This document describes the surgical procedure for repairing a symphysis pubis separation. The key steps involve:
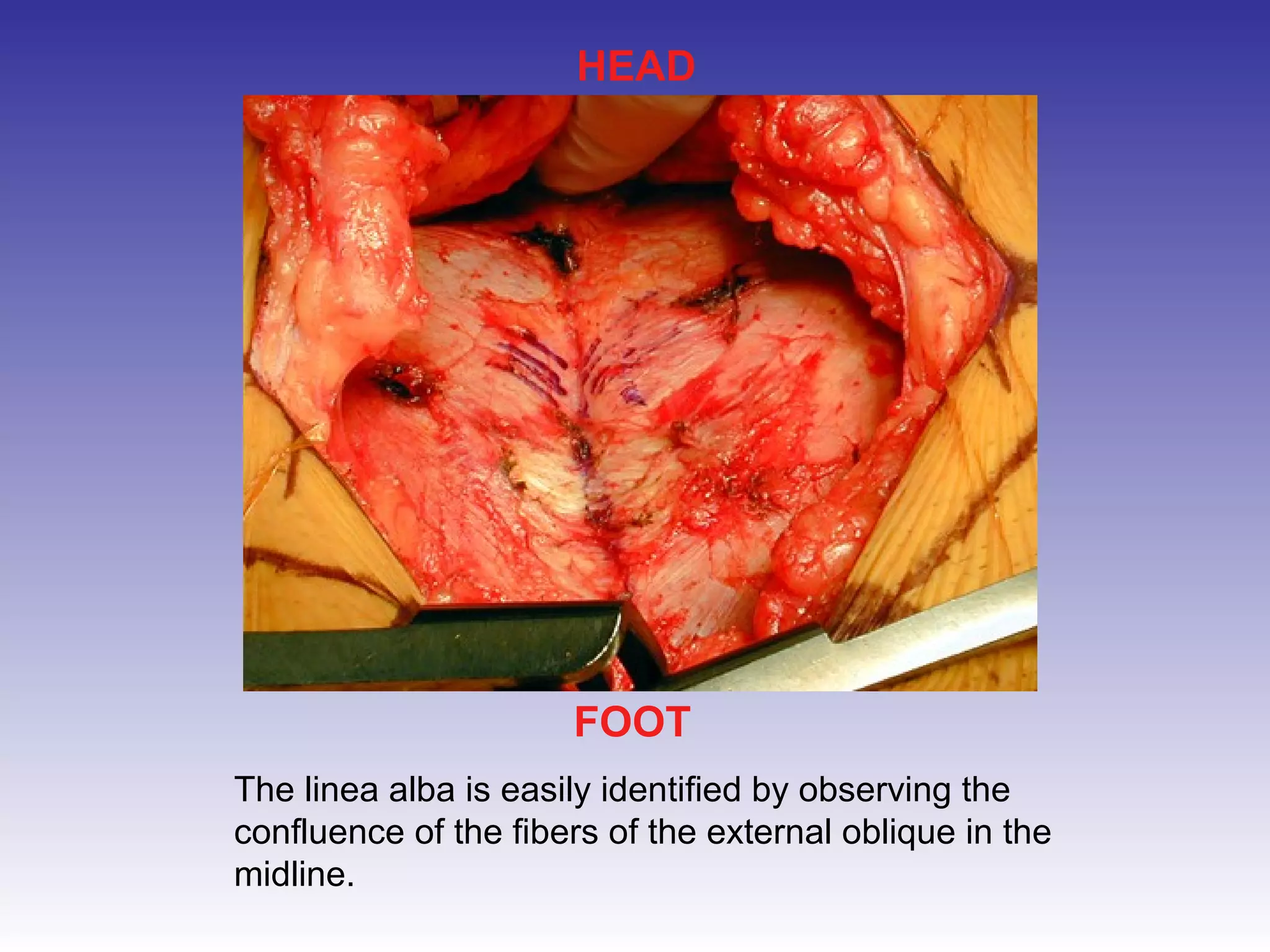
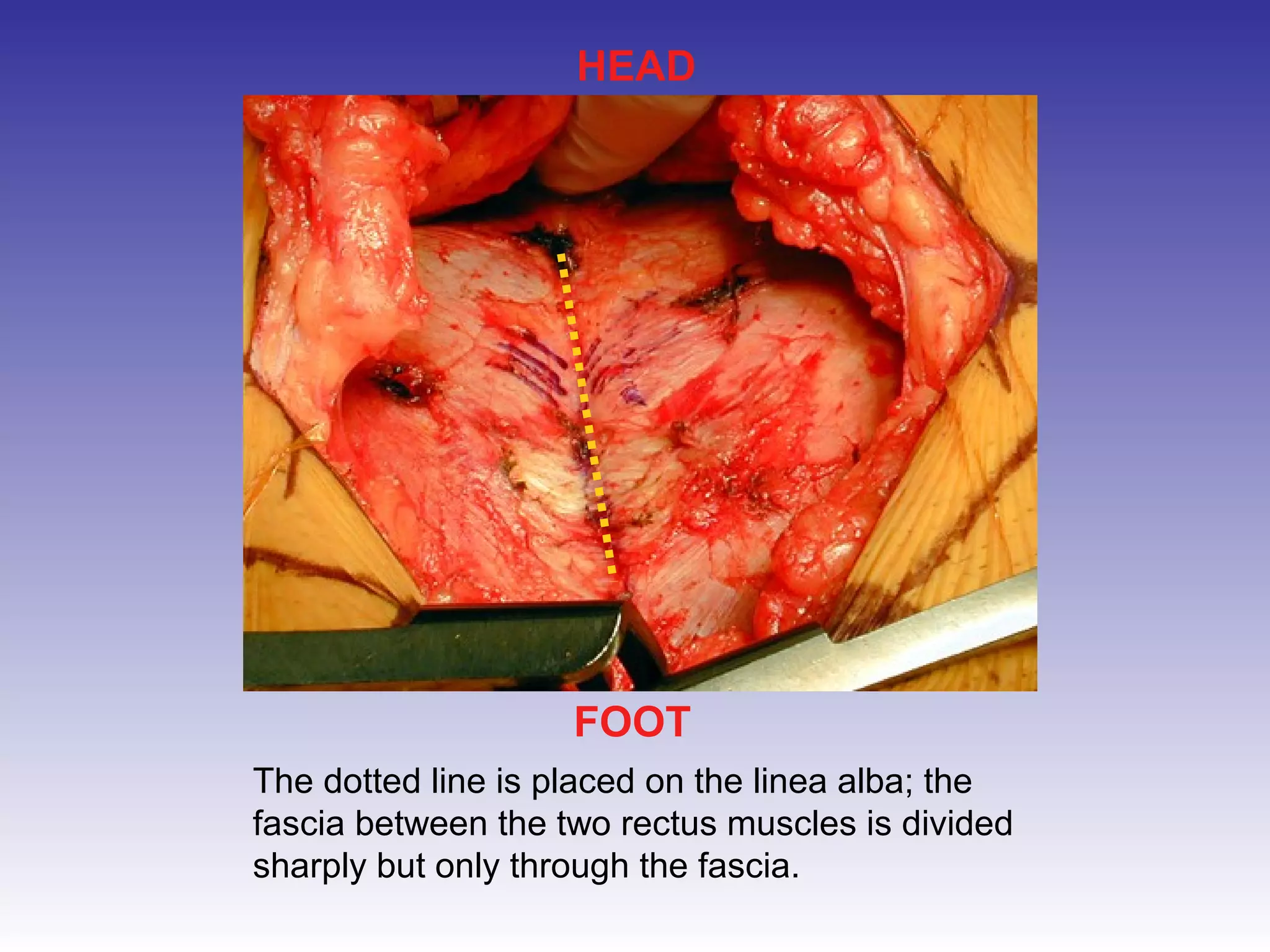
