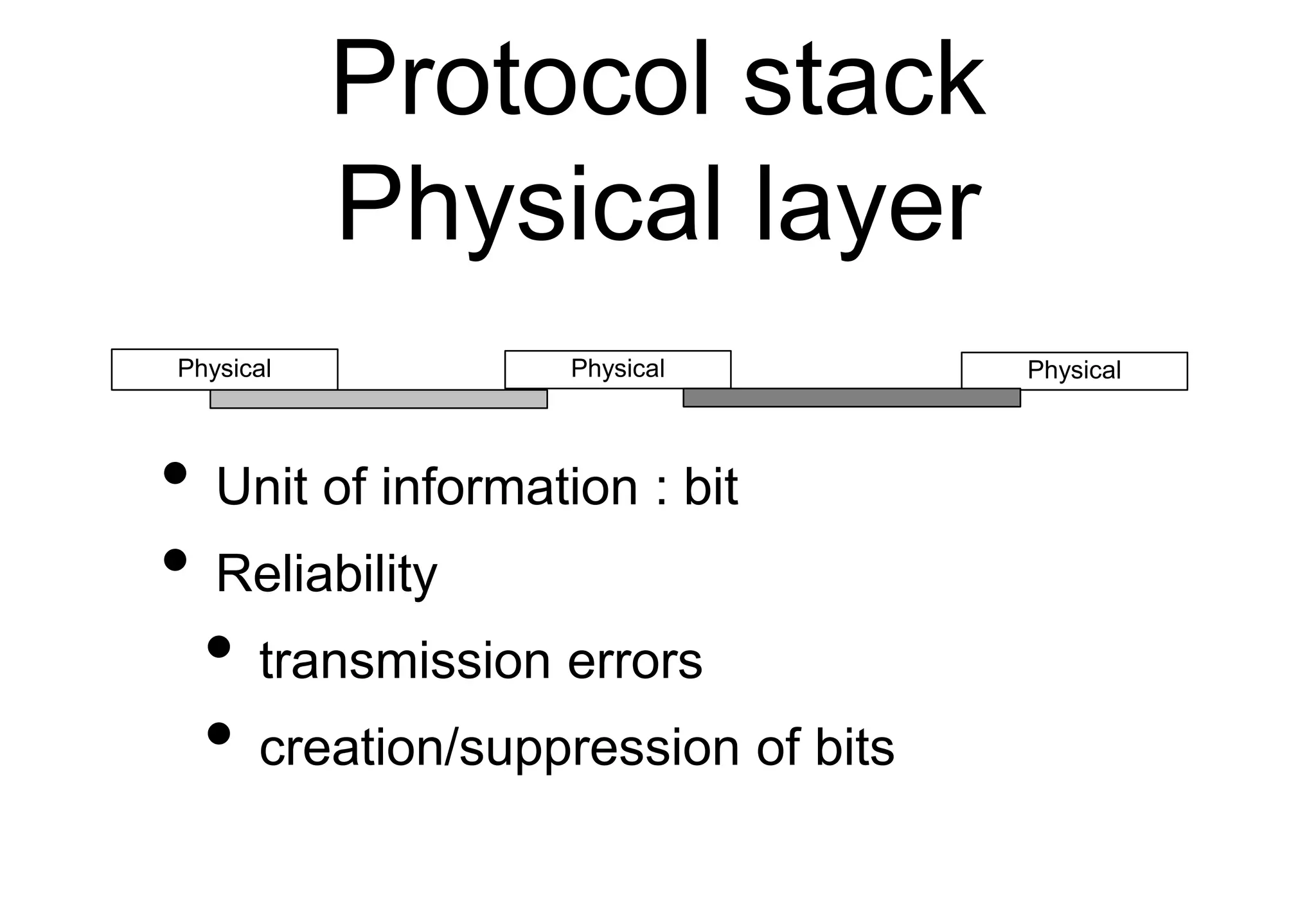
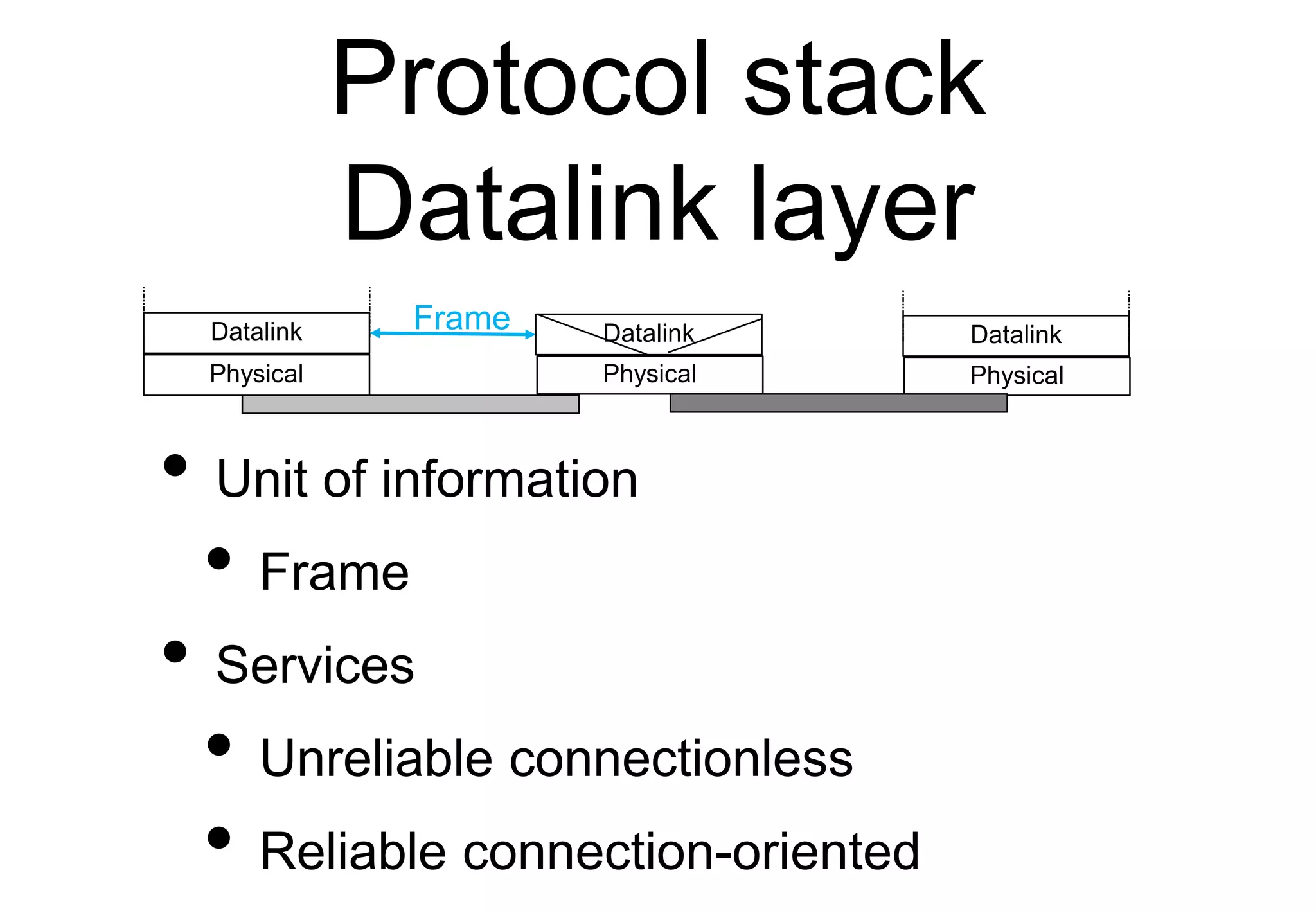
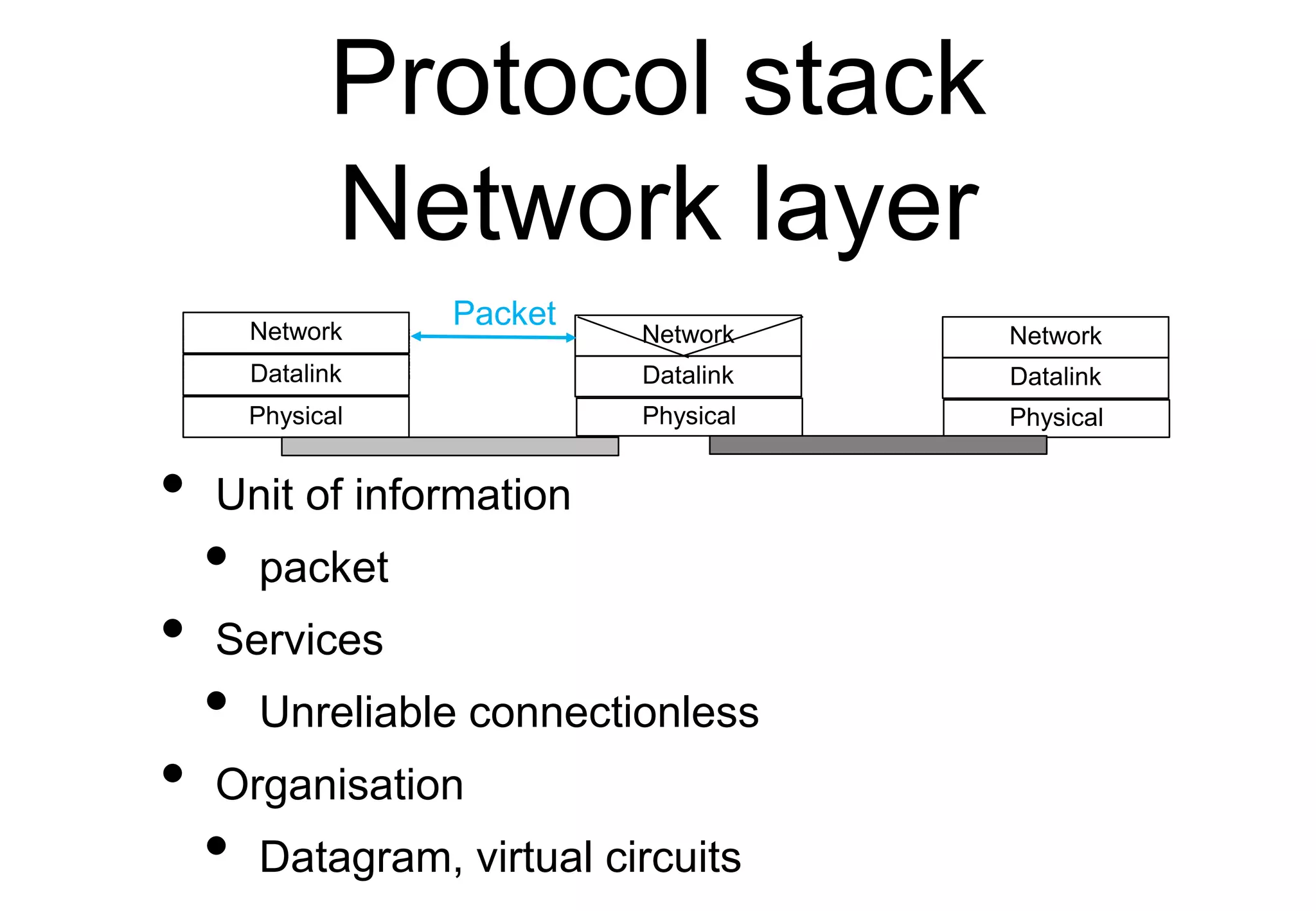
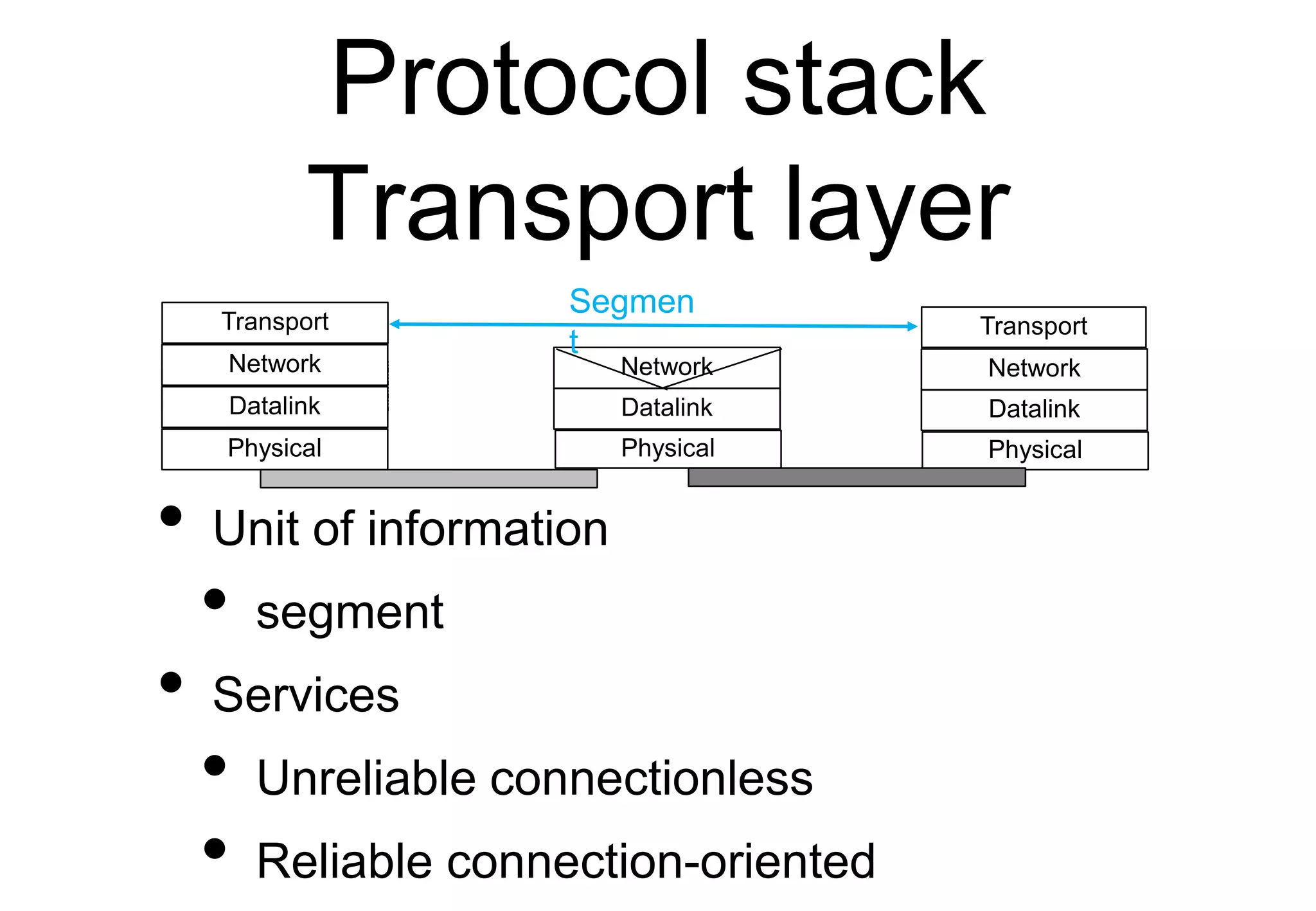
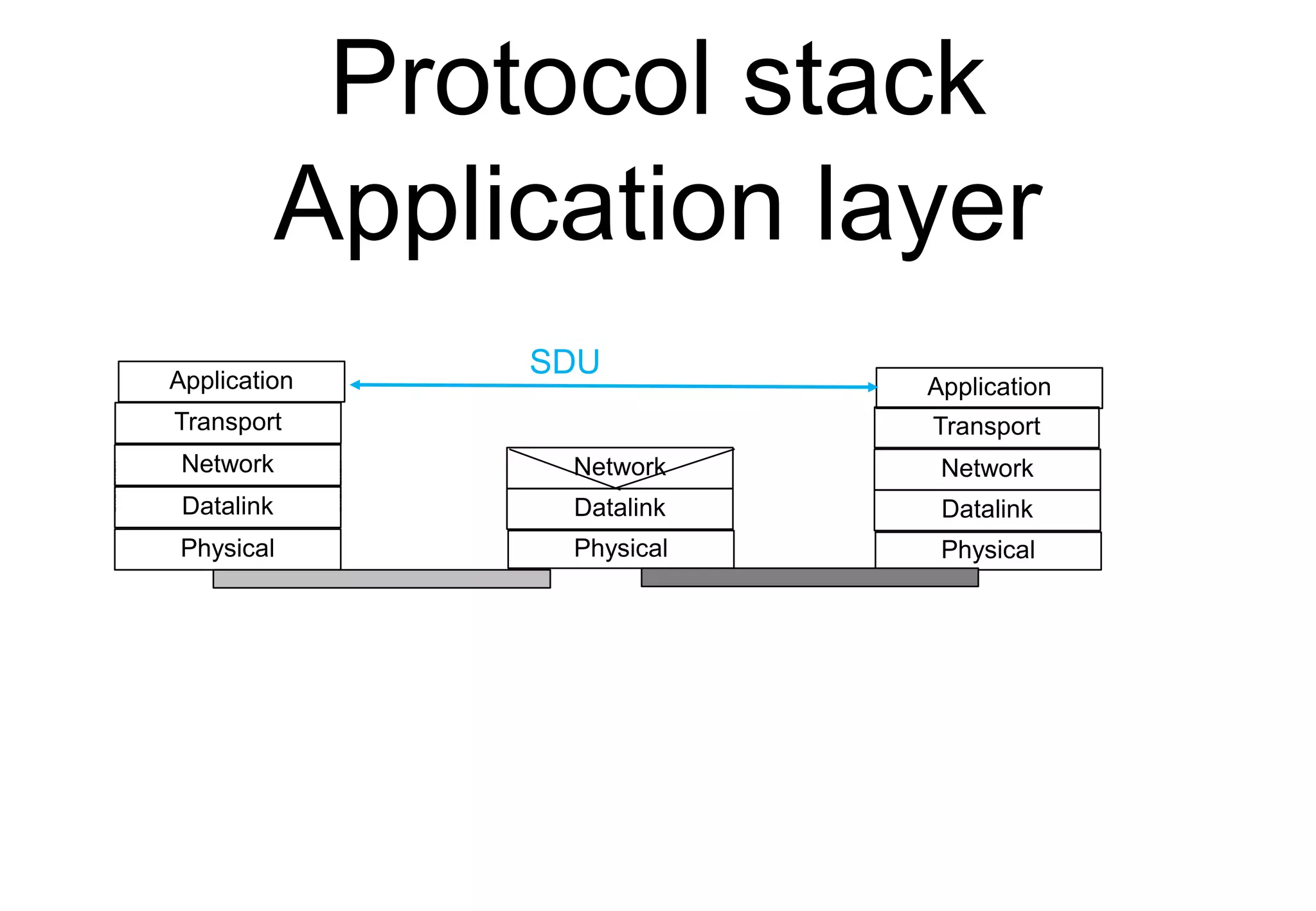
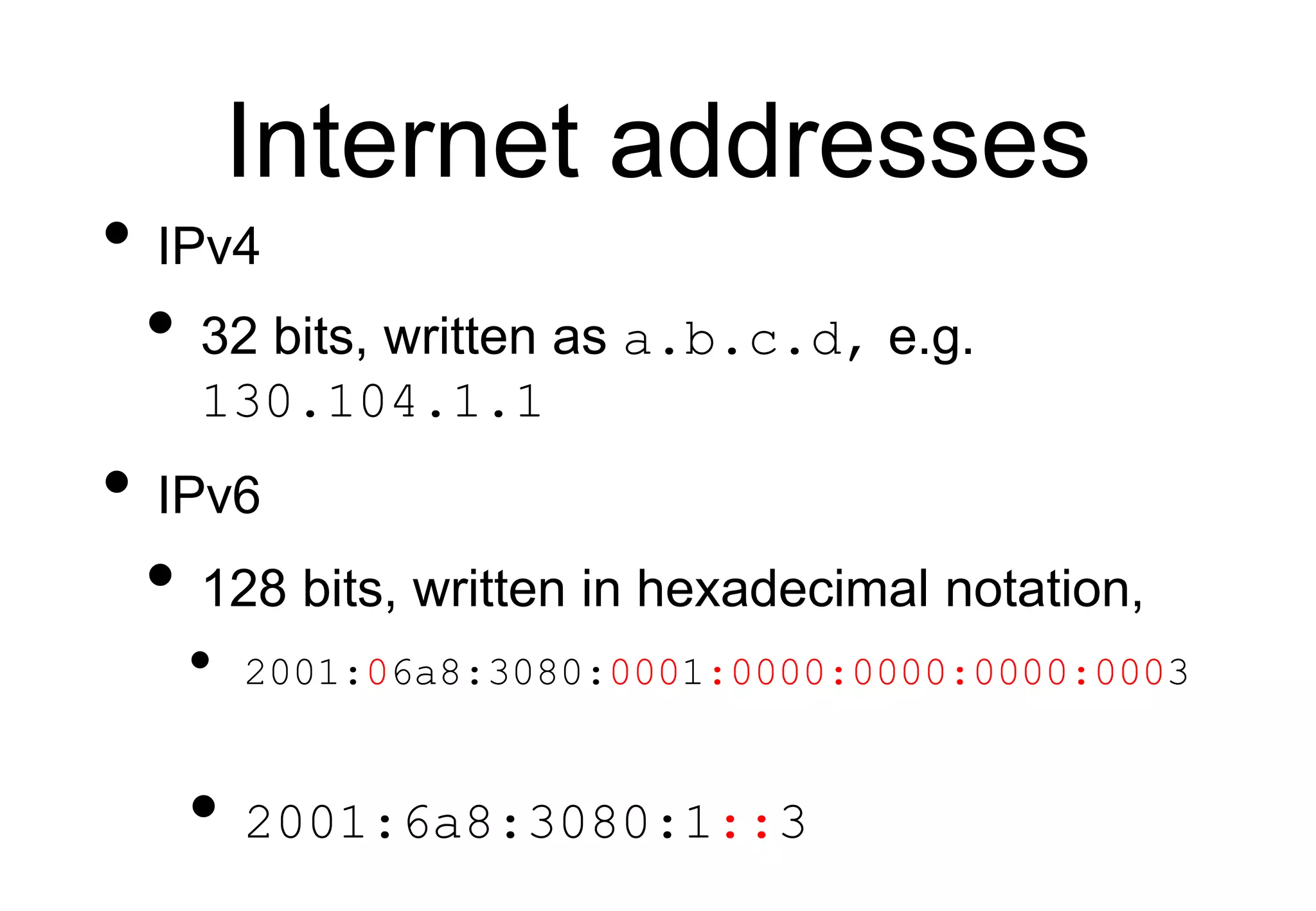
