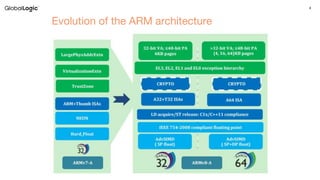
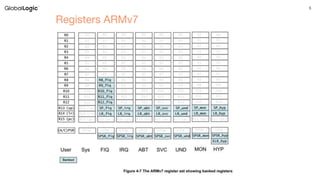
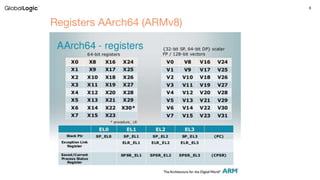
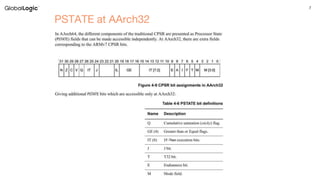
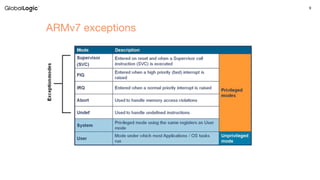
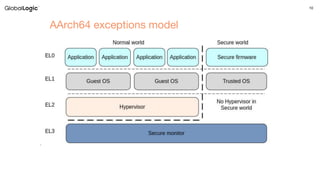
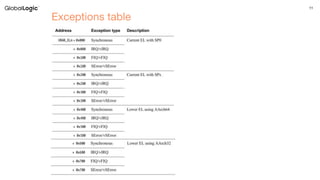
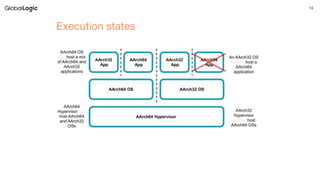
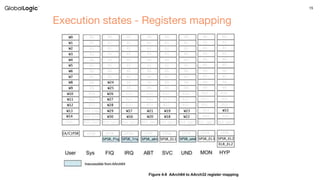
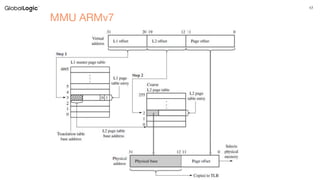
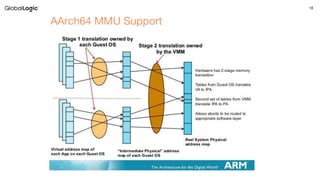
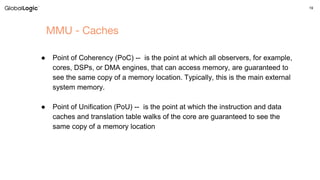
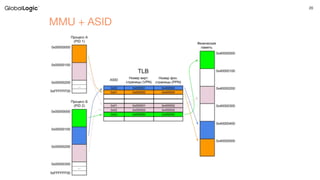
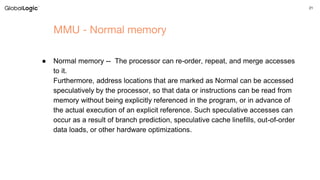
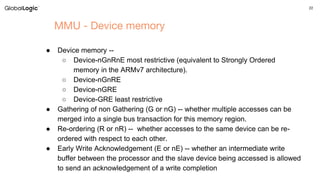
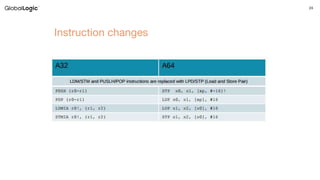
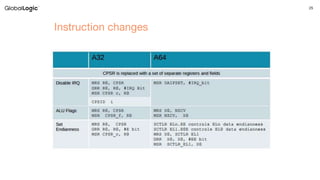
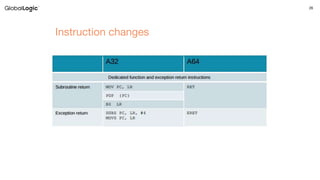
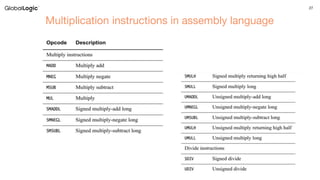
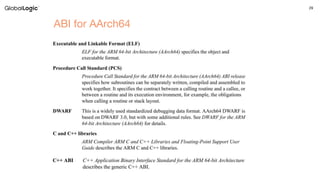
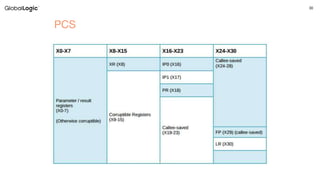
The document discusses ARM architecture focusing on kernel development, highlighting ARM's RISC design and separate instruction/data pathways. It covers registers, exception handling, memory management units (MMUs), and instruction specifics for both ARMv7 and ARMv8 architectures. Additionally, it includes references to ARM architecture manuals and provides contact information for further inquiries.