1) Making an incision above the pubic symphysis and retracting tissues to expose the injury;
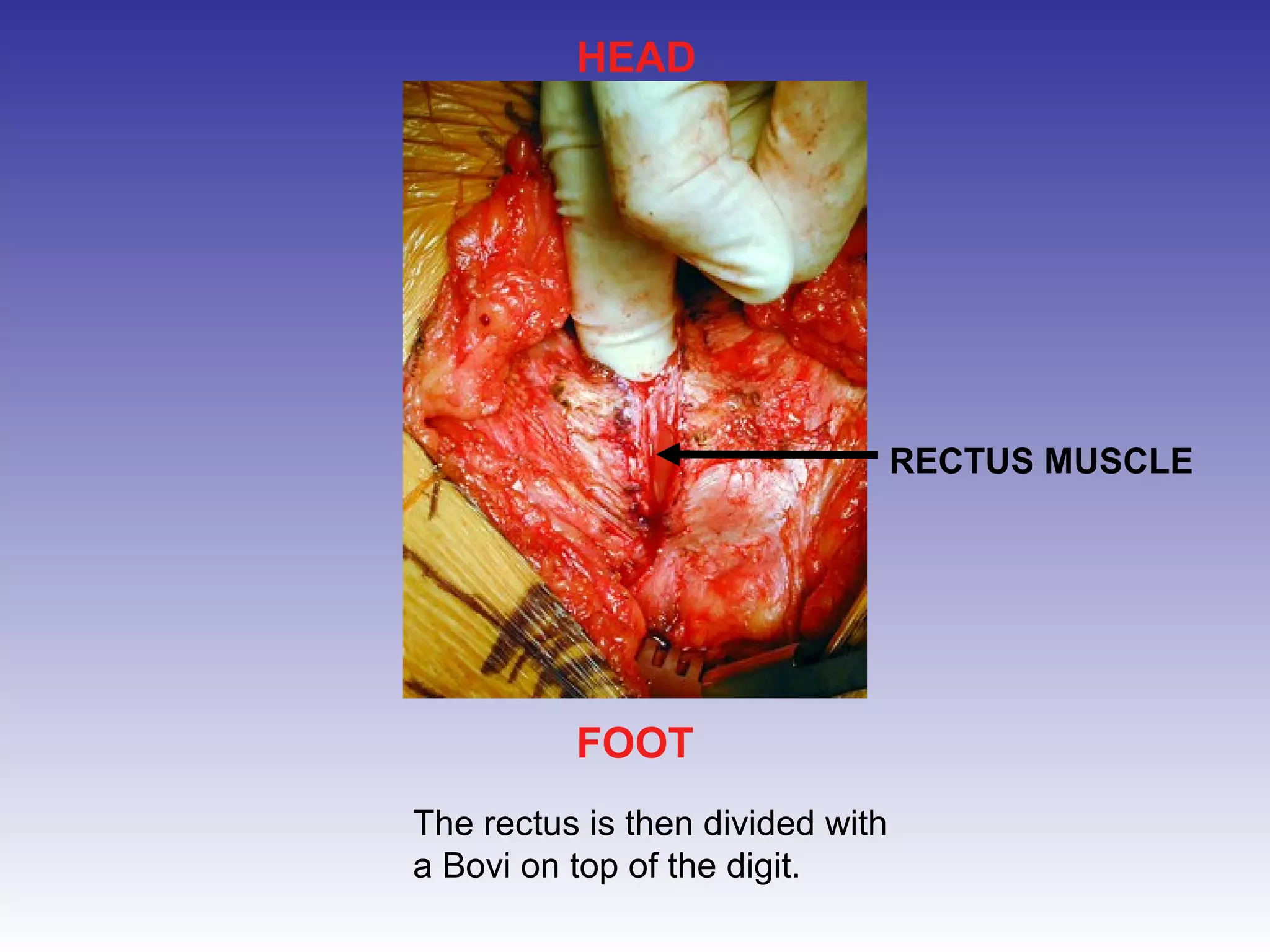
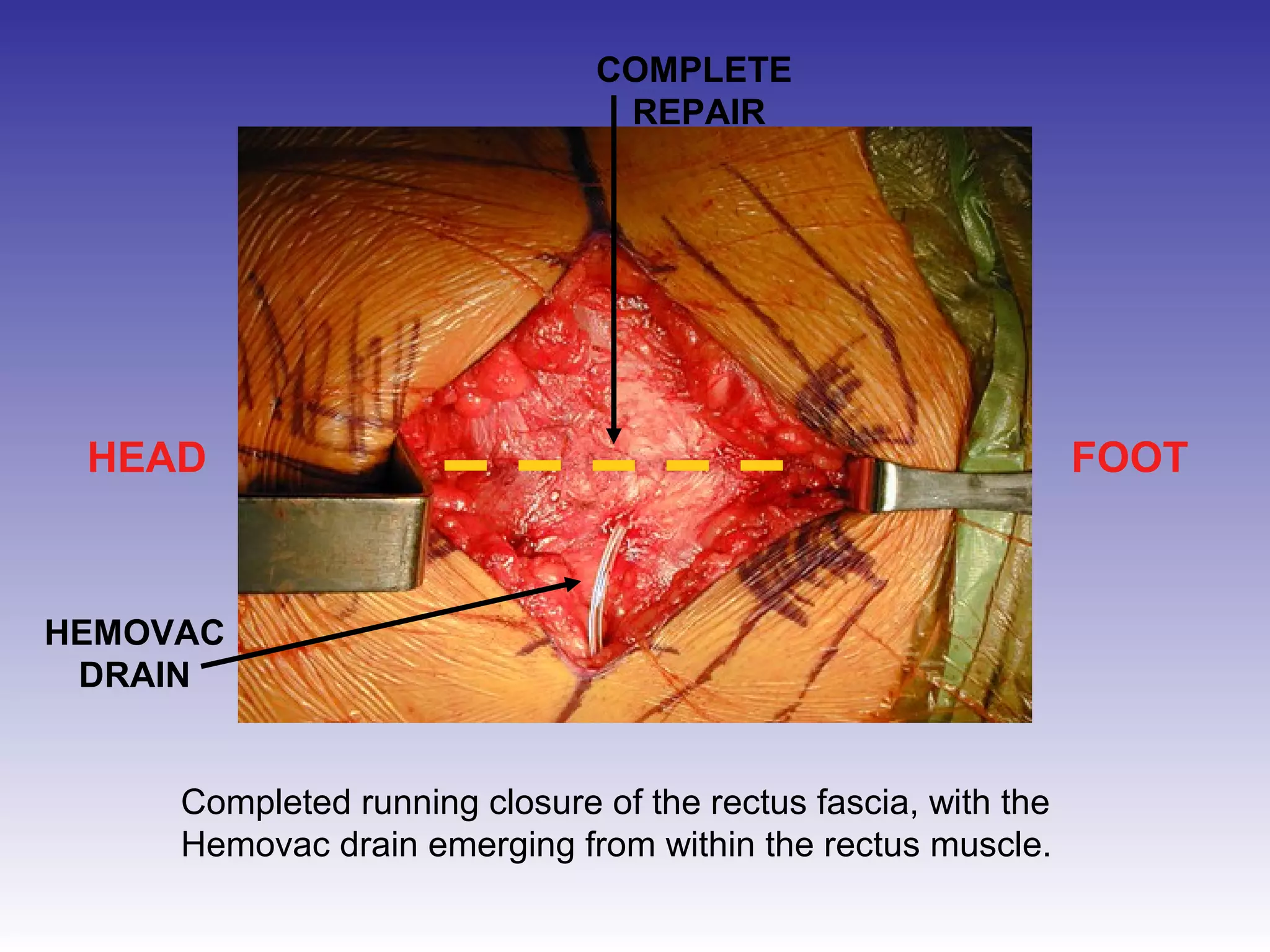
2) Splitting the rectus muscles