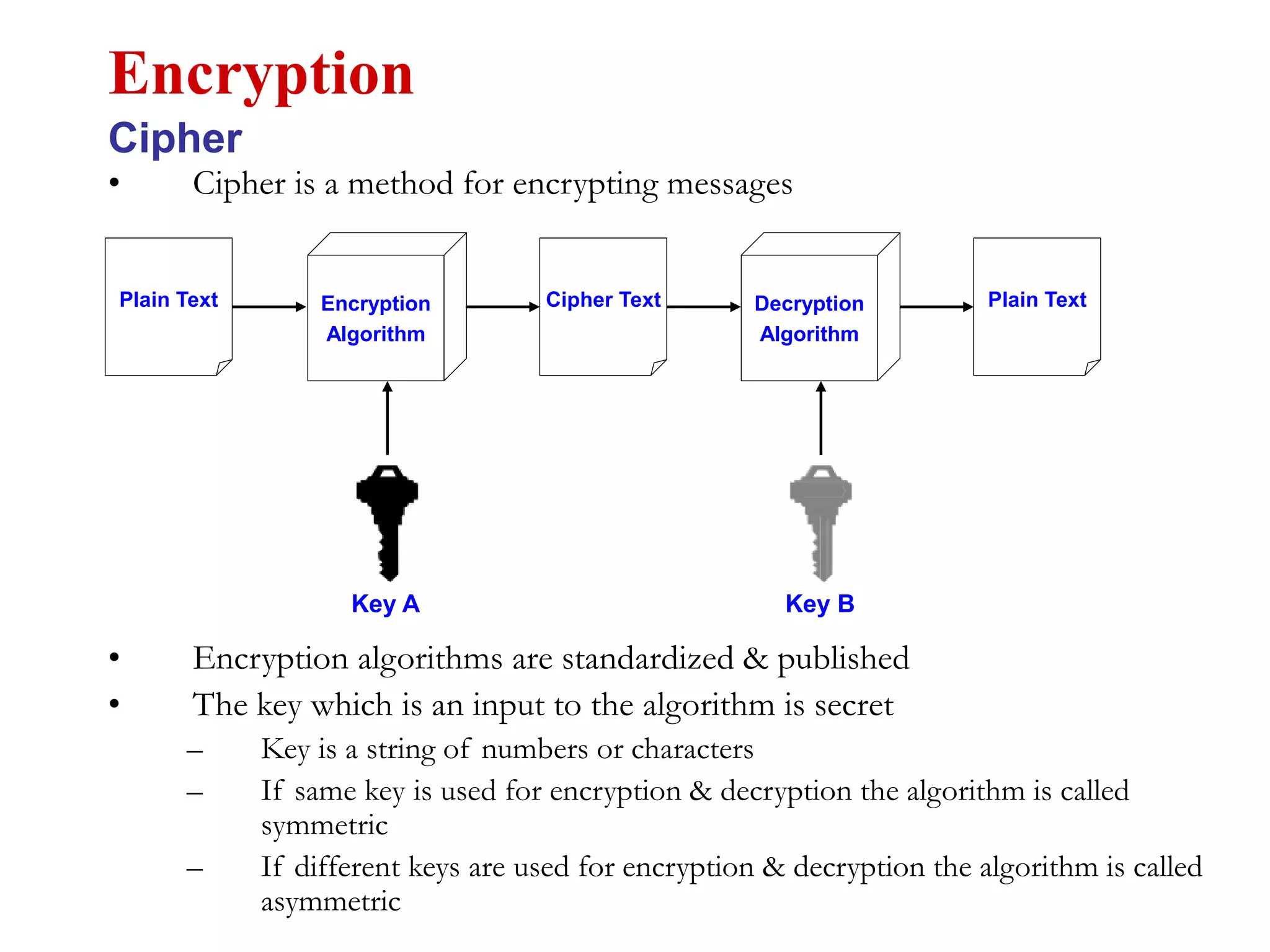
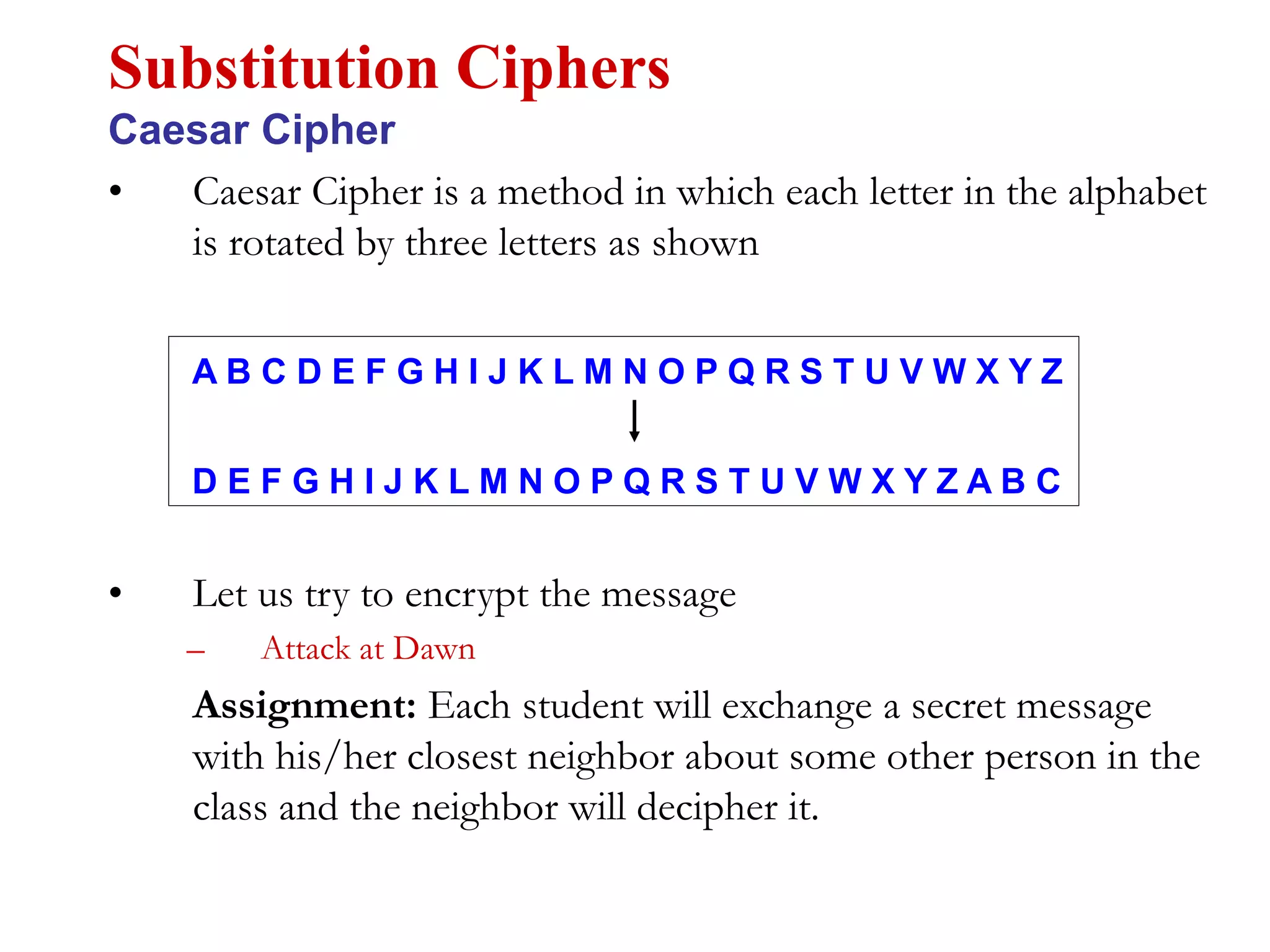
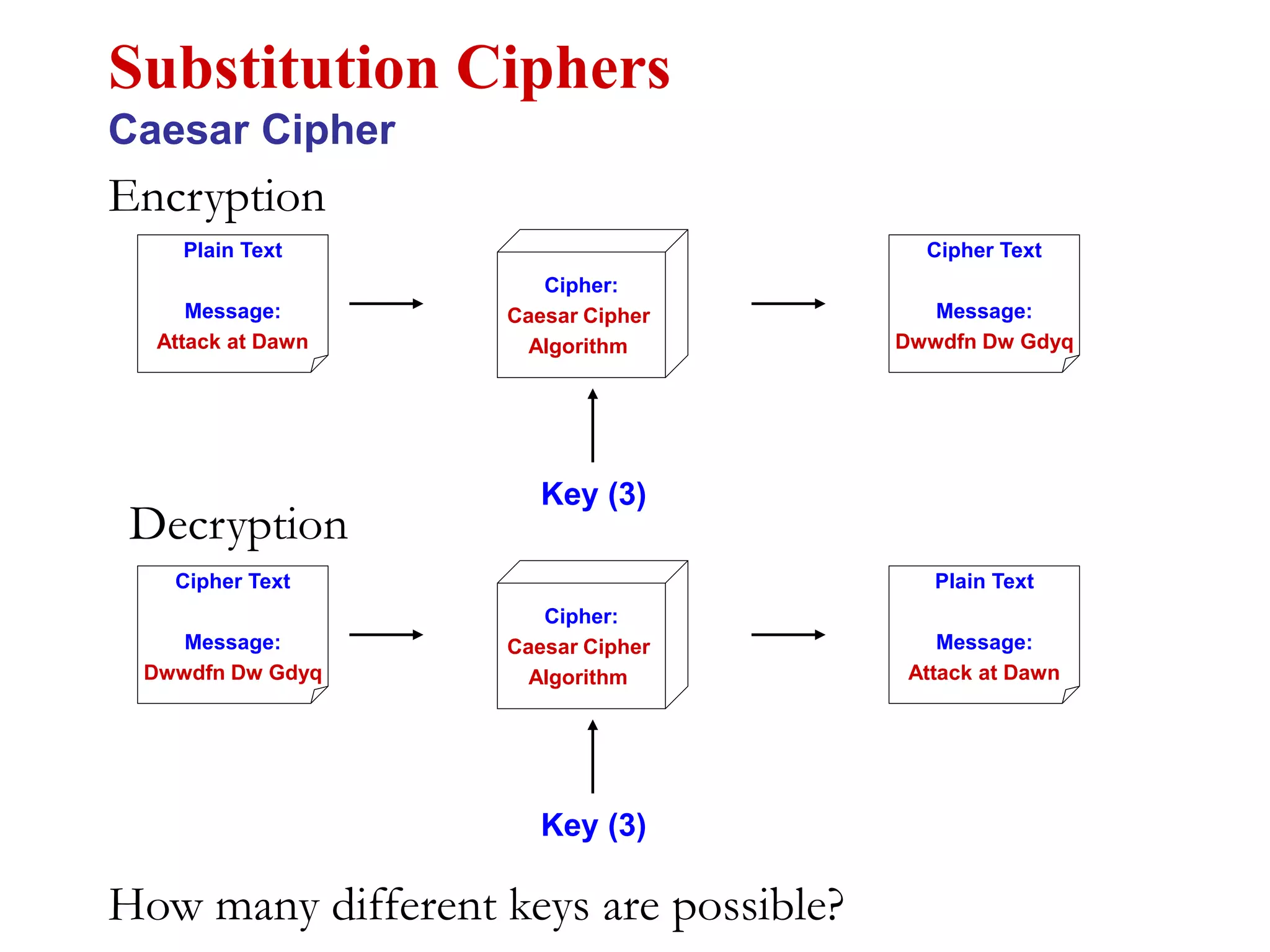
