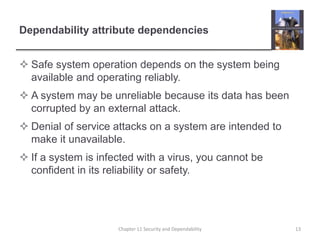
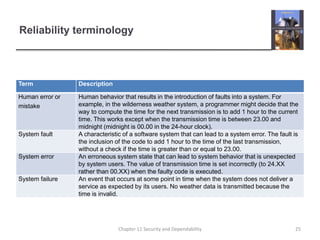
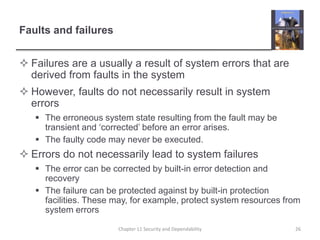
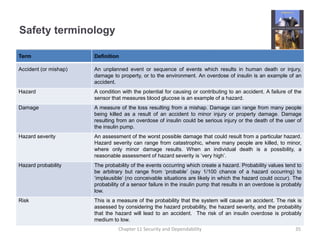
This document discusses the key aspects of system dependability, including availability, reliability, safety, and security. It notes that dependability reflects the degree to which users trust a system and defines it as covering attributes like availability, reliability, and security. It also discusses factors that influence perceptions of reliability and availability, such as usage patterns, outage length and number of users affected.