Embed presentation
Downloaded 203 times

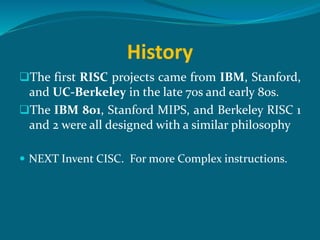

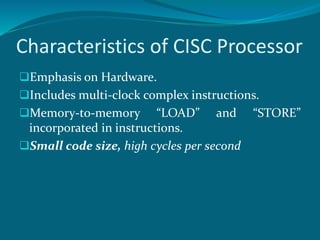
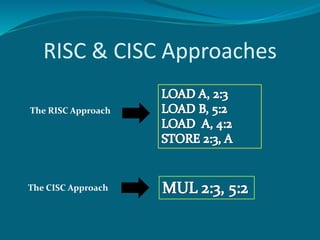


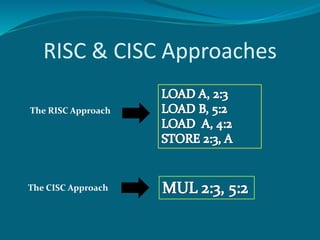
CISC processors have a large number of complex instructions that can perform operations directly from memory to memory. In contrast, RISC processors have a small set of simple instructions that operate only within registers, with load and store as separate instructions. The first RISC projects in the late 1970s-early 1980s from IBM, Stanford, and UC-Berkeley aimed for single-cycle execution with a fixed-length instruction format. RISC emphasizes hardware simplicity while CISC focuses on smaller code size and higher cycles per second.