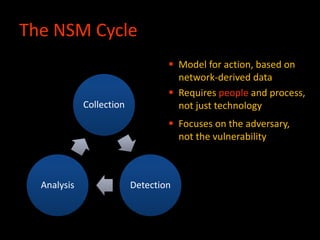
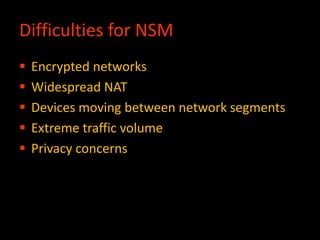
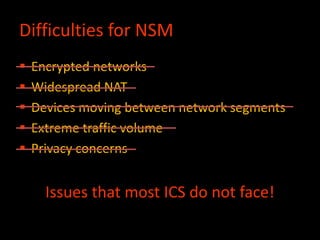
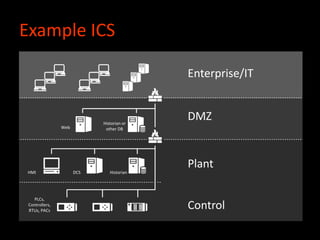
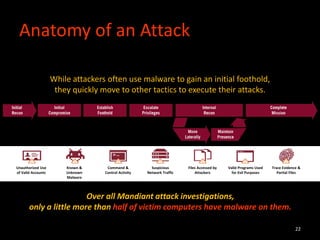
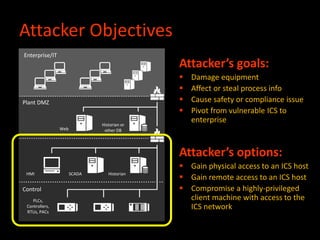
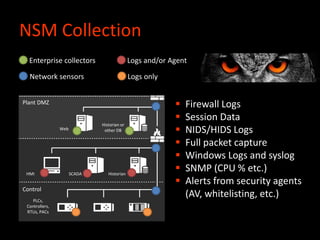
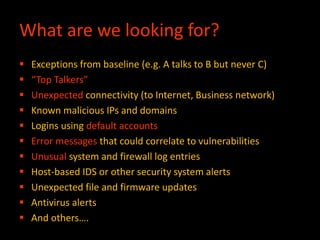
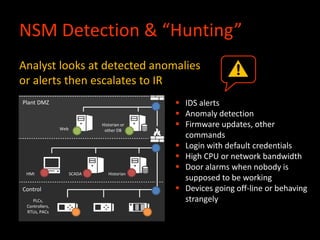
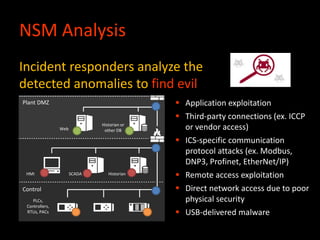
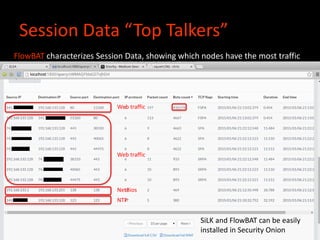
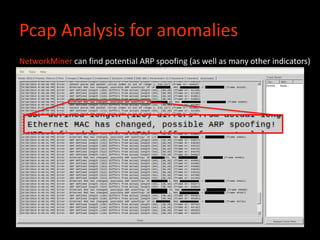
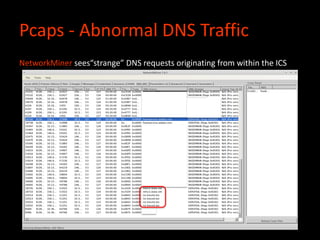
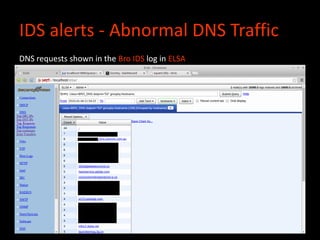
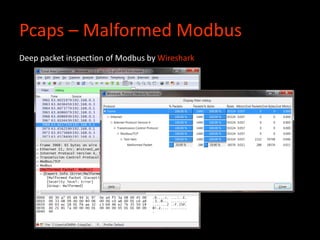
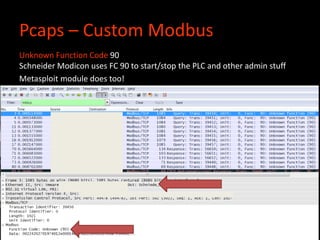
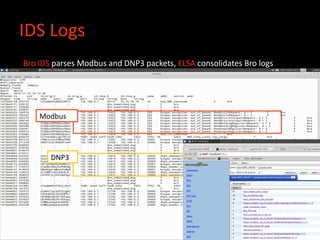
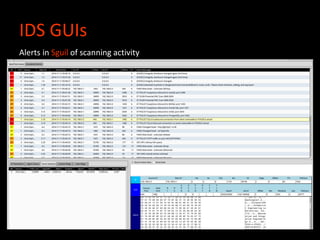
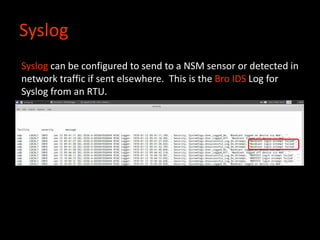
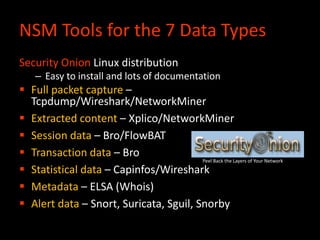
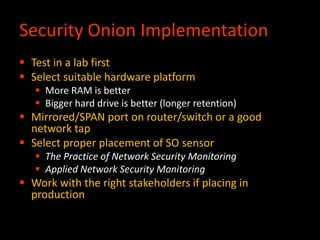
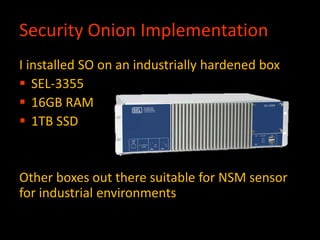
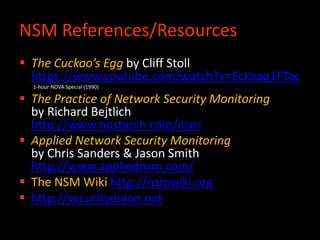
Chris Sistrunk discussed implementing network security monitoring (NSM) on industrial control systems (ICS). NSM involves collecting network data through tools like Security Onion, analyzing the data to detect anomalies, and investigating anomalies to identify potential threats. While ICS networks pose different challenges than typical IT networks, the same NSM methodology of collection, detection, and analysis can be applied. Free and open source tools like Security Onion allow implementing NSM on ICS to hunt for threats without disrupting operations. The most important part of NSM is having knowledgeable people to interpret data and identify what is normal versus potentially malicious activity on the network.