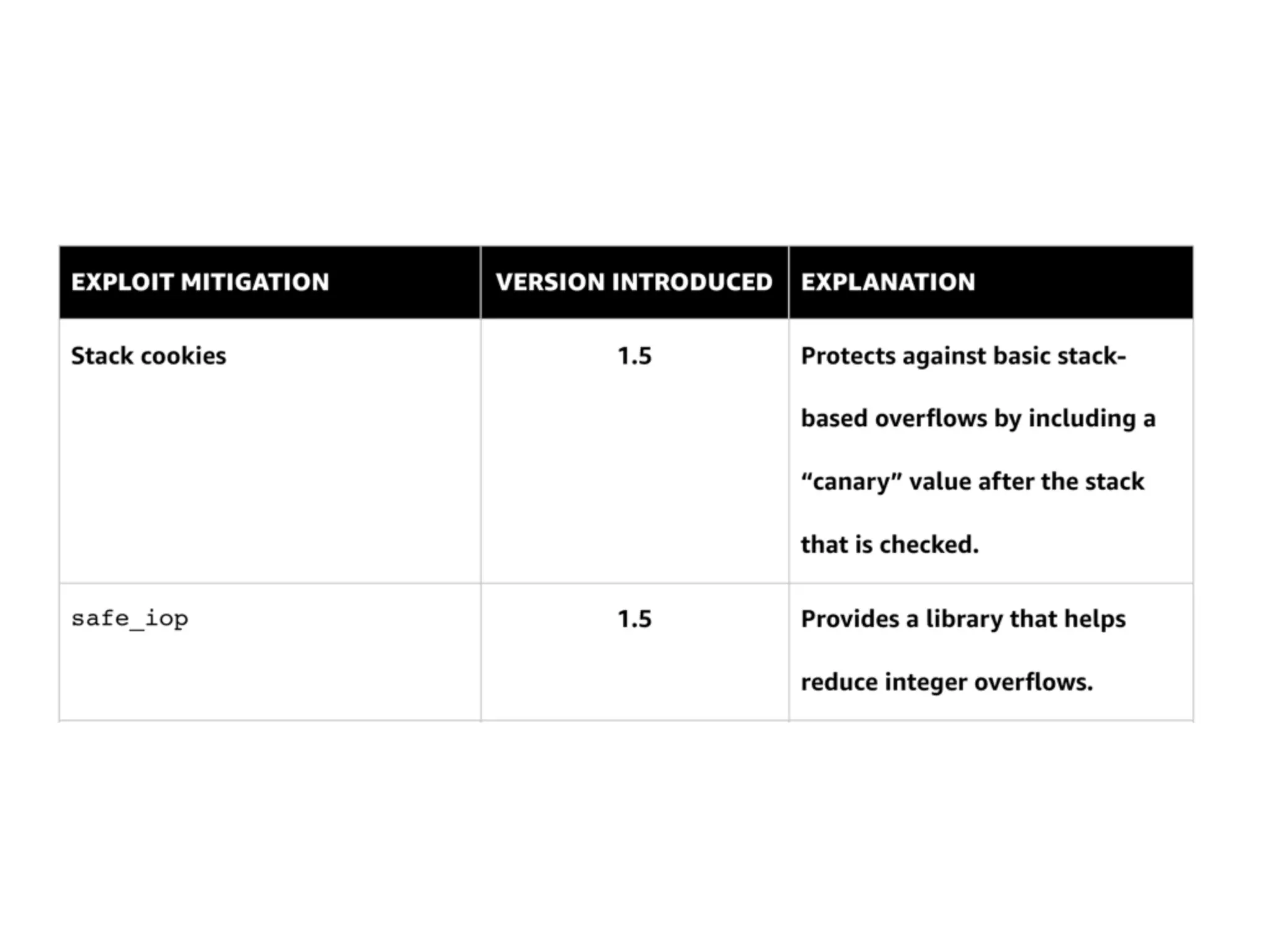
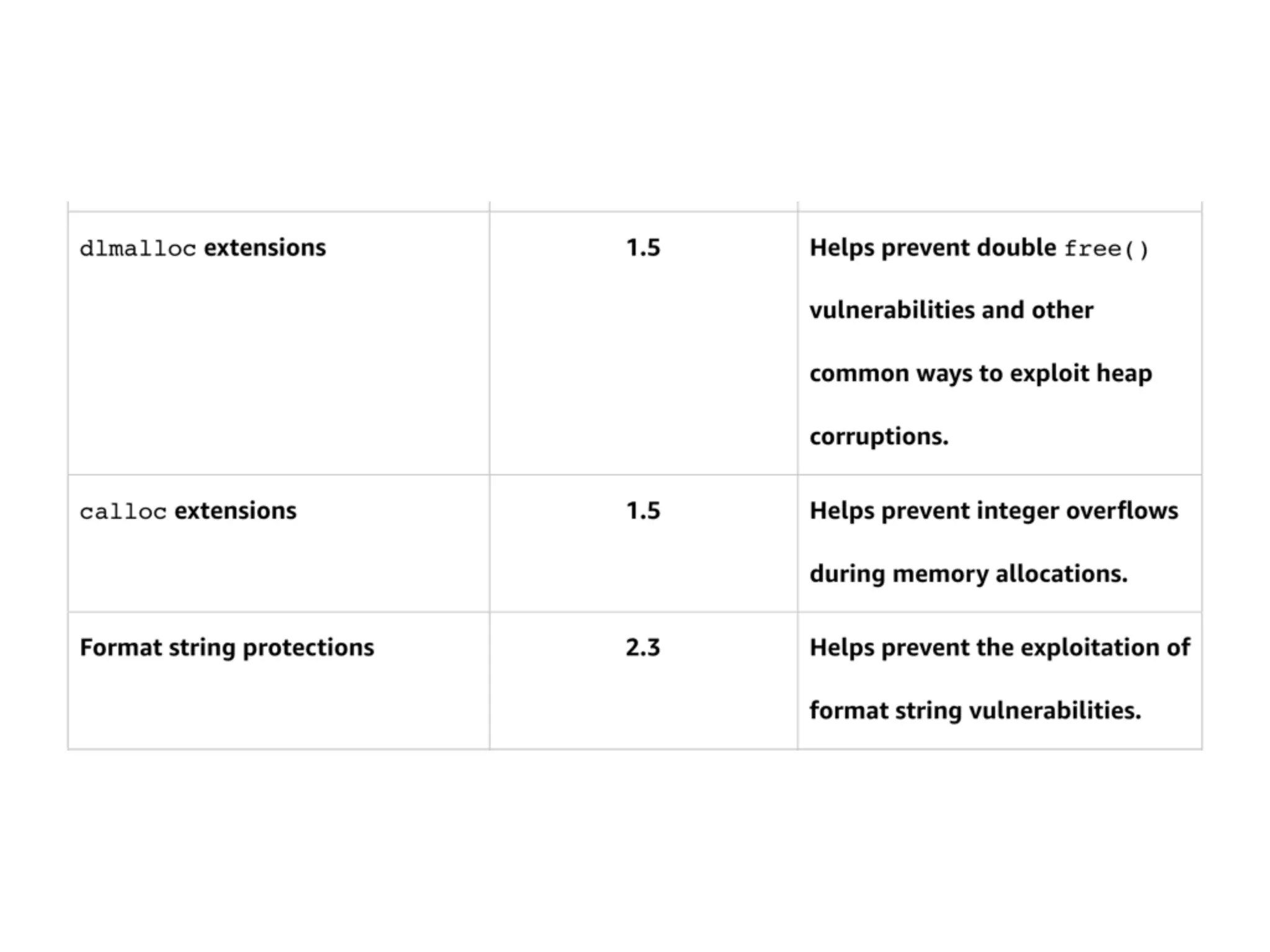
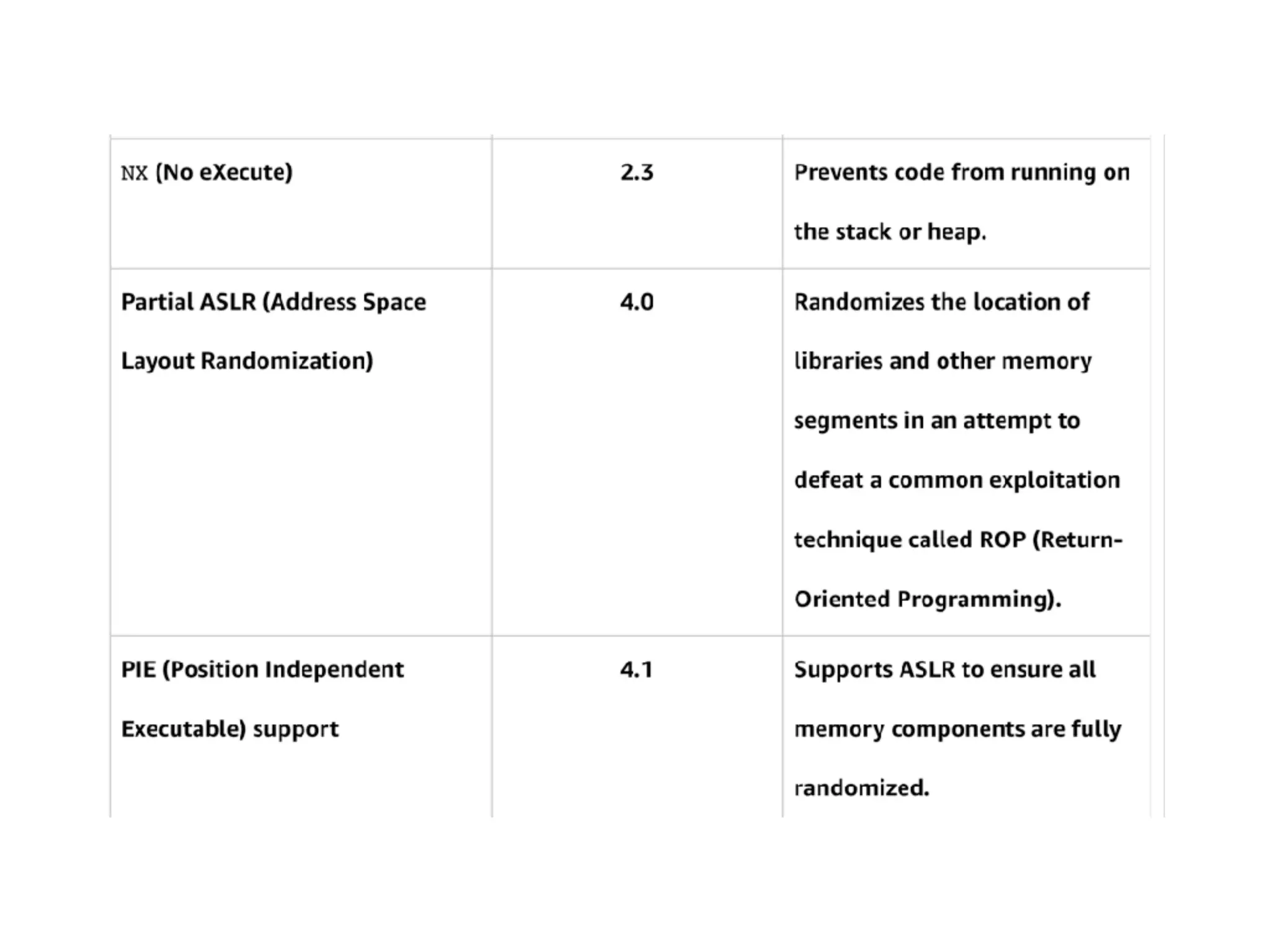
