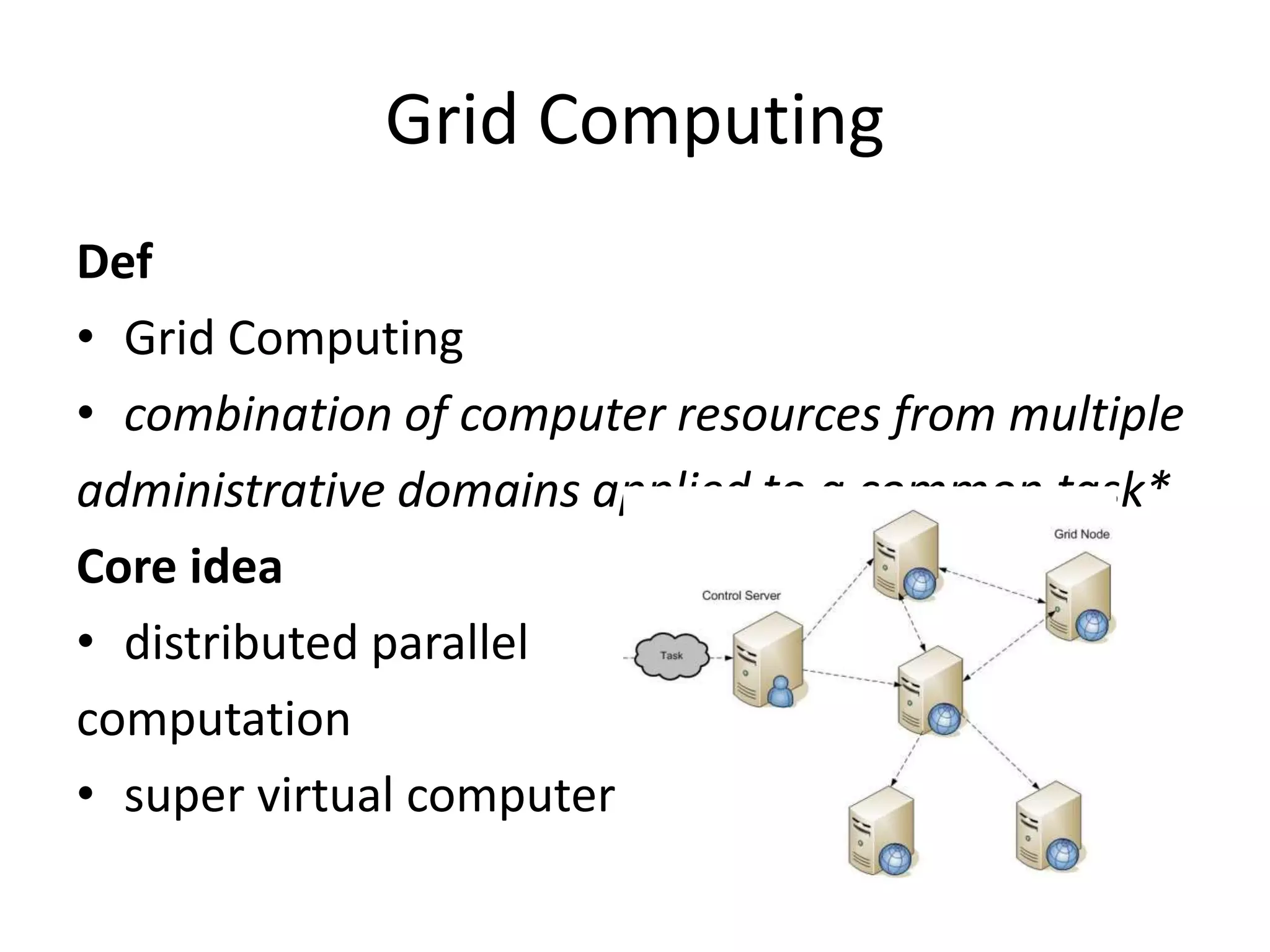
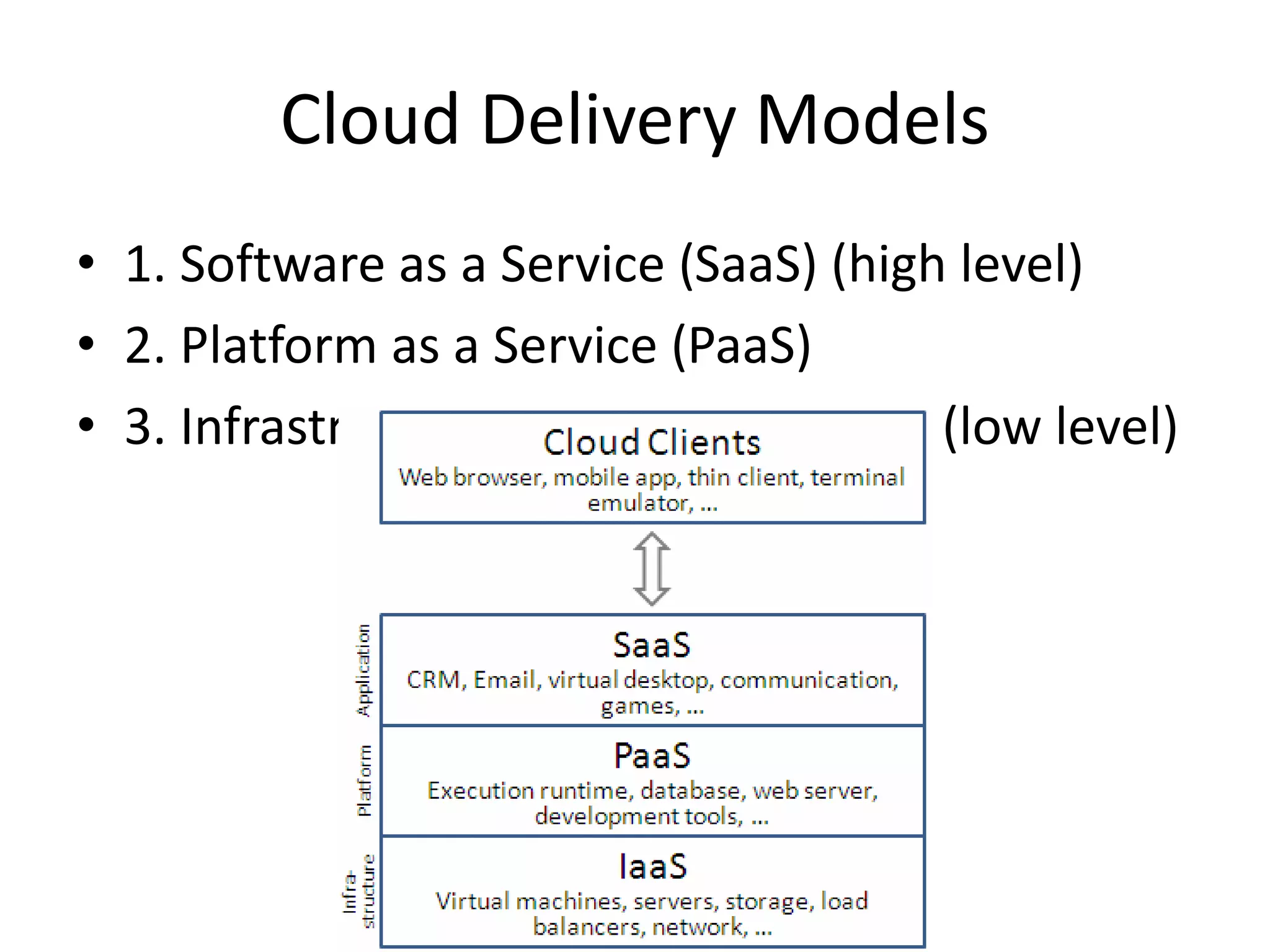
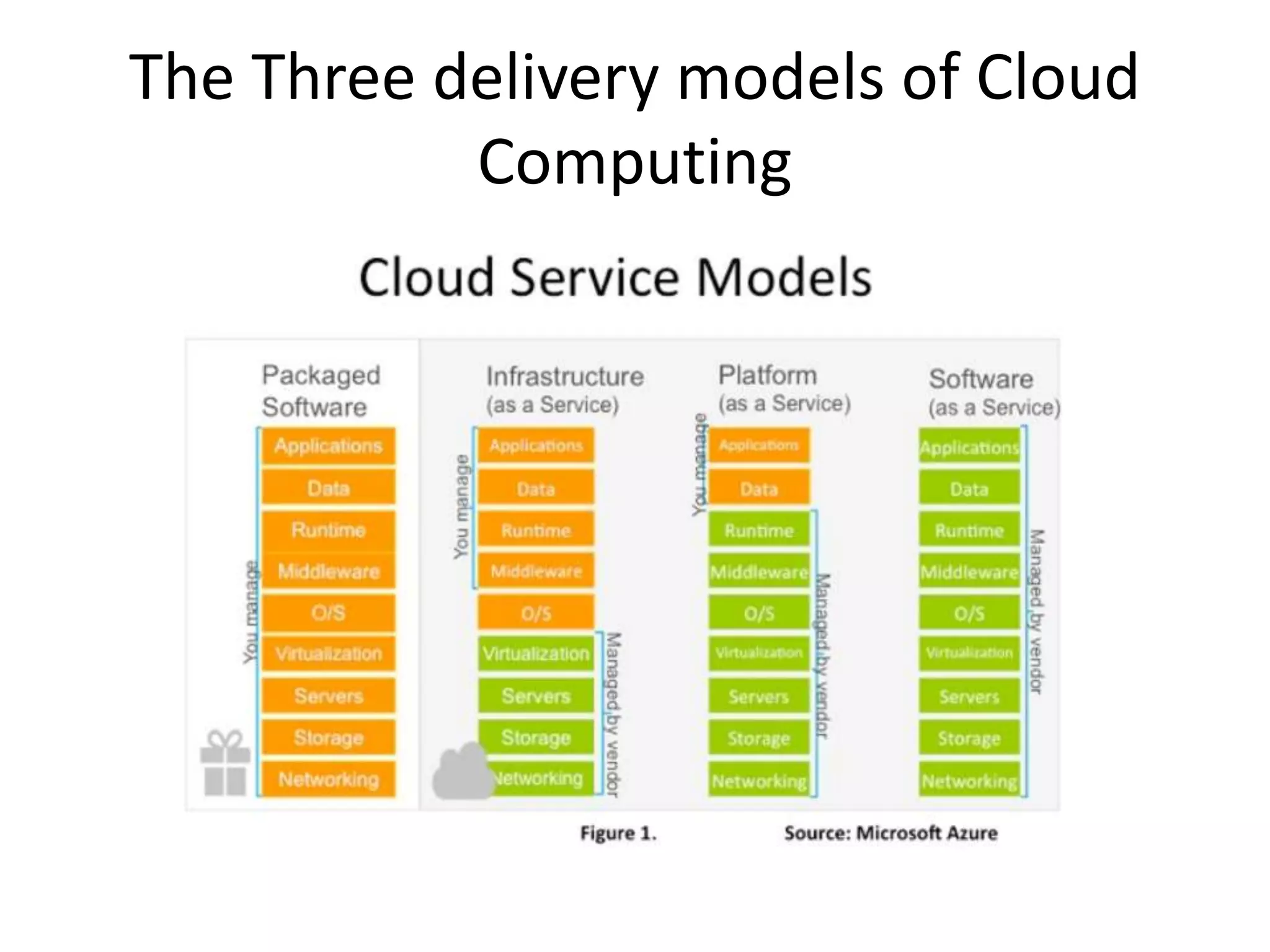
Grid computing and utility computing were early models that influenced the development of cloud computing. Cloud computing provides on-demand access to shared computing resources like networks, servers, storage, applications and services via the internet. There are three cloud computing delivery models: Infrastructure as a Service (IaaS), Platform as a Service (PaaS), and Software as a Service (SaaS). IaaS provides basic computing resources, PaaS provides platforms to build applications, and SaaS provides ready-to-use applications. While cloud computing provides advantages like reduced costs and increased scalability, it also faces challenges regarding privacy, security, and vulnerabilities from infrastructure failures or attacks.