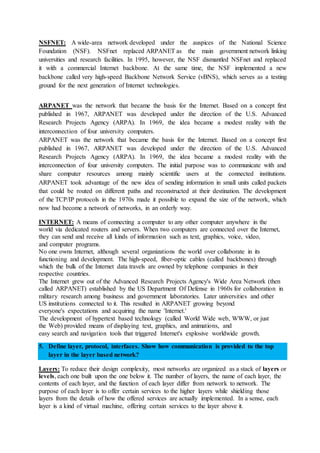
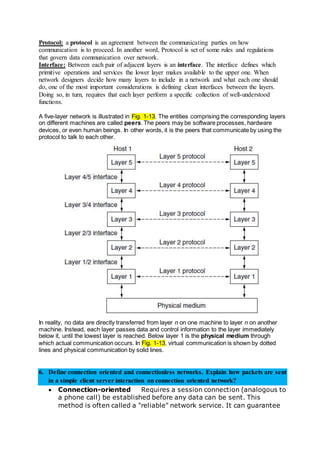
The document discusses computer networks and the data link layer. It provides classifications of computer networks including PAN, LAN, MAN and WAN. It discusses the goals of computer networks which include resource sharing, reliability, cost savings, performance and communication. It then discusses point-to-point subnets and their possible topologies. Finally, it discusses the services provided by the data link layer, including encapsulation, frame synchronization, error control and logical link control.




![9. What is error control? Error correction and detection using hamming code (odd/ even
parity for the given code).
Error control (automatic repeat request, ARQ), in addition to ARQ provided by some transport-
layer protocols, to forward error correction (FEC) techniques provided on the physical, and to
error-detection and packet canceling provided at all layers, including the network layer. Data-
link-layer error control (i.e. retransmission of erroneous packets) is provided in wireless
networks and V.42 telephone network modems, but not in LAN protocols such as Ethernet,
since bit errors are so uncommon in short wires. In that case, only error detection and canceling
of erroneous packets are provided.
10. Name and define the fields of Ethernet frame format.
A data packet on the wire and the frame as its payload consist of binary data. Data on Ethernet
is transmitted with most-significant octet (byte) first; within each octet, however, the least-
significant bit is transmitted first, except for the frame check sequence (FCS).
The internal structure of an Ethernet frame is specified in IEEE 802.3-2012.[1]
The table below
shows the complete Ethernet frame, as transmitted, for the payload size up to the MTU of 1500
octets. Some implementations of Gigabit Ethernet (and higher speed Ethernets) support larger
frames, known as jumbo frames.](https://image.slidesharecdn.com/computer-network-solution-160214182226/85/Computer-network-solution-9-320.jpg)