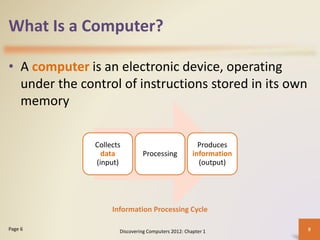
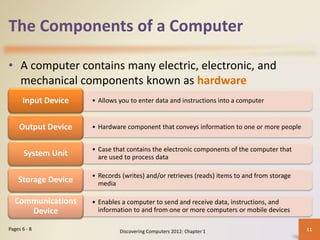
This document provides an overview of an introductory course on information technology. It outlines the course requirements, including exams, assignments, and a final project that contribute to the overall grade. It also describes lecture notes, written assignments, presentations, and other class activities. Tips are provided on how to earn more marks, such as avoiding plagiarism and demonstrating a strong work ethic. The course aims to teach basic computer knowledge, hardware, office applications, and internet skills.