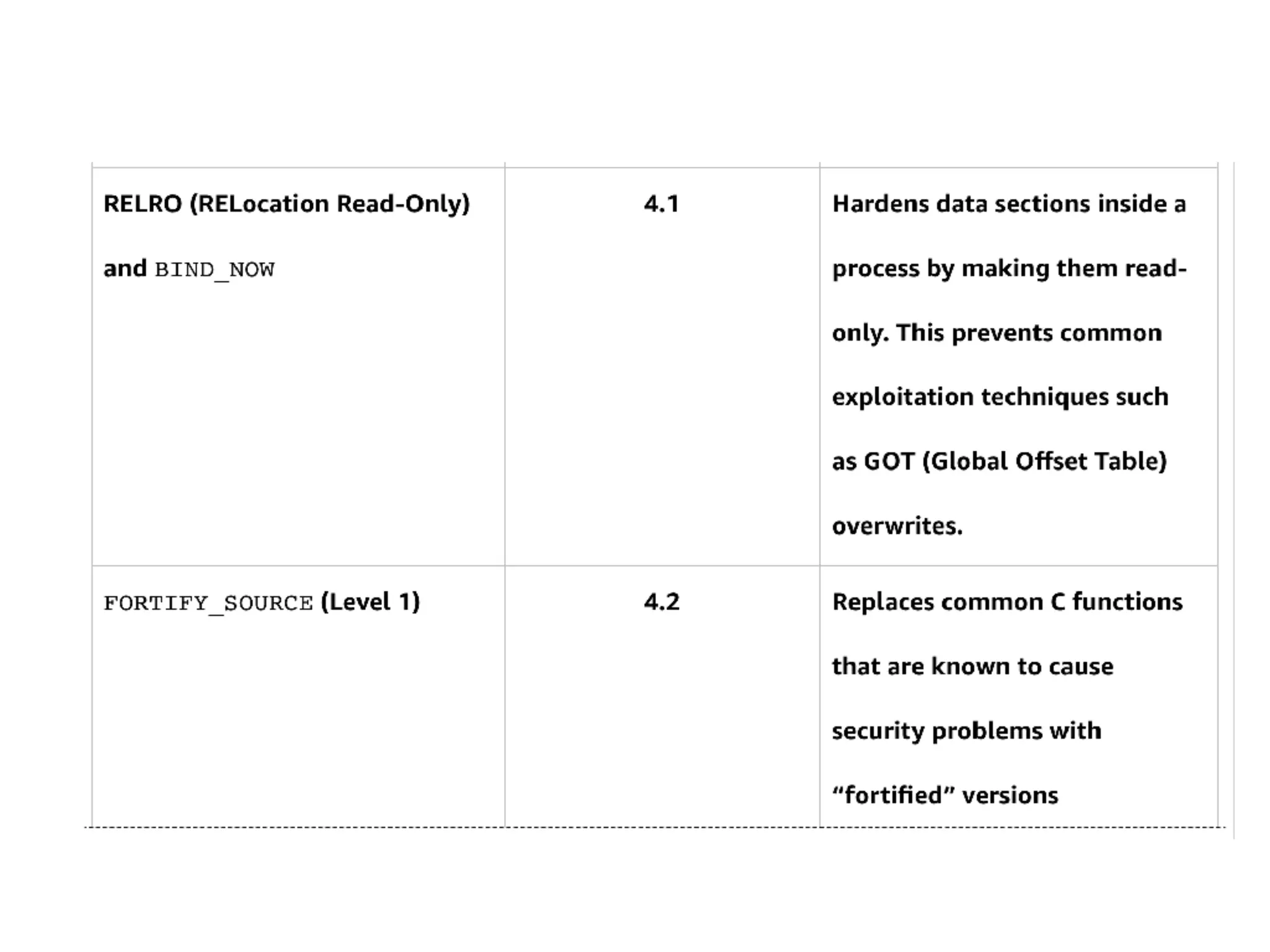
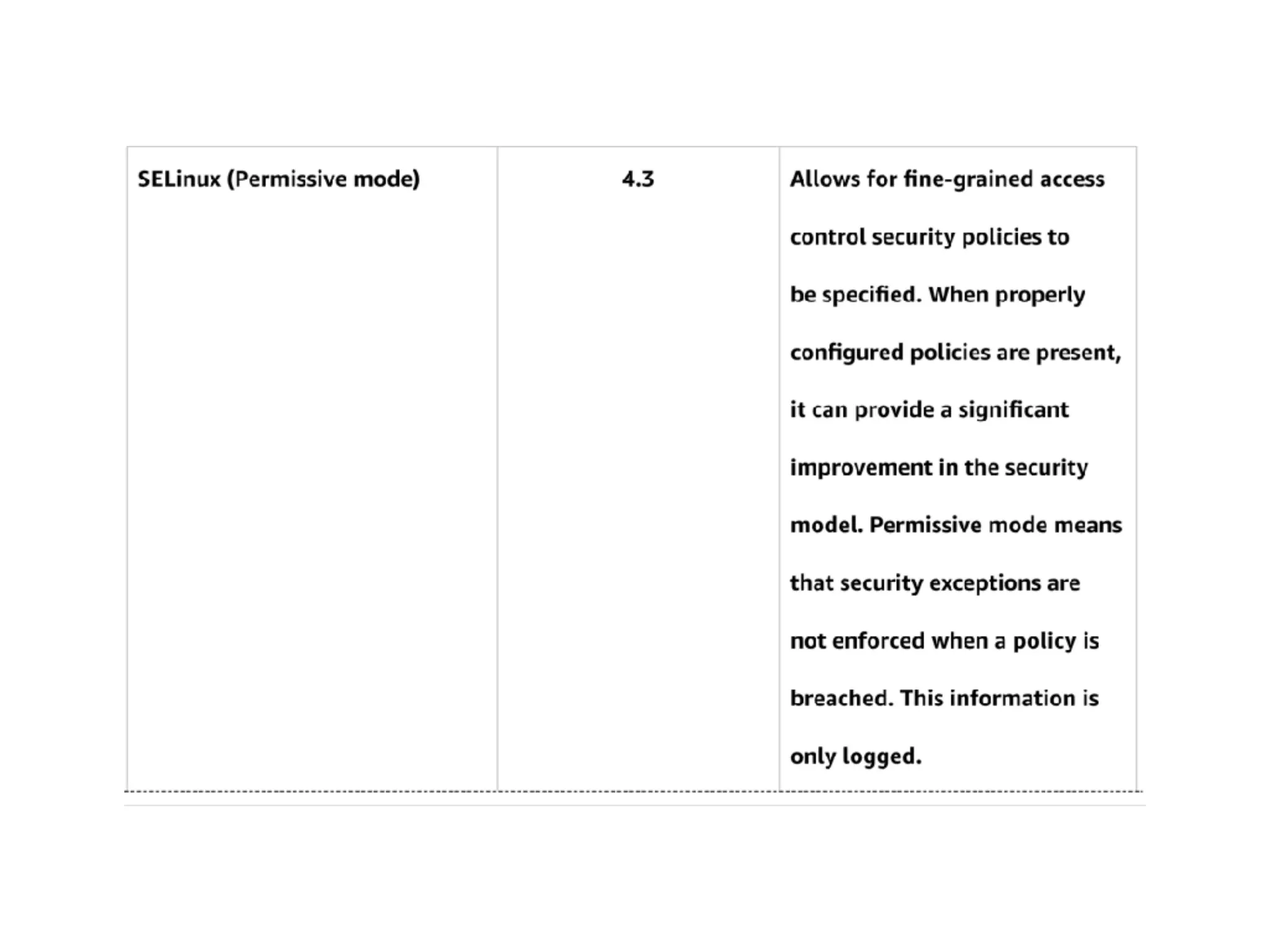
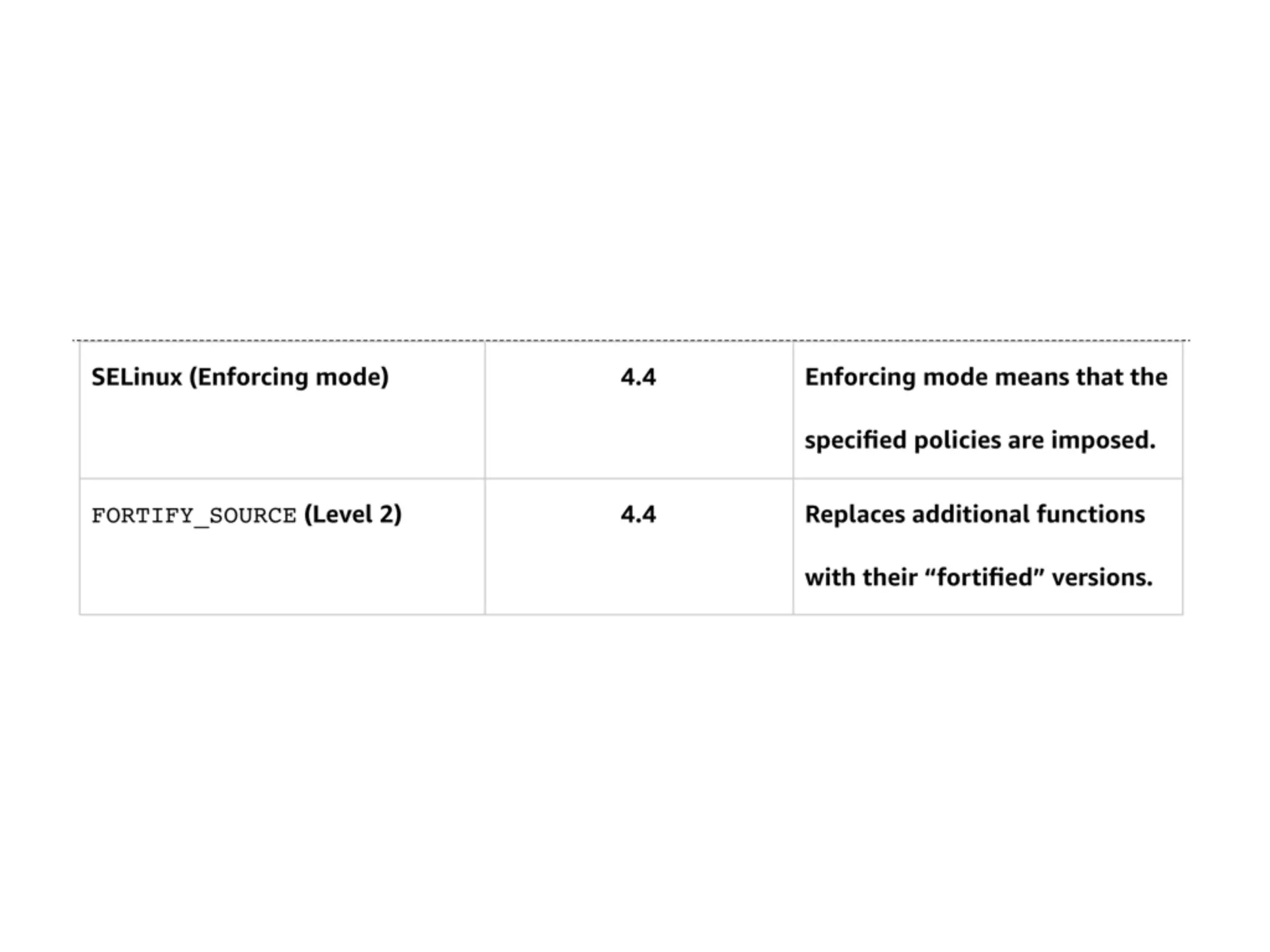
