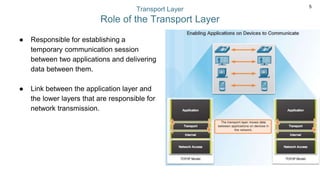
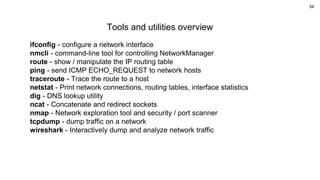
This document provides an agenda and overview of topics related to the transport layer and networking essentials. The agenda includes discussions of the transport layer, UDP overview, TCP communication process, the socket API, and tools and utilities. Specific topics that will be covered include the role and functions of the transport layer, UDP features and headers, TCP reliability mechanisms like connection establishment and termination, sequence numbers and acknowledgments, window sliding, and data loss/retransmission. The document also provides brief overviews and usage examples for common networking tools like ifconfig, nmcli, route, ping, traceroute, netstat, dig, ncat, nmap, tcpdump, and wireshark.






![35
NAME
ifconfig - configure a network interface
SYNOPSIS
ifconfig [-v] [-a] [-s] [interface]
ifconfig [-v] interface [aftype] options | address ...
DESCRIPTION
Ifconfig is used to configure the kernel-resident network interfaces. It is used at boot time
to set up interfaces as necessary. After that, it is usually only needed when debugging or
when system tuning is needed.](https://image.slidesharecdn.com/networkingessentialslect3-211119072509/85/Networking-essentials-lect3-35-320.jpg)
![36
NAME
nmcli - command-line tool for controlling NetworkManager
SYNOPSIS
nmcli [OPTIONS...] {help | general | networking | radio | connection | device | agent | monitor} [COMMAND] [ARGUMENTS...]
DESCRIPTION
nmcli is a command-line tool for controlling NetworkManager and reporting network status. It can be utilized as a r
eplacement for nm-applet or other graphical clients. nmcli is used to create, display, edit, delete, activate, and
deactivate network connections, as well as control and display network device status.](https://image.slidesharecdn.com/networkingessentialslect3-211119072509/85/Networking-essentials-lect3-36-320.jpg)
![37
NAME
route - show / manipulate the IP routing table
SYNOPSIS
route [-CFvnNee] [-A family |-4|-6]
route [-v] [-A family |-4|-6] add [-net|-host] target [netmask Nm] [gw Gw] [metric N] [mss M] [window W] [irtt I] [reject] [mod]
[dyn] [reinstate] [[dev] If]
route [-v] [-A family |-4|-6] del [-net|-host] target [gw Gw] [netmask Nm] [metric M] [[dev] If]
route [-V] [--version] [-h] [--help]](https://image.slidesharecdn.com/networkingessentialslect3-211119072509/85/Networking-essentials-lect3-37-320.jpg)
![38
NAME
ping - send ICMP ECHO_REQUEST to network hosts
SYNOPSIS
ping [-aAbBdDfhLnOqrRUvV46] [-c count] [-F flowlabel] [-i interval] [-I
interface] [-l preload] [-m mark] [-M pmtudisc_option] [-N node info_option] [-w deadline] [-W timeout] [-p pattern] [-Q
tos] [-s packetsize] [-S sndbuf] [-t ttl] [-T timestamp option] [hop ...] destination
DESCRIPTION
ping uses the ICMP protocol's mandatory ECHO_REQUEST datagram to elicit
an ICMP ECHO_RESPONSE from a host or gateway.](https://image.slidesharecdn.com/networkingessentialslect3-211119072509/85/Networking-essentials-lect3-38-320.jpg)
![39
NAME
traceroute - Trace the route to a host
SYNOPSIS
traceroute [OPTION...] HOST
DESCRIPTION
Print the route packets trace to network host.
-f, --first-hop=NUM Set initial hop distance, that is the time-to-live.
-g, --gateways=GATES List of gateways for loose source routing.