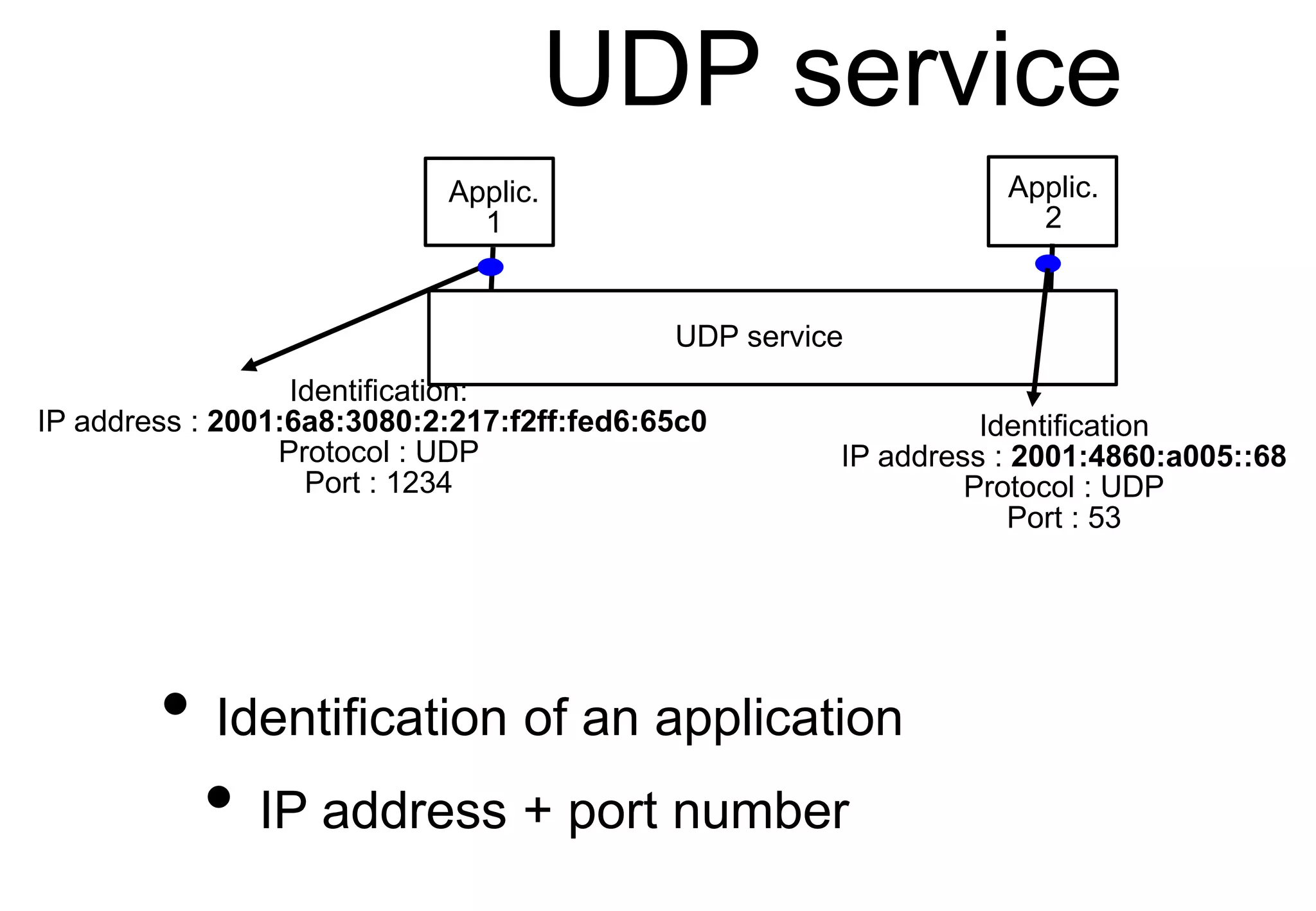
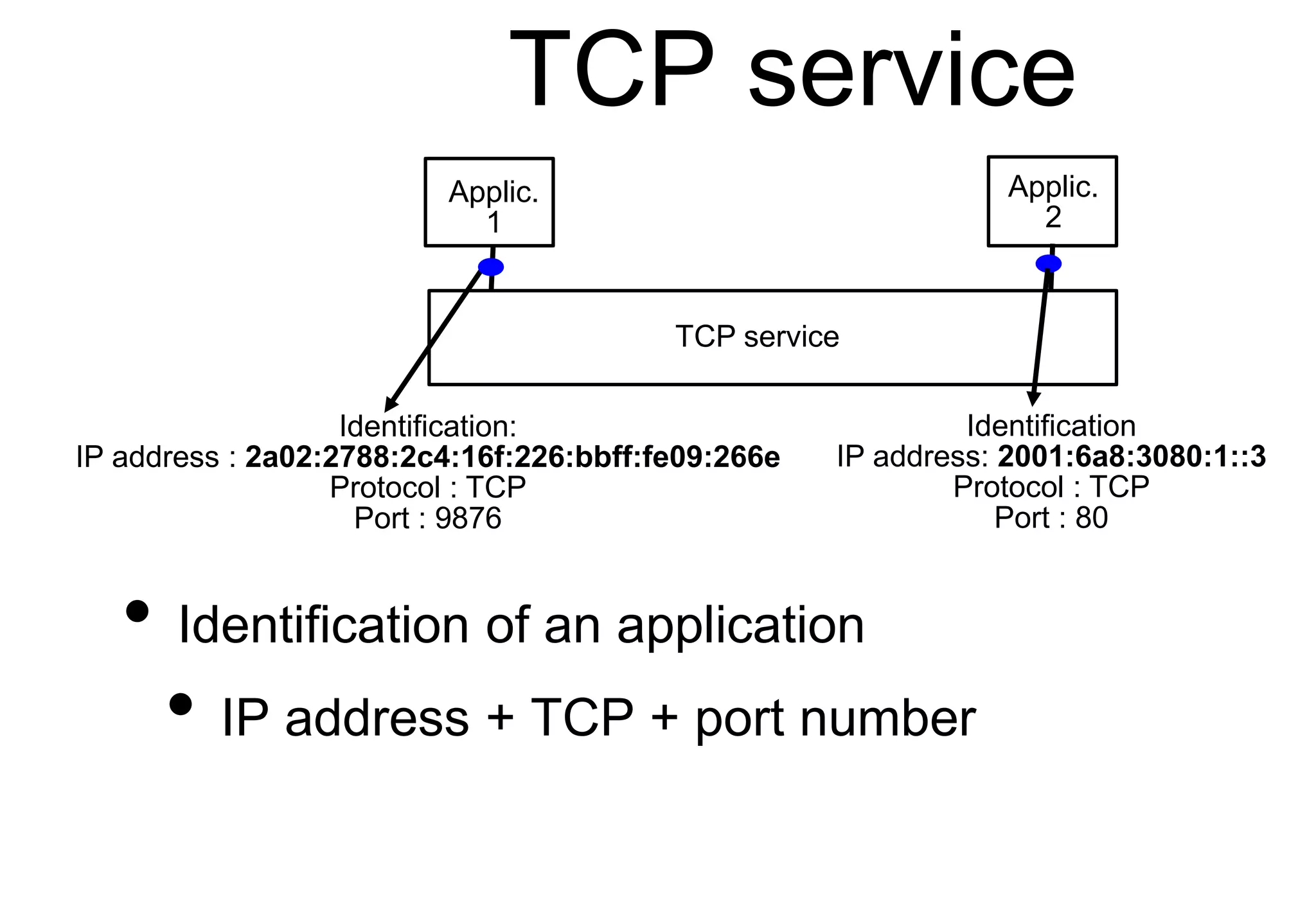
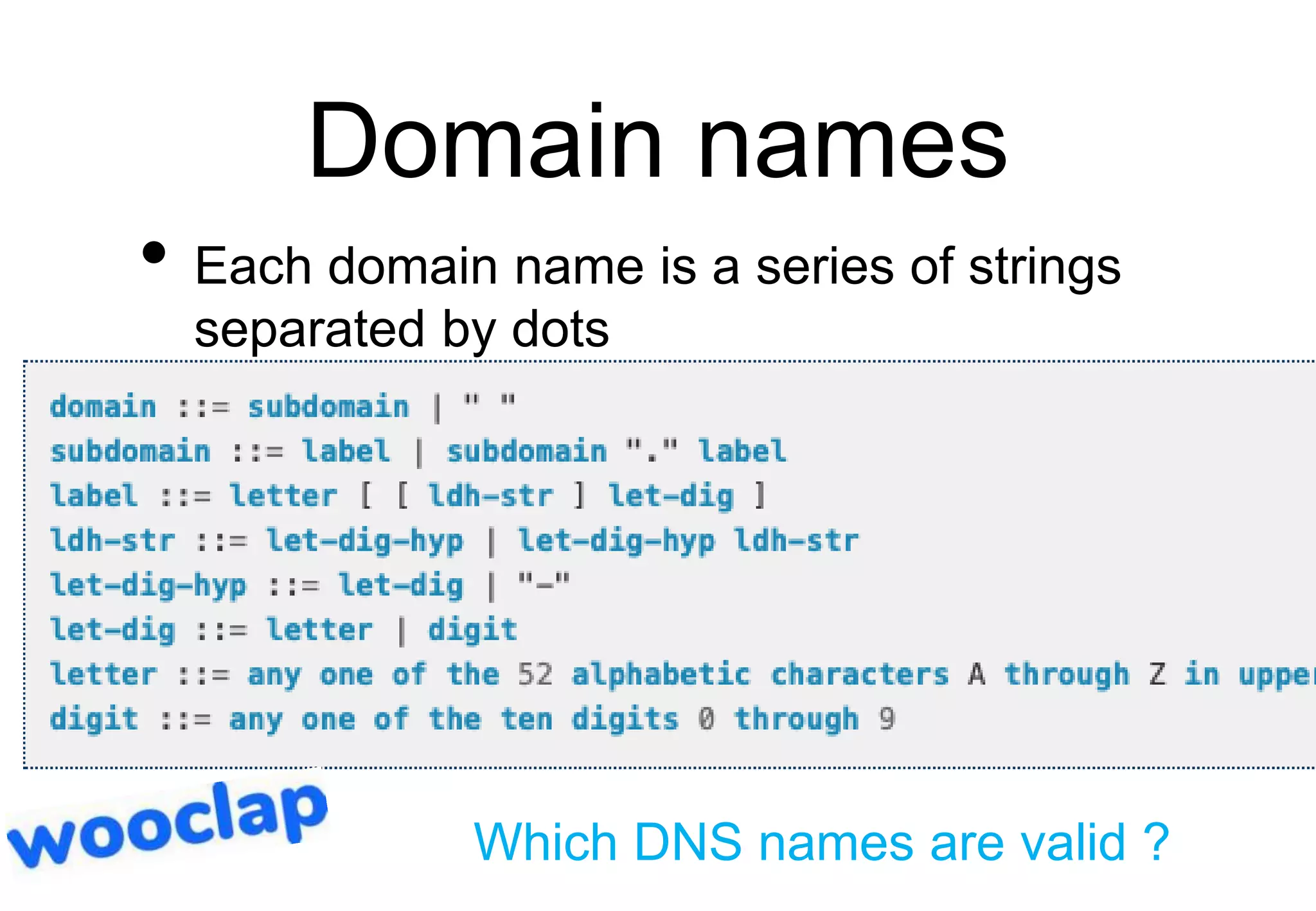
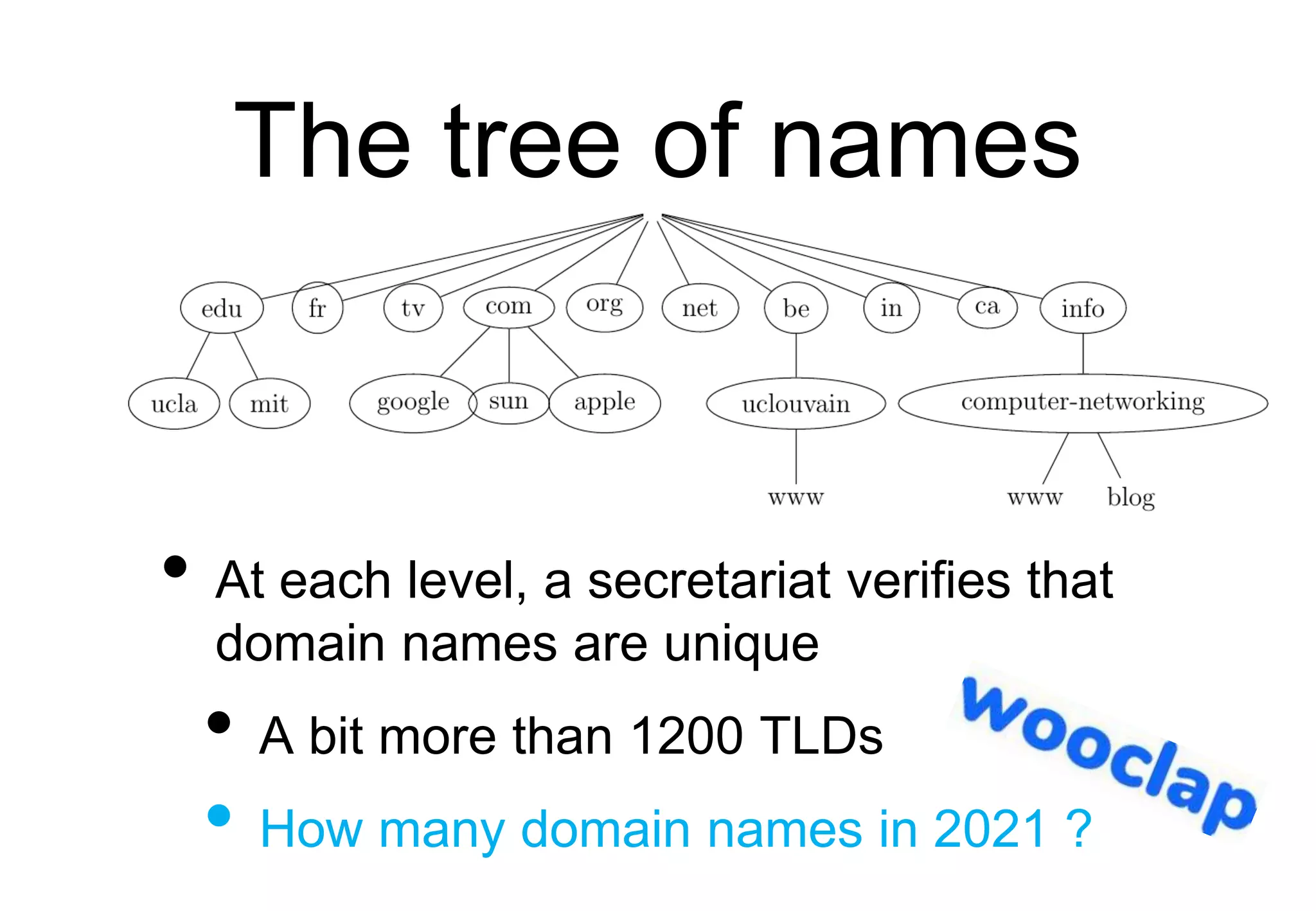
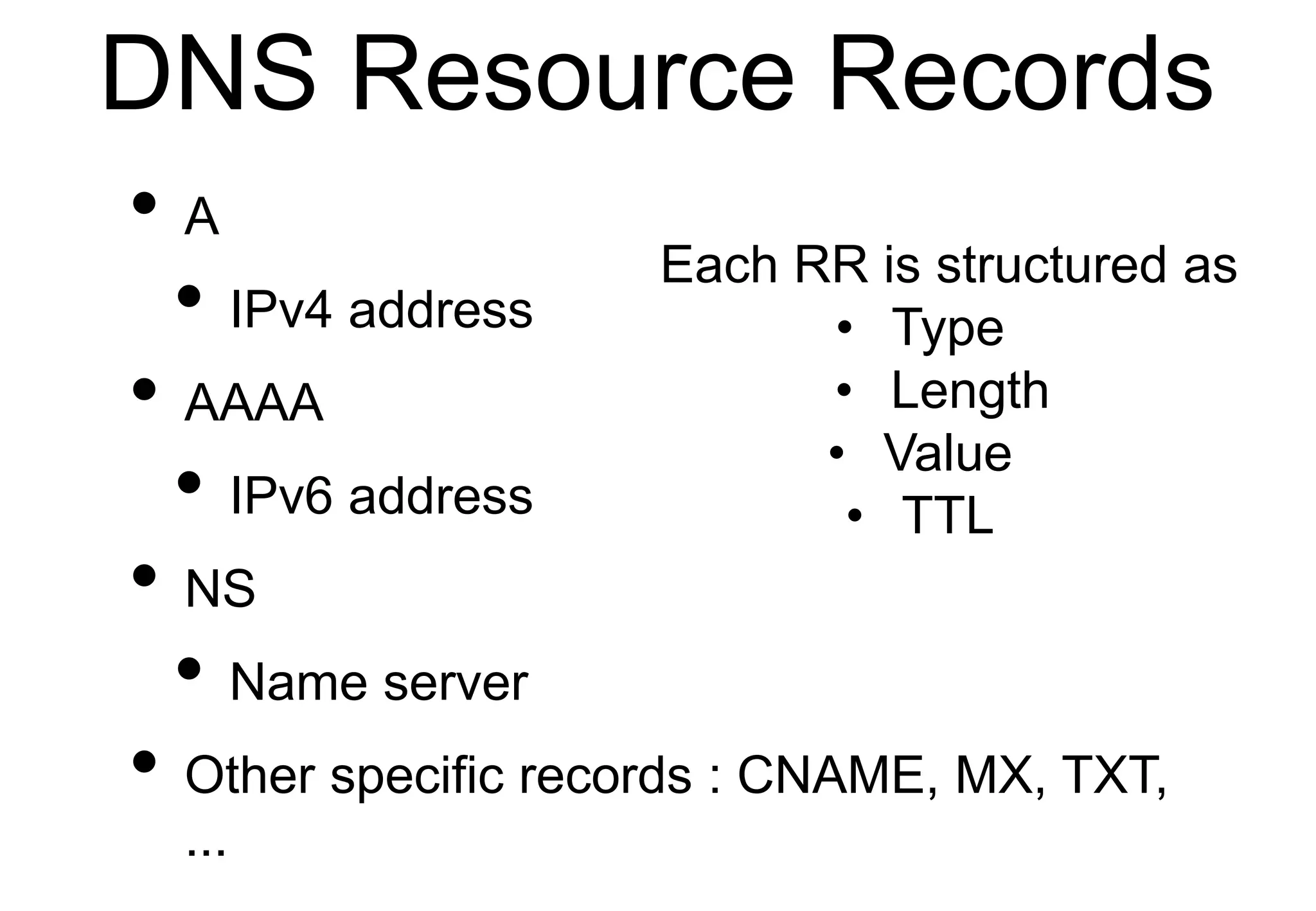
