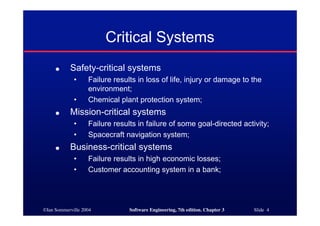
This document discusses critical systems and system dependability. It defines critical systems as those where failure could have severe consequences, such as safety-critical systems where failure could result in loss of life. It describes four dimensions of dependability for critical systems: availability, reliability, safety, and security. Availability and reliability refer to a system operating properly and delivering services as expected. Safety ensures a system cannot cause harm or damage. Security protects a system from external attacks. The document uses an insulin pump as an example of a safety-critical system to illustrate dependability requirements and discusses techniques for achieving dependability.