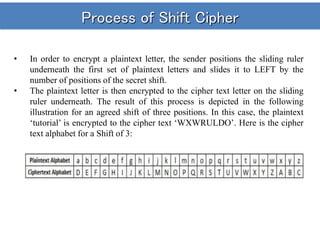
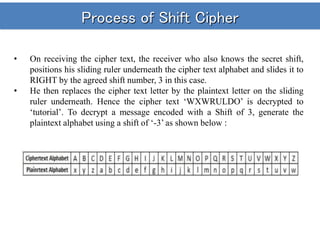
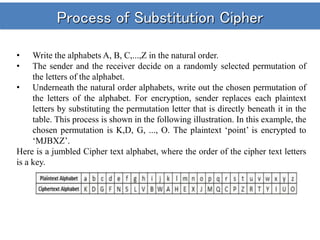
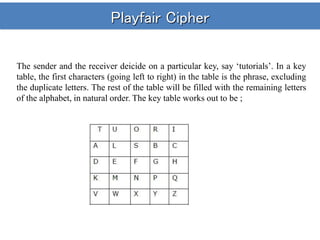
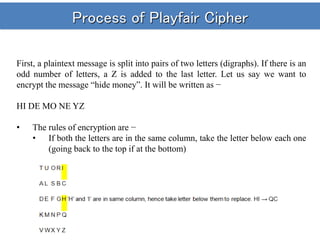
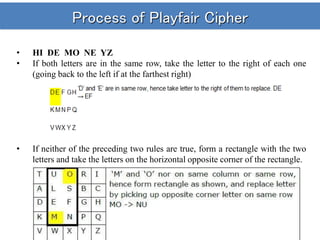
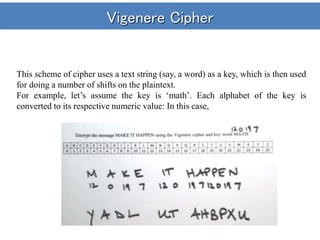
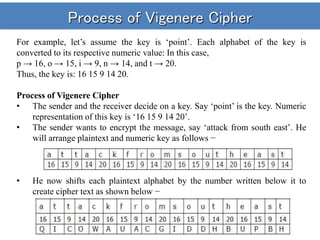
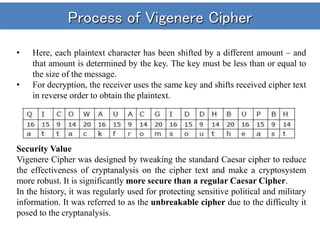
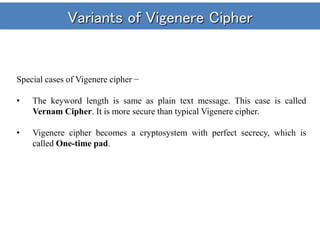
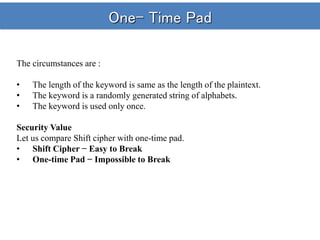
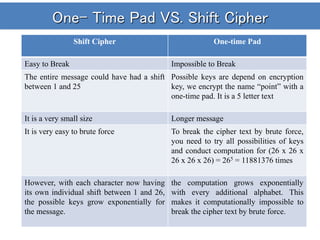
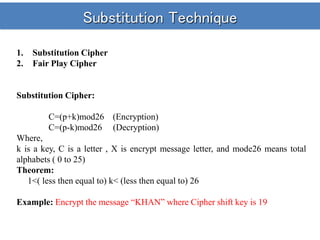
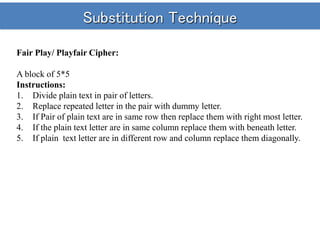
The document provides information on various historical cryptosystems and ciphers, beginning with a brief overview of symmetric and asymmetric key encryption. It then discusses several manual ciphers such as the Caesar cipher, simple substitution cipher, Playfair cipher, and Vigenere cipher. The Caesar cipher performs monoalphabetic substitution by shifting letters of the alphabet. The simple substitution cipher and Playfair cipher improve security by using permutation or paired letter substitution instead of just shifting. The Vigenere cipher further enhances security by applying multiple Caesar shifts using a keyword. The document also covers the one-time pad cipher and its information theoretic security if the pad is truly random and never reused.