-I, --icmp Use ICMP ECHO as probe.](https://image.slidesharecdn.com/networkingessentialslect3-211119072509/85/Networking-essentials-lect3-39-320.jpg)
![40
NAME
netstat - Print network connections, routing tables, interface statistics, masquerade connections, and multicast memberships
SYNOPSIS
netstat [address_family_options] [--tcp|-t] [--udp|-u] [--udplite|-U] [--sctp|-S] [--raw|-w] [--l2cap|-2] [--rfcomm|-f] [--listening|-
l] [--all|-a] [--numeric|-n] [--numeric-hosts] [--numeric-ports] [--numeric-users] [--symbolic|-N] [--extend|-e[--extend|-e]] [--
timers|-o] [--program|-p] [--verbose|-v] [--continuous|-c] [--wide|-W]
netstat {--route|-r} [address_family_options] [--extend|-e[--extend|-e]] [--verbose|-v] [--numeric|-n] [--numeric-hosts]
[--numeric-ports] [--numeric-users] [--continuous|-c]](https://image.slidesharecdn.com/networkingessentialslect3-211119072509/85/Networking-essentials-lect3-40-320.jpg)
![41
NAME
dig - DNS lookup utility
SYNOPSIS
dig [@server] [-b address] [-c class] [-f filename] [-k filename] [-m] [-p port#] [-q name] [-t type] [-v] [-x addr] [-y
[hmac:]name:key] [[-4] | [-6]] [name] [type] [class] [queryopt...]
dig [-h]
dig [global-queryopt...] [query...]
DESCRIPTION
dig is a flexible tool for interrogating DNS name servers. It performs DNS lookups and displays the answers that are returned
from the name server(s) that were queried. Most DNS administrators use dig to troubleshoot DNS problems because of its
flexibility, ease of use and clarity of output. Other lookup tools tend to have less functionality than dig.](https://image.slidesharecdn.com/networkingessentialslect3-211119072509/85/Networking-essentials-lect3-41-320.jpg)
![42
NAME
ncat - Concatenate and redirect sockets
SYNOPSIS
ncat [OPTIONS...] [hostname] [port]
DESCRIPTION
Ncat is a feature-packed networking utility which reads and writes data across networks from the command line. Ncat was
written for the Nmap Project and is the culmination of the currently splintered family of Netcat incarnations.
-p, --source-port port Specify source port to use
-s, --source addr Specify source address to use (doesn't affect -l)
-l, --listen Bind and listen for incoming connections
-k, --keep-open Accept multiple connections in listen mode
-n, --nodns Do not resolve hostnames via DNS
-t, --telnet Answer Telnet negotiations
-u, --udp Use UDP instead of default TCP
Echo server - ncat -l 12345 -k -c 'xargs -n1 echo'
Server Client](https://image.slidesharecdn.com/networkingessentialslect3-211119072509/85/Networking-essentials-lect3-42-320.jpg)
![43
NAME
nmap - Network exploration tool and security / port scanner
SYNOPSIS
nmap [Scan Type...] [Options] {target specification}
DESCRIPTION
Nmap (“Network Mapper”) is an open source tool for network exploration and security auditing. It was designed to rapidly
scan large networks, although it works fine against single hosts. Nmap uses raw IP packets in novel ways to determine what
hosts are available on the network, what services (application name and version) those hosts are offering, what operating
systems (and OS versions) they are running, what type of packet filters/firewalls are in use, and dozens of other characteristics.](https://image.slidesharecdn.com/networkingessentialslect3-211119072509/85/Networking-essentials-lect3-43-320.jpg)
![44
NAME
tcpdump - dump traffic on a network
SYNOPSIS
tcpdump [ -AbdDefhHIJKlLnNOpqStuUvxX# ] [ -B buffer_size ]
[ -c count ]
[ -C file_size ] [ -G rotate_seconds ] [ -F file ]
[ -i interface ] [ -j tstamp_type ] [ -m module ] [ -M secret ]
DESCRIPTION
Tcpdump prints out a description of the contents of packets on a network interface that match the boolean expression; the
description is preceded by a time stamp, printed, by default, as hours, minutes, seconds, and fractions of a second since
midnight.
tcpdump -i eth0
tcpdump host 1.1.1.1
tcpdump port 80 -w capture_file.pcap](https://image.slidesharecdn.com/networkingessentialslect3-211119072509/85/Networking-essentials-lect3-44-320.jpg)
![45
NAME
wireshark - Interactively dump and analyze network traffic
SYNOPSIS
wireshark [ -a <capture autostop condition> ] ...
[ -b <capture ring buffer option> ] ... [ -B <capture buffer size> ]
[ -c <capture packet count> ] [ -C <configuration profile> ]
DESCRIPTION
Wireshark is a GUI network protocol analyzer. It lets you interactively browse packet data from a live network or from a
previously saved capture file. Wireshark's native capture file format is pcap format, which is also the format used by tcpdump and
various other tools.](https://image.slidesharecdn.com/networkingessentialslect3-211119072509/85/Networking-essentials-lect3-45-320.jpg)