The document provides an introduction to computer networks, including:
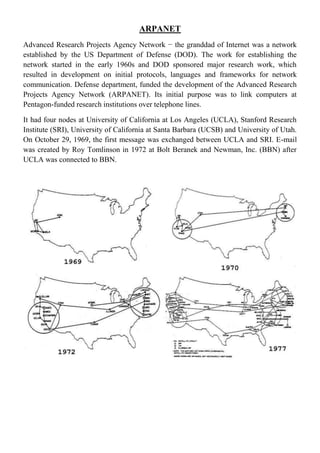
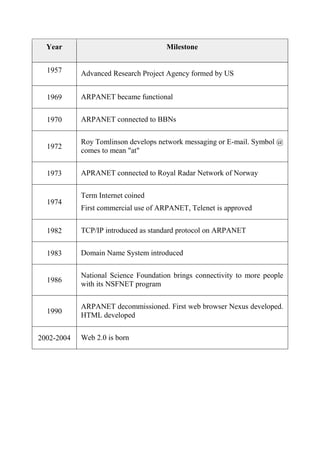
- ARPANET was the first network established by the US Department of Defense in the 1960s to connect research institutions over telephone lines.
- Key milestones include the development of email in 1972 and the introduction of TCP/IP as the standard protocol in 1982.
- Computer networks allow for resource sharing, high reliability, and flexible access across connected devices through hardware like routers and switches, transmission media, and network protocols.