The document discusses various polyalphabetic ciphers including the Vigenere cipher, one-time pad cipher, Playfair cipher, and Hill cipher. It provides examples of encrypting and decrypting messages with the Vigenere cipher and Playfair cipher. The Vigenere cipher uses a keyword to shift the letters of a plaintext by various amounts, while the Playfair cipher encrypts pairs of letters based on their positions in a 5x5 grid generated from a keyword. The document also describes how the Hill cipher works by converting the plaintext and keyword into matrices and performing matrix multiplication to encrypt messages in blocks of letters.
![Computer Security & Networks
Dr. Saif Kassim Alfraije Page 1
Polyalphabetic Cipher
Leon Battista invented the Polyalphabetic Substitution Cipher in year 1568.
“Poly means Many in Greek language”. This method uses a mixed alphabet to
encrypt a message. The Enigma machine is more complex but still fundamentally a
polyalphabetic substitution cipher.
In polyalphabetic substitution, each occurrence of a character may have a different
substitute. The Polyalphabetic Cipher was adapted as a twist on the standard
Caesar cipher to reduce the effectiveness of frequency analysis on the ciphertext.
The polyalphabetic cipher uses a text string (for example, a word) as a key, which
is then used for doing a number of shifts on the plaintext.
Polyalphabetic Cipher Types
A. Vigenère Cipher
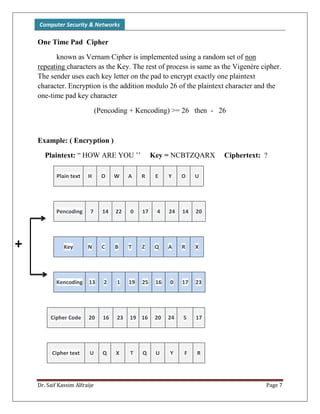
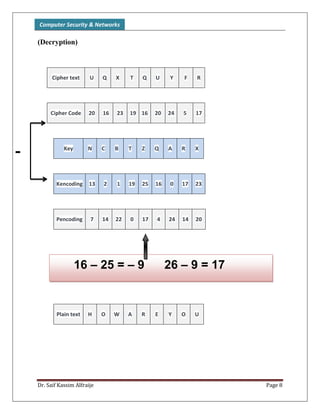
B. One Time Pad Cipher
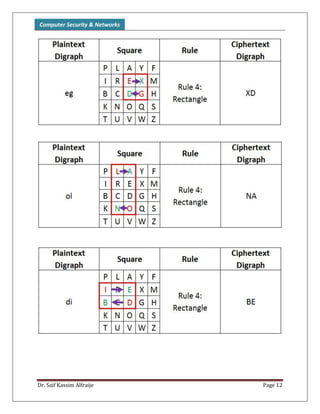
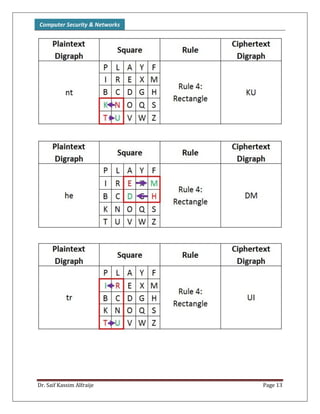
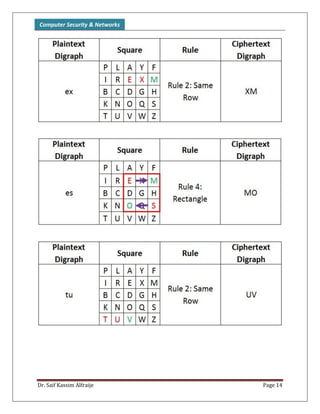
C. Playfair Cipher
D. Hill Cipher
Vigenere cipher
One such cipher is the famous Vigenere cipher, the Vigenere cipher uses
the power of 26 possible shift ciphers. A tool that was used for the Vigenère
Cipher was a (code wheel) or (Keyword). Vigenere cipher shifts the characters in a
string by some places. Now those some places are determined by the characters
that are present in the key string.
P=P1P2P3…… C=C1C2C3…….. k=[(K1,K2,….. , KM), (K1,K2,….. , KM),..]
Encryption : Ci = Pi + Ki Decryption : Pi = Ci - Ki](https://image.slidesharecdn.com/chapter03-151121204704-lva1-app6891/75/Computer-Security-Cryptography-Ch03-1-2048.jpg)