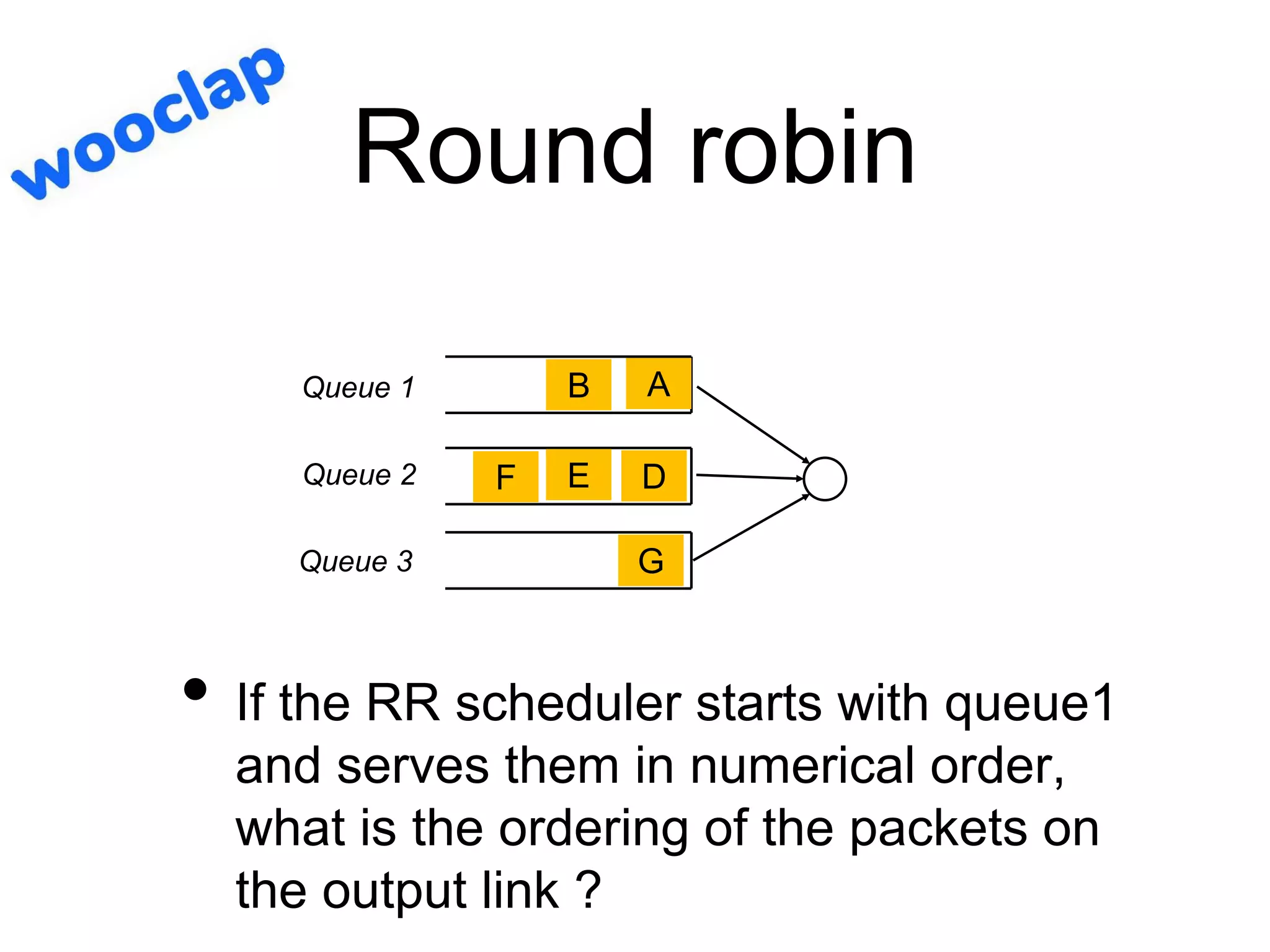