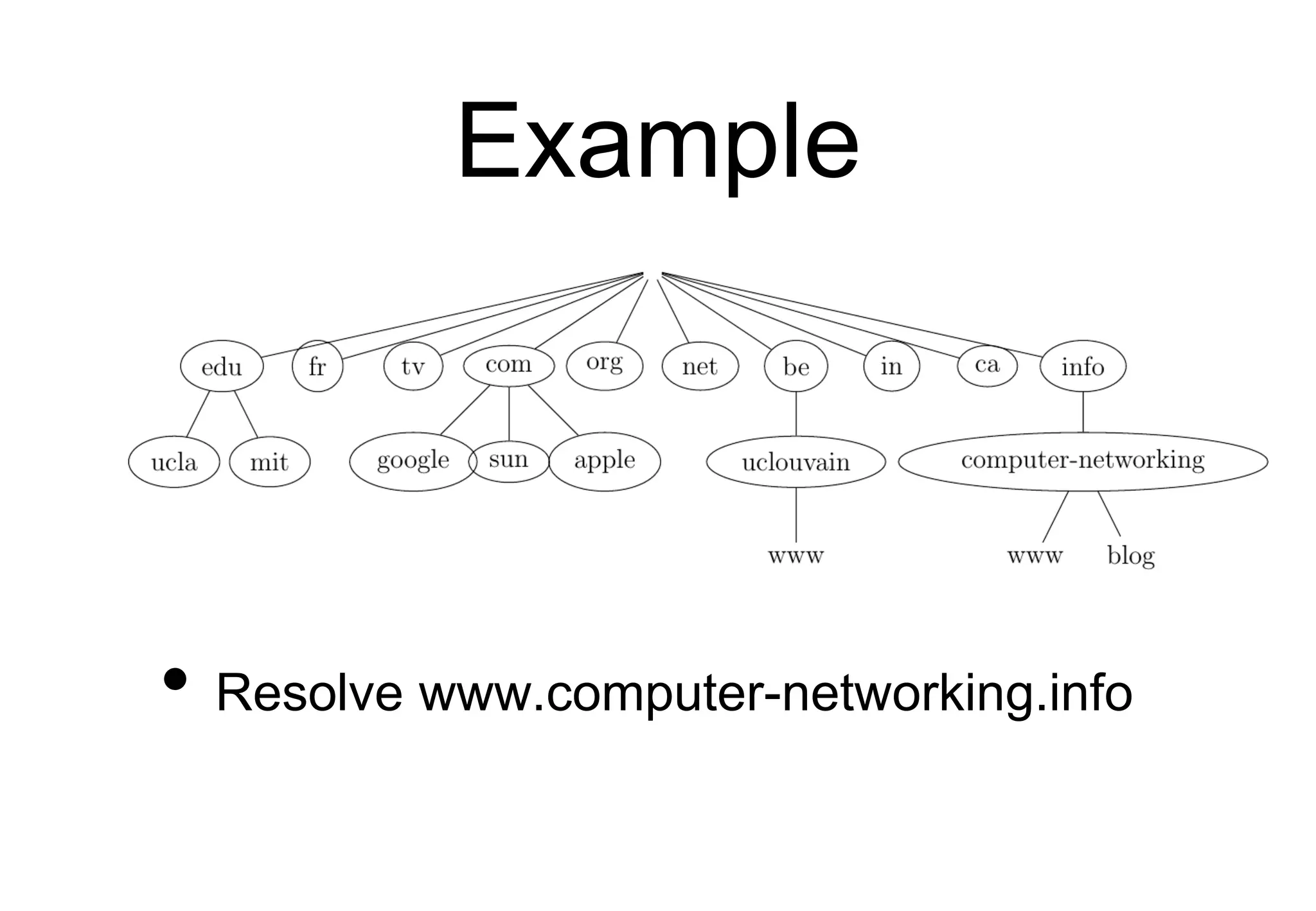
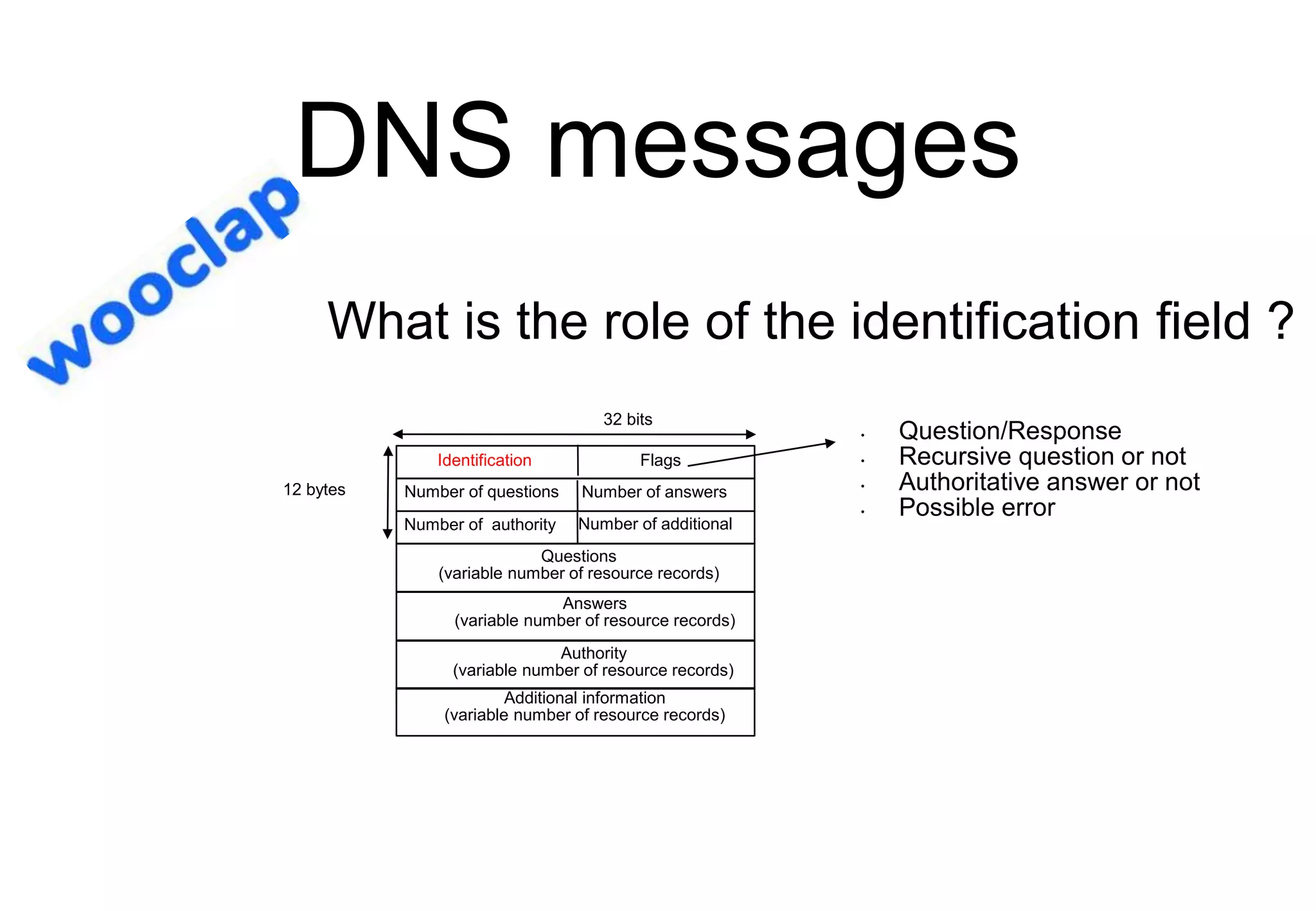
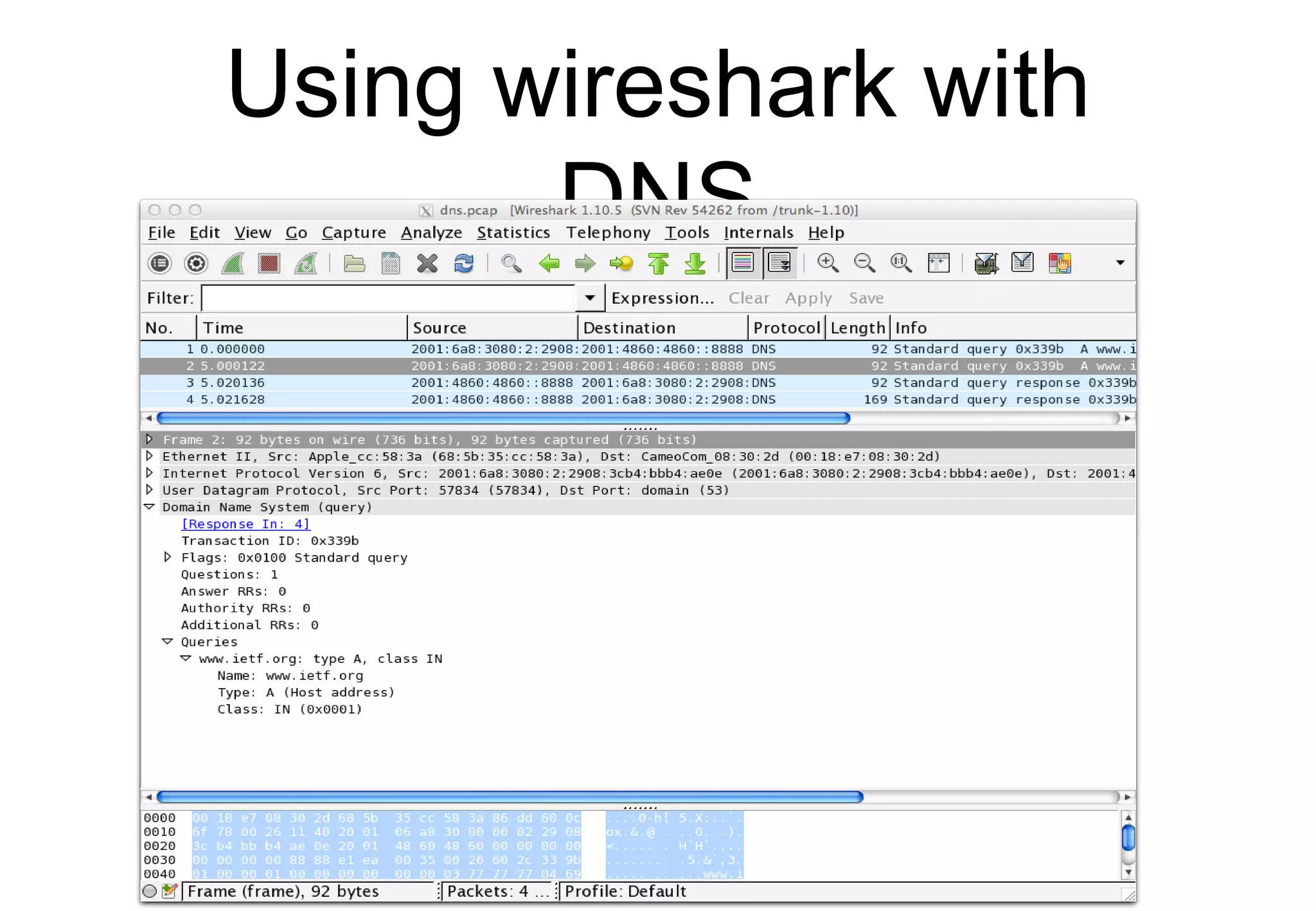
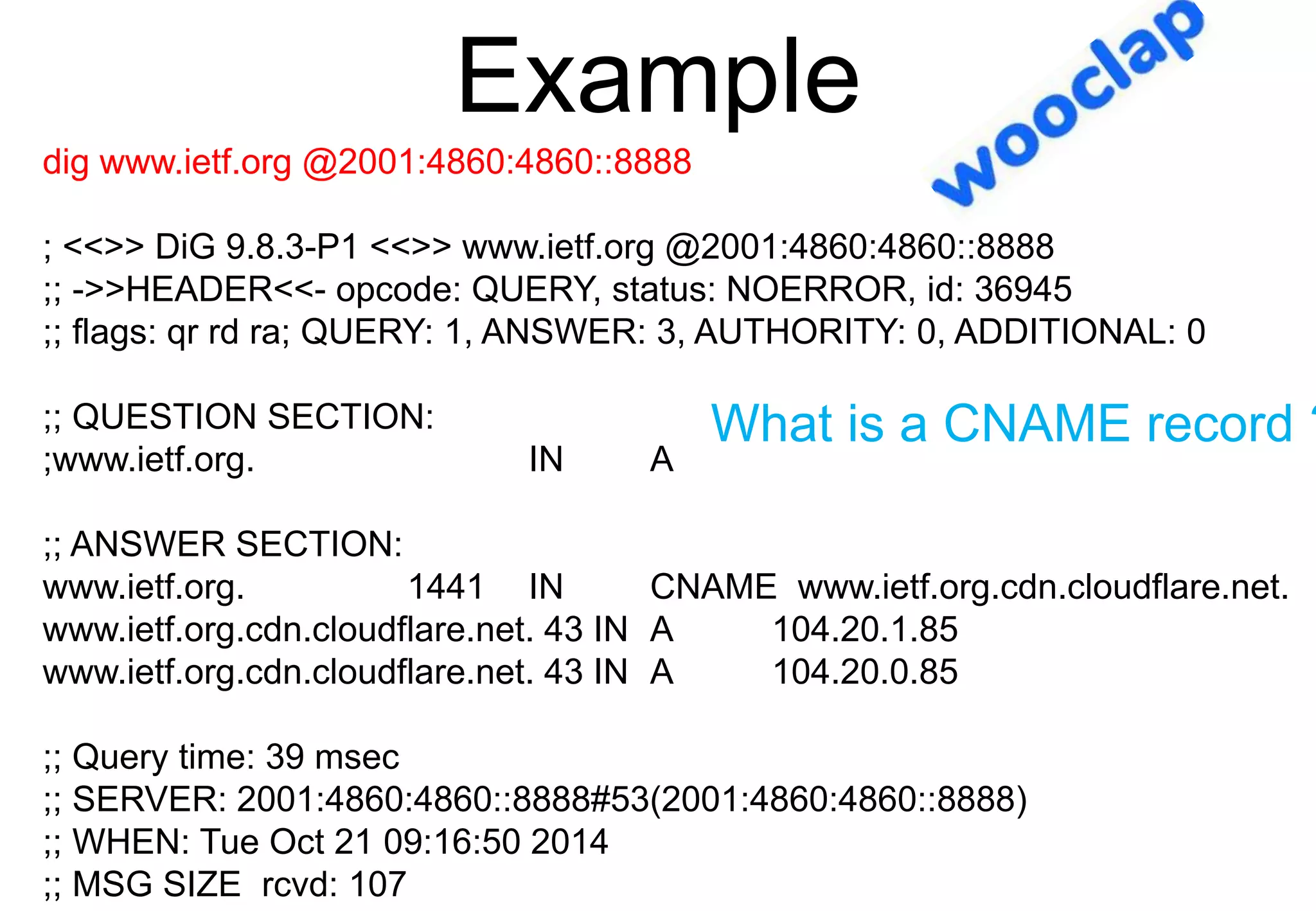
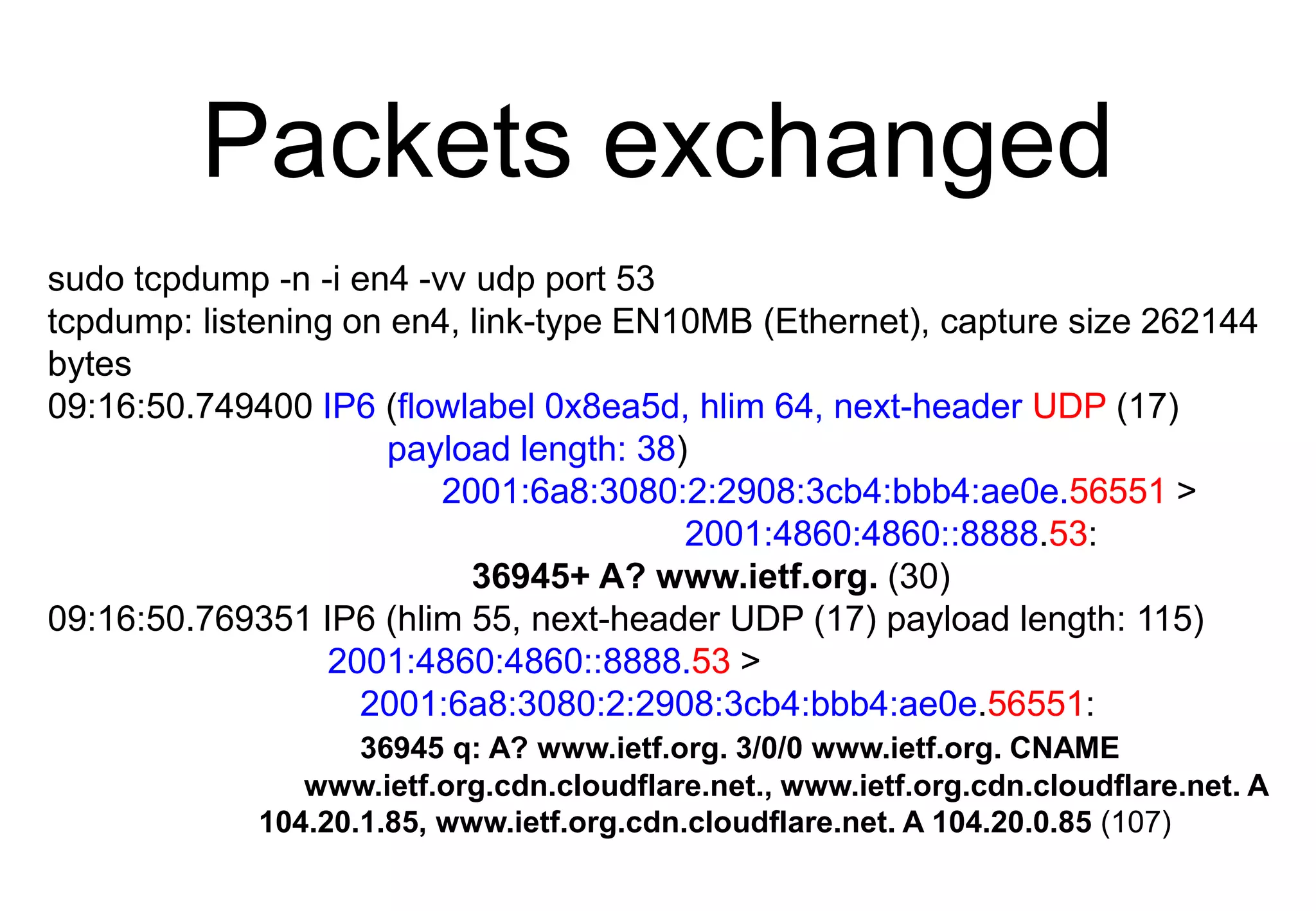
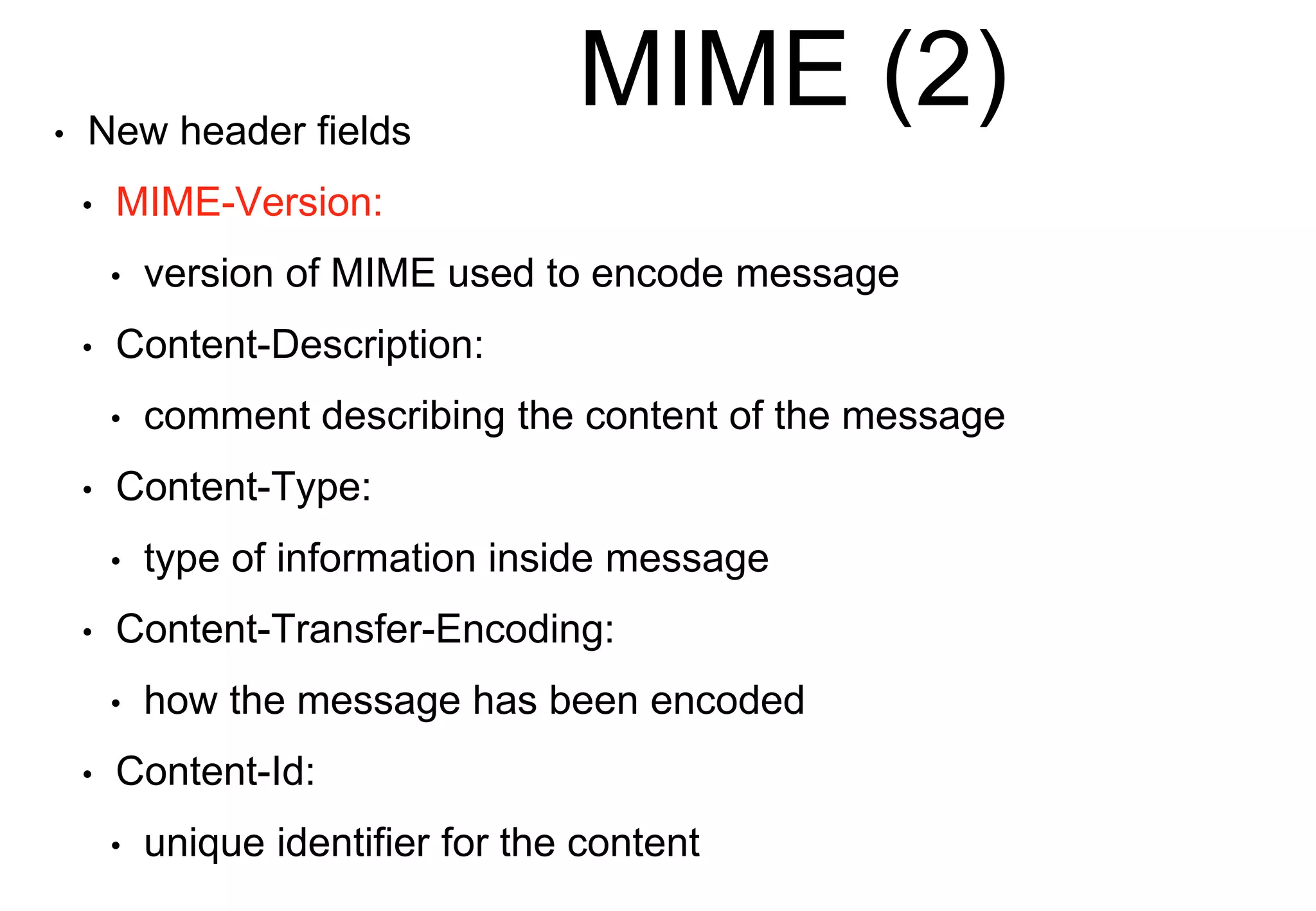