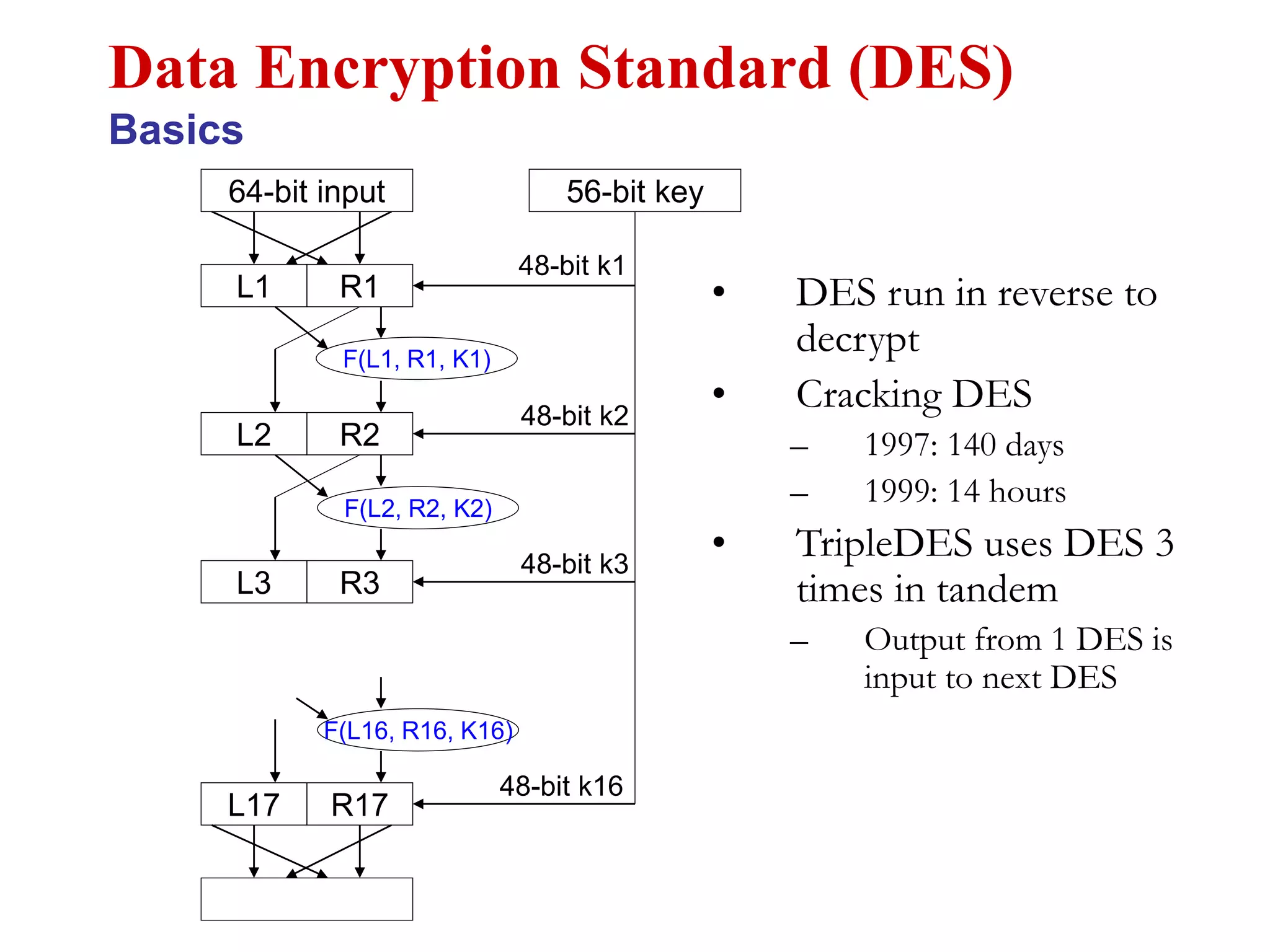
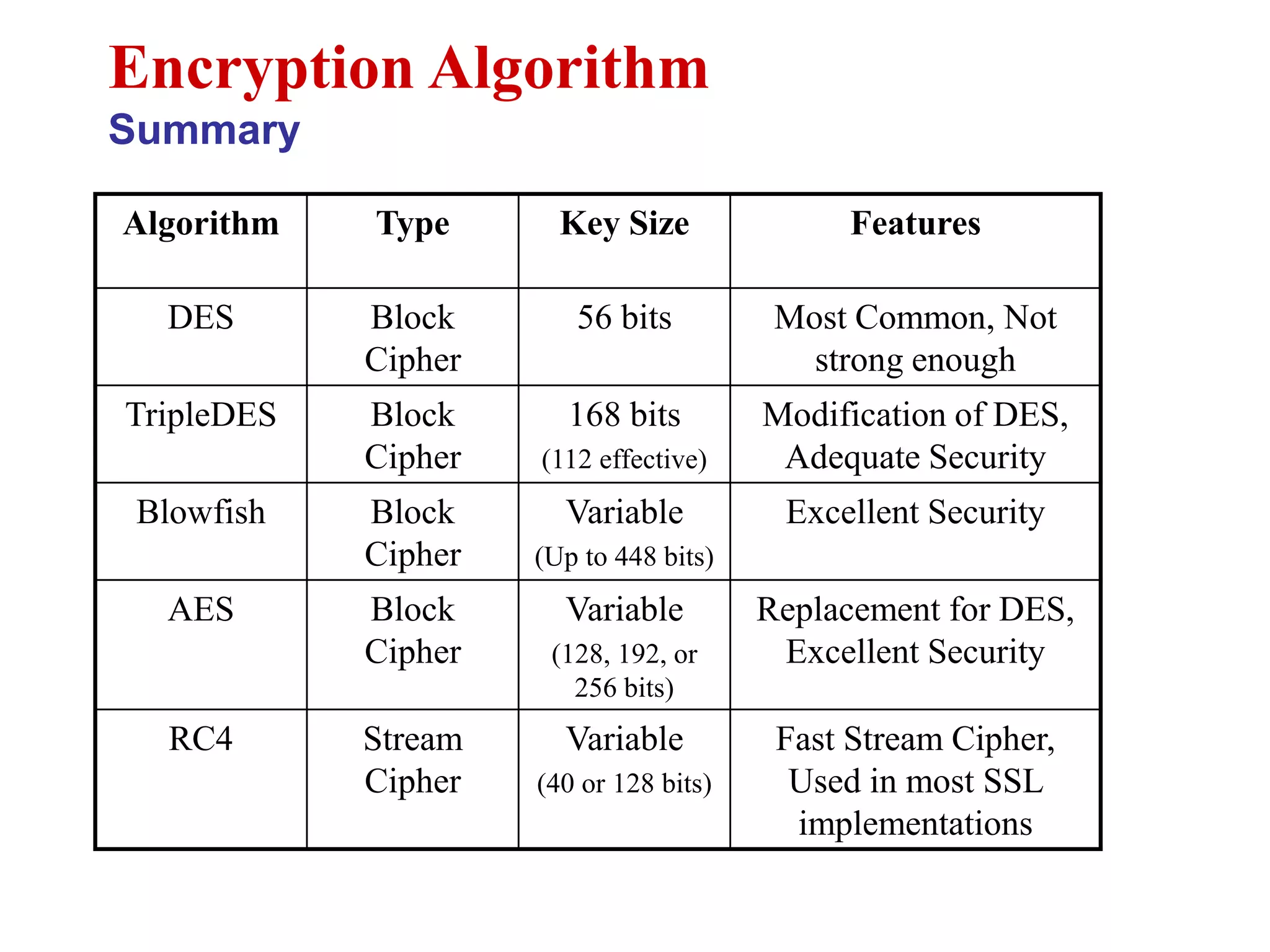
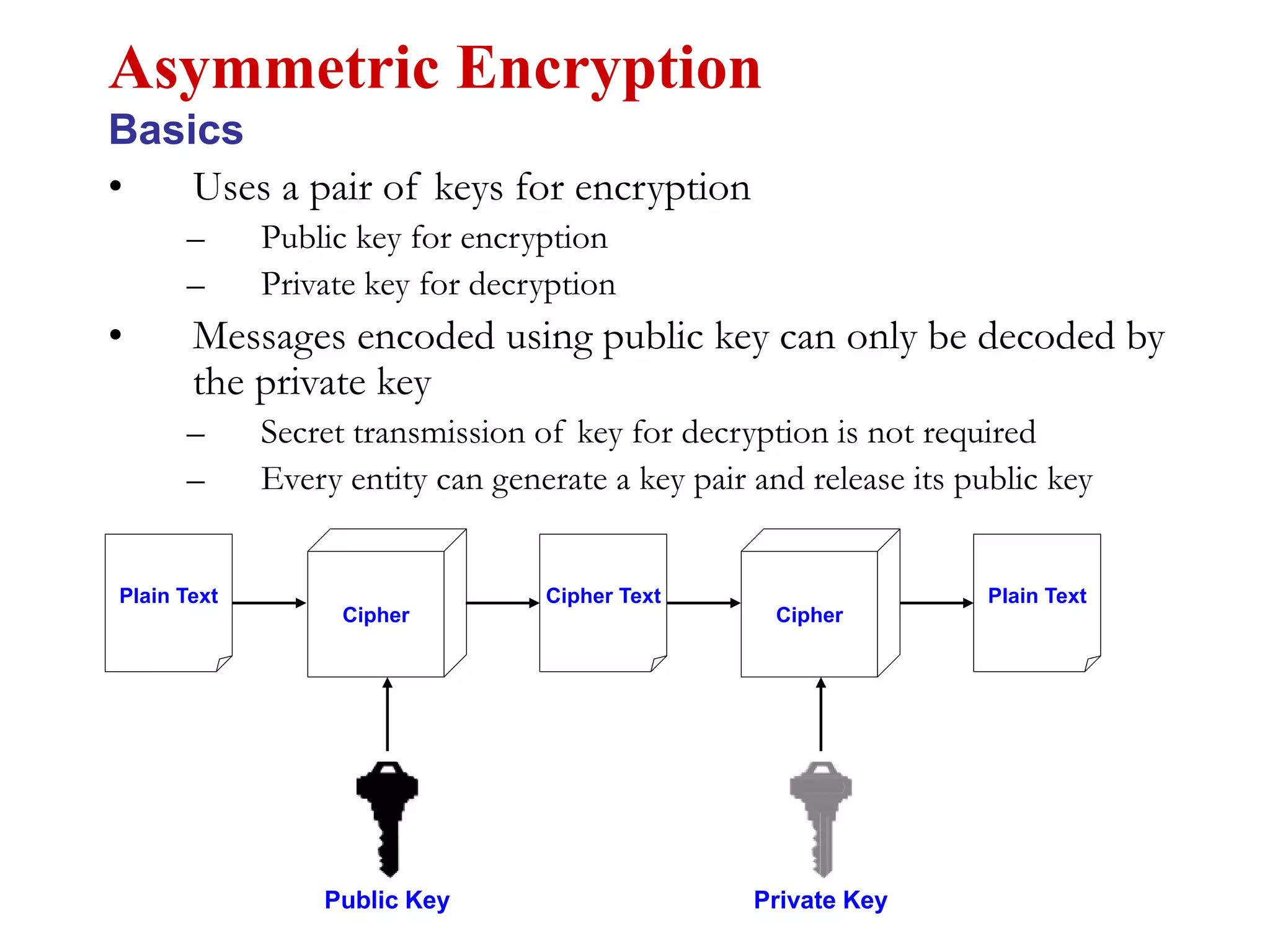
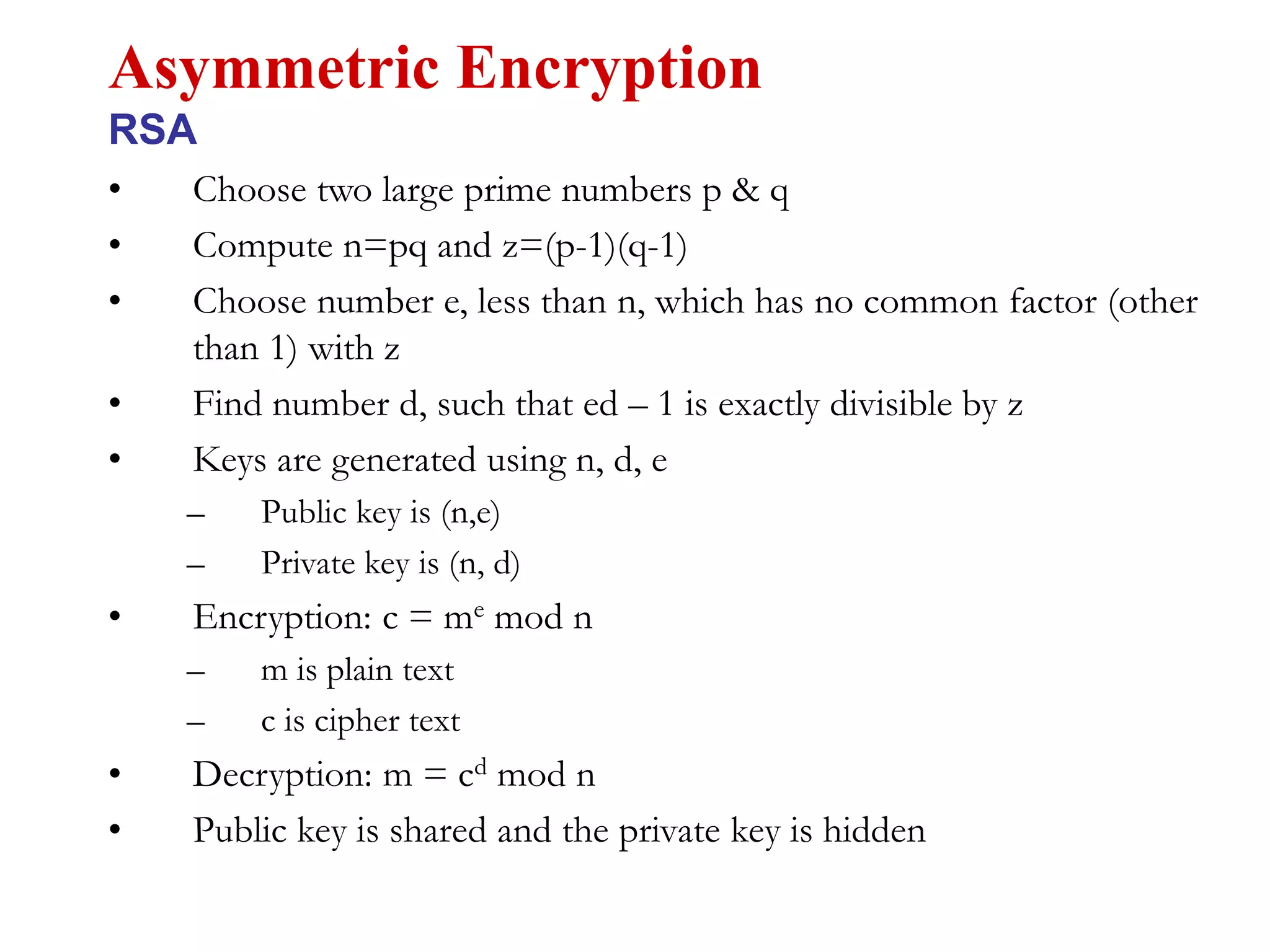
