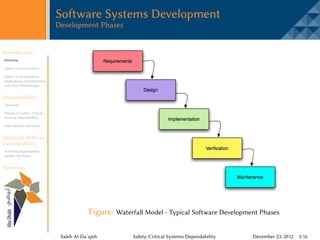
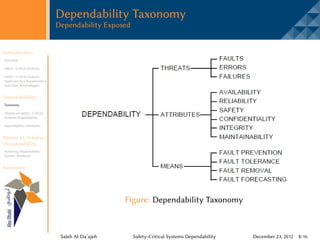
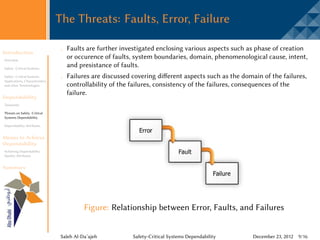
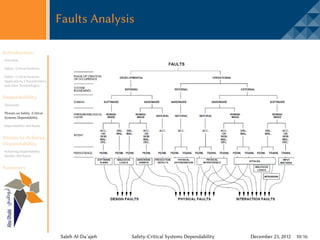
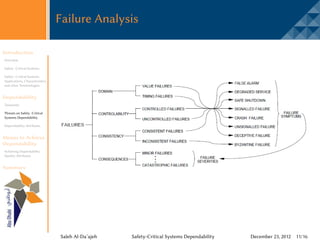
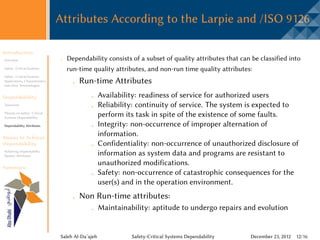
The document discusses safety-critical systems and their dependability. It defines safety-critical systems as those whose failure could result in catastrophic consequences such as loss of life. Examples include failures that caused loss of spacecraft, power outages, and airplane crashes. Dependability is the ability of a system to deliver services and avoid failures. It consists of threats like faults, errors, and failures; attributes like availability and reliability; and means to achieve attributes like fault prevention and fault tolerance. The document outlines techniques used to develop dependable safety-critical systems, including verification, validation, and engineering practices applied at early stages.