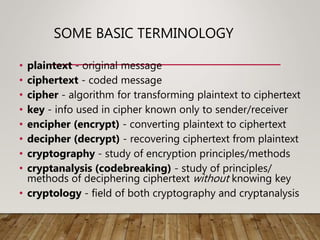
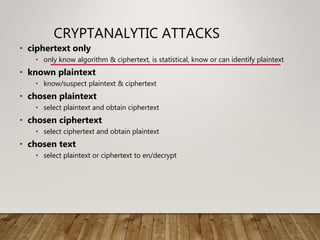
This document discusses classical encryption techniques including monoalphabetic substitution ciphers like the Caesar cipher and cryptanalysis using letter frequencies. It also covers the Playfair cipher, polyalphabetic ciphers like the Vigenère cipher, transposition ciphers, product ciphers combining multiple techniques, and steganography for hiding messages. Rotor machines like the Enigma machine are presented as early examples of complex ciphers before the development of modern cryptography.