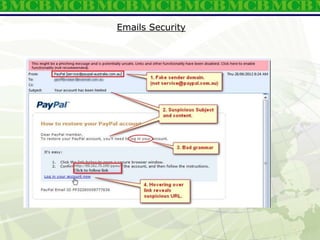
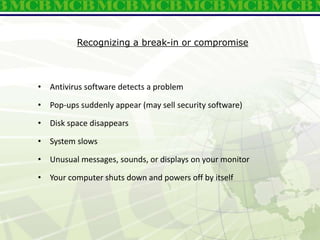
Cyber Security Awareness training outlines key topics to help employees secure MCB information systems and data from cyber attacks. The training covers password security, email security, safe web browsing, social engineering, and MCB security policies. Case studies of real-world cyber attacks show how hackers have stolen millions from banks by exploiting human and technical vulnerabilities. The training emphasizes that security is everyone's responsibility and all employees must follow security protocols to protect MCB networks and data.










![Use A Strong Password
• ATM PIN Code
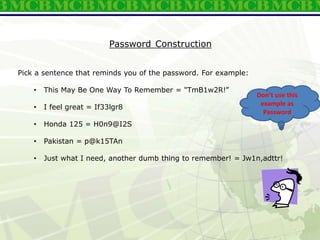
• Setting a Password (Total 95 Characters)
-10 digits: 0123456789
-26 lower case letters: abcdefghijklmnopqrstuvwxyz
-26 upper case letters: ABCDEFGHIJKLMNOPQRSTUVWXYZ
-33 special characters: `~!@#$%^&*()-_=+[]{}|;':",./<>?
• Two Factor Authentication
• One Time Password (OTP) E.g Whatsapp Login
• Never share your OTP with anyone](https://image.slidesharecdn.com/itsecurityawareness-v1-230413174238-5e7cba3c/85/IT-Security-Awareness-v1-7-ppt-13-320.jpg)