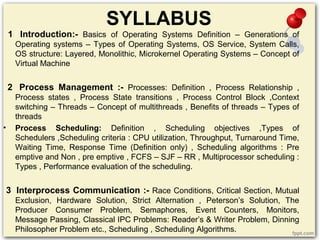
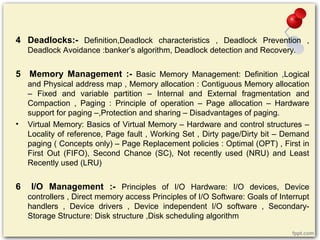
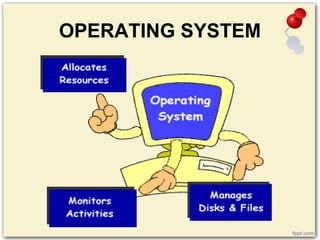
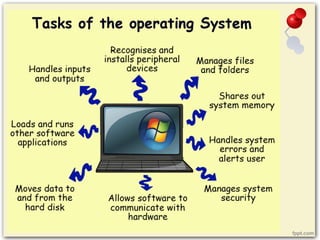
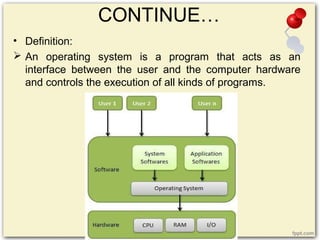
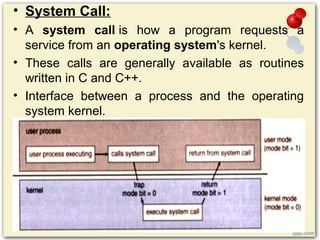
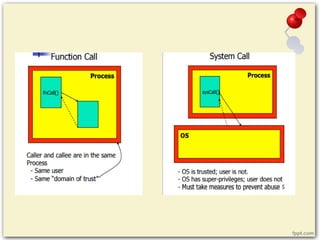
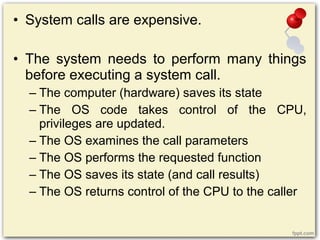
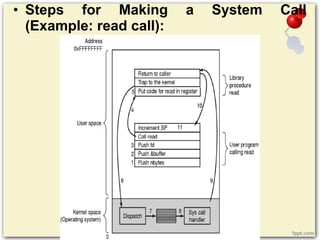
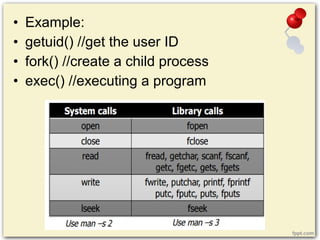
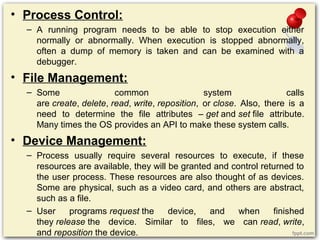
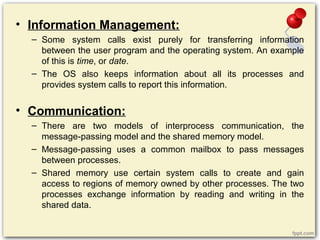
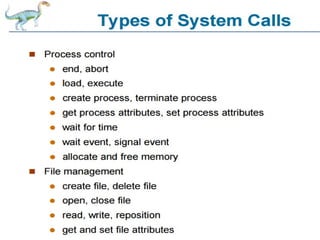
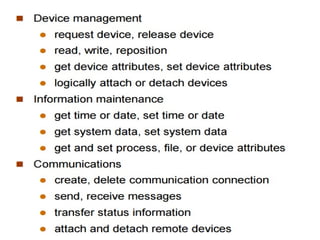
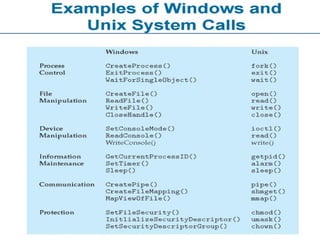
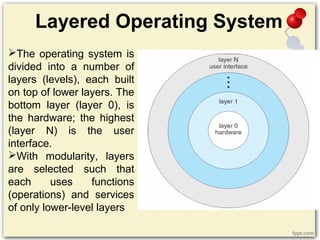
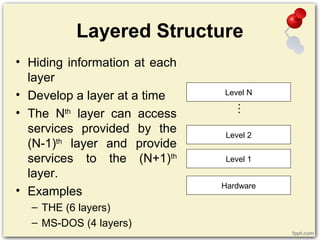
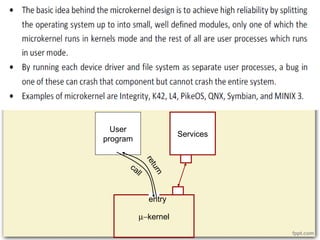
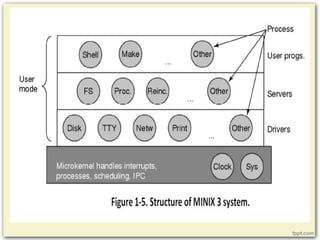
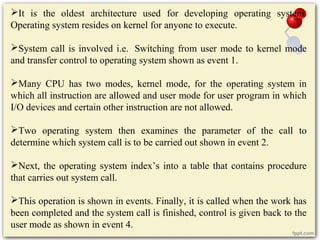
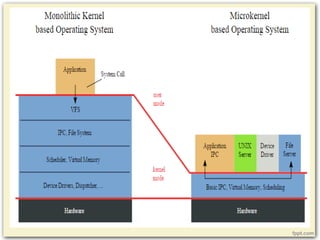
The document provides a comprehensive overview of operating systems, covering their definition, functions, types, and key components like process management, memory management, and file management. It discusses the evolution of operating systems, from early systems to modern types, including batch, multiprogramming, and real-time systems, along with their characteristics and advantages. Additionally, it outlines the services provided by operating systems and the role of system calls in facilitating communication between user programs and the OS.