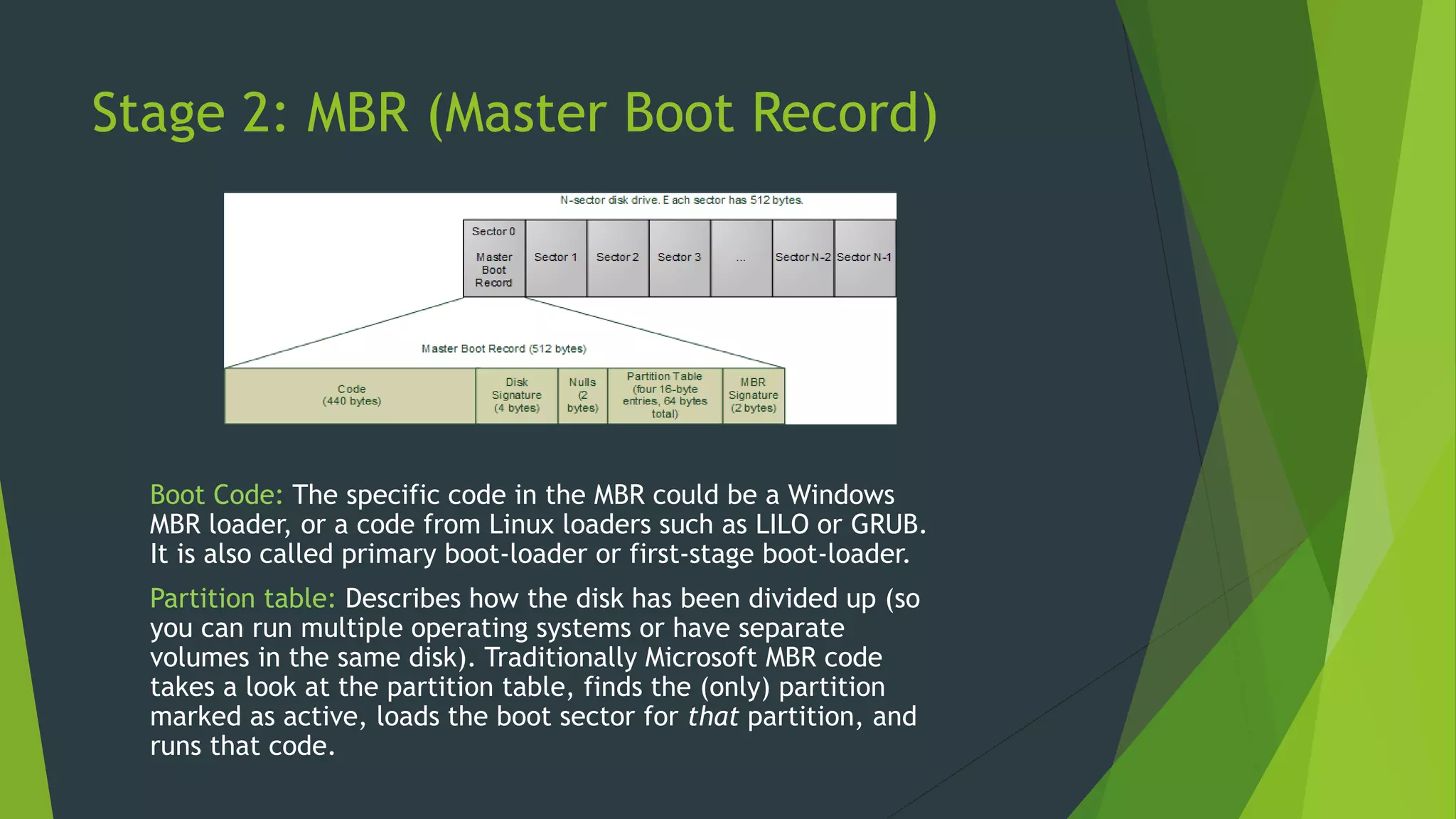
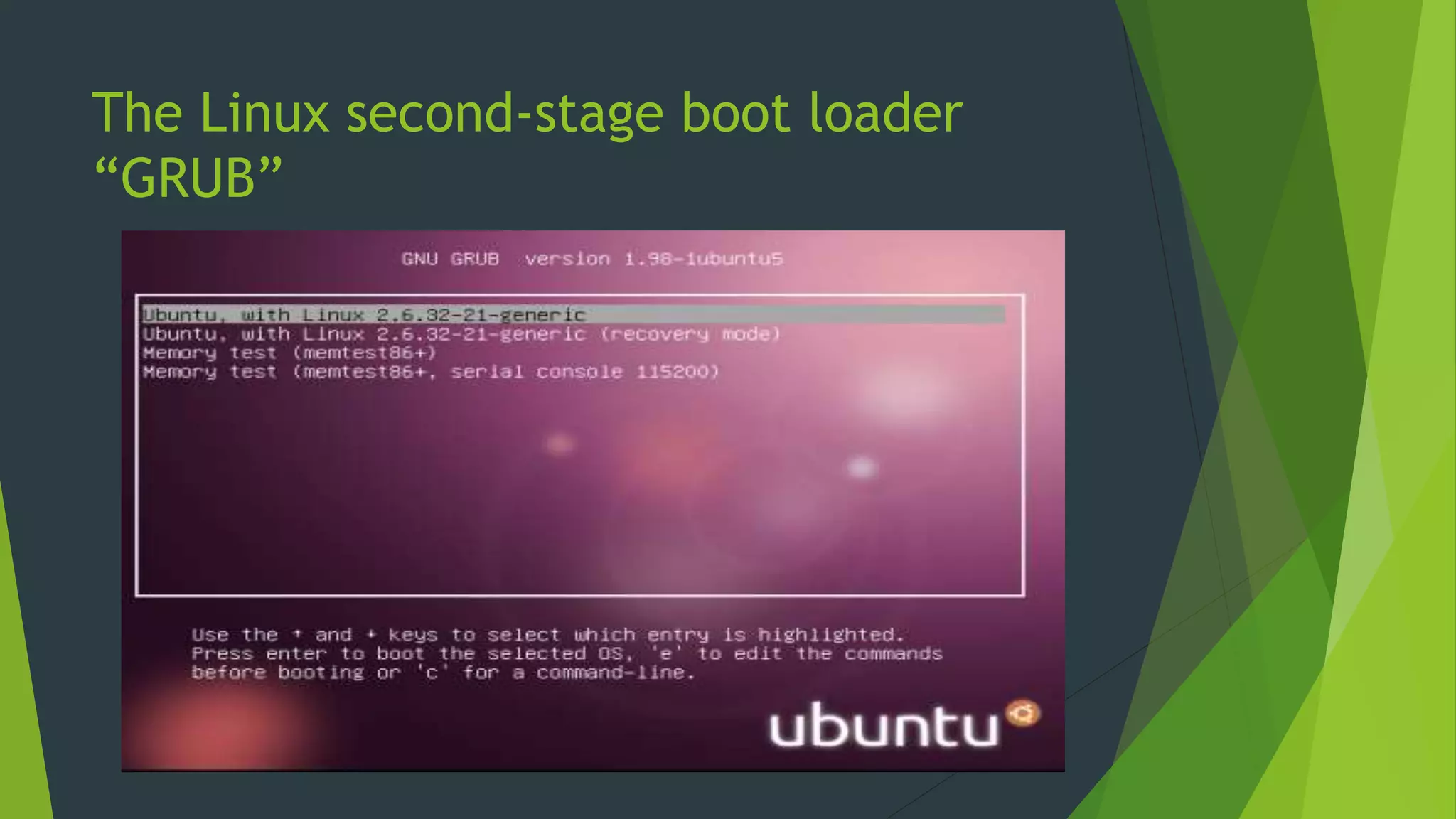
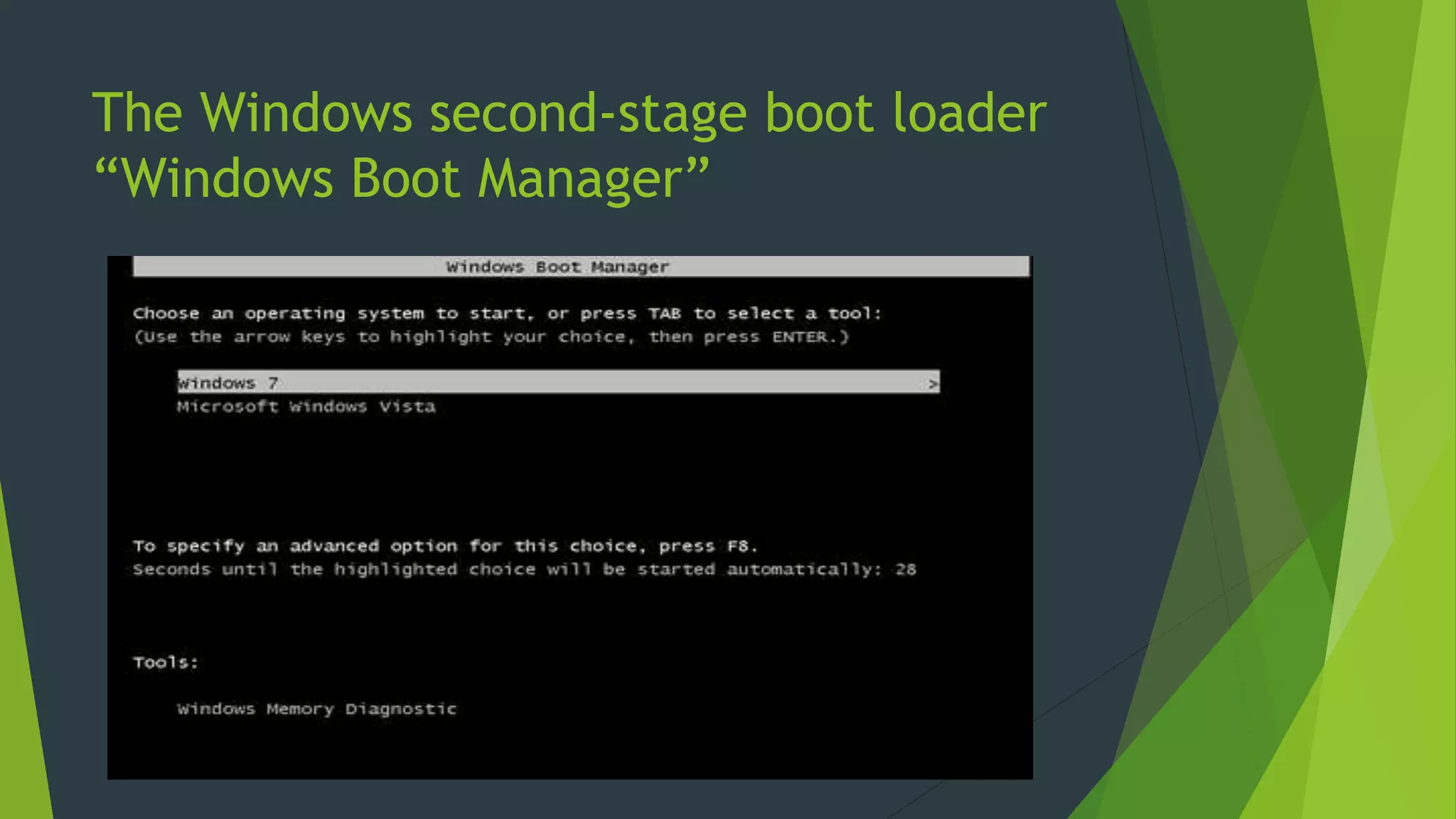
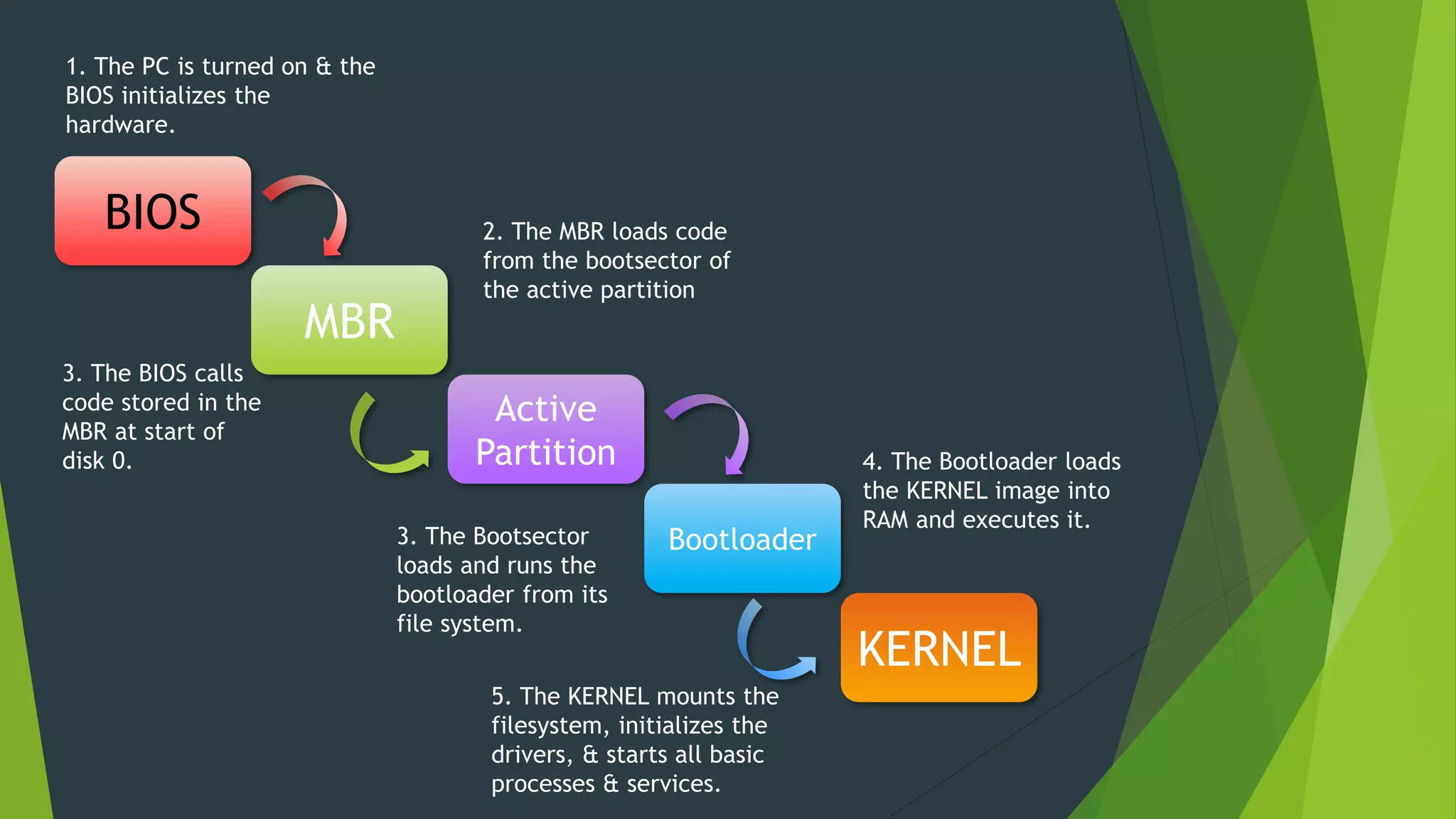
The document summarizes the boot process of an operating system. It begins with the BIOS executing code from the ROM chip and loading the master boot record (MBR) from the hard disk. The MBR then loads the volume boot record (VBR) from the active partition, which loads the second stage boot loader like NTLDR or GRUB. This boot loader then loads and executes the kernel, which initializes the filesystem and launches core processes.