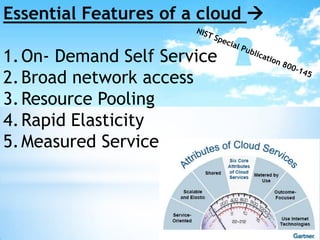
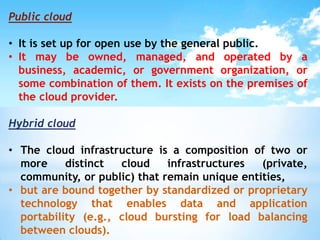
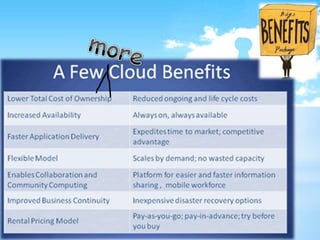
- The document discusses cloud computing concepts including virtualization, essential cloud features, cloud service models (SaaS, PaaS, IaaS, BPaaS), deployment models (private, public, hybrid, community cloud), and benefits of cloud computing.
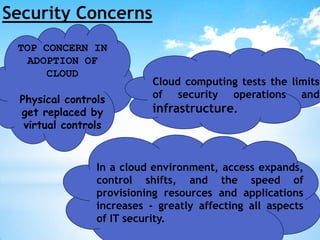
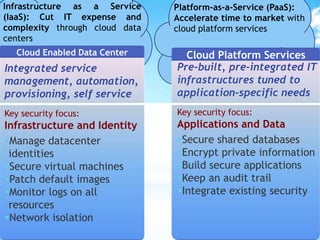
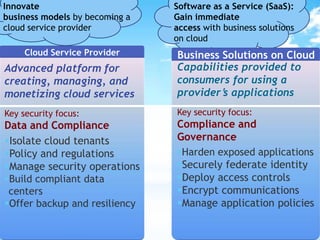
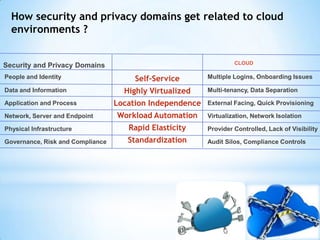
- It outlines security concerns in cloud environments related to issues like physical controls being replaced by virtual controls, expanded access and shifted control, and increased speed of provisioning. It discusses how security domains map to cloud environments.
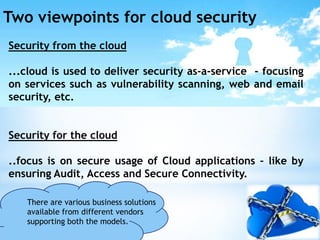
- Finally, it presents two viewpoints on cloud security - security from the cloud focuses on security-as-a-service, while security for the cloud focuses on secure usage of cloud applications.