and using retractors to further expose the pubic bones;
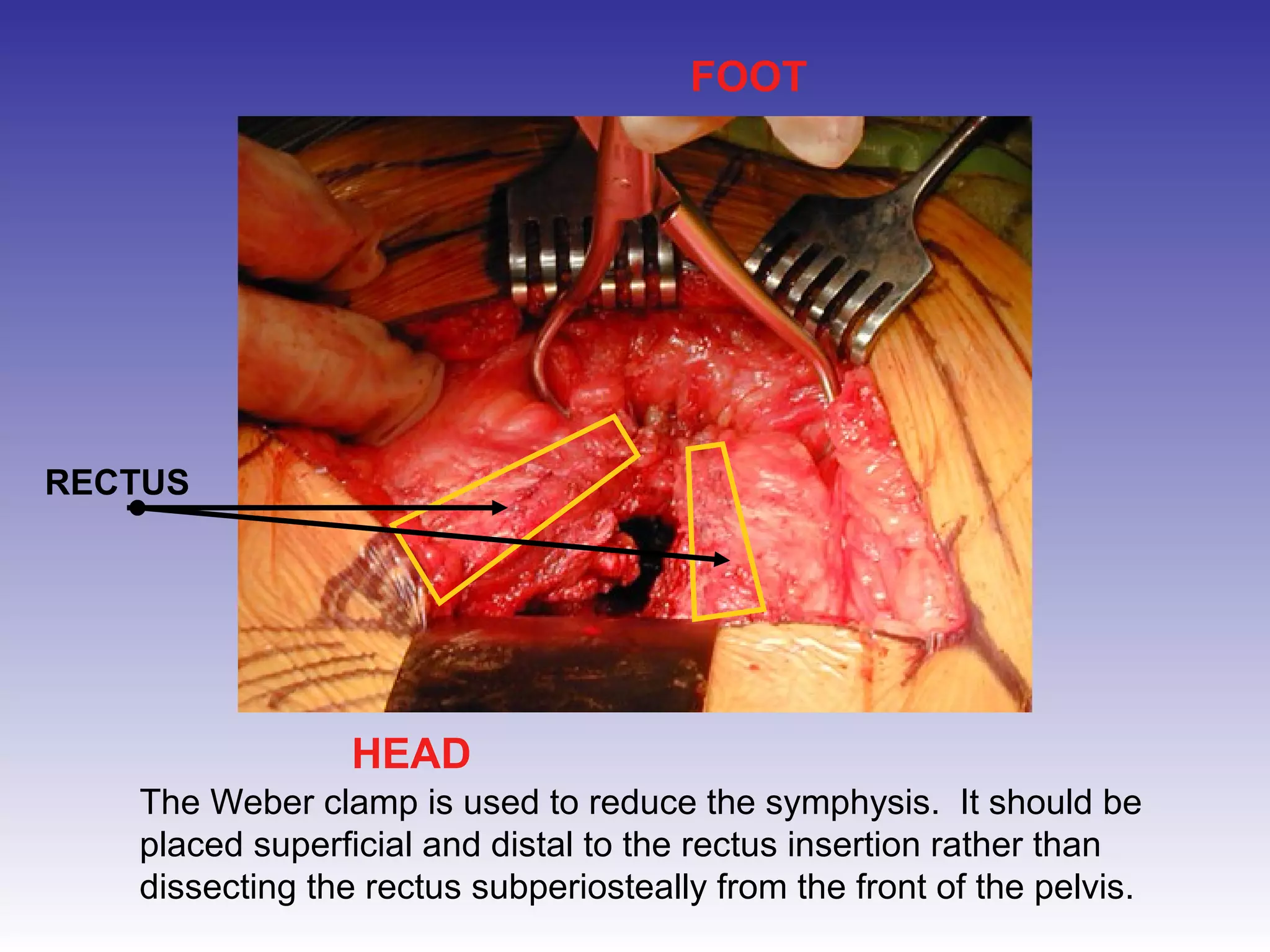
