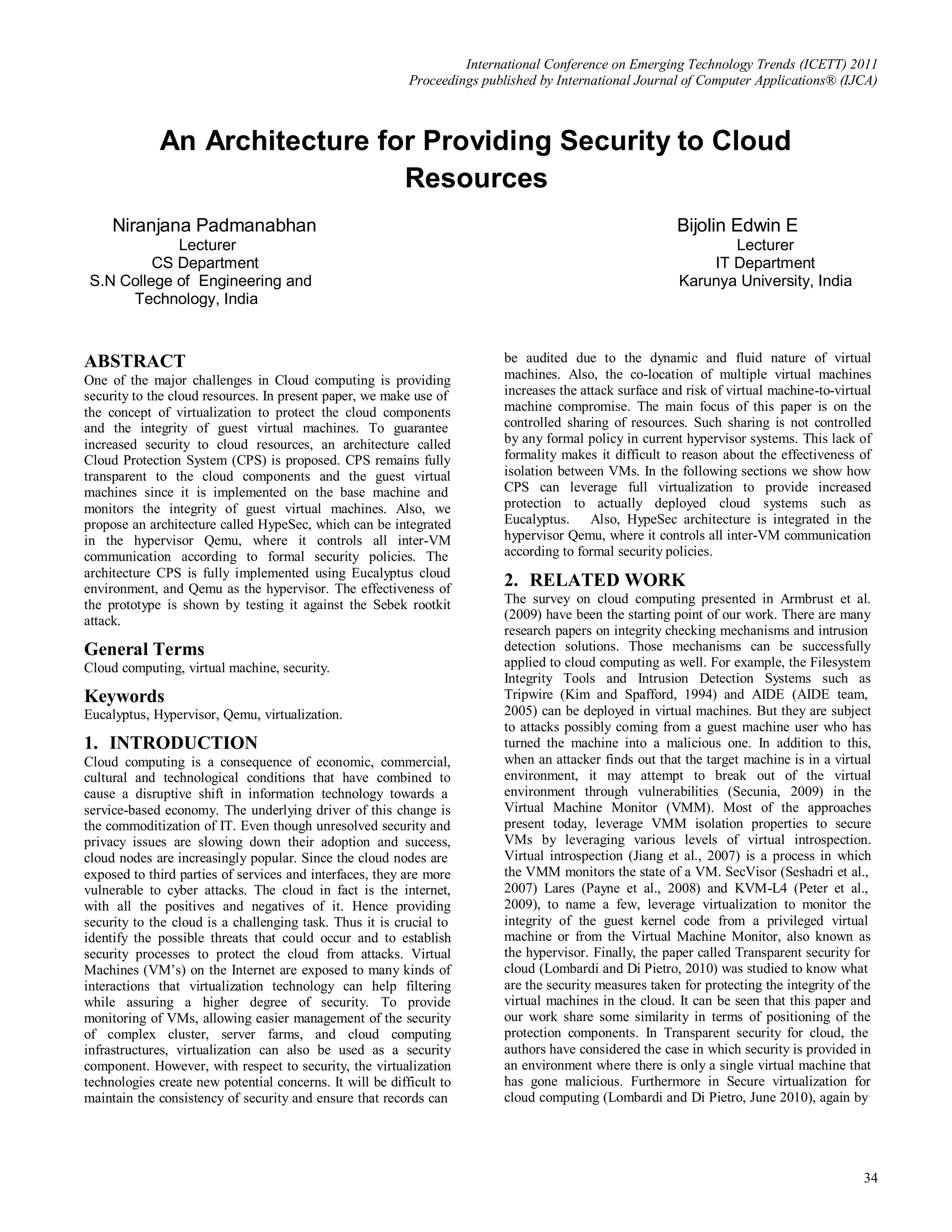
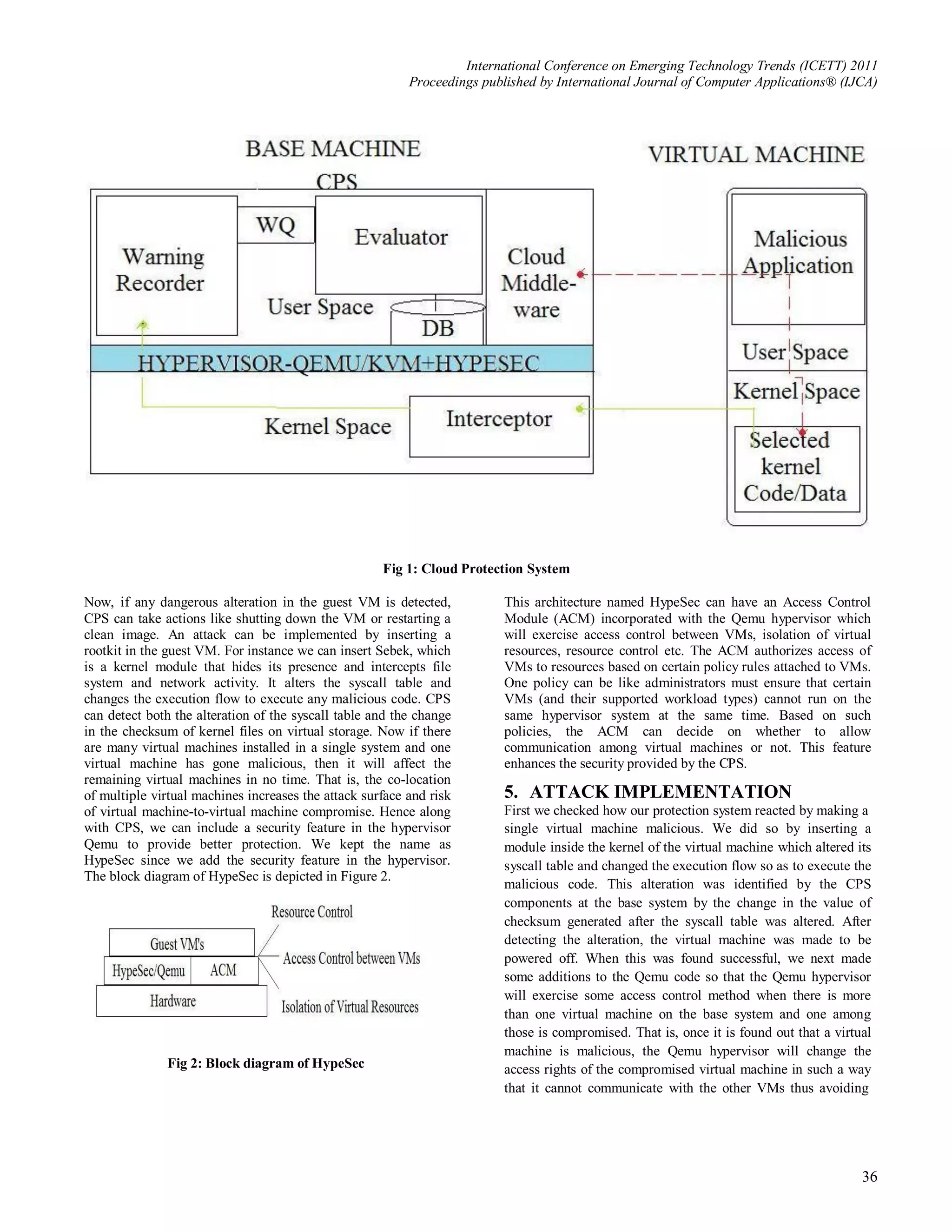
This document summarizes a paper presented at the International Conference on Emerging Technology Trends (ICETT) in 2011. The paper proposes an architecture called Cloud Protection System (CPS) to provide increased security to cloud resources using virtualization. CPS monitors the integrity of guest virtual machines in a cloud system like Eucalyptus. It also proposes HypeSec, which controls inter-VM communication in the Qemu hypervisor according to security policies. The effectiveness of CPS implemented in Eucalyptus is shown by testing against the Sebek rootkit attack.

![International Conference on Emerging Technology Trends (ICETT) 2011
Proceedings published by International Journal of Computer Applications® (IJCA)
the attack on the non malicious VMs. Then the compromised [3] Seshadri A, Luk M, Qu N, Perrig A. Secvisor: a tiny
virtual machine was made to be powered off in order to avoid it hypervisor to provide life time kernel code integrity for
from affecting the critical kernel code or data of the base system. commodity oses. In SOSP’07: Proceedings of twenty first
ACM SIGOPS symposium on operating systems principles,
This was done after the CPS components detected the change in
ACM, New York, NY, USA, 2007. p. 335–50.
the syscall table checksum of the malicious VM. There is of
course a small amount of overhead introduced by this technique [4] Payne BD, Carbone M, Sharif M, Lee W. Lares: An
architecture for secure active monitoring using
but compared with the detection capability of our system, it can
virtualization. In SP ’08: Proceedings of the 2008 IEEE
be neglected. symposium on security and privacy (sp2008), IEEE
Computer Society, Washington, DC, USA, 2008. pp. 233-
6. CONCLUSION 47.
In this paper, we have introduced an architecture named Cloud [5] Lombardi F, Di Pietro R. Kvmsec: a security extension for
Protection System that can provide security to the cloud linux kernel virtual machines. In SAC ’09: Proceedings of
