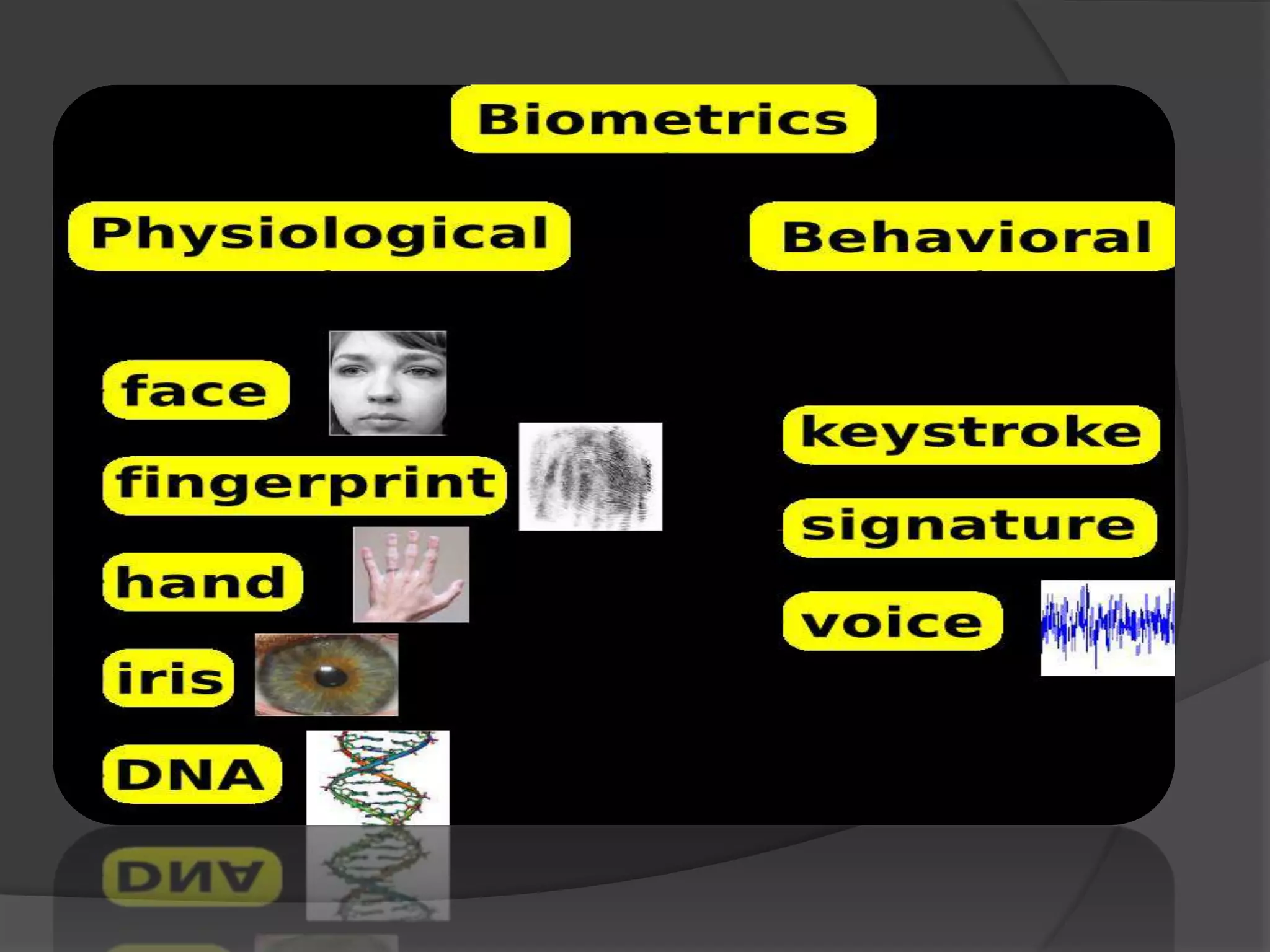
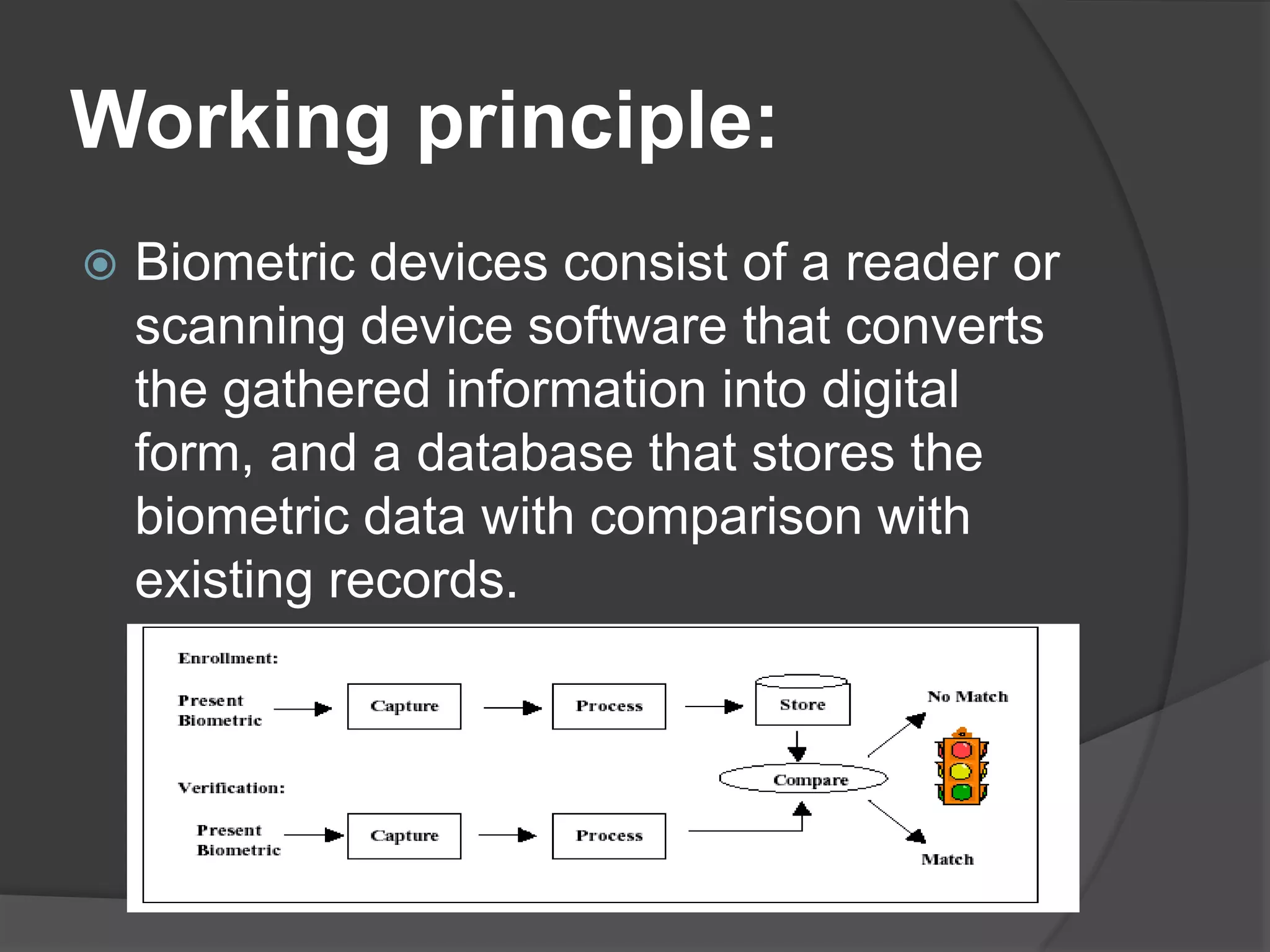
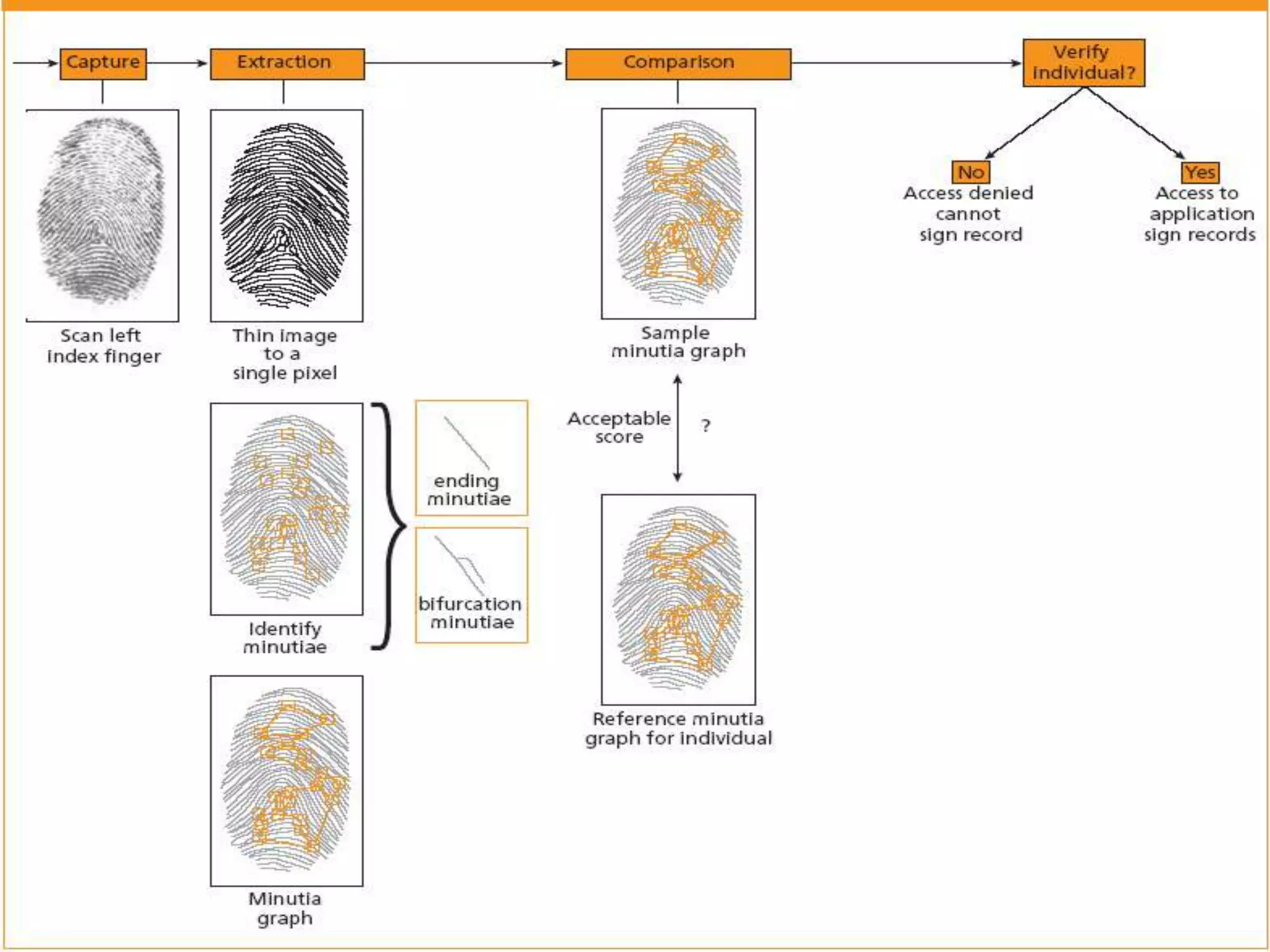
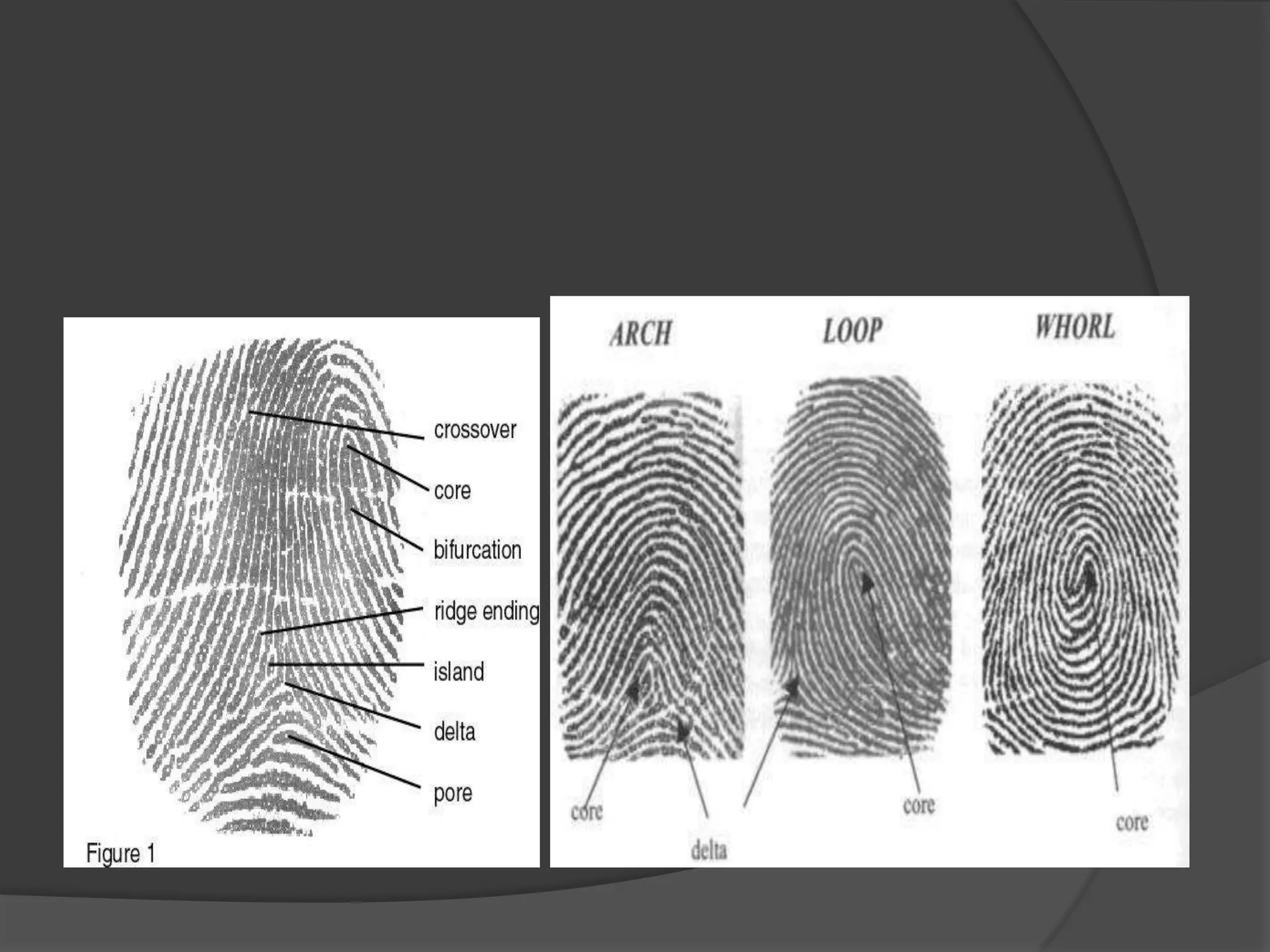