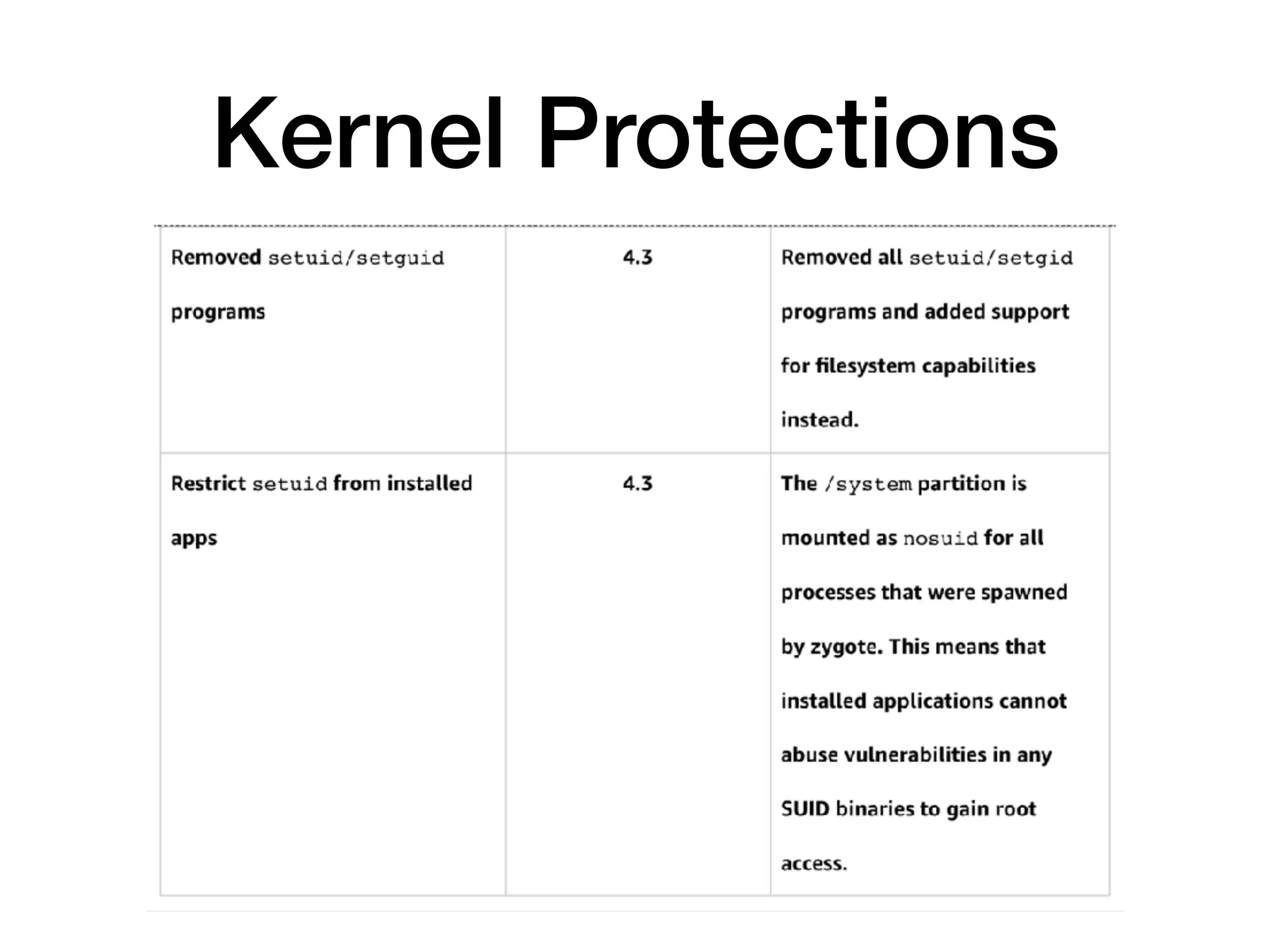
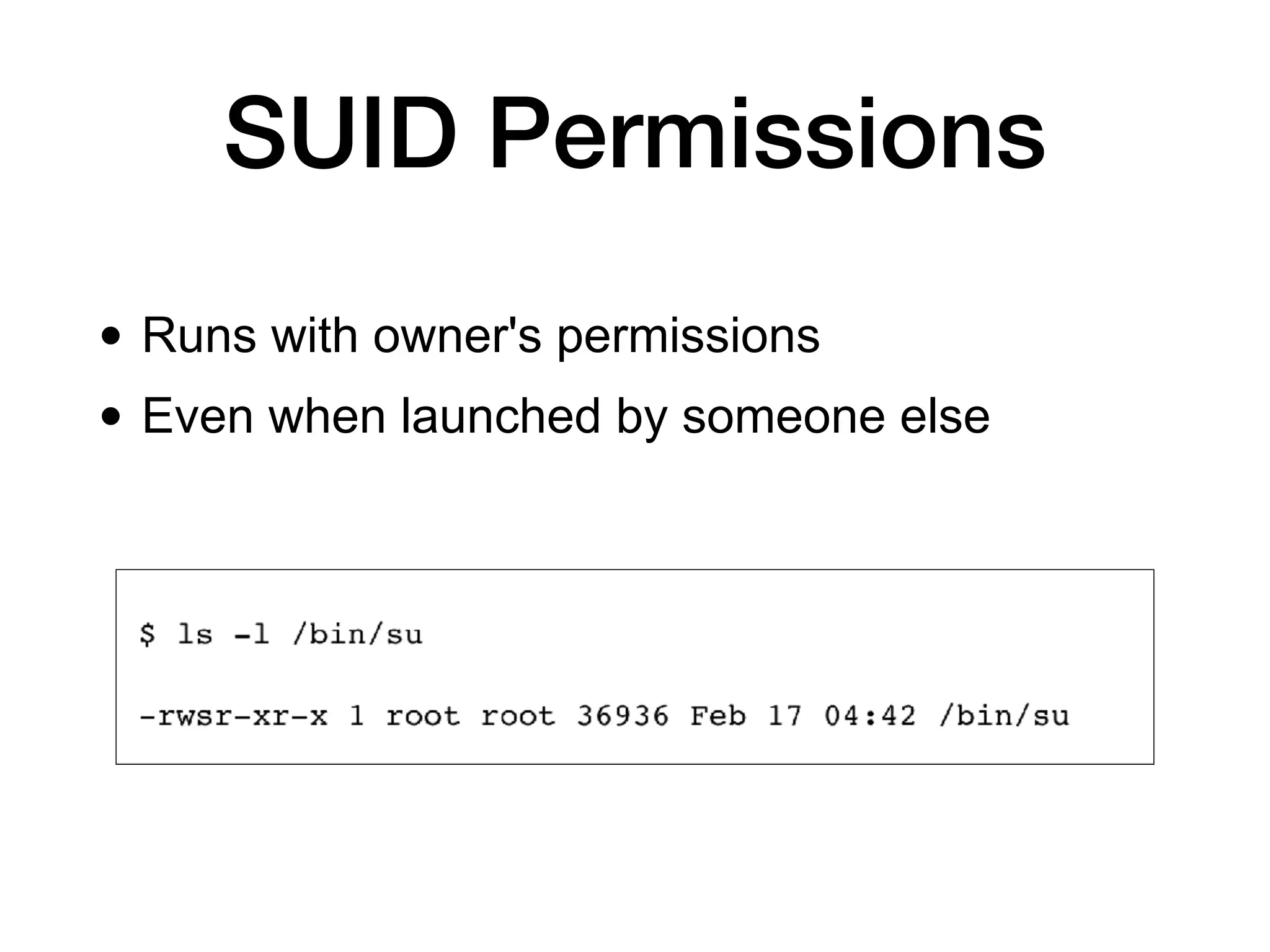
