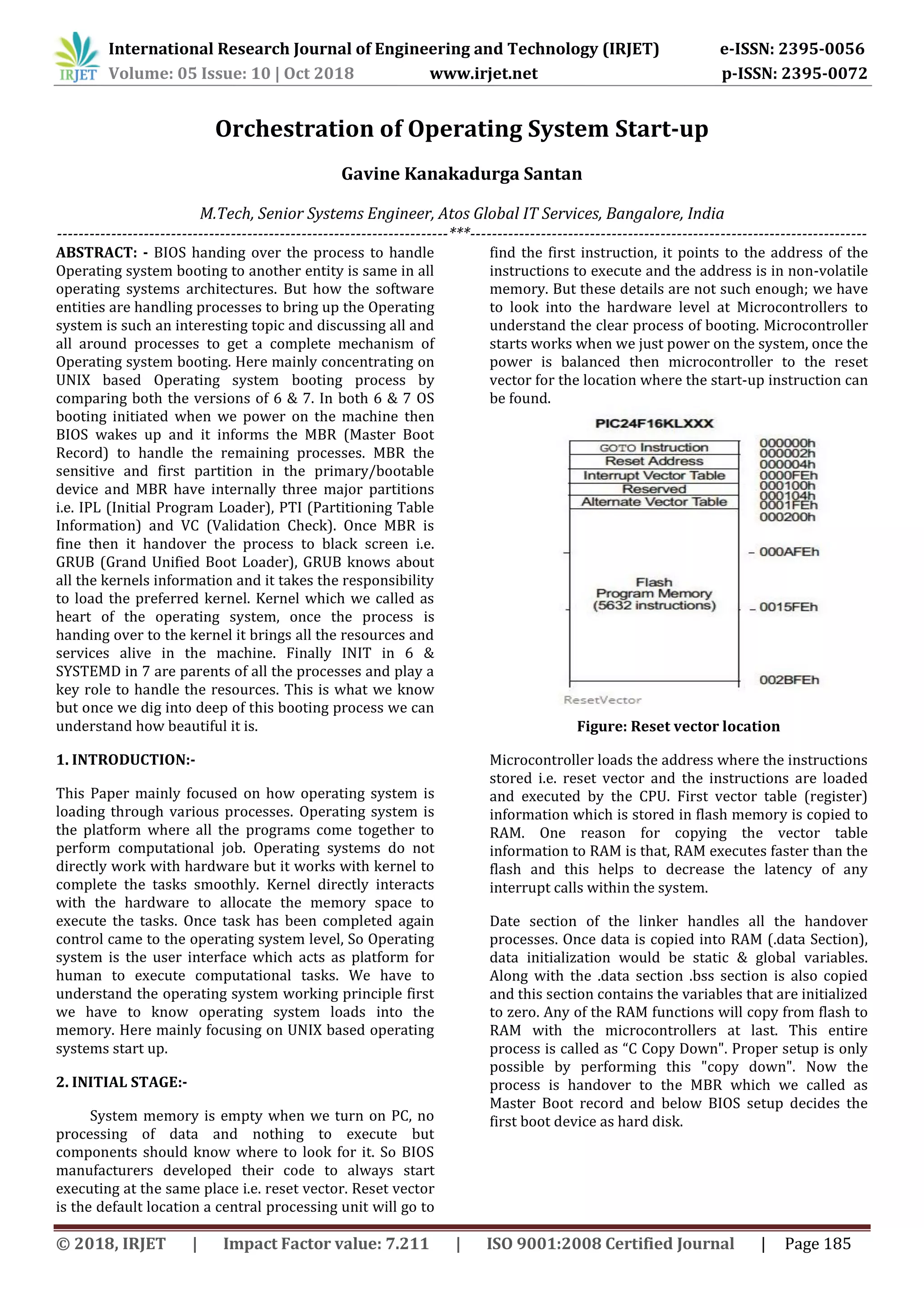
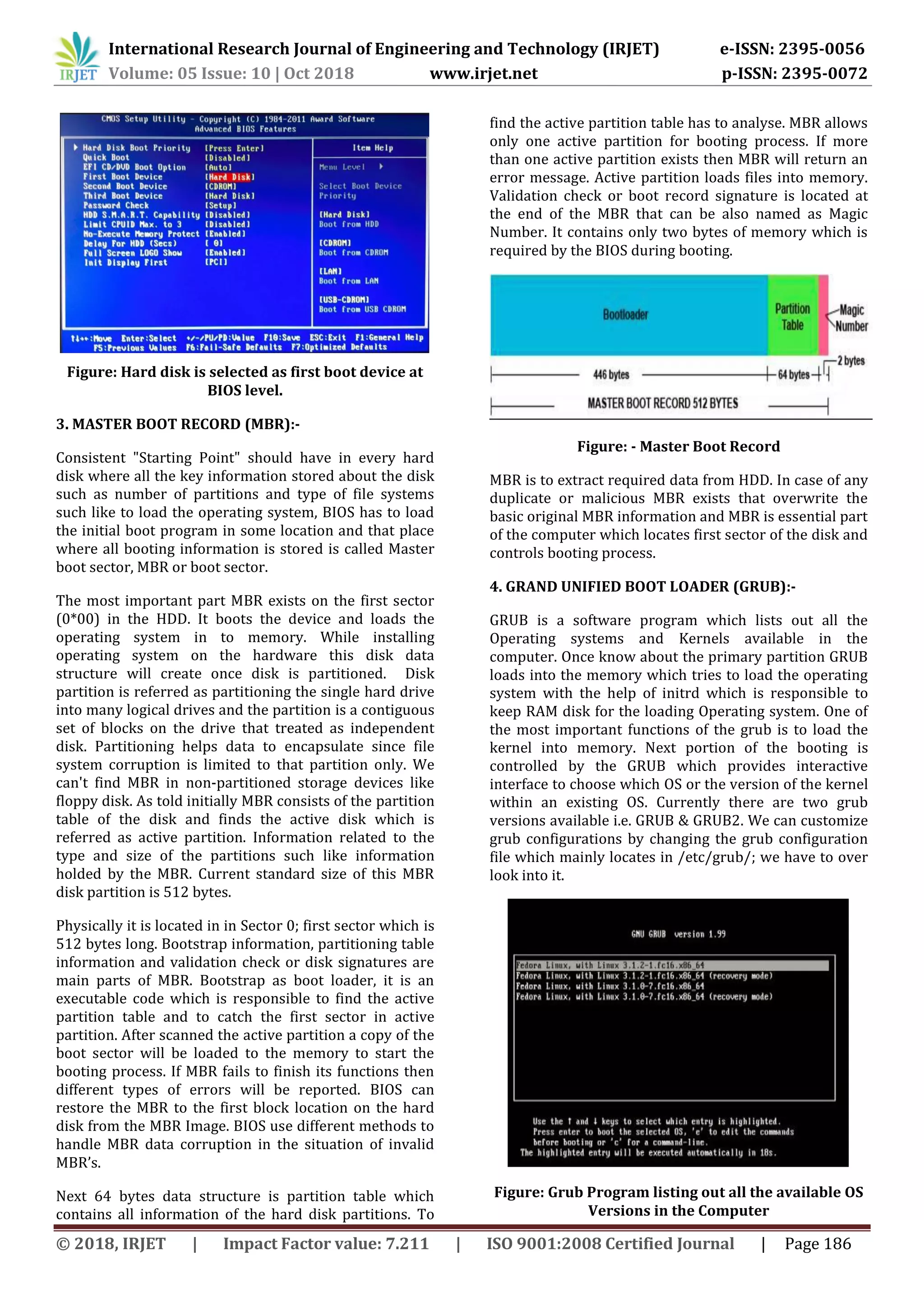
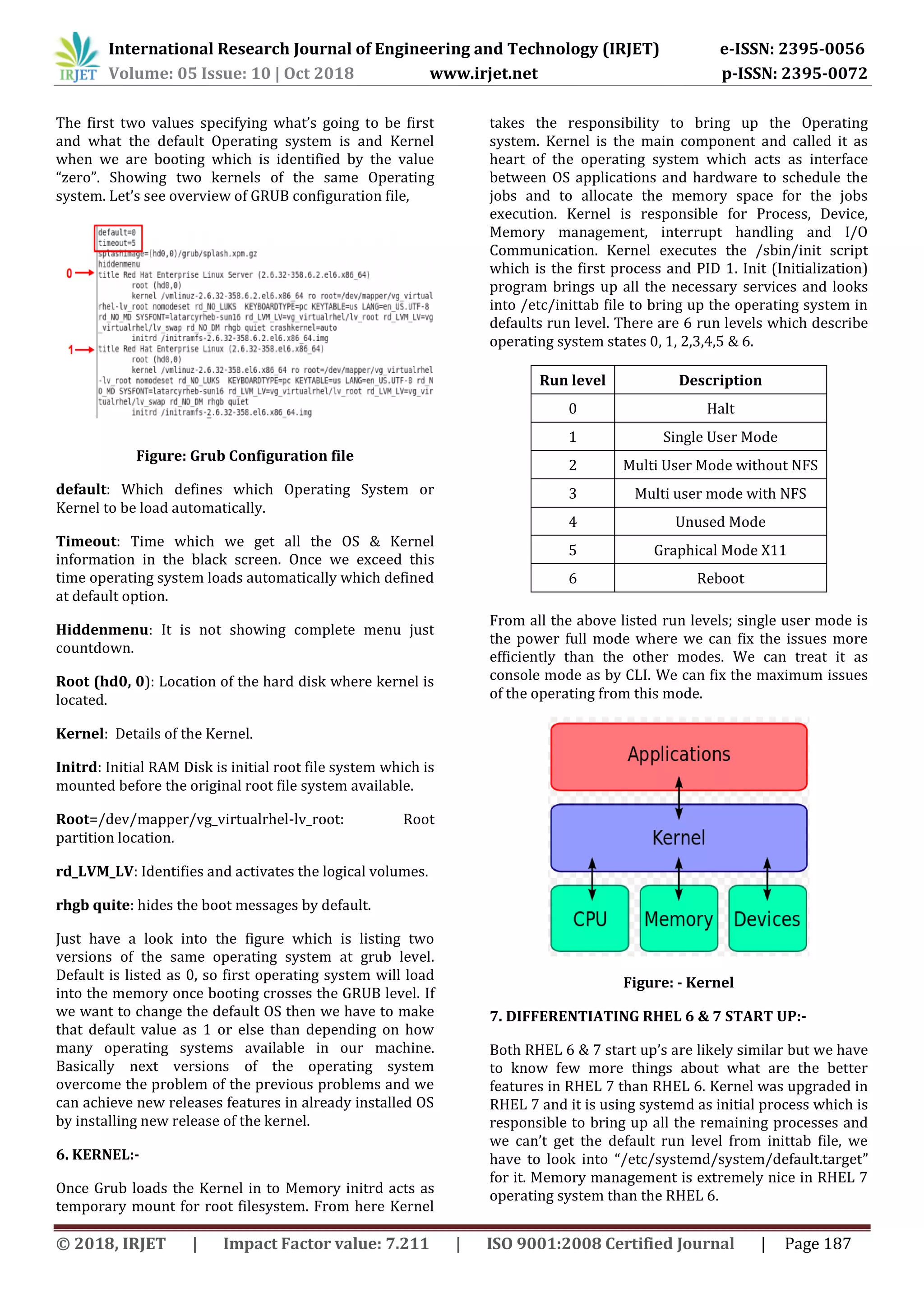
The document summarizes the startup process for UNIX-based operating systems like Red Hat Enterprise Linux versions 6 and 7. It describes how the BIOS hands over control at startup to the master boot record (MBR) on the hard disk, which then loads the boot loader GRUB. GRUB displays a menu to select the operating system and kernel version to load. The kernel is loaded into memory and initializes resources and services. In RHEL 6, the init process brings up the operating system, while in RHEL 7 systemd performs this role. The document provides details on each step in the boot sequence from the hardware level up through GRUB and kernel loading.