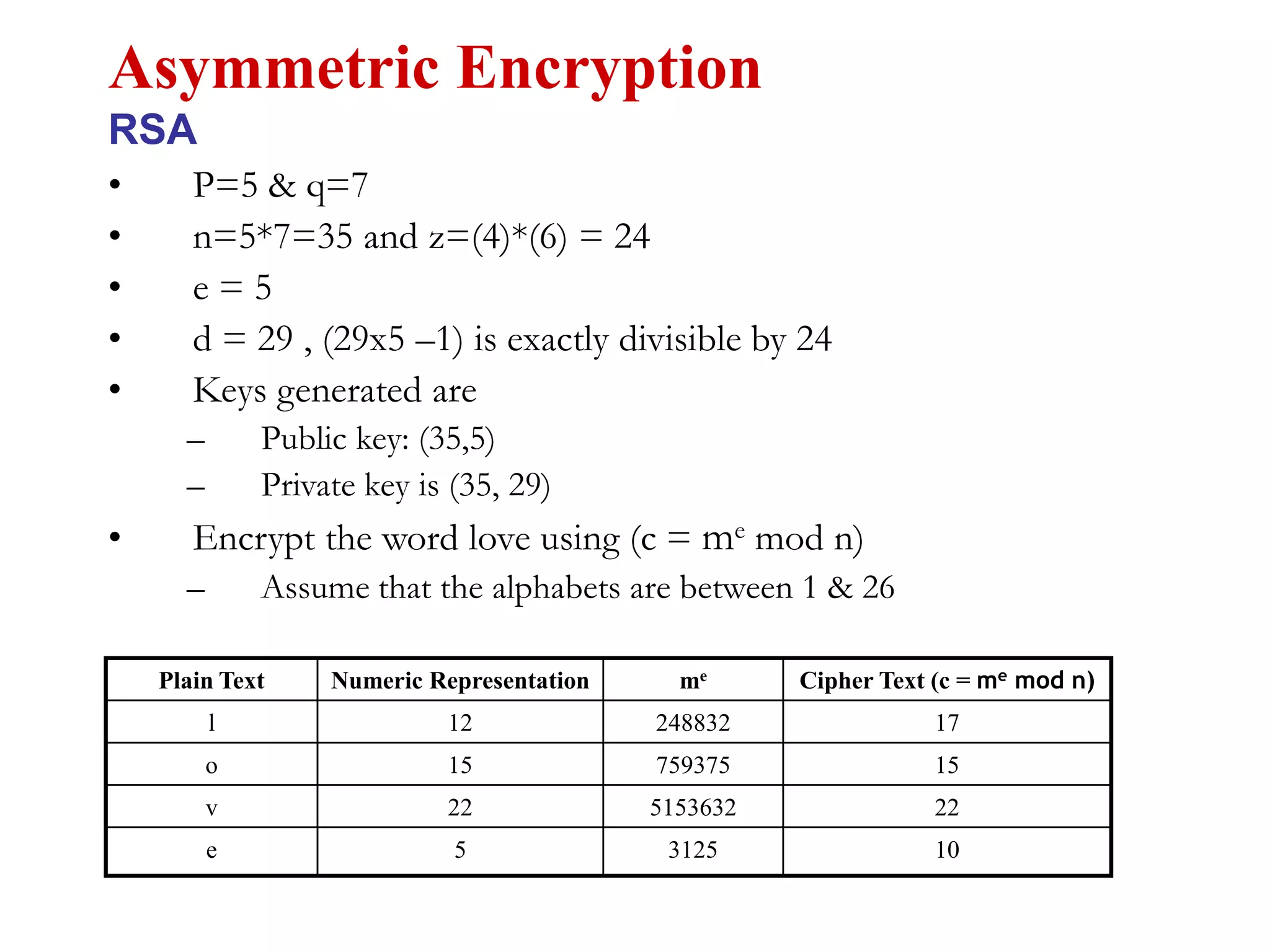
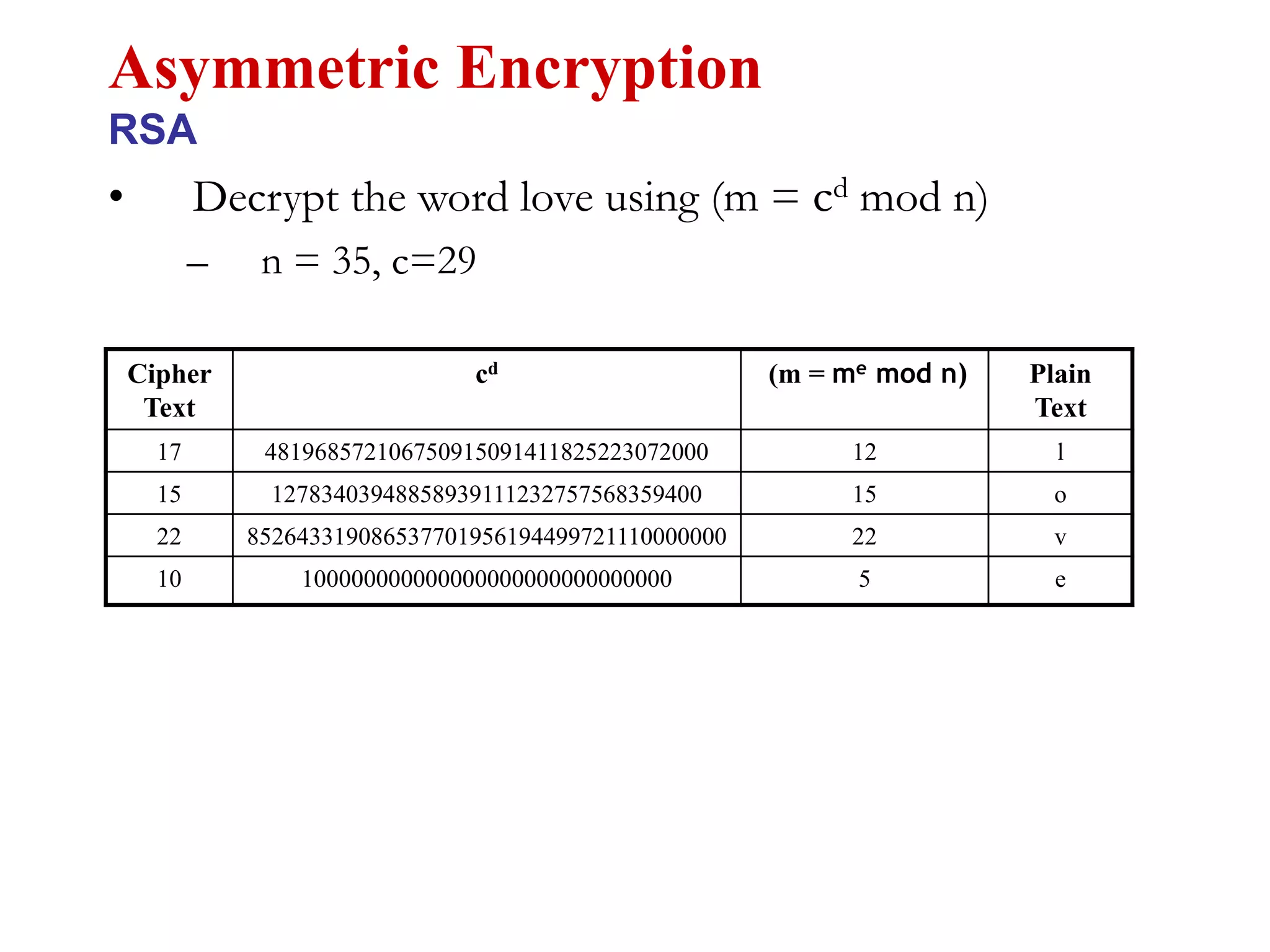
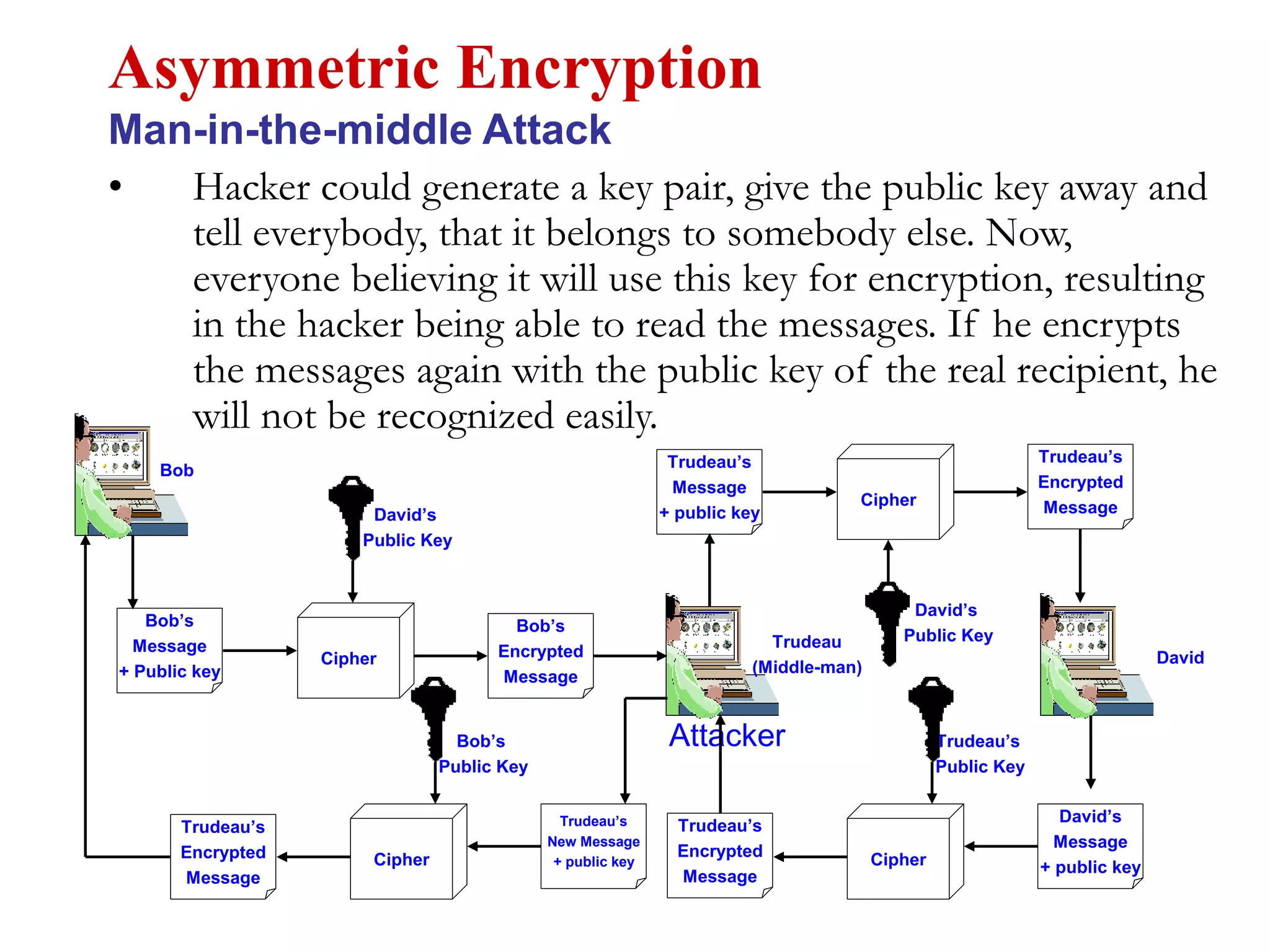