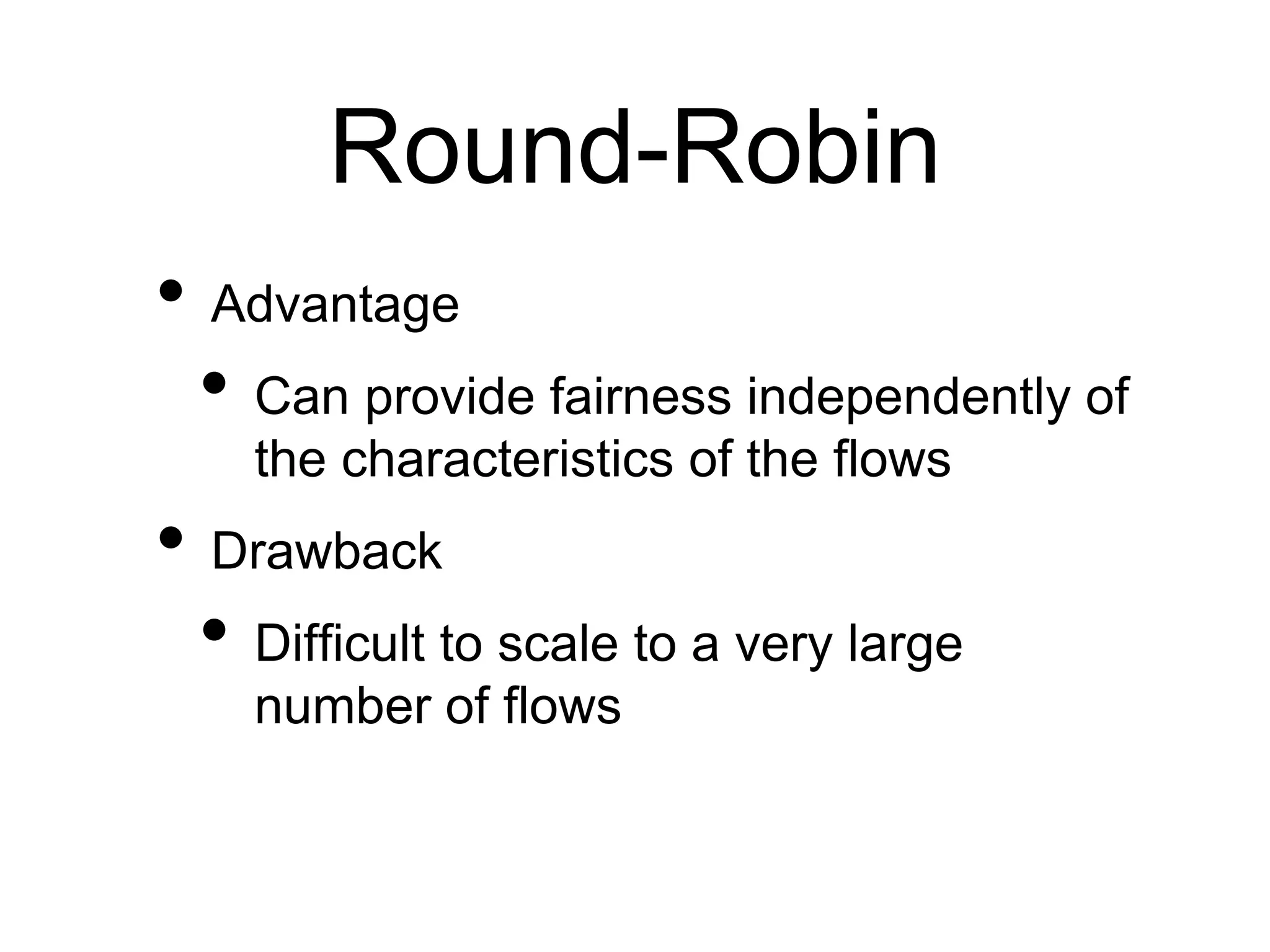