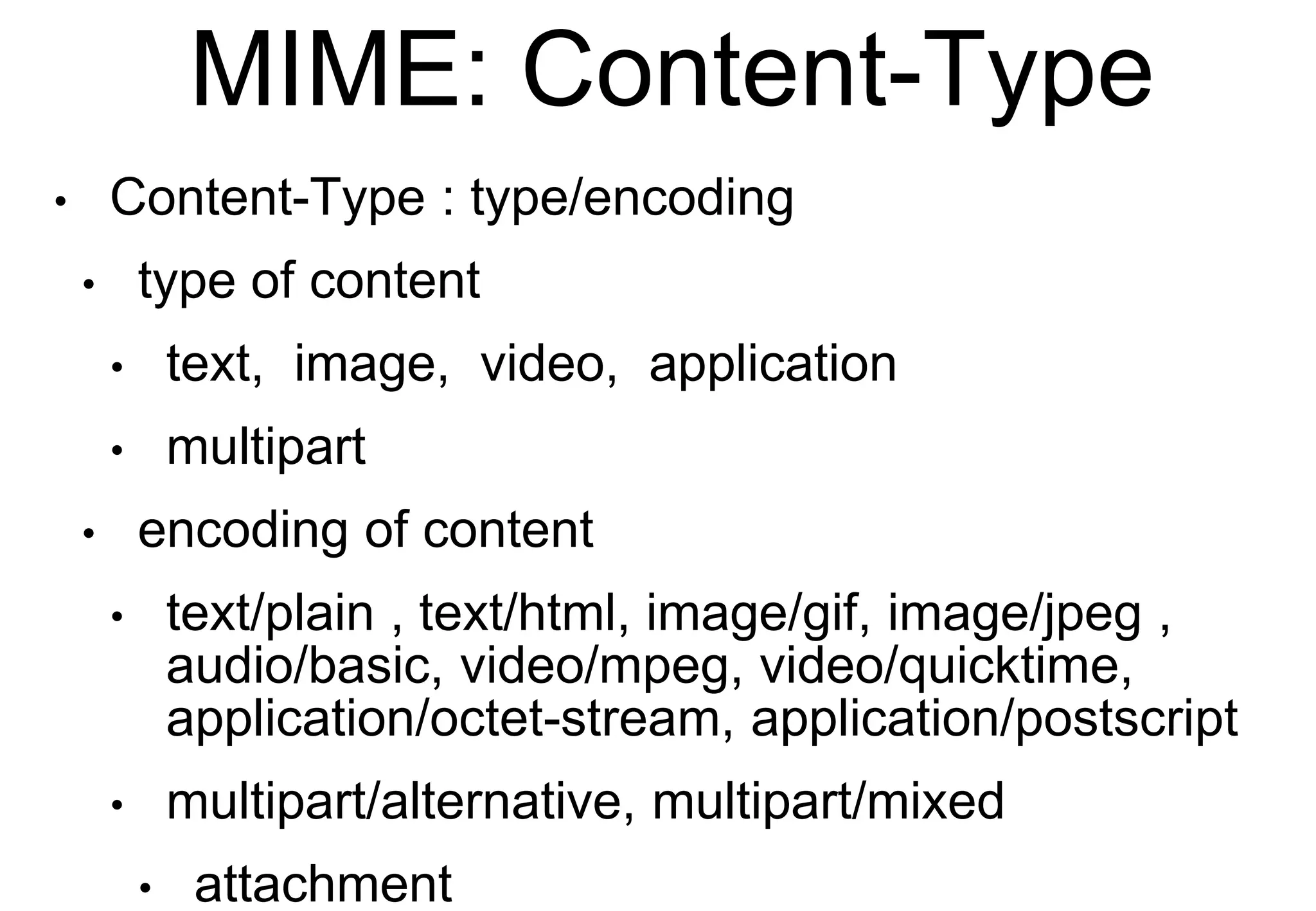
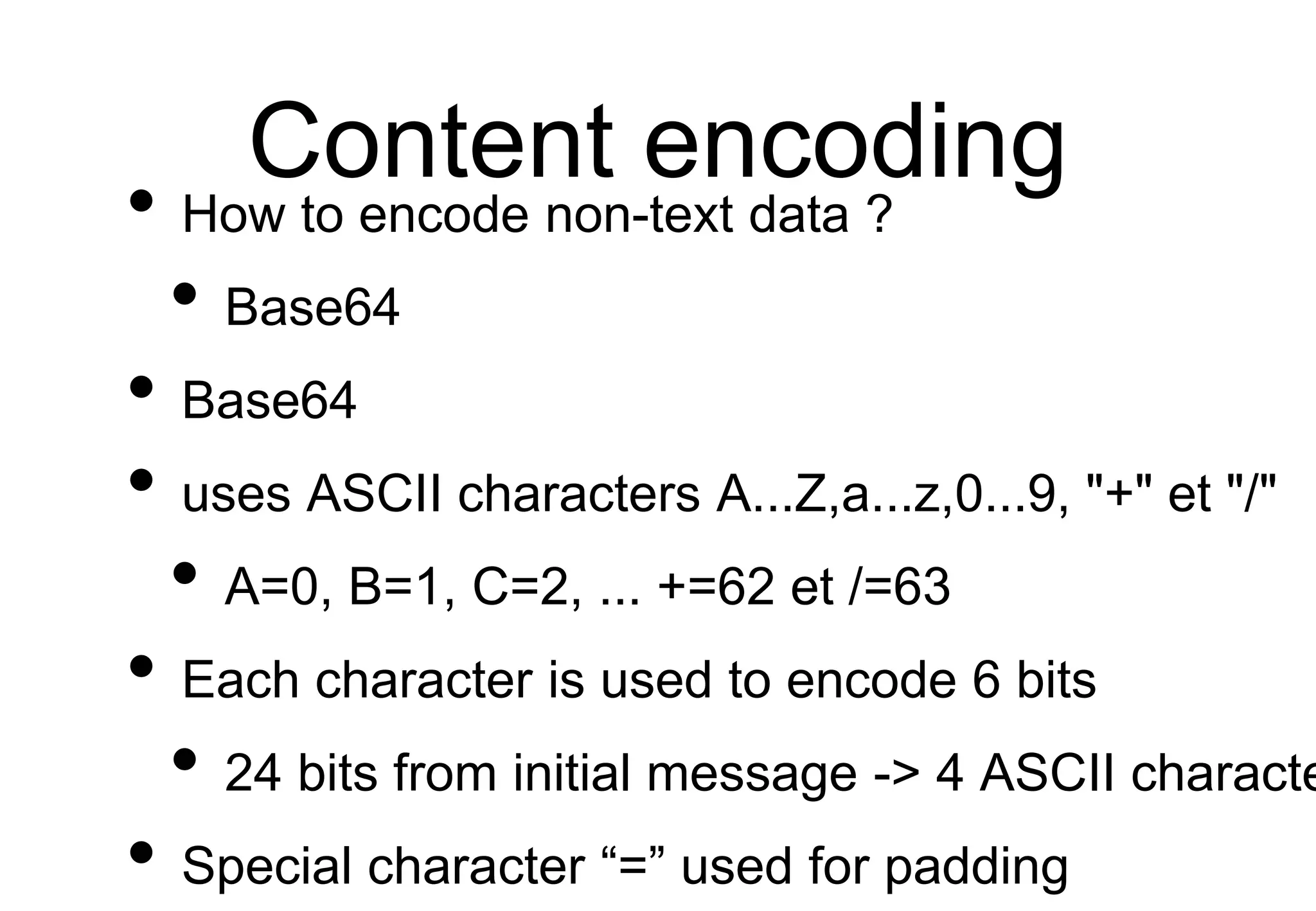
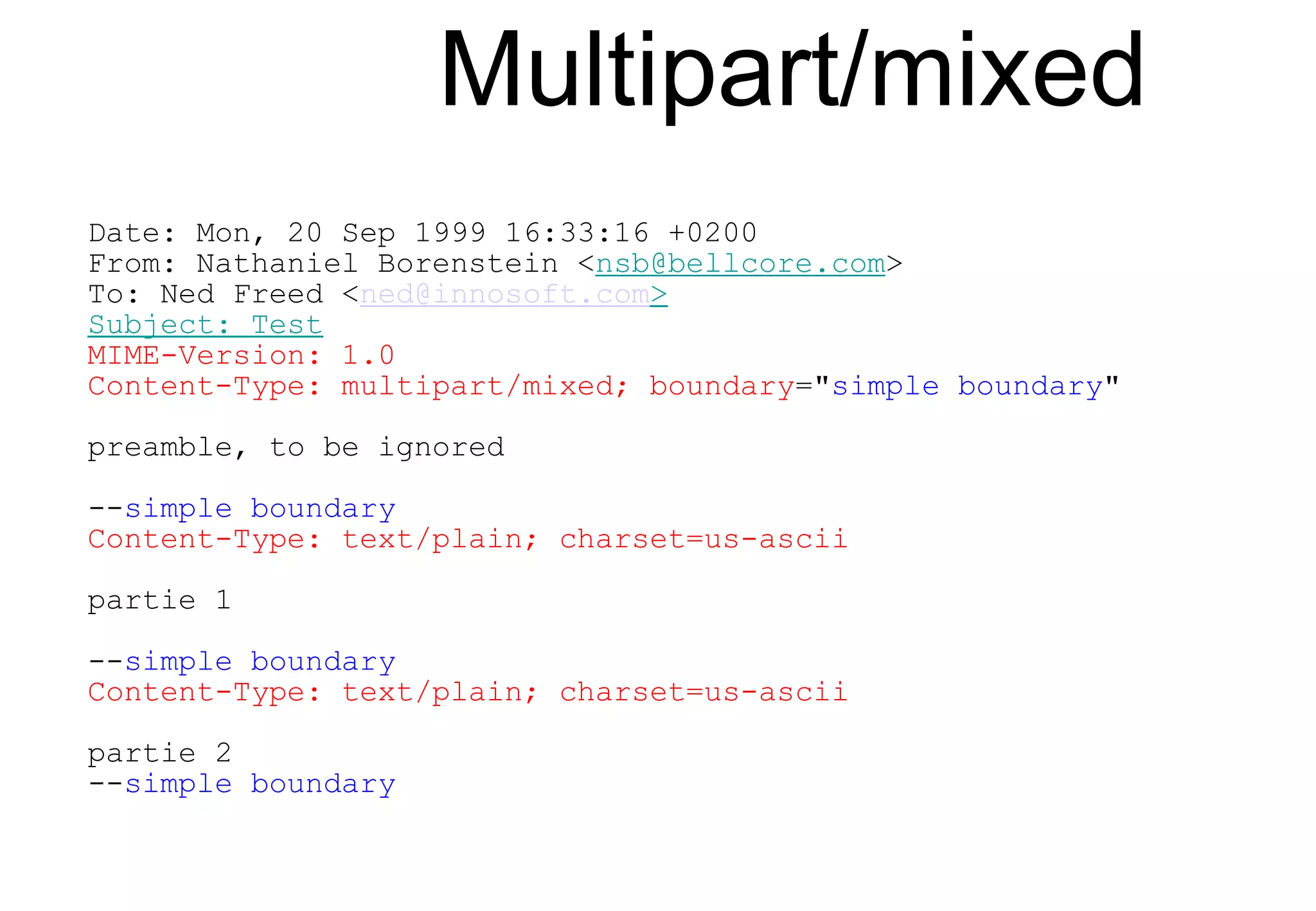
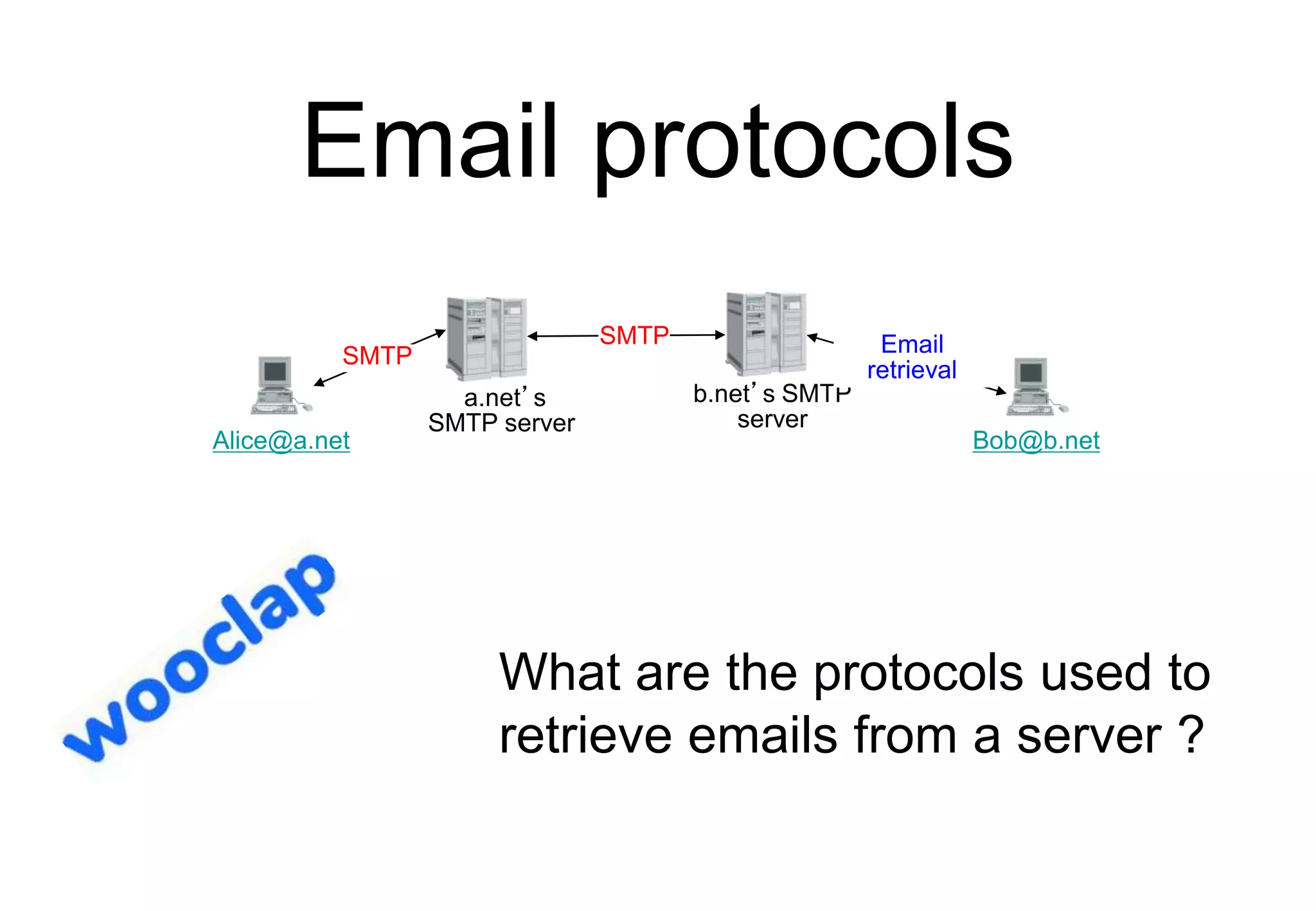
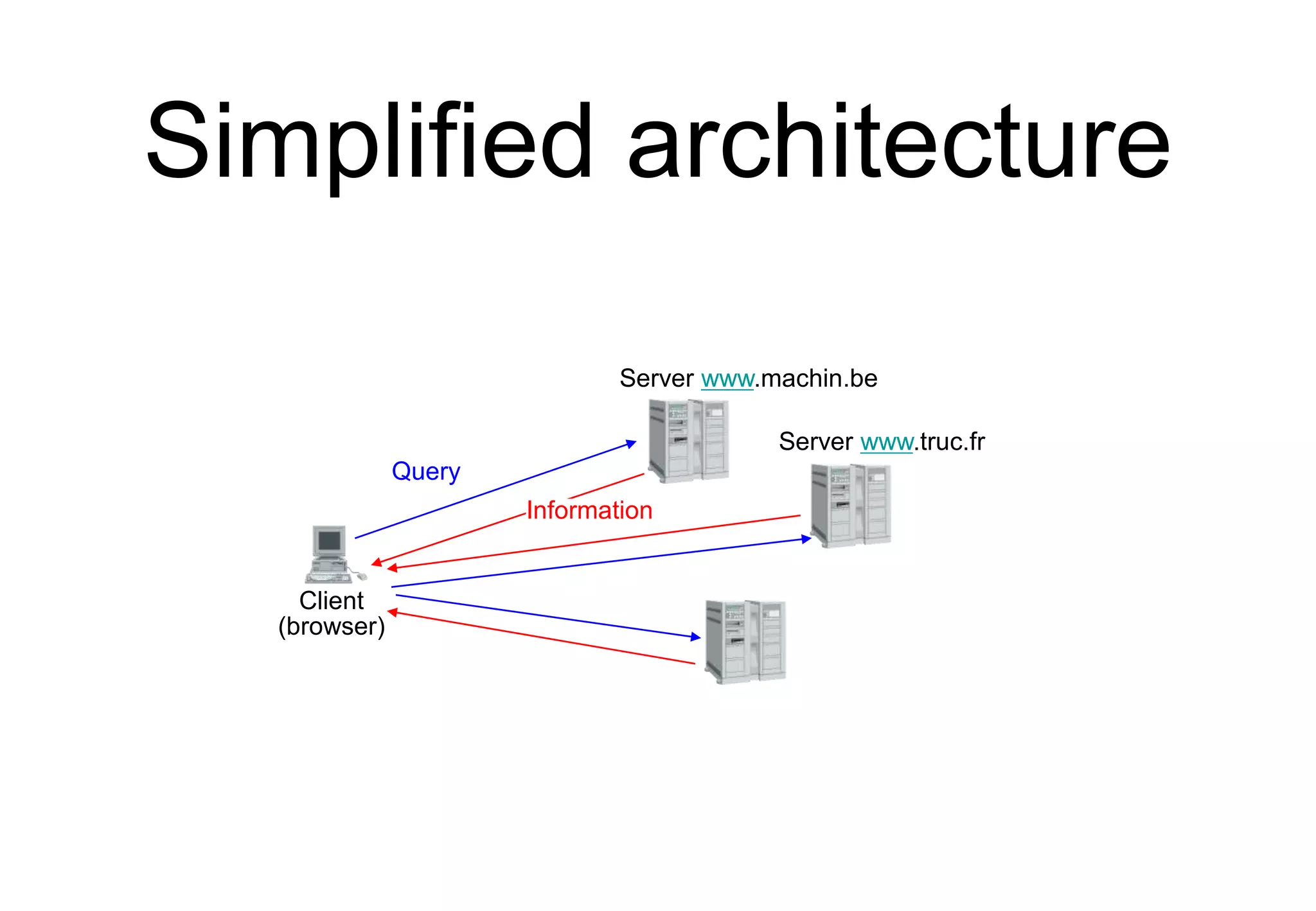