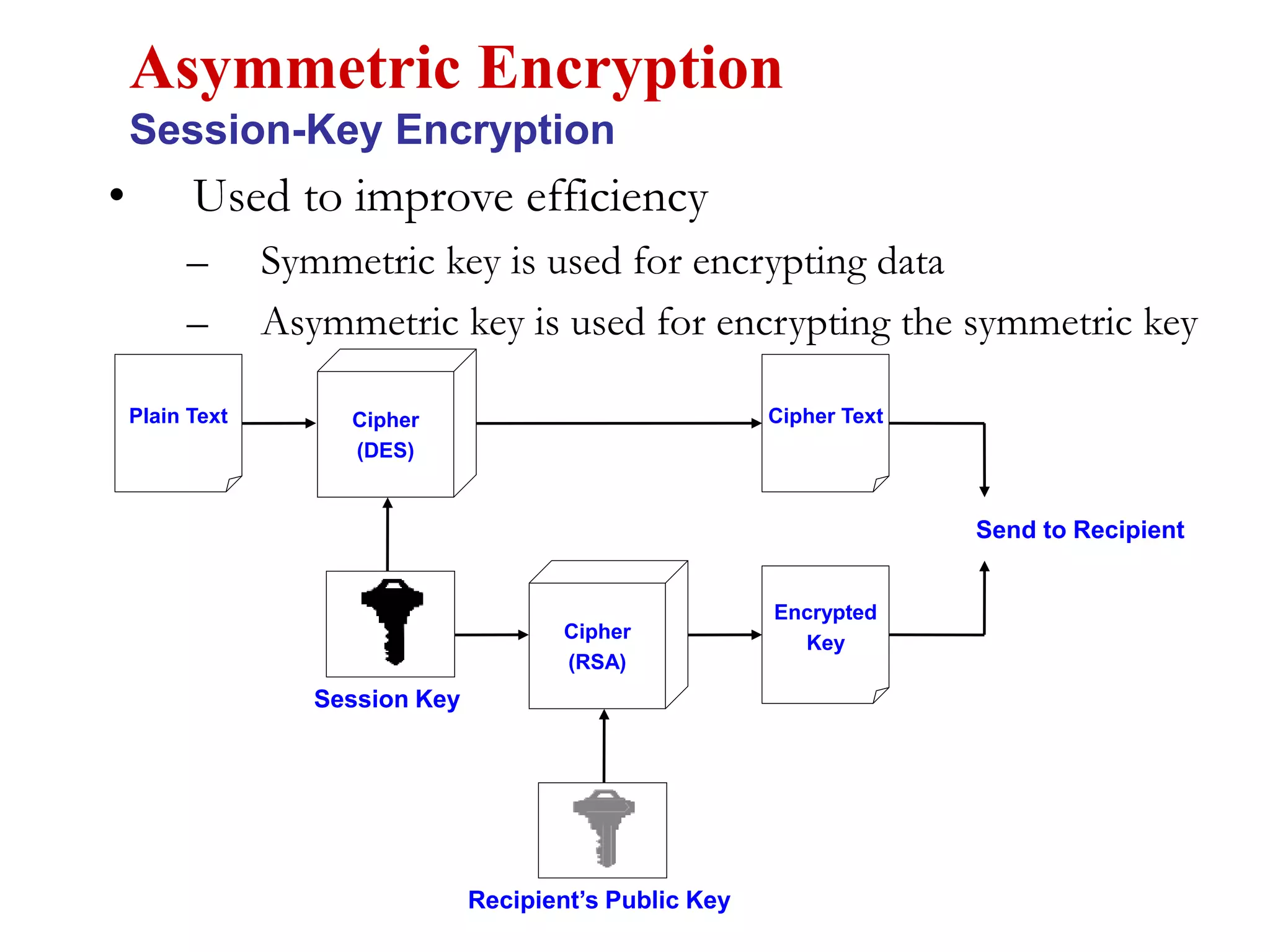
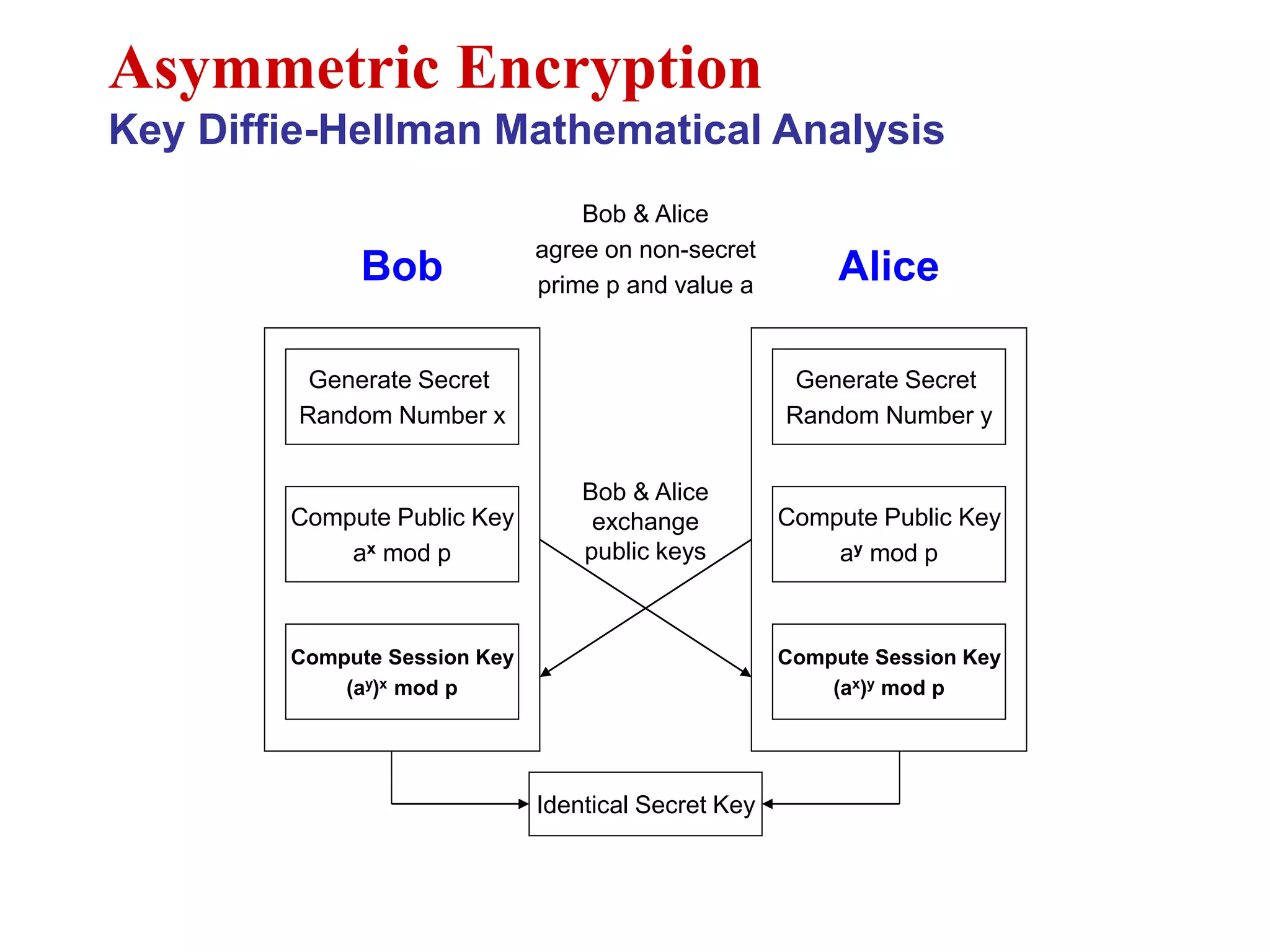
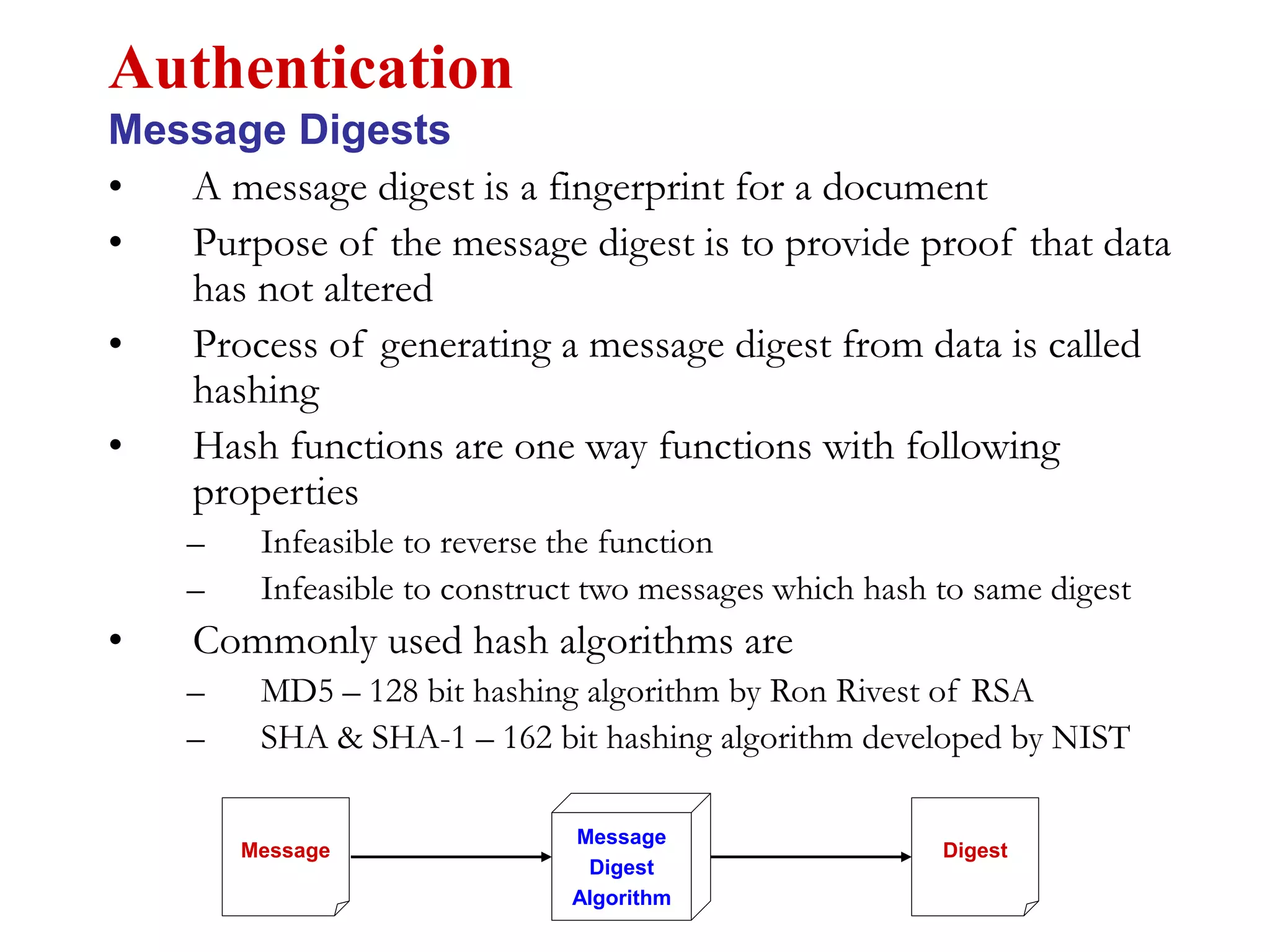
