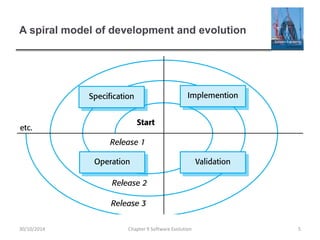
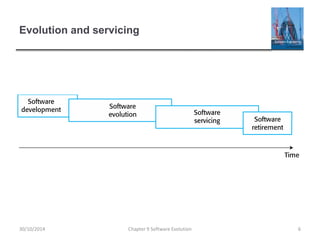
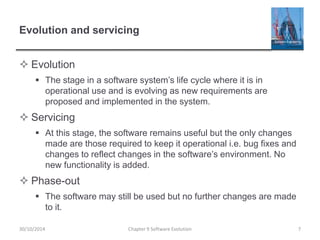
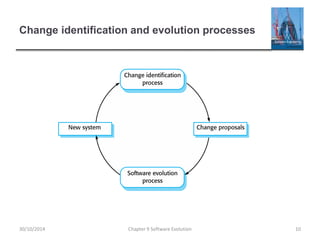
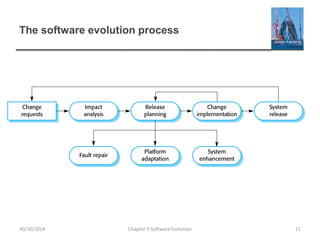
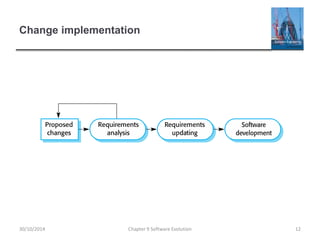
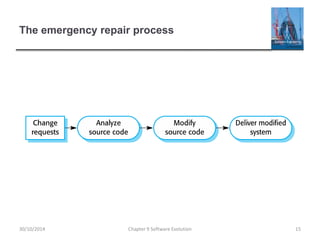
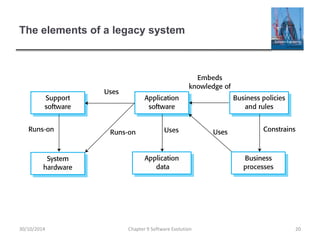
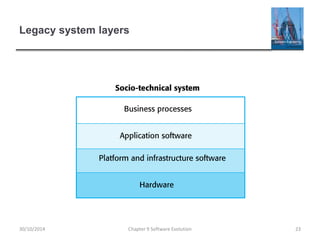
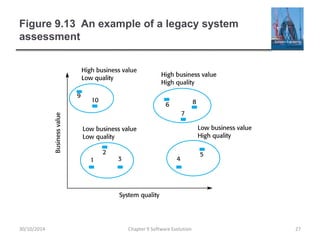
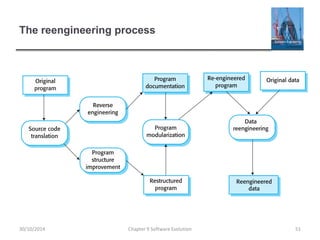
The chapter discusses software evolution, including that software change is inevitable due to new requirements, business changes, and errors. It describes how organizations must manage change to existing software systems, which represent huge investments. The majority of large software budgets are spent evolving, rather than developing new, systems. The chapter outlines the software evolution process and different approaches to evolving systems, including addressing urgent changes. It also discusses challenges with legacy systems and their management.