resources via virtualization. CPS monitors the guest and the the 2009 ACM symposium on applied Computing, ACM,
middleware components and ensures that the integrity has not New York, NY, USA, 2009. pp. 2029–34.
been compromised. To enhance the security provided, HypeSec
architecture is proposed which is integrated along with the [6] Qumranet. Linux kernel virtual machine.
hypervisor Qemu. CPS combined with HypeSec can be http://kvm.qumranet.com.
deployed on any cloud implementation. Our protection system [7] Peter M, Schild H, Lackorzynski A, Warg A. Virtual
ensures that the integrity of the virtual machines is not machines jailed: virtualization in systems with small trusted
compromised. computing bases. In VDTS ’09: Proceedings of the 1st
EuroSys Workshop on virtualization technology for
7. ACKNOWLEDGMENTS dependable systems, ACM, New York, NY, USA, 2009.
Our thanks to the experts who have contributed towards the p.18–23.
development of this paper. [8] Rhee J, Riley R, Xu D, Jiang X. Defeating dynamic data
kernel rootkit attacks via vmm-based guest transparent
8. REFERENCES monitoring. Availability, Reliability and Security, 2009.
[1] Armbrust M, Fox A, Griffith R. Above the clouds: A ARES ’09.
Berkeley view of cloud computing. Technical Report [9] Lombardi F, Di Pietro R. Transparent security for cloud. In
UCB/EECS-2009-28, EECS Department, University of SAC’10: Proceedings of the 2010 ACM symposium on
California, Berkeley, February 2009. applied computing.
[2] Bellard F. Qemu, a fast and portable dynamic translator. In [10] Lombardi F, Di Pietro R. Secure virtualization for cloud
ATEC ’05: Proceedings of the annual conference on computing. In Elsevier, June 2010: Journal of Network and
USENIX annual technical conference, Berkeley, CA, USA, Computer Applications.
2005. USENIX Association, p. 41.
37](https://image.slidesharecdn.com/icett014-111216004053-phpapp02/75/An-Architecture-for-Providing-Security-to-Cloud-Resources-4-2048.jpg)