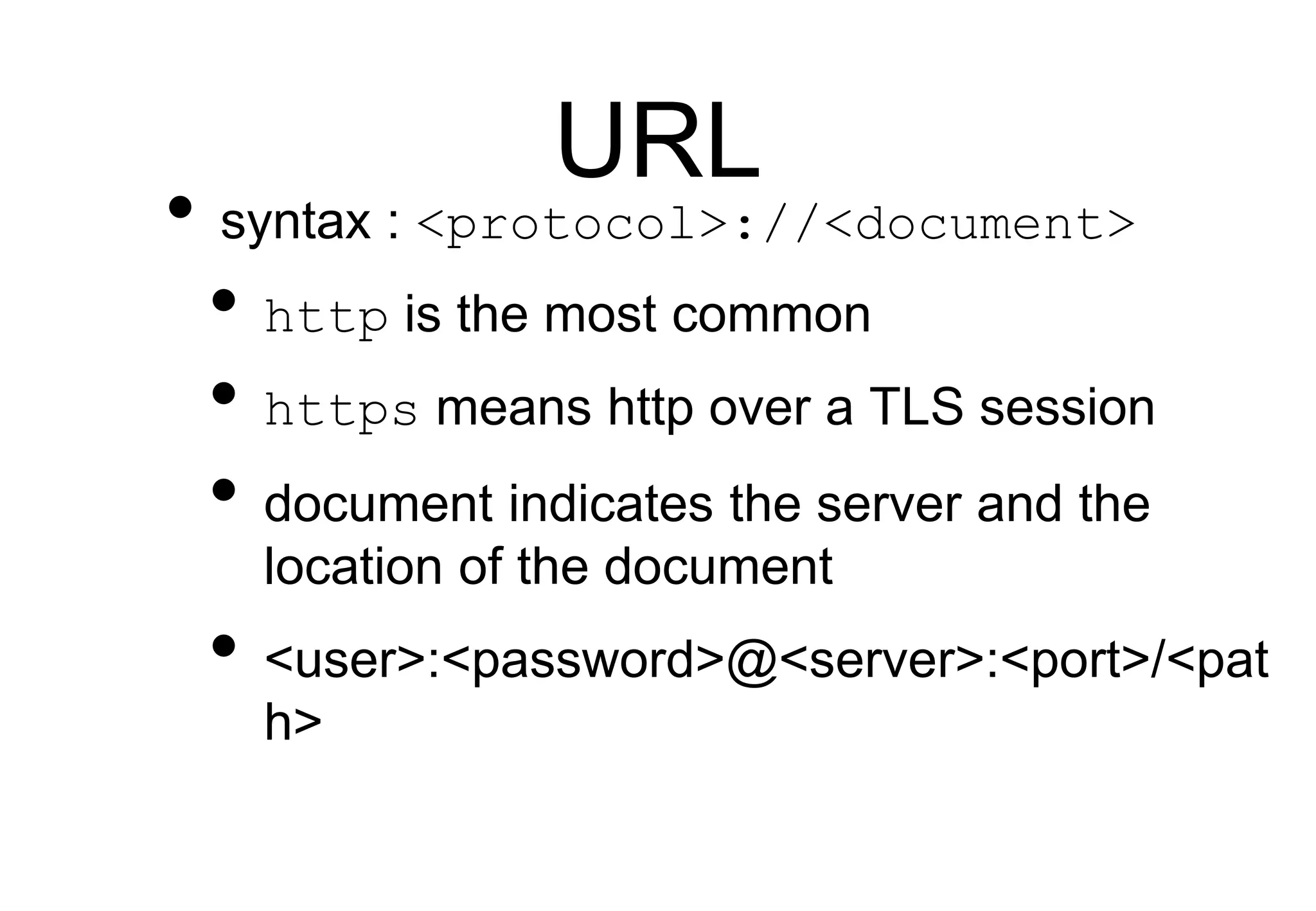
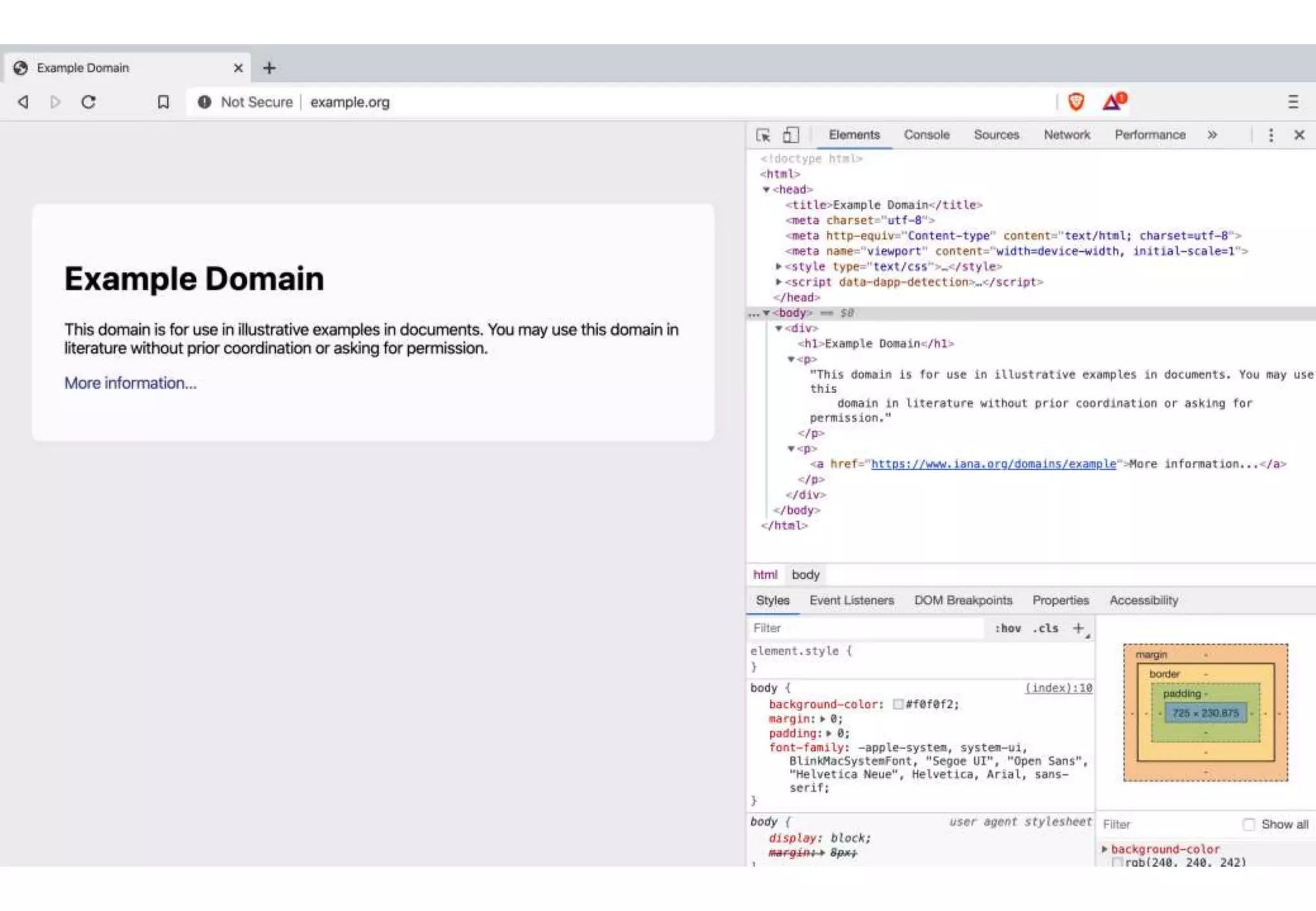
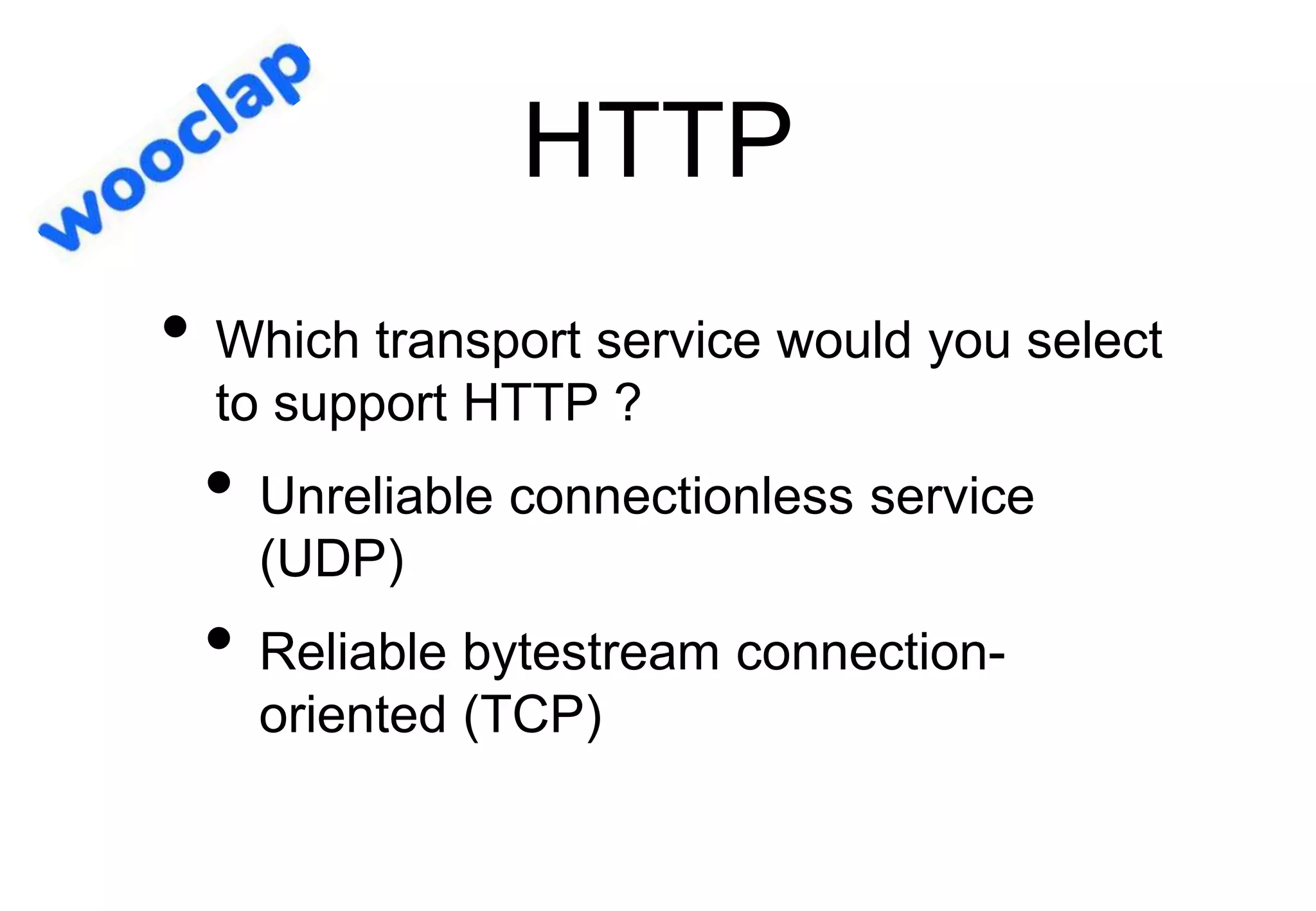
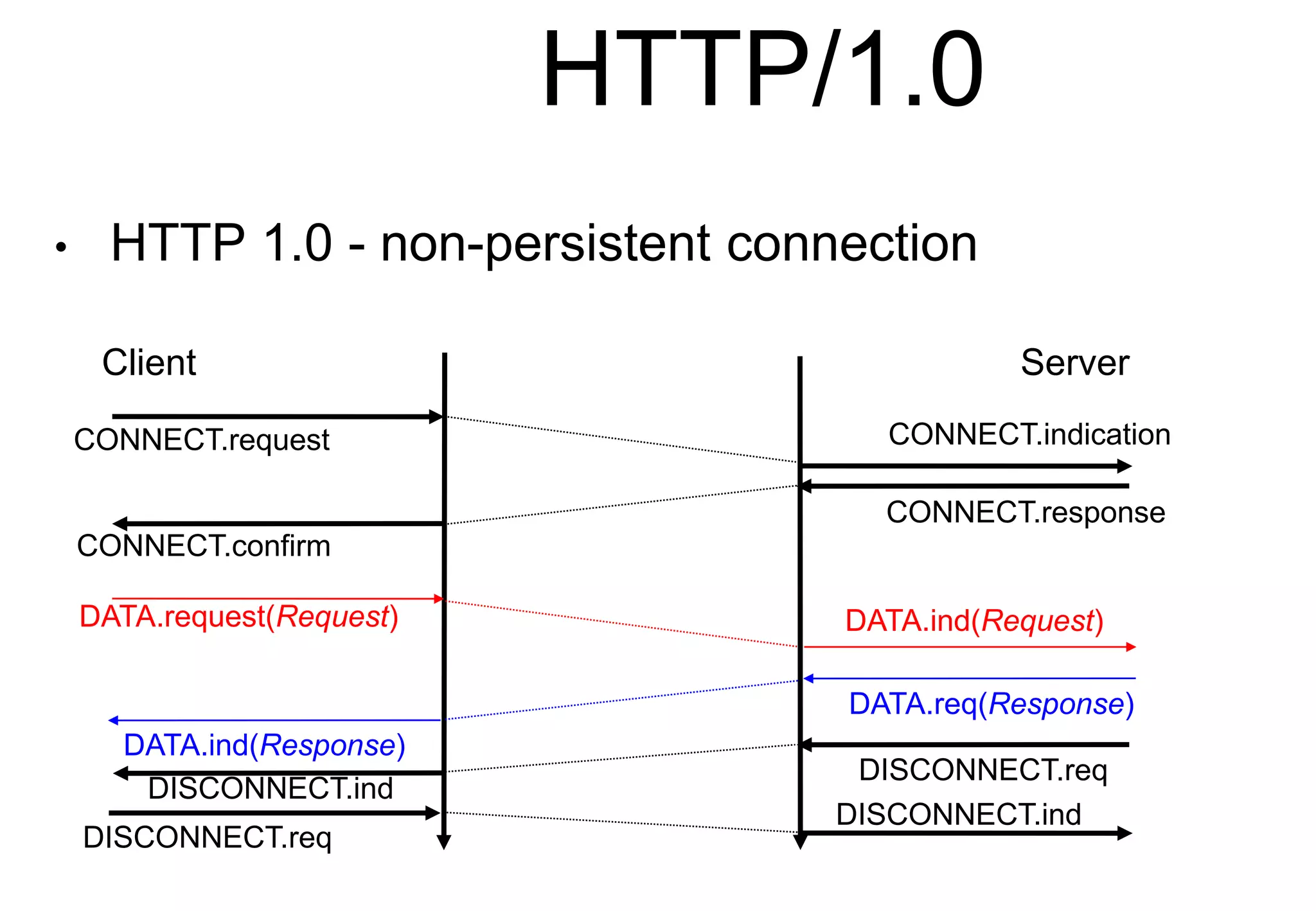
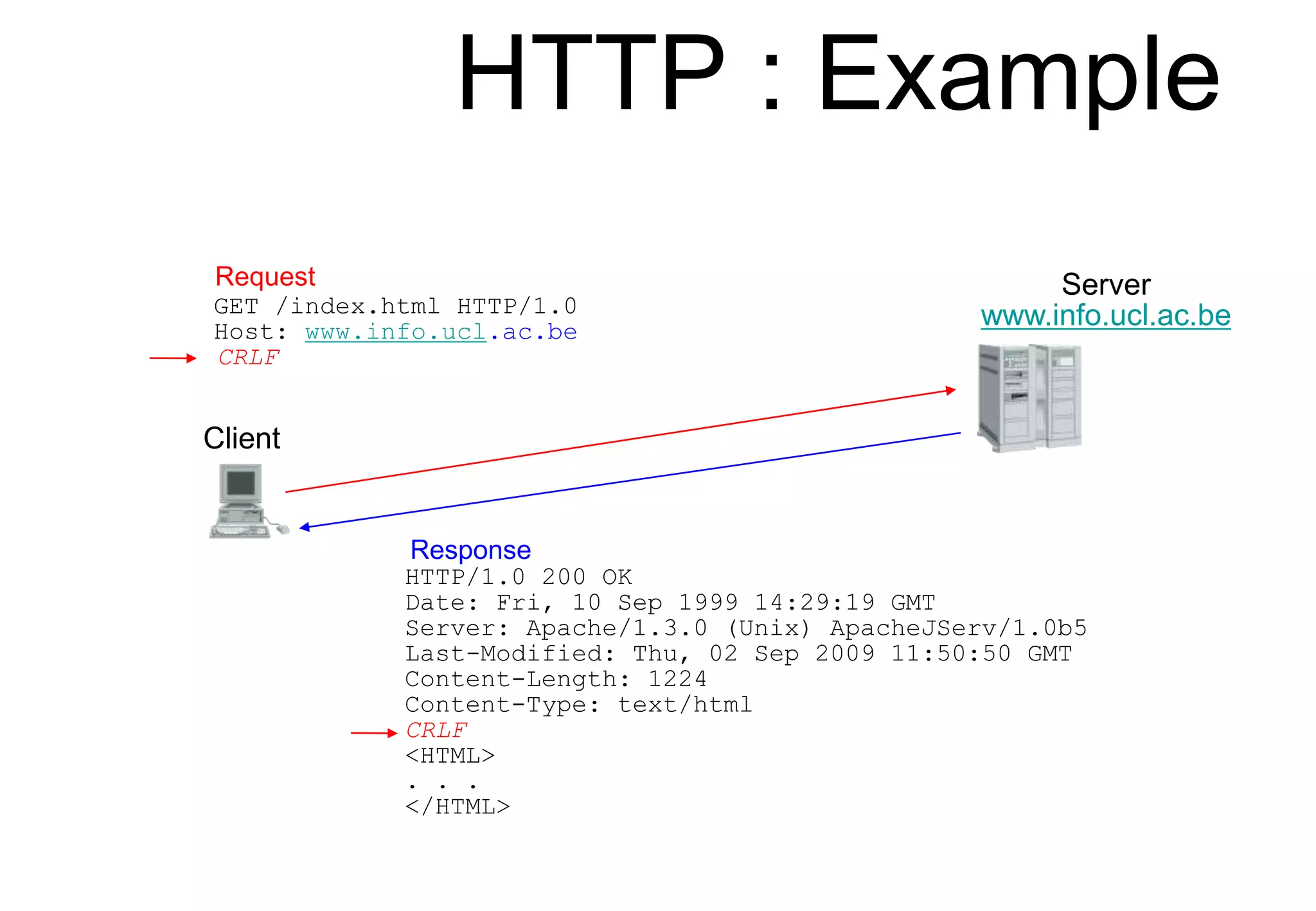
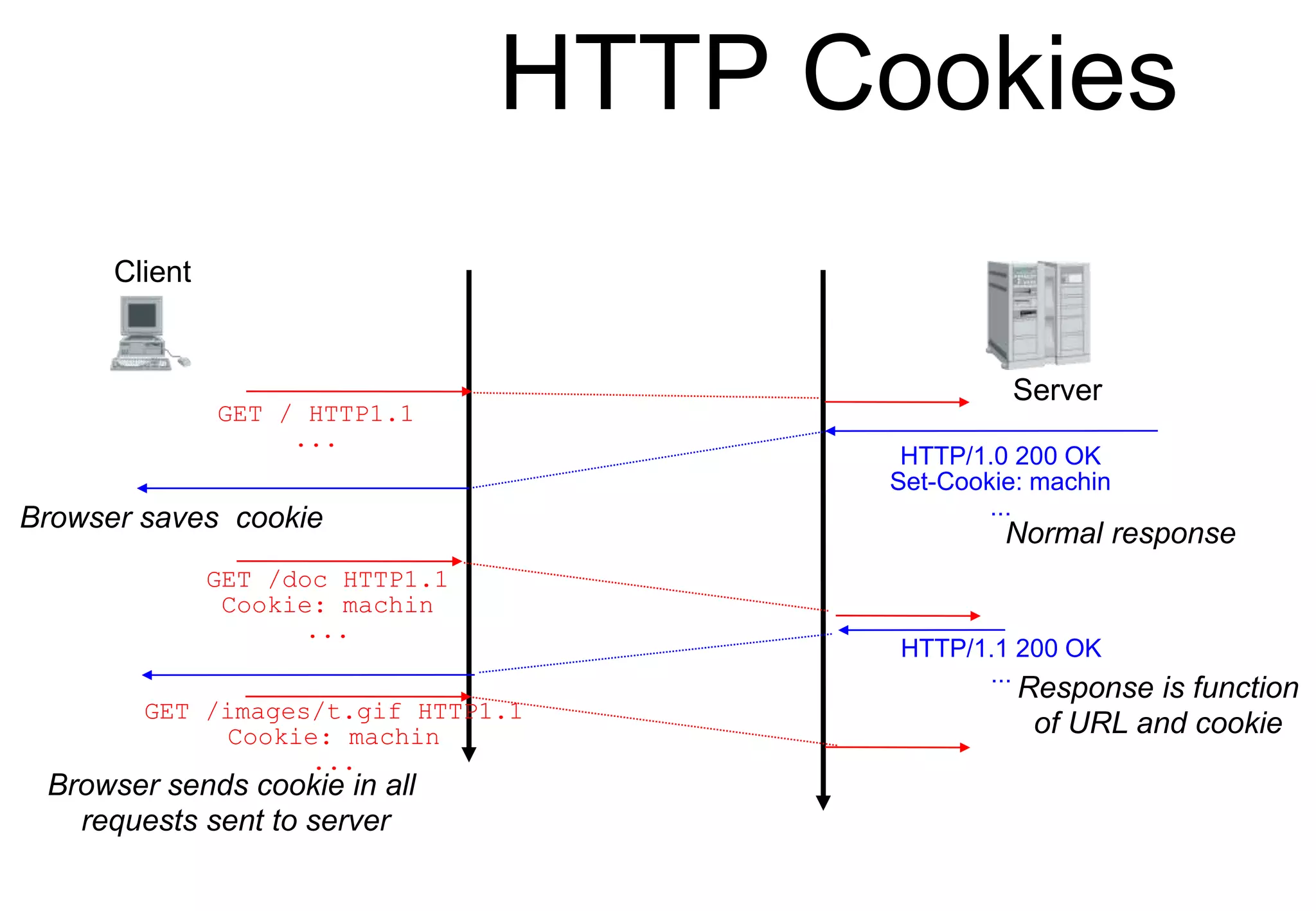