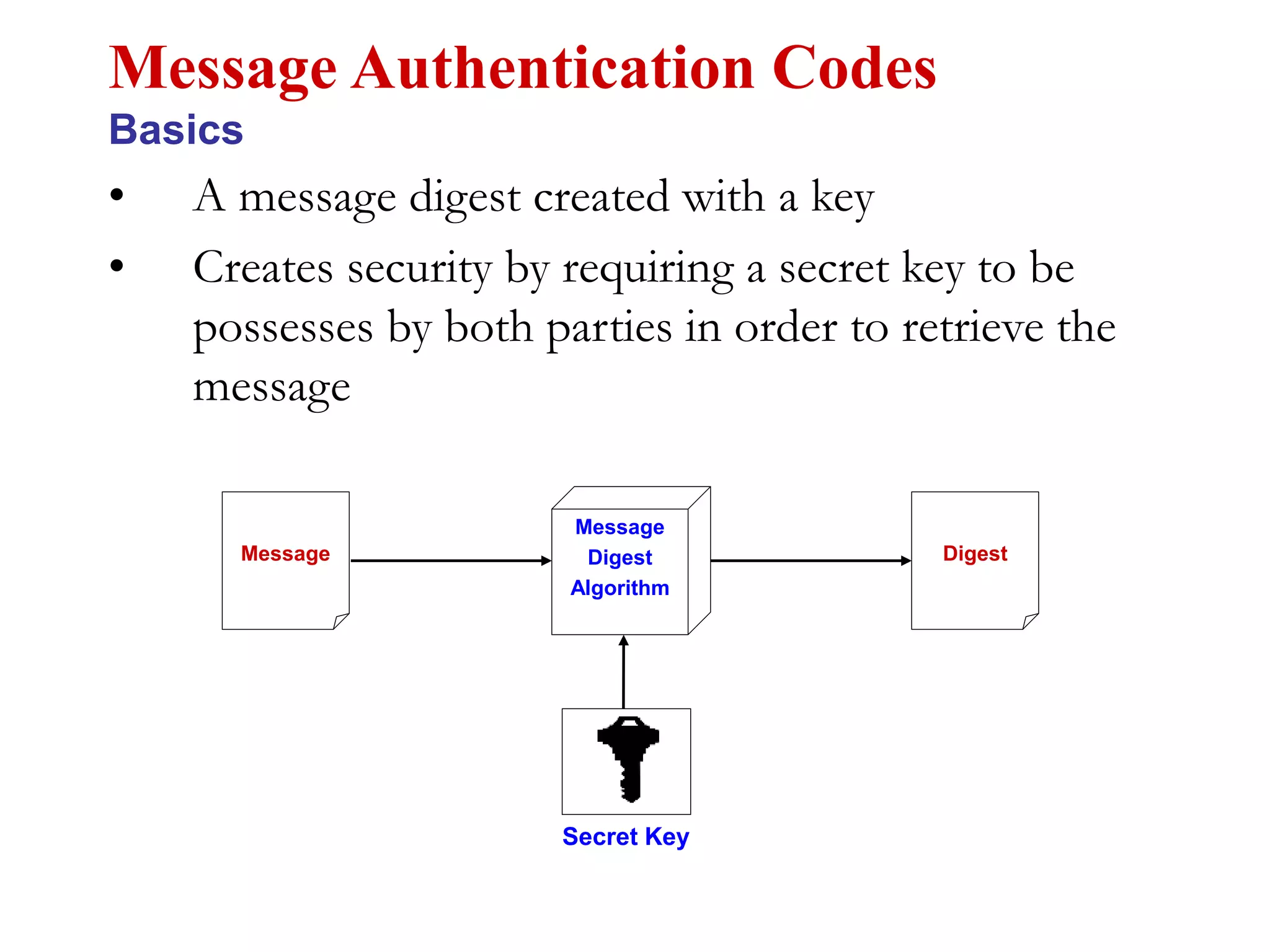
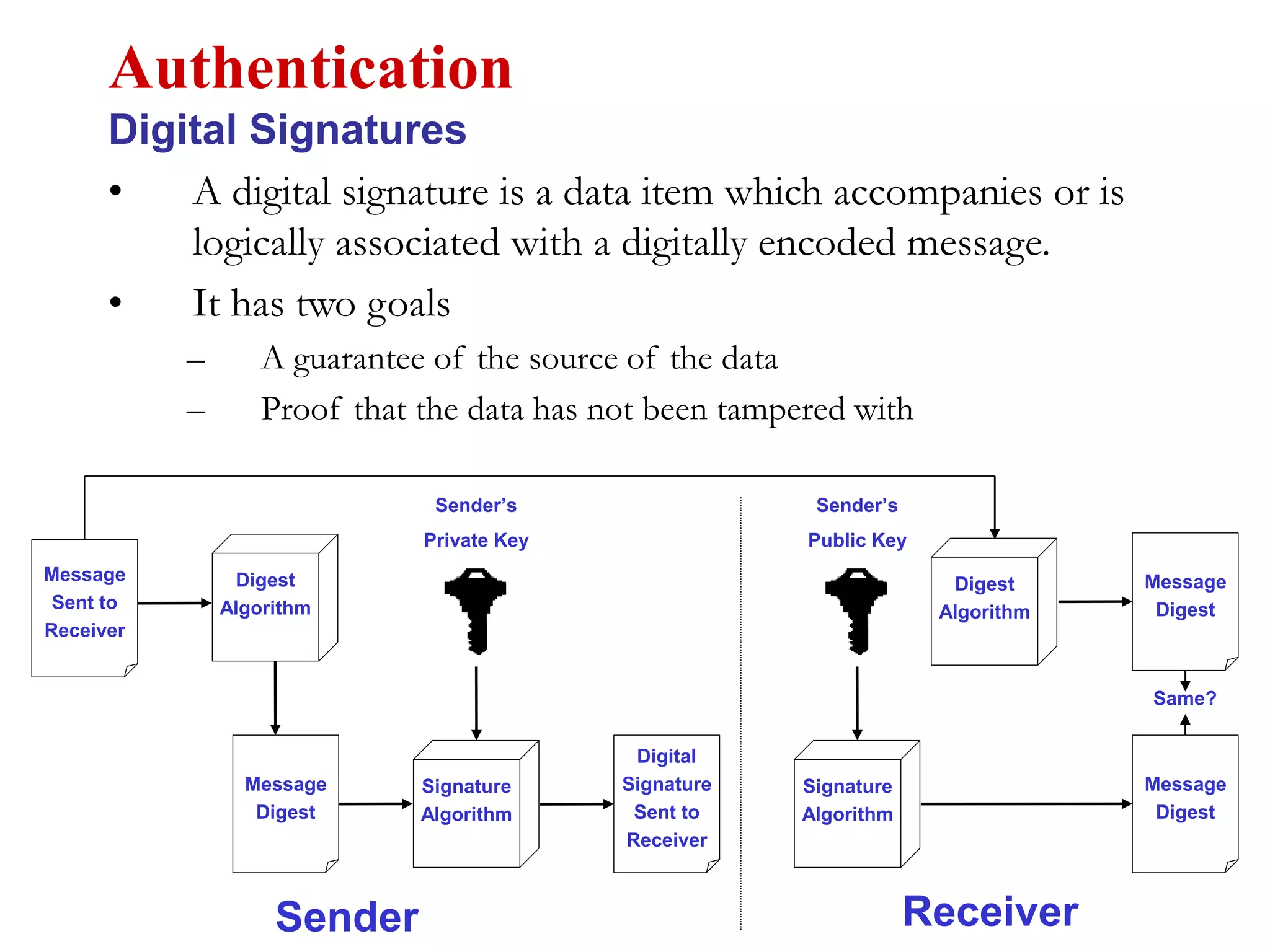
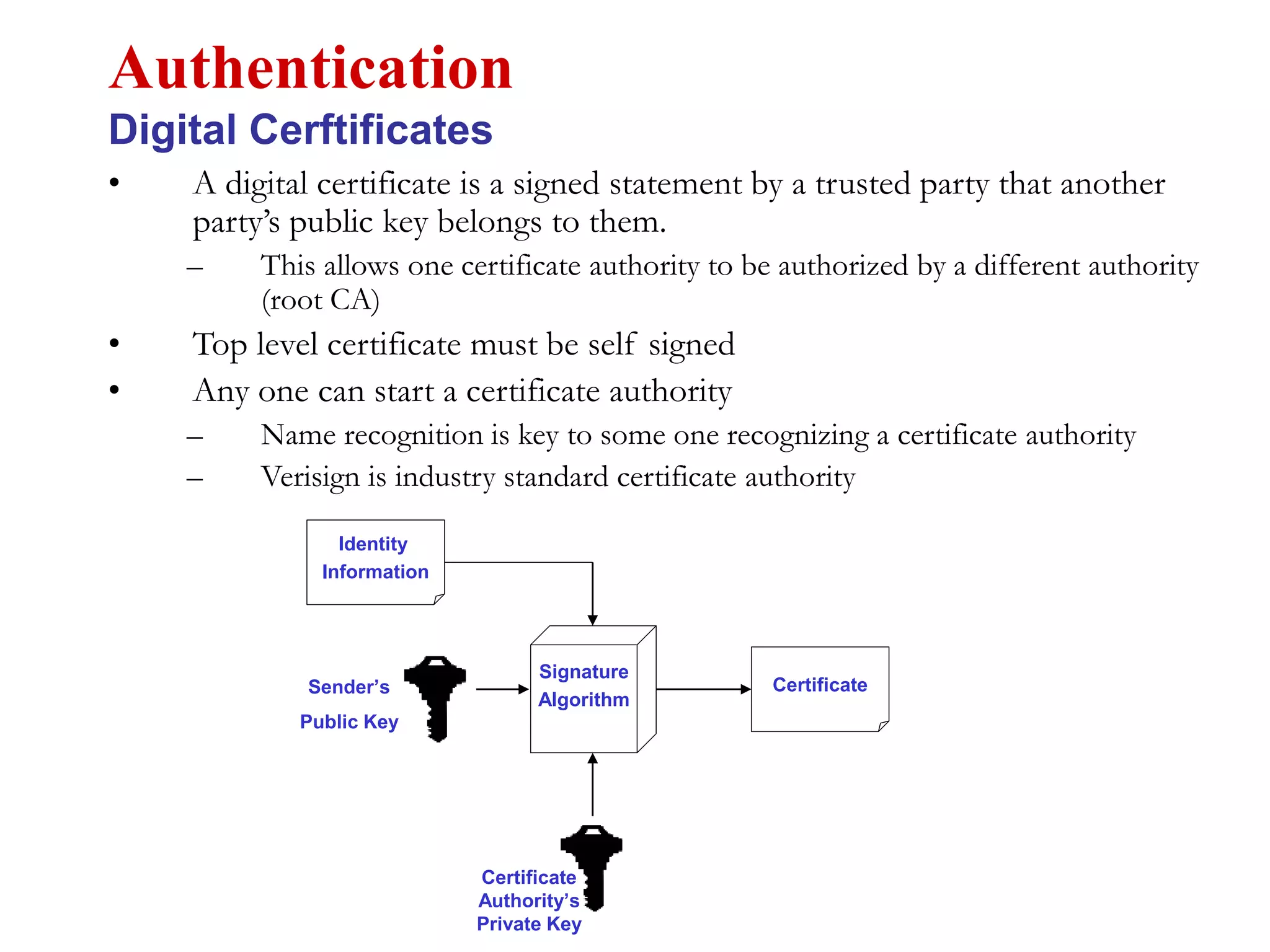
