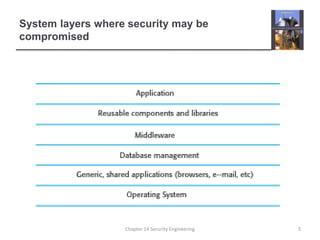
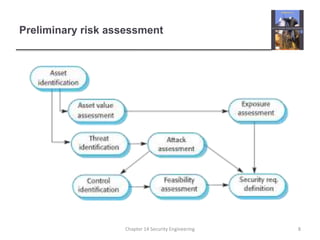
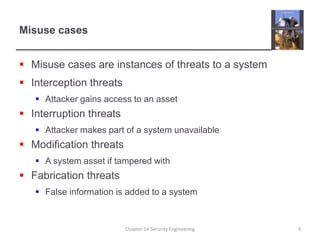
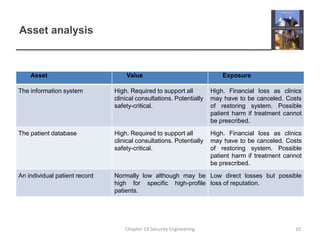
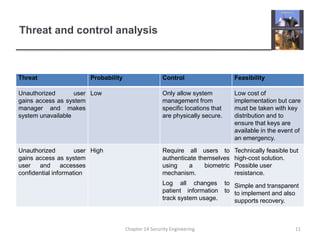
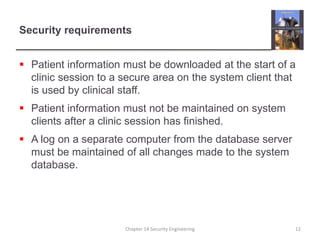
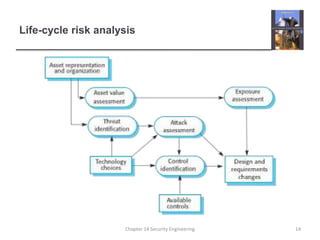
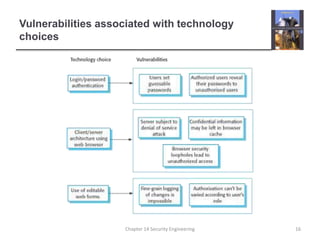
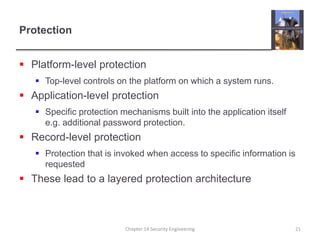
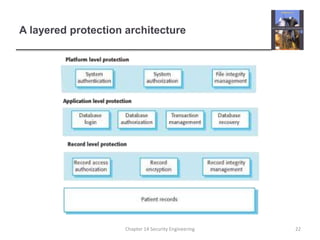
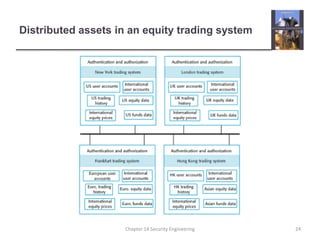
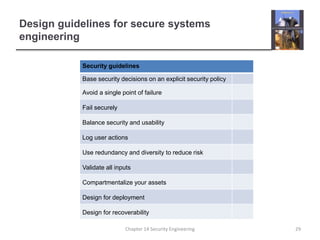
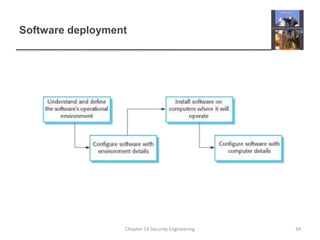
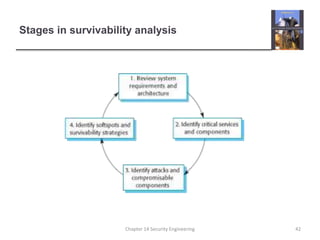
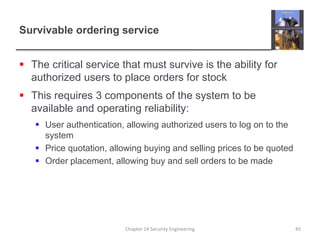
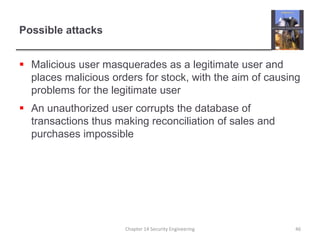
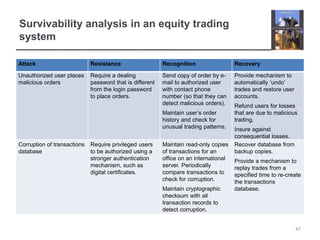
This document provides an overview of topics covered in Chapter 14 on Security Engineering. It discusses security engineering and how it is concerned with applying security to applications, as well as security risk assessment and designing systems based on risk assessments. The document outlines the importance of security management, as well as risk management approaches like preliminary risk assessment, life cycle risk assessment, and operational risk assessment. It also discusses designing systems for security through approaches like incorporating security into architectural design, following best practices, and minimizing vulnerabilities introduced during deployment. Finally, the document discusses system survivability and delivering essential services even when under attack.