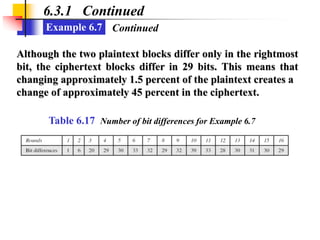
This document summarizes a chapter about the Data Encryption Standard (DES). It provides an overview of DES, describing it as a symmetric-key block cipher developed by IBM and adopted by the National Institute of Standards and Technology. The chapter then goes into details about the structure and design of DES, including its use of an initial and final permutation, 16 rounds of encryption using subkey values, and weaknesses like its short key length. It also discusses analyses of DES security, noting brute force, differential cryptanalysis, and linear cryptanalysis as potential attack methods.