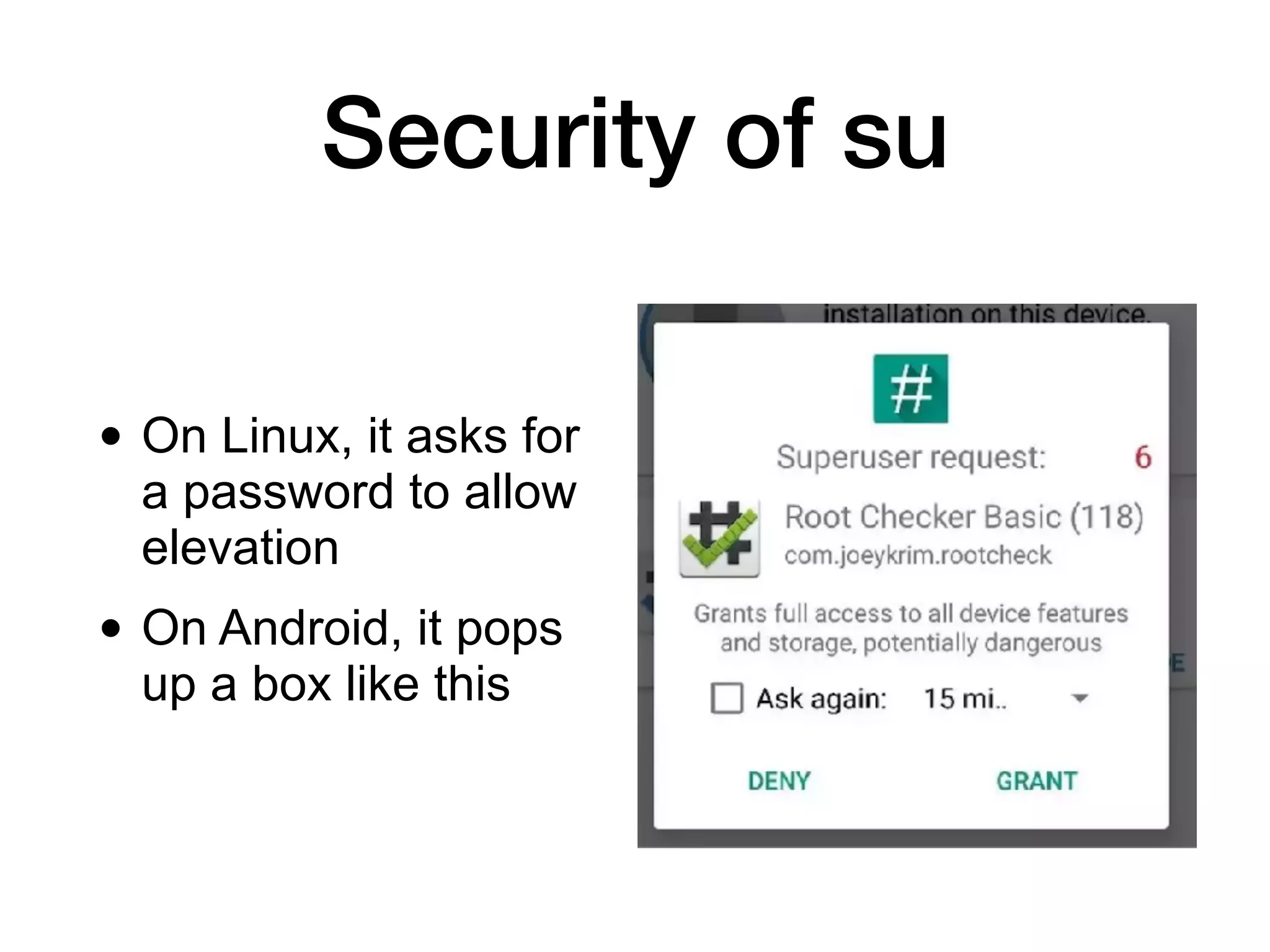
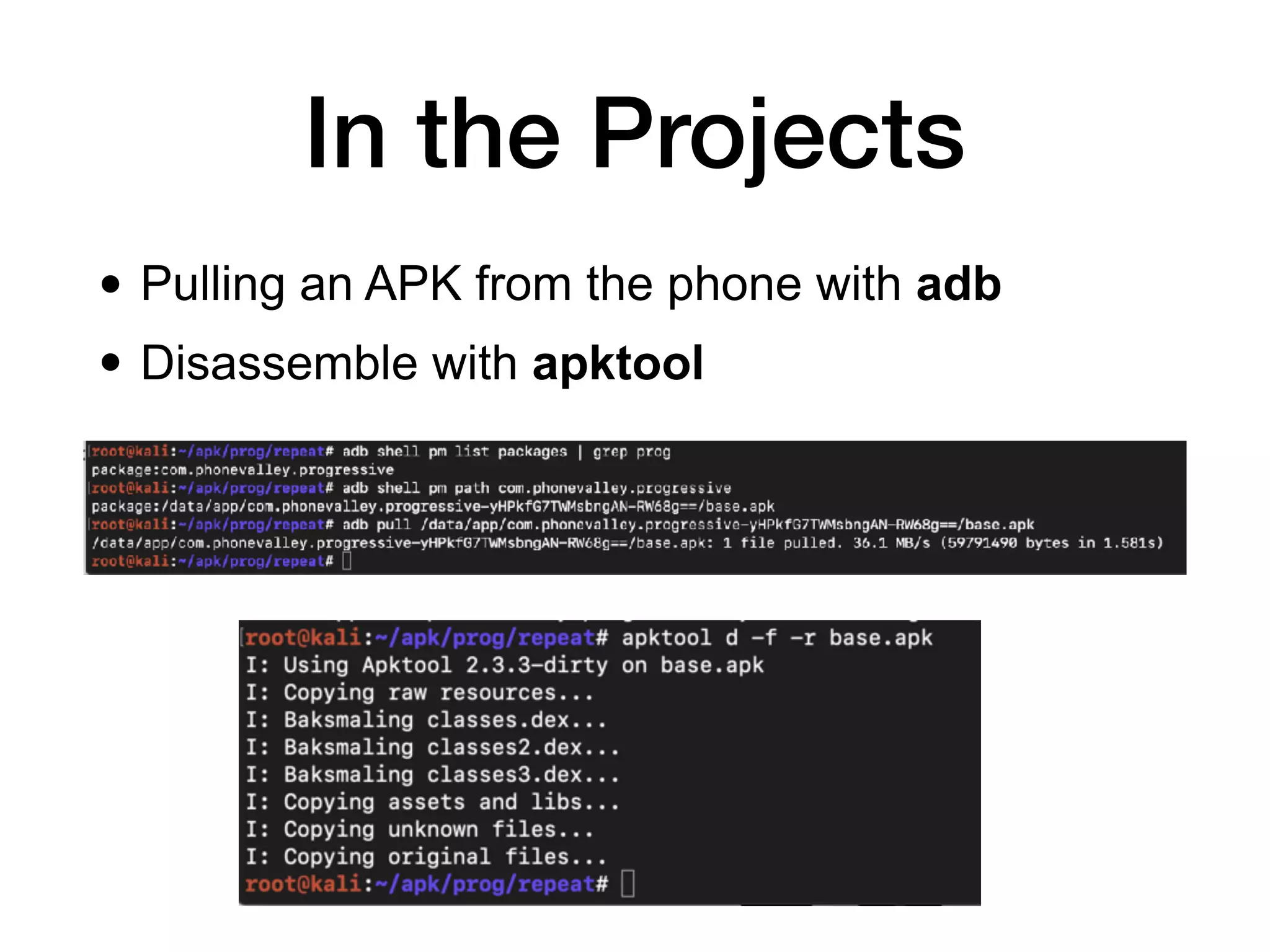
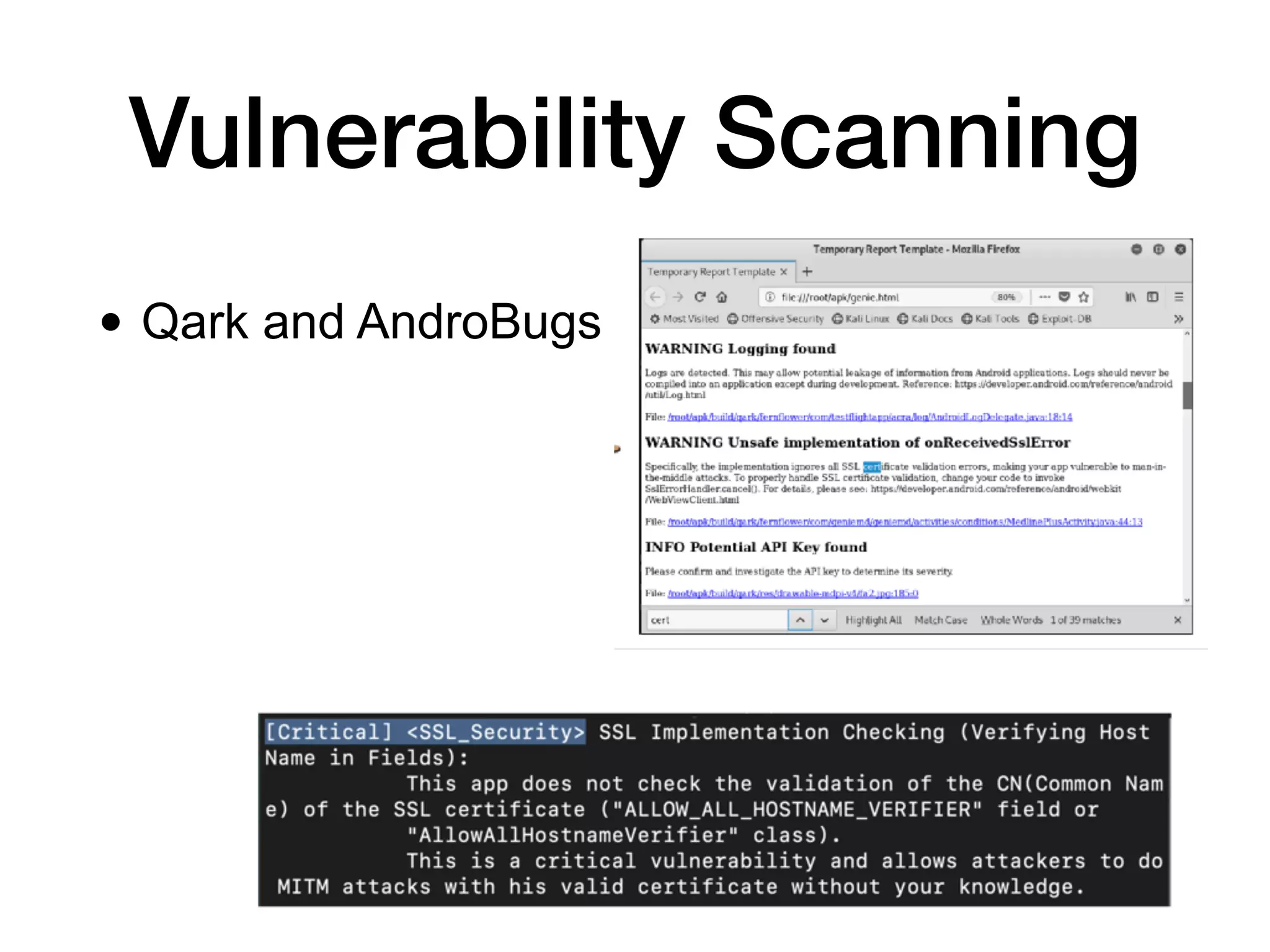