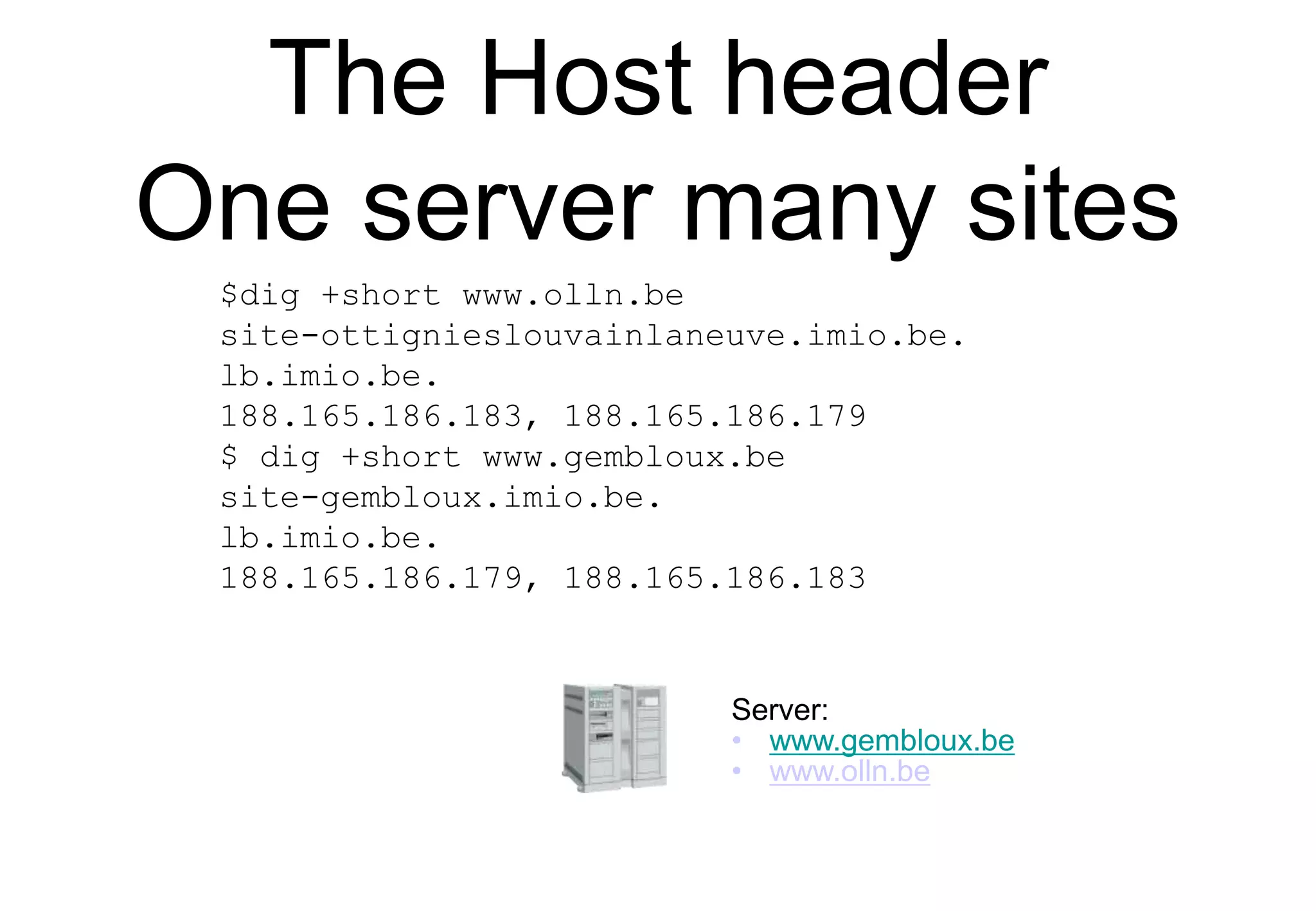
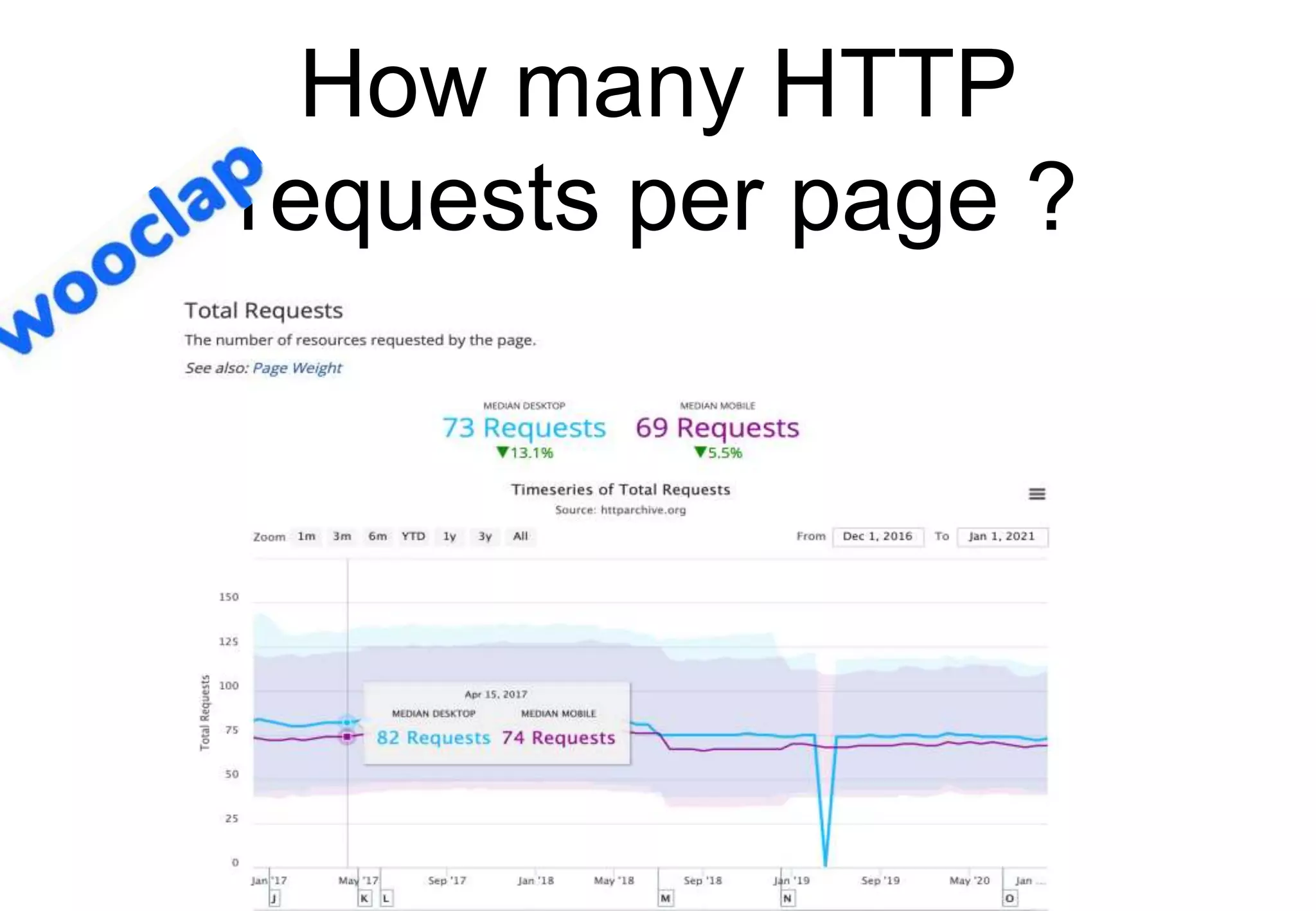
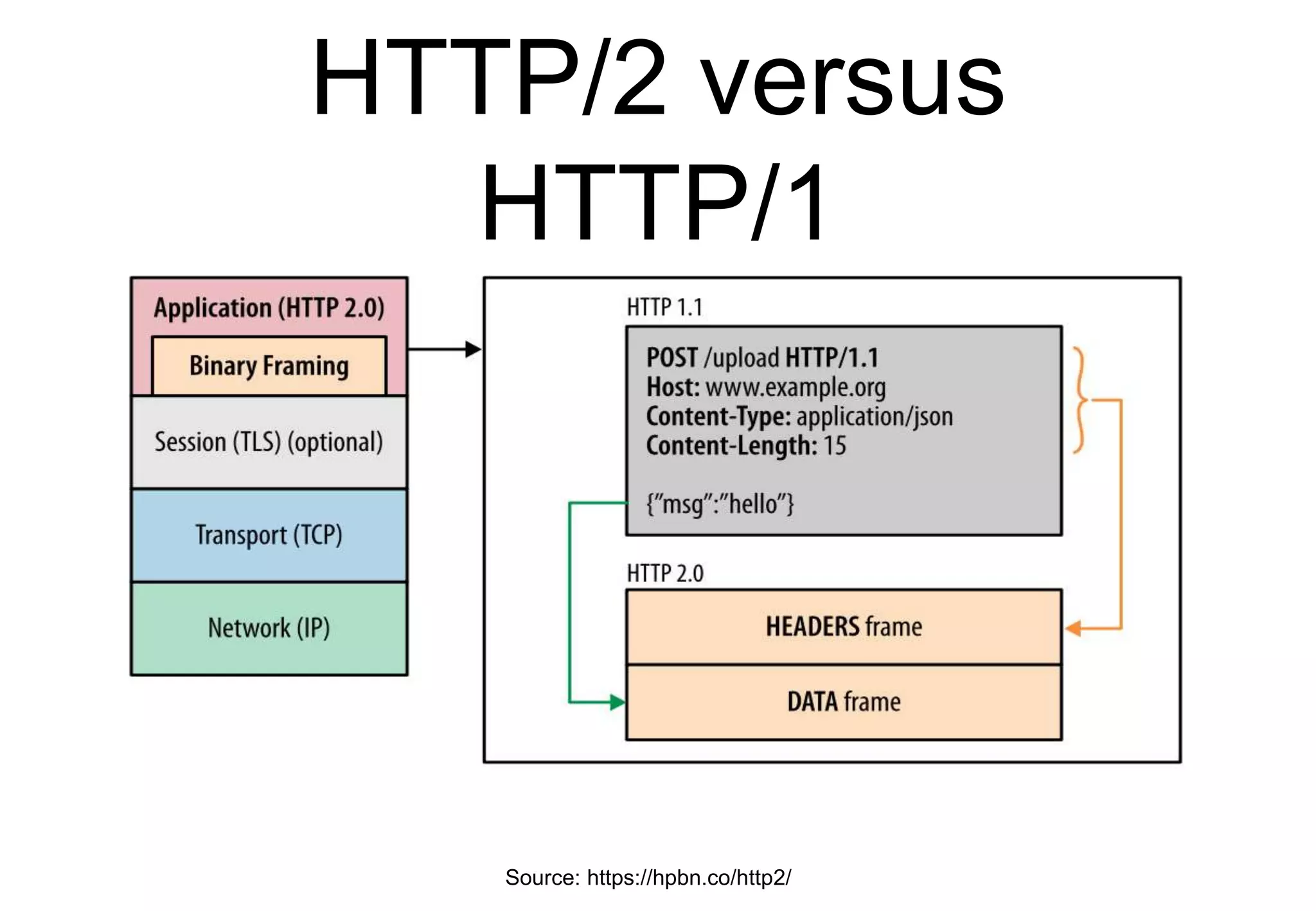
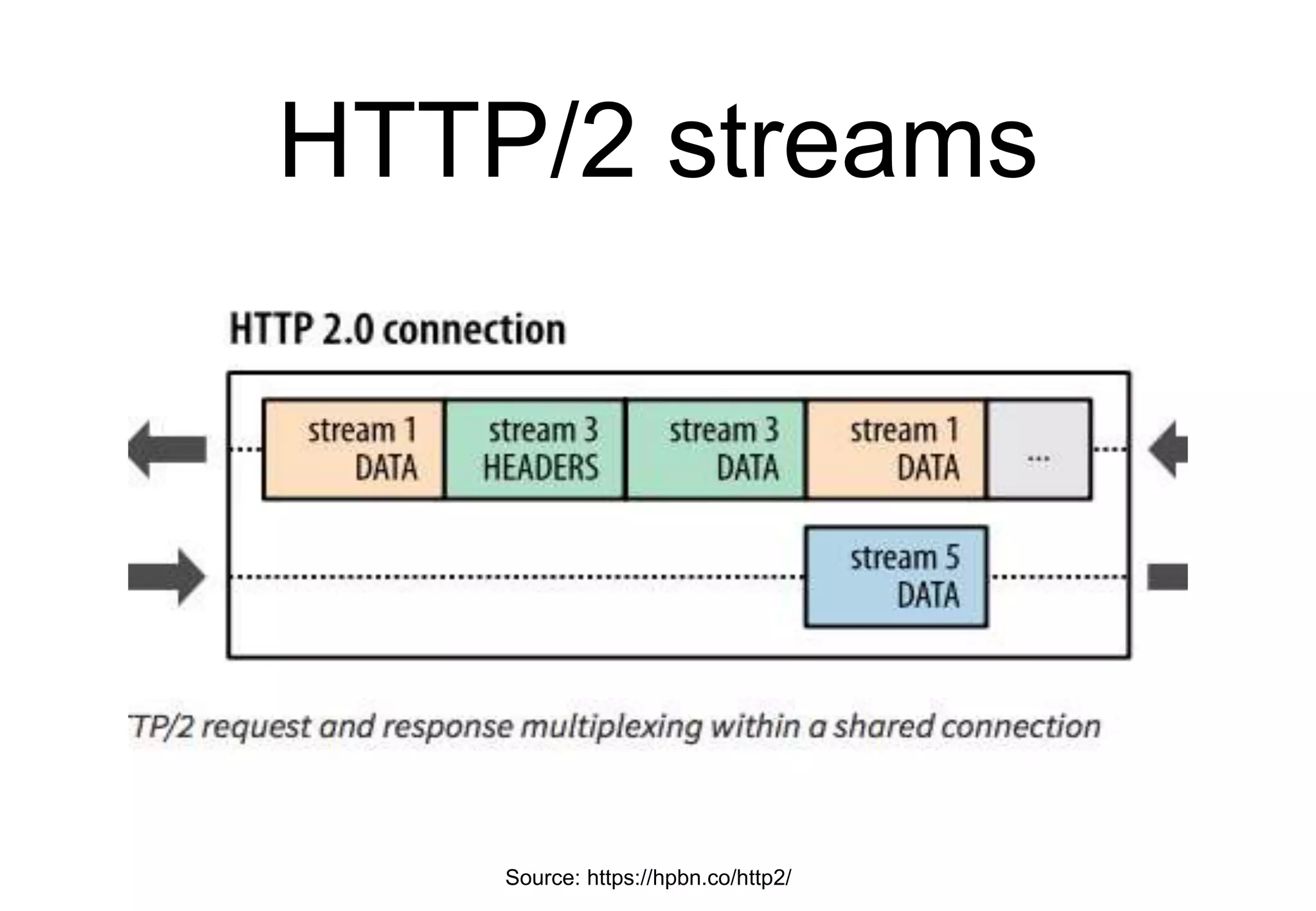
The document outlines a comprehensive agenda focusing on the structure of the Internet protocol stack, covering components such as DNS, email systems, web protocols, and naming conventions. It explains the details of packet transmission, TCP/UDP services, email protocols, MIME, and web architecture, including HTTP methods and response formats. Additionally, it discusses the mechanisms for resolving domain names, the functioning of email servers, and the organization of data packets in network communication.