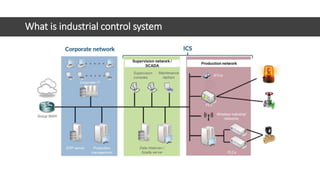
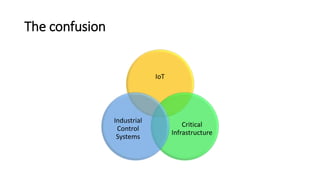
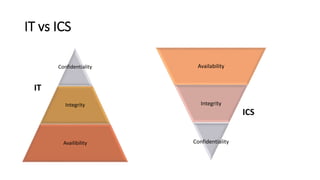
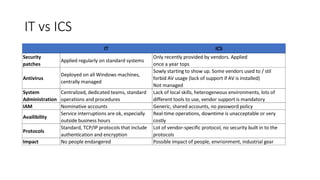
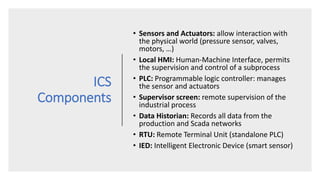
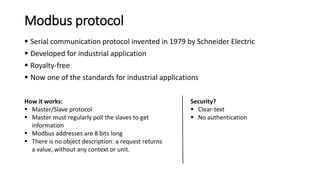
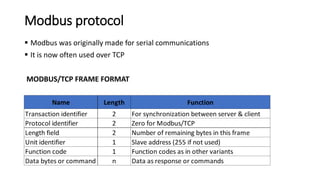
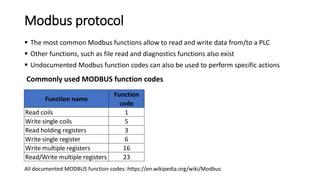
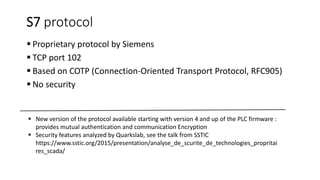
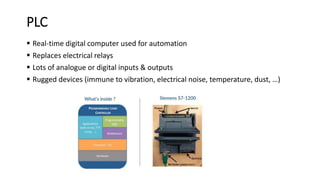
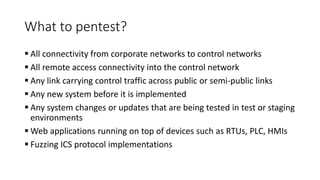
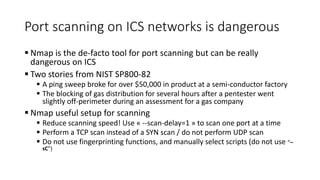
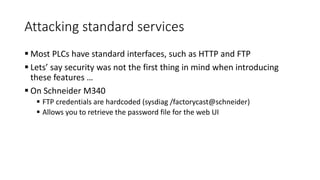
This document provides an overview of industrial control systems (ICS) security. It defines ICS and compares them to IT systems. Key differences include availability prioritization over confidentiality and integrity in ICS. The document outlines common ICS components like PLCs and protocols like Modbus. It also discusses common ICS security issues, penetration testing methodology, and approaches to securing ICS. Resources for learning more about ICS security are provided.