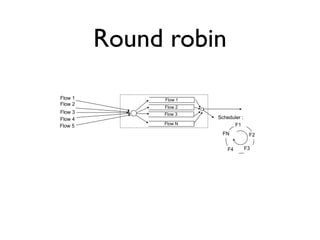
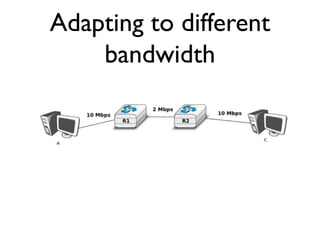
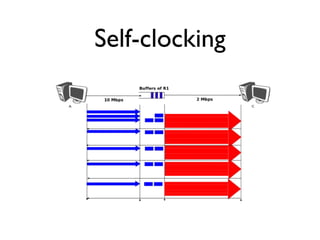
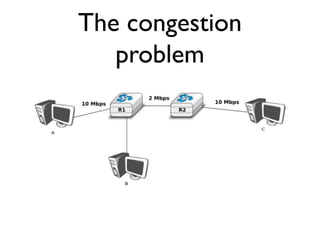
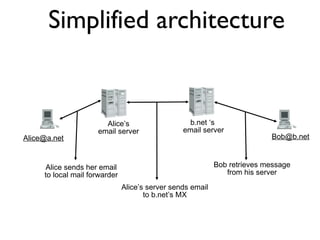
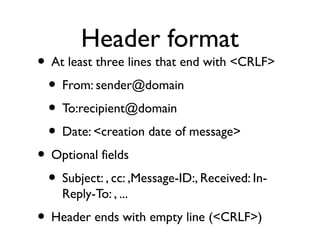
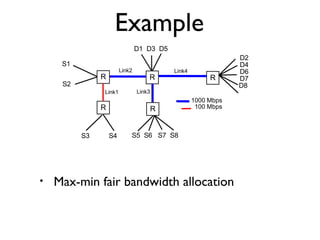
The document discusses various topics related to sharing resources and internet applications. It begins by covering medium access control protocols like ALOHA, CSMA, and CSMA/CD. It then discusses congestion control, including max-min fairness, router queuing strategies, and window-based congestion control. Finally, it summarizes several internet applications - DNS, email protocols like SMTP, and the basic web client-server architecture.

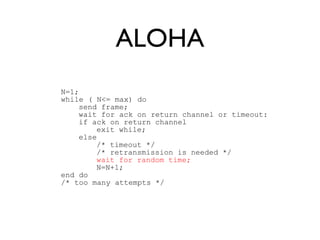
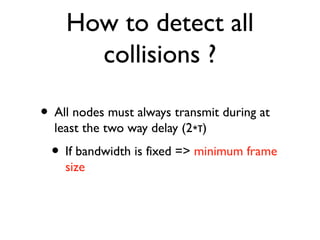
![CSMA/CA : sender
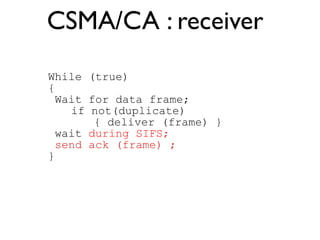
N=1;
while ( N<= max) do
if (previous frame corruped)
{ wait until channel free during t>=EIFS; }
else
{ wait until endofframe;
wait until channel free during t>=DIFS; }
backoff_time = int(random[0,min(255,7*2N-1)])*T
wait(channel free during backoff_time)
send data frame ;
wait for ack or timeout:
if ack received
exit while;
else /* timeout retransmission is needed */
N=N+1; }
end do](https://image.slidesharecdn.com/5-sharing-app-141015134431-conversion-gate01/85/5-sharing-app-18-320.jpg)
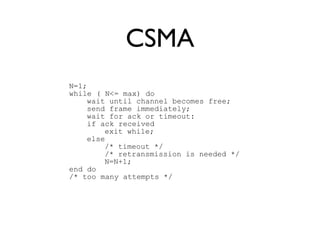
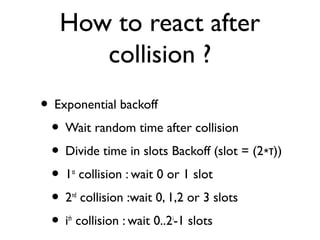
![Backoff
A B C
DIFS
DIFS
Backoff[0,7]
Backoff[0,7]
Channel busy!
Busy
Data frame
Data frame
SIFS
Ack frame
Remaining
backoff](https://image.slidesharecdn.com/5-sharing-app-141015134431-conversion-gate01/85/5-sharing-app-19-320.jpg)
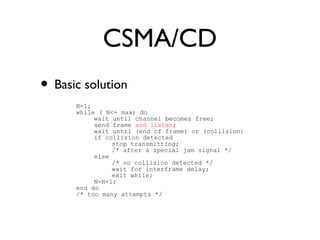
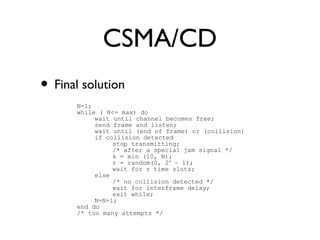
![RTS/CTS
A B C
DIFS+Backoff
Busy[
100microsec+
SIFS+
CTS+
SIFS+
ACK
]
RTS [100 microsec]
SIFS
CTS[100microsec]
Data [100 microsec]
SIFS
ACK frame
SIFS](https://image.slidesharecdn.com/5-sharing-app-141015134431-conversion-gate01/85/5-sharing-app-22-320.jpg)

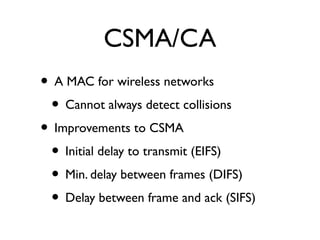
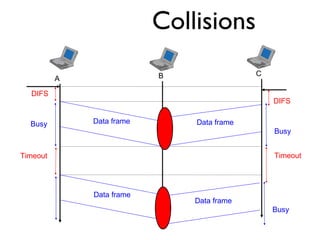
![Router output port
Q[1]
Q[2]
Q[3]
Q[N]
Flow identification
Input links
Output link
Flow identification
Identifies the TCP/UDP flow
to which the arriving packet
belongs
Buffer acceptance
accepts or rejects
incoming packets
Queuing strategy
Logical organization of the
router's buffers
Scheduler
Chooses the packet to
be transmitted first on
the output link](https://image.slidesharecdn.com/5-sharing-app-141015134431-conversion-gate01/85/5-sharing-app-27-320.jpg)