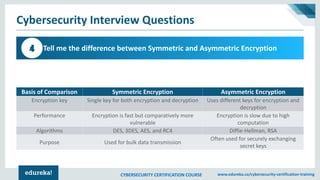
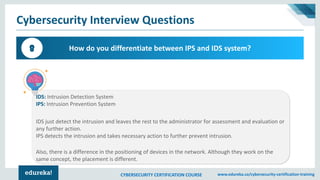
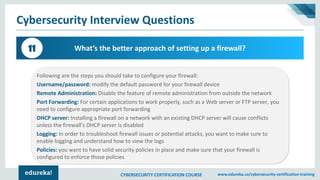
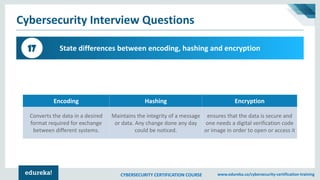
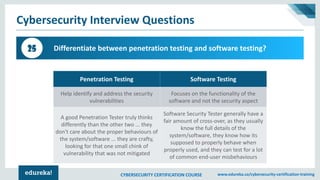
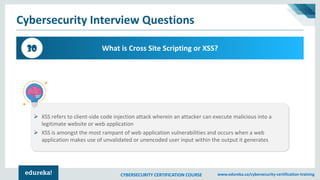
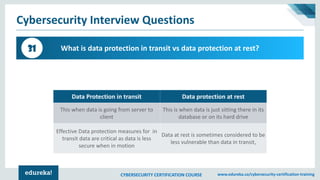
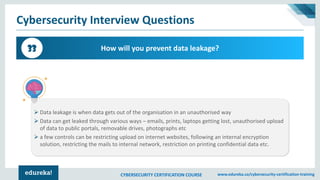
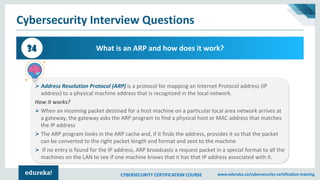
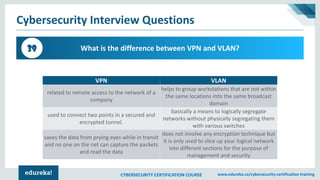
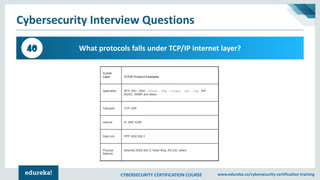
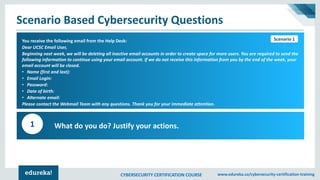
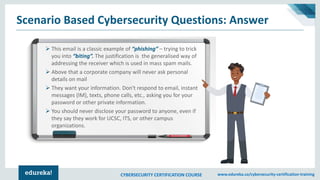
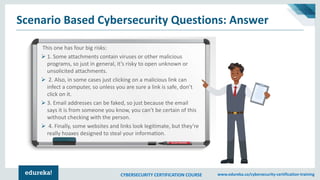
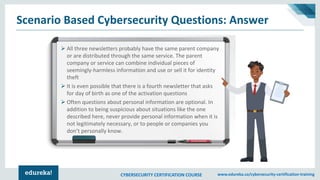
The document provides an overview of various cybersecurity topics, including definitions, protocols, frameworks, and attack prevention strategies. It covers key concepts such as encryption, identity theft prevention, firewall setup, and different types of hackers. Additionally, it addresses specific interview questions that explore the fundamentals and practical aspects of cybersecurity.