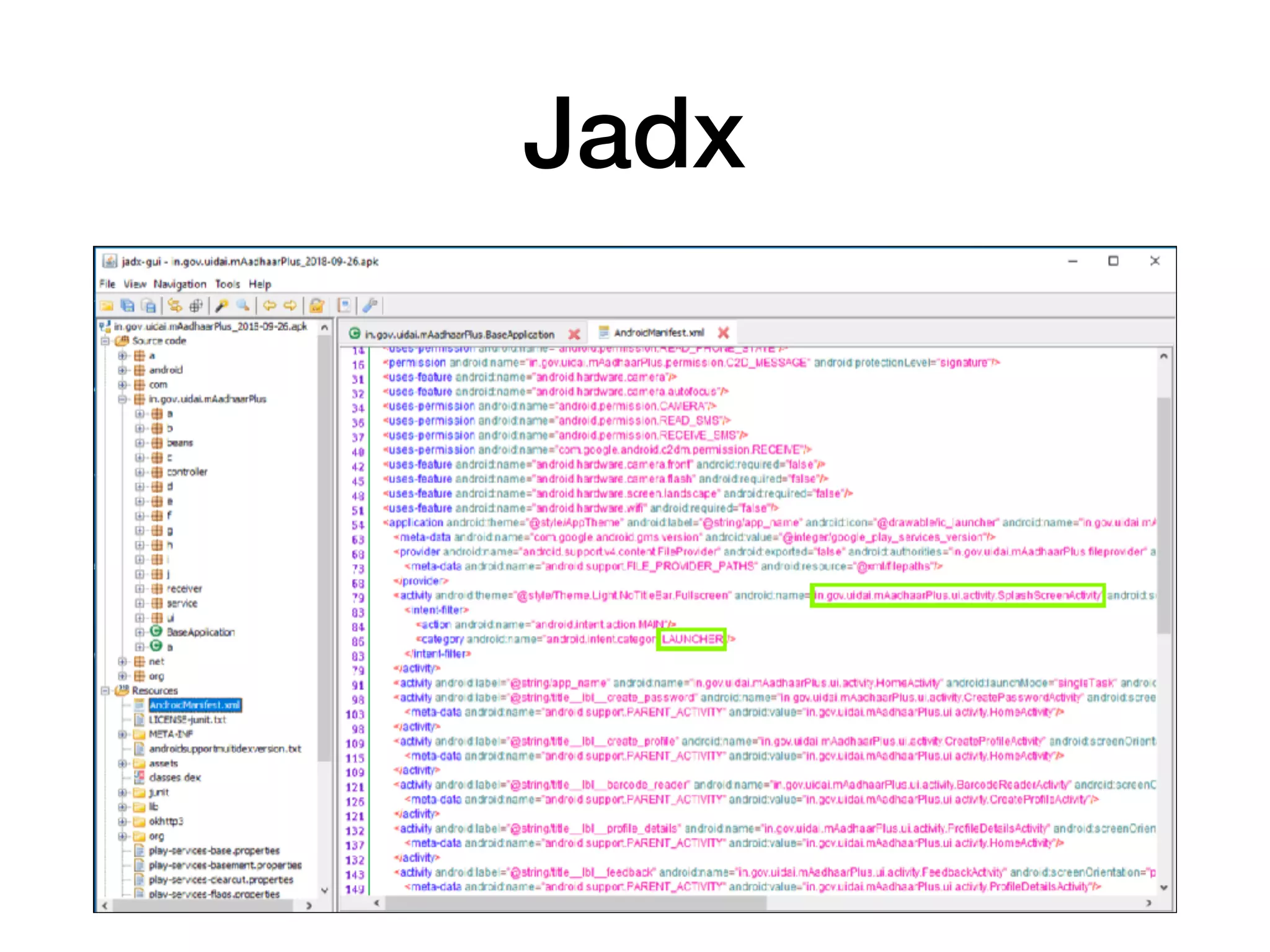
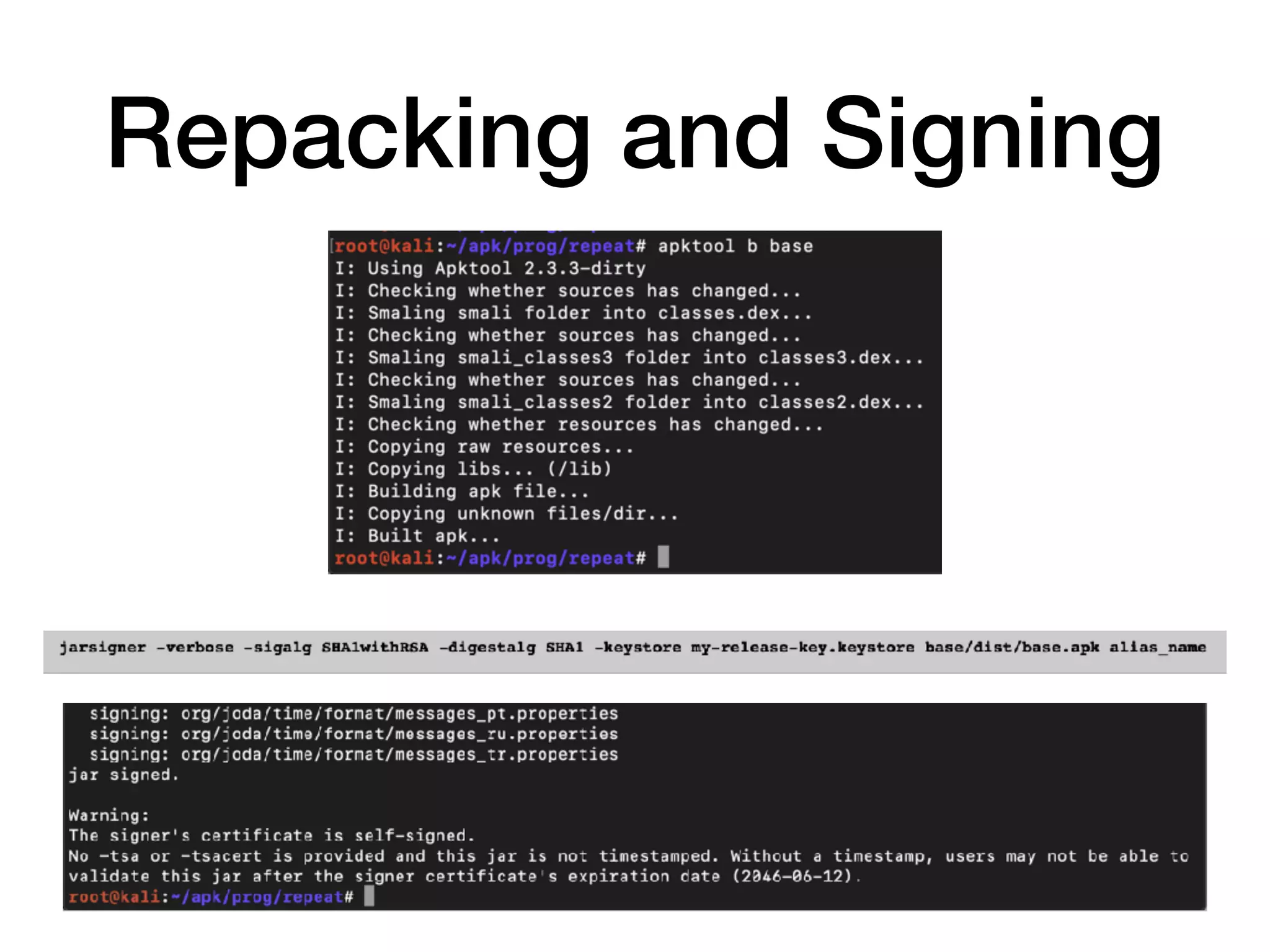
This document provides a comprehensive overview of analyzing Android applications, focusing on reverse-engineering techniques and security models. It covers rooting methods, generic exploit mitigations, and various vulnerabilities associated with Android devices. Additionally, it details tools and techniques for vulnerability scanning and code modification in applications.