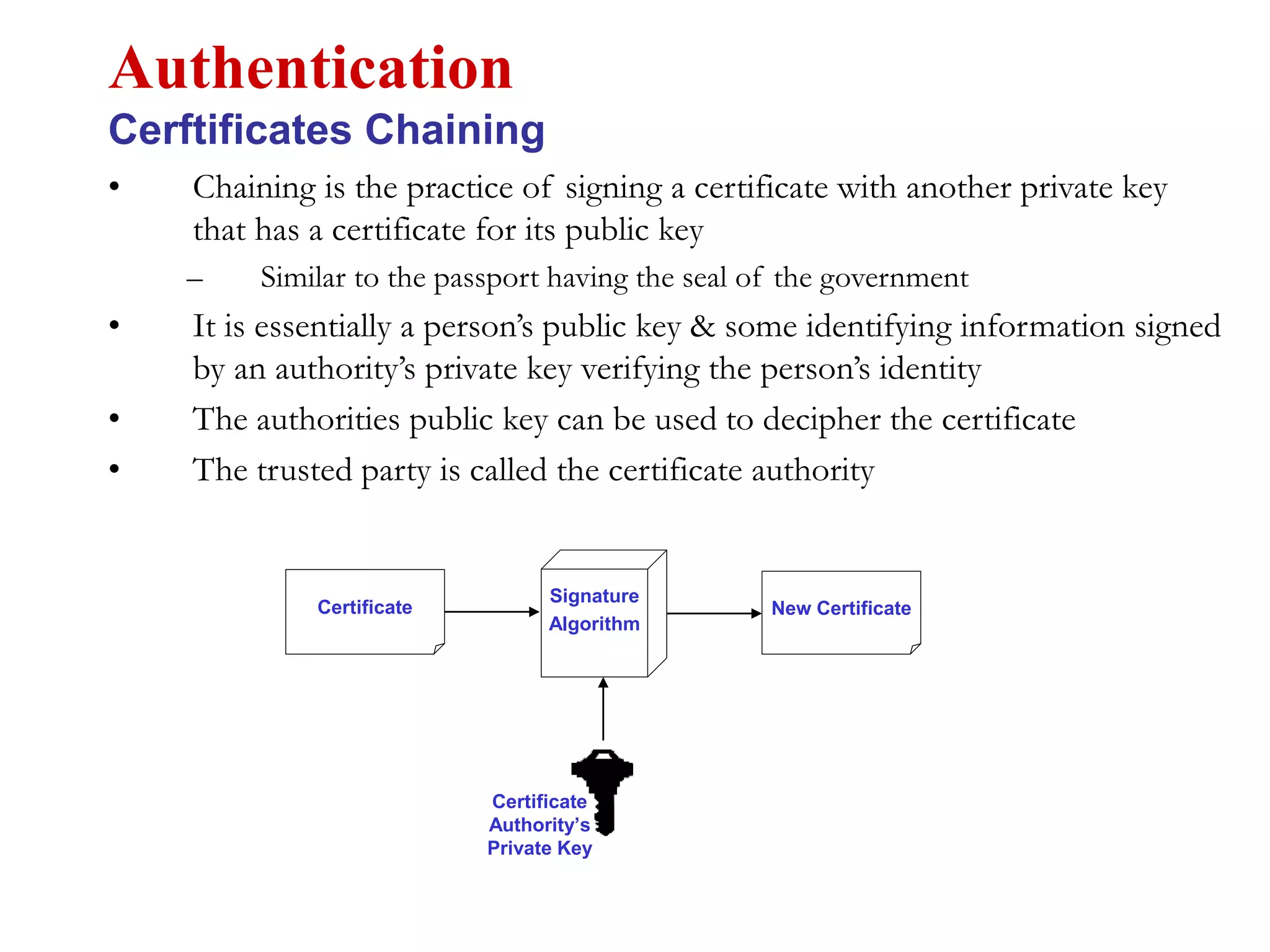
This document discusses computer security and cryptography. It covers the basics of cryptography including the needs for secure communication, encryption algorithms, symmetric and asymmetric encryption, encryption standards like DES and AES, cryptanalysis techniques, and authentication methods. It provides an overview of the key concepts and techniques in cryptography.