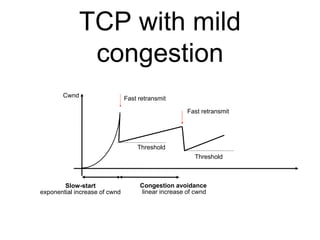
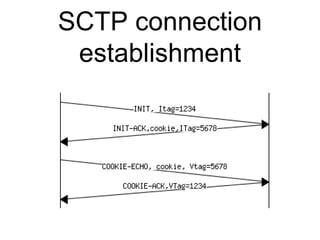
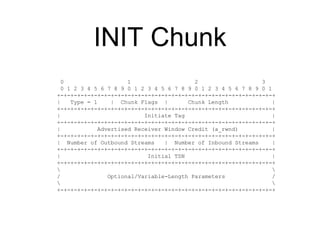
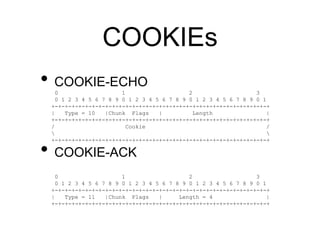
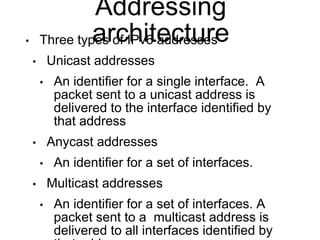
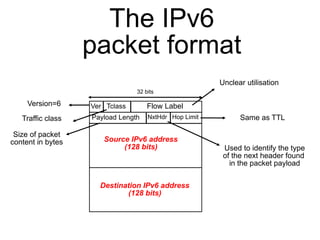
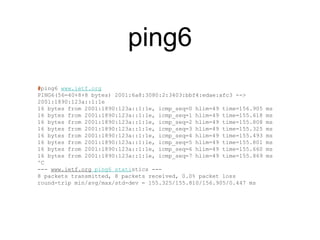
This document discusses several topics related to Internet protocols including congestion control using TCP, Explicit Congestion Notification, Stream Control Transmission Protocol (SCTP), and IPv6. It provides details on TCP congestion control using Additive Increase Multiplicative Decrease (AIMD), SCTP segments and connection establishment, IPv6 addressing architecture, and ICMPv6 functions like ping6 and traceroute6.