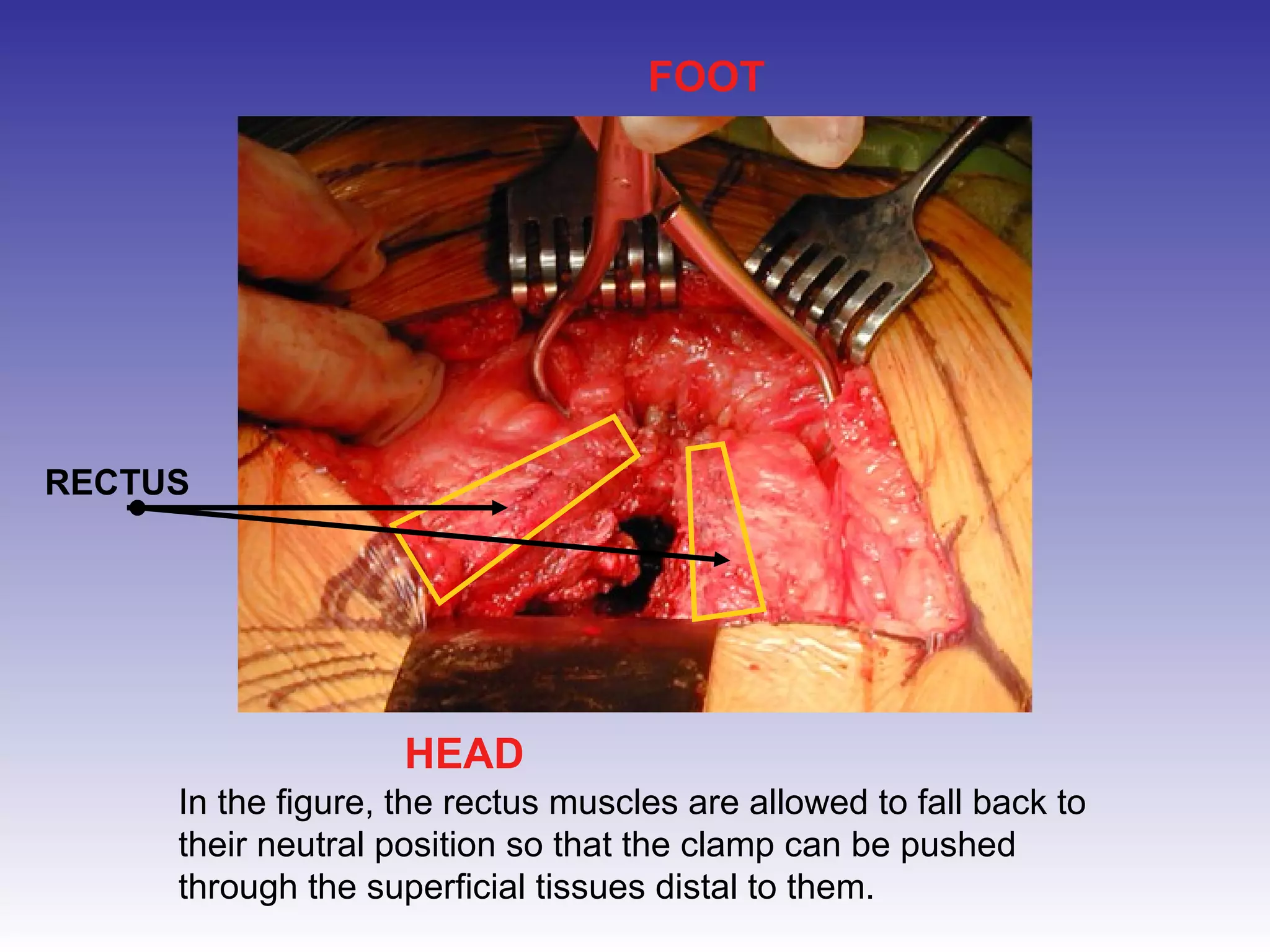
3) Reducing the separated pubic bones using a clamp;