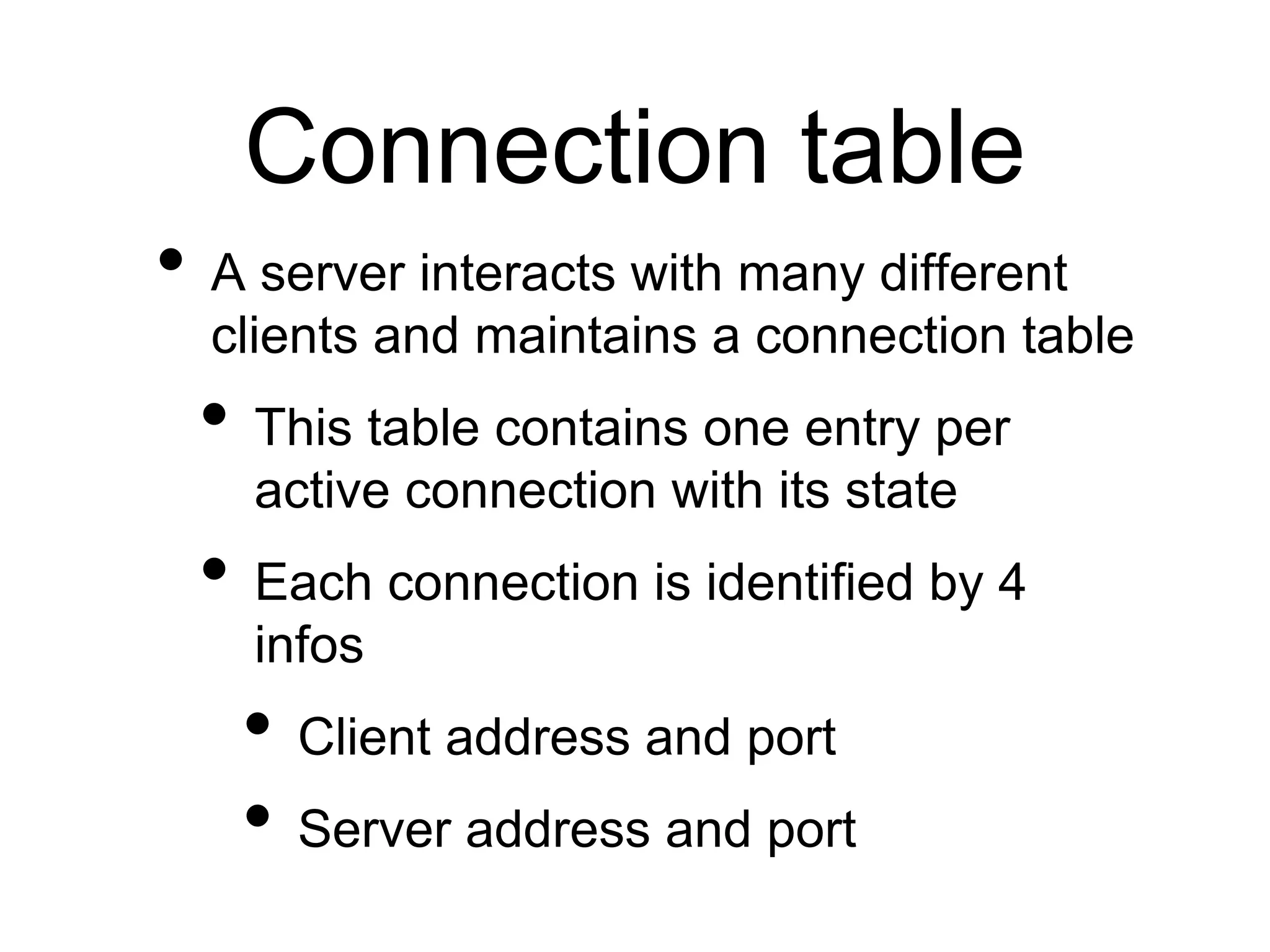
