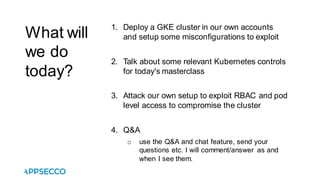
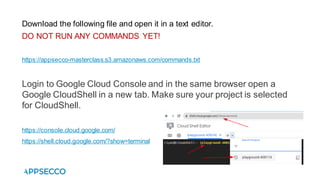
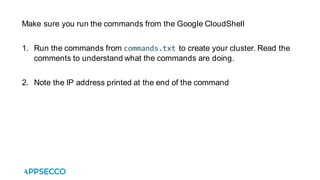
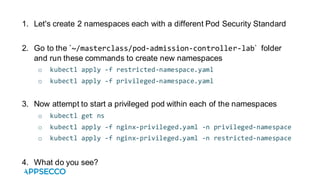
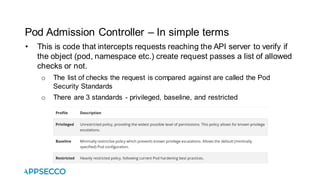
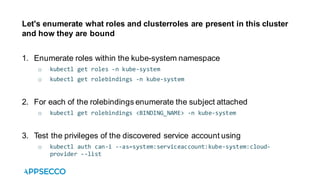
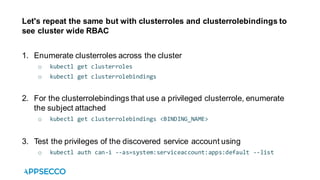
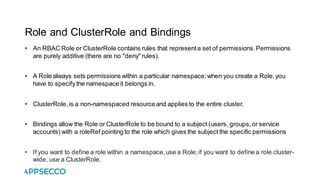
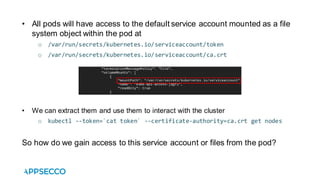
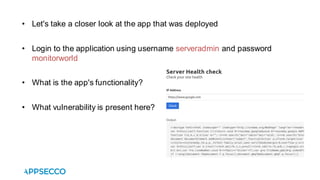
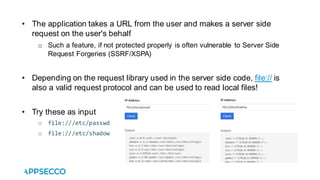
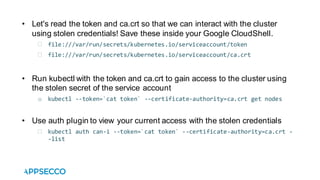
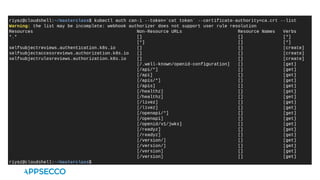
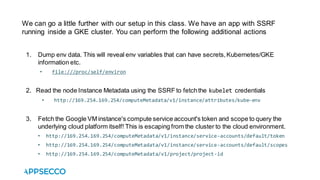
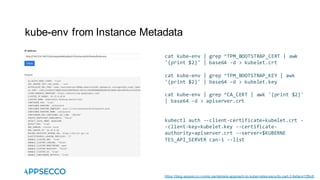
The document outlines a hands-on masterclass focused on deploying a Google Kubernetes Engine (GKE) cluster and exploring Kubernetes security controls, particularly related to Role-Based Access Control (RBAC) and Pod Security Admission. Participants learn to exploit misconfigurations for security assessments, including performing attacks and post-exploitation techniques on their setup. Additional resources and references are provided for further learning on Kubernetes security and the related services offered by Appsecco.