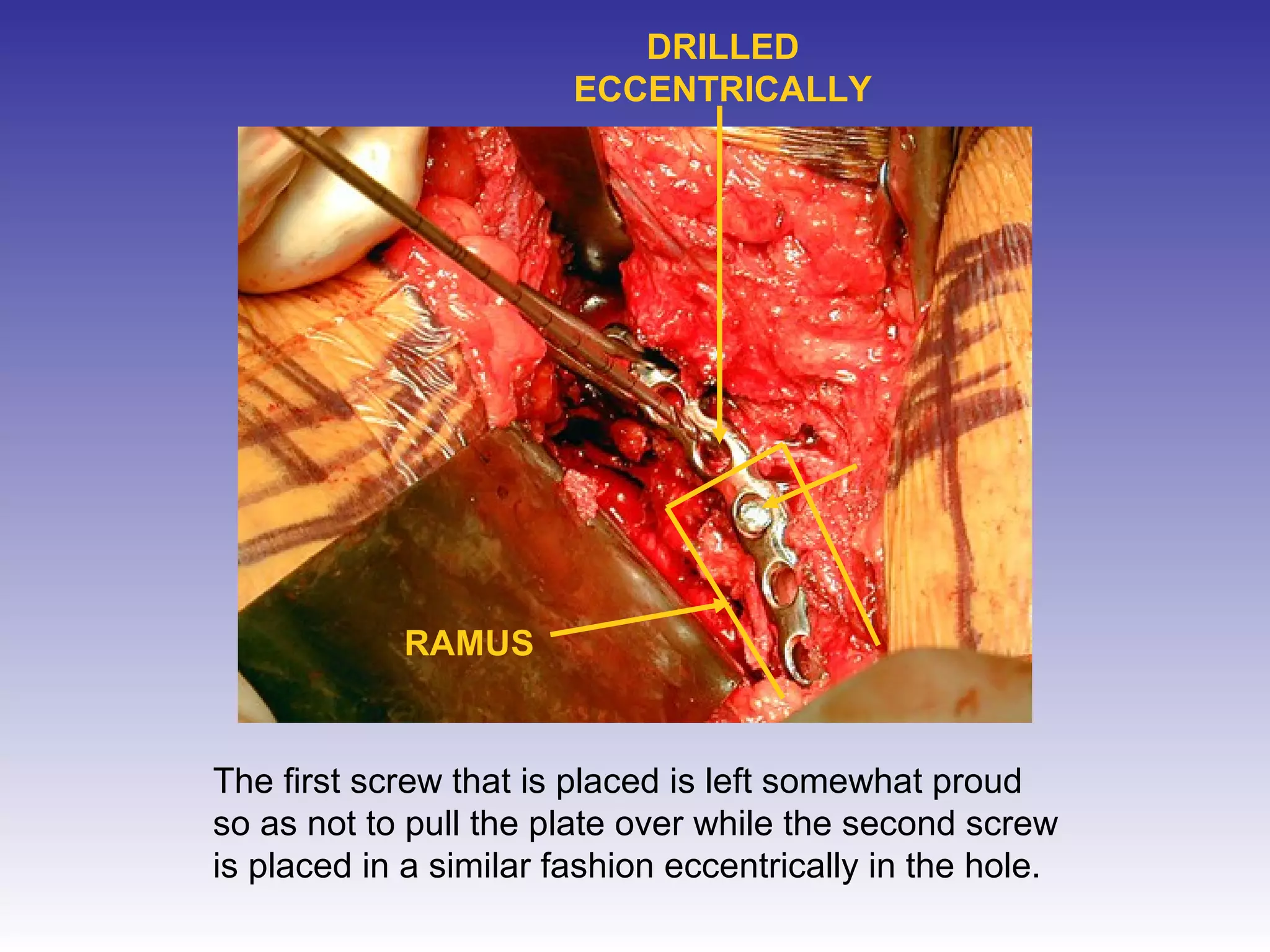
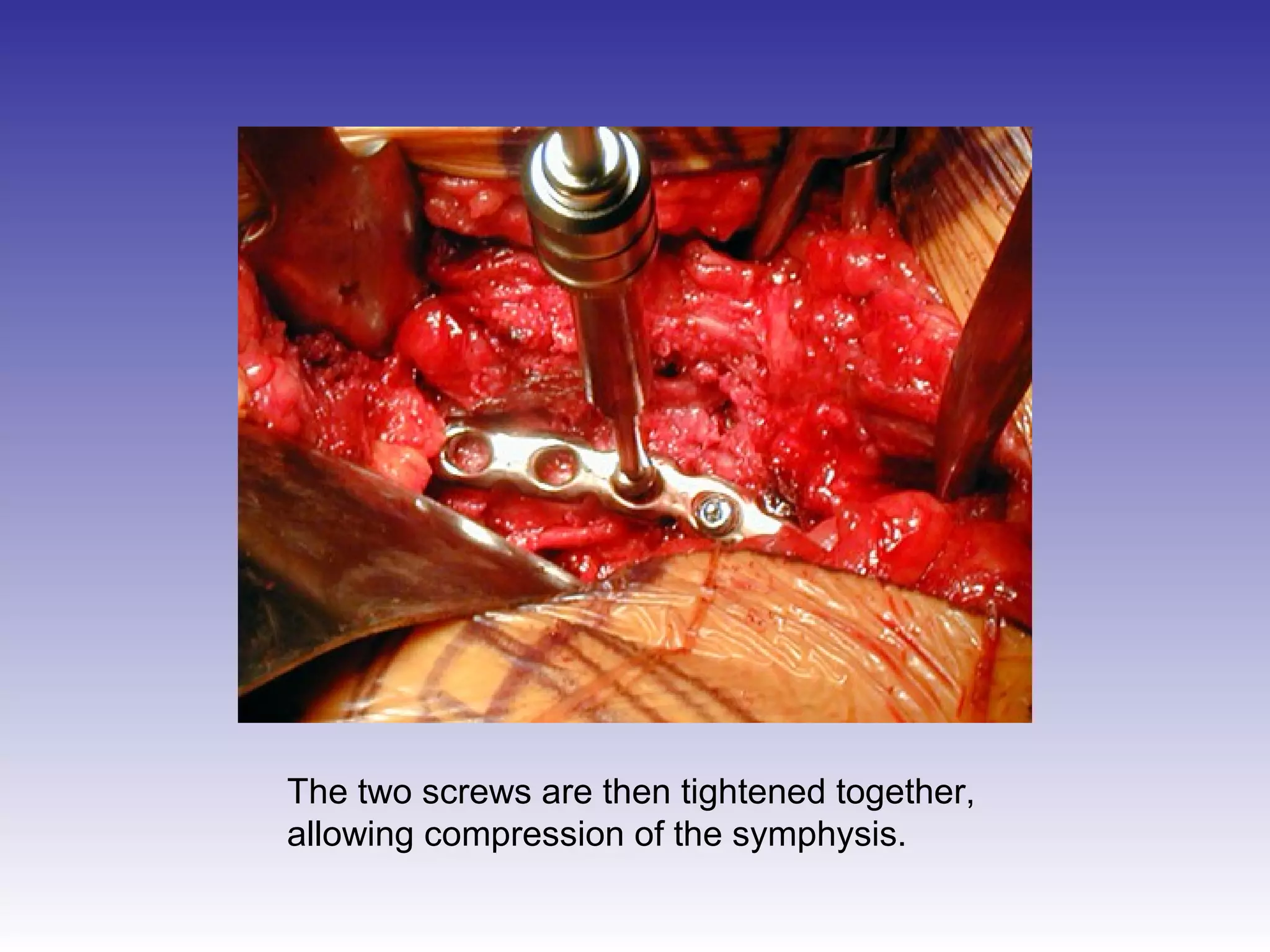
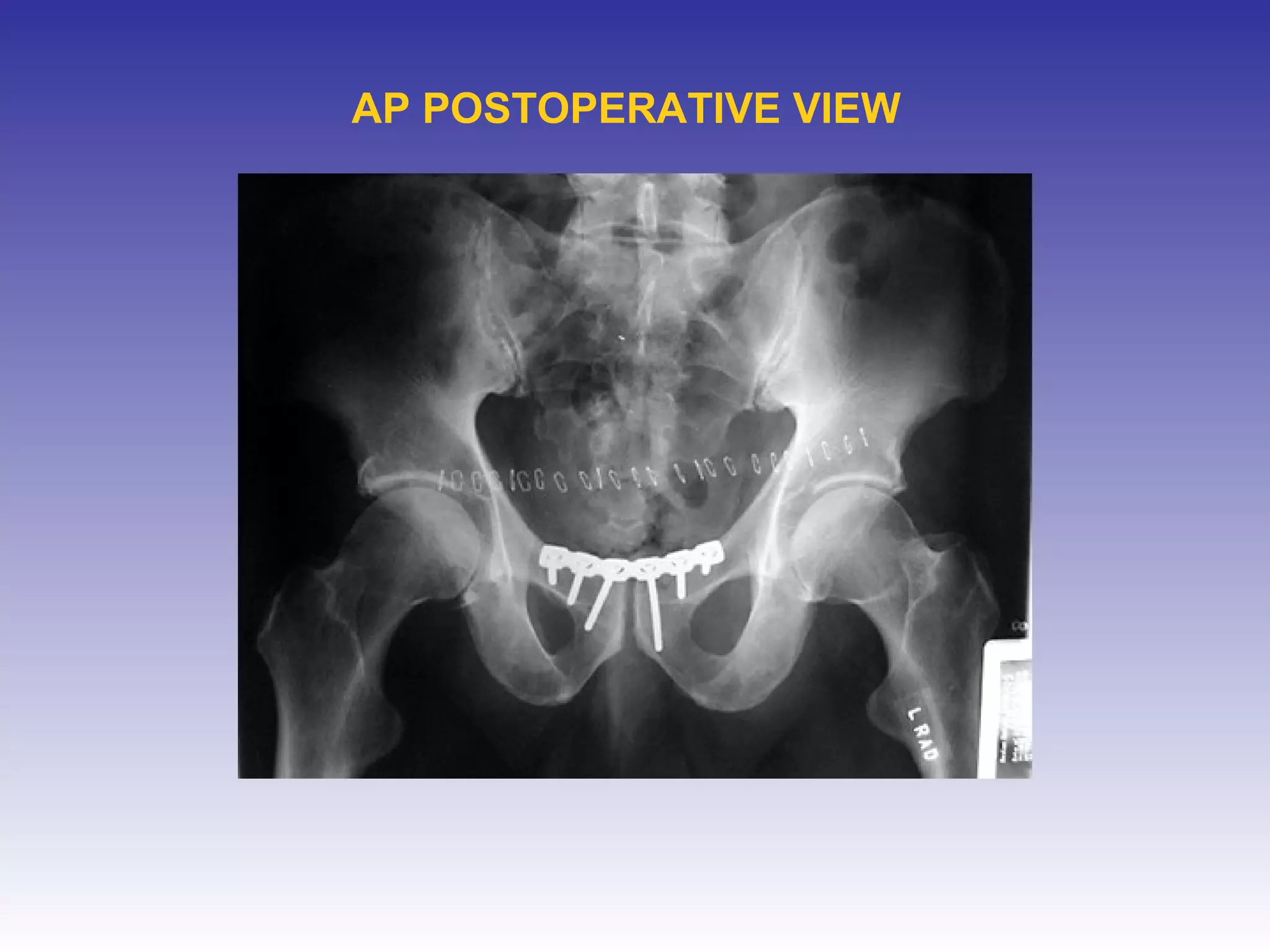
4) Placing a contoured metal plate and screws to stabilize the repaired symphysis.