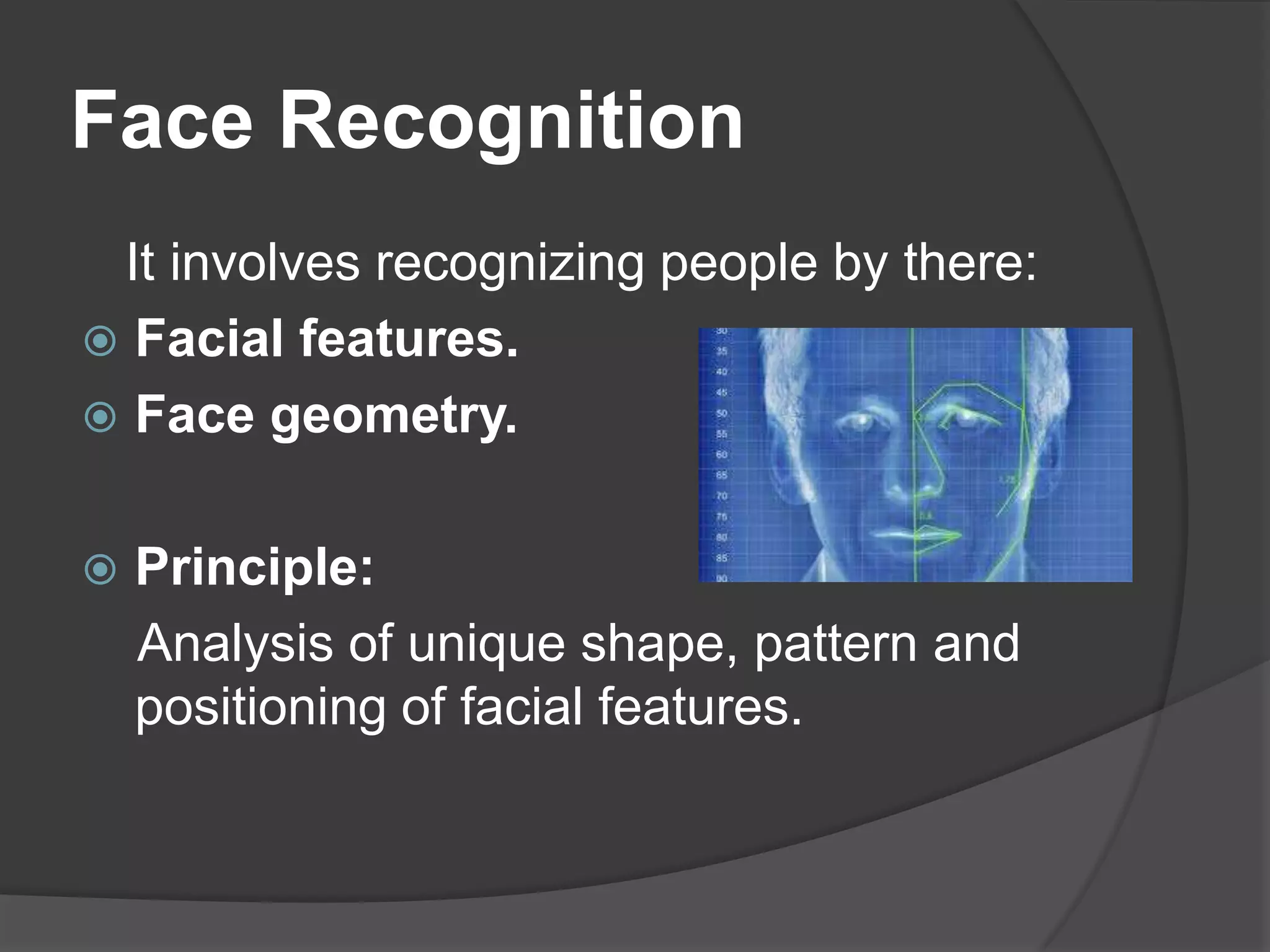
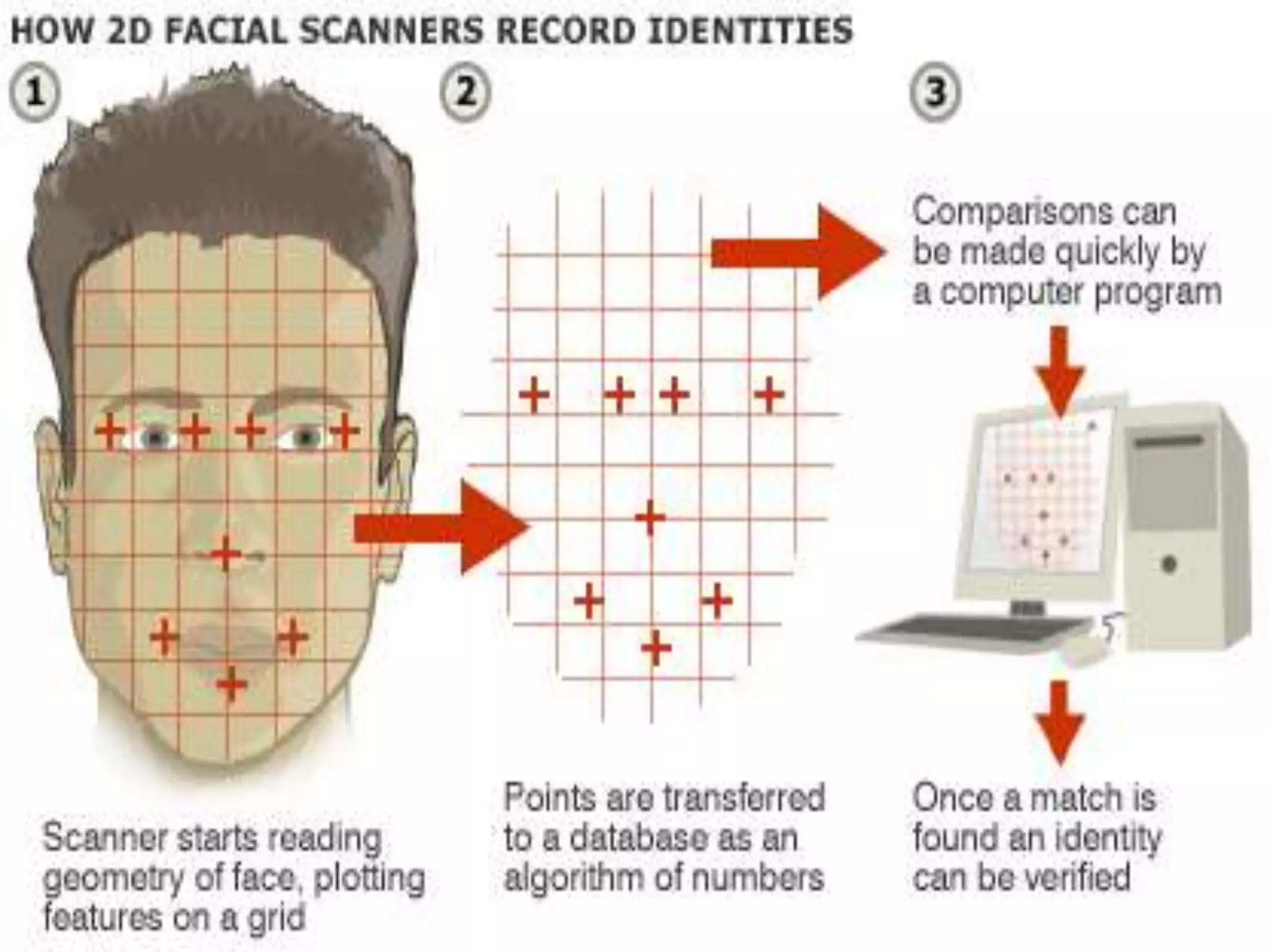
This document discusses biometrics, which uses human body characteristics for authentication purposes. It describes biometric devices that scan and digitize characteristics like fingerprints, irises, and facial patterns. Biometrics can be physiological (fingerprints, iris scans) or behavioral (signatures, voice). To work, characteristics must be universal, unique, and permanent for each individual. Biometric systems enroll users by storing their data, and then verify identities by matching live scans to enrolled data. Examples of biometric technologies discussed include fingerprint recognition, face recognition using facial features, voice recognition, iris recognition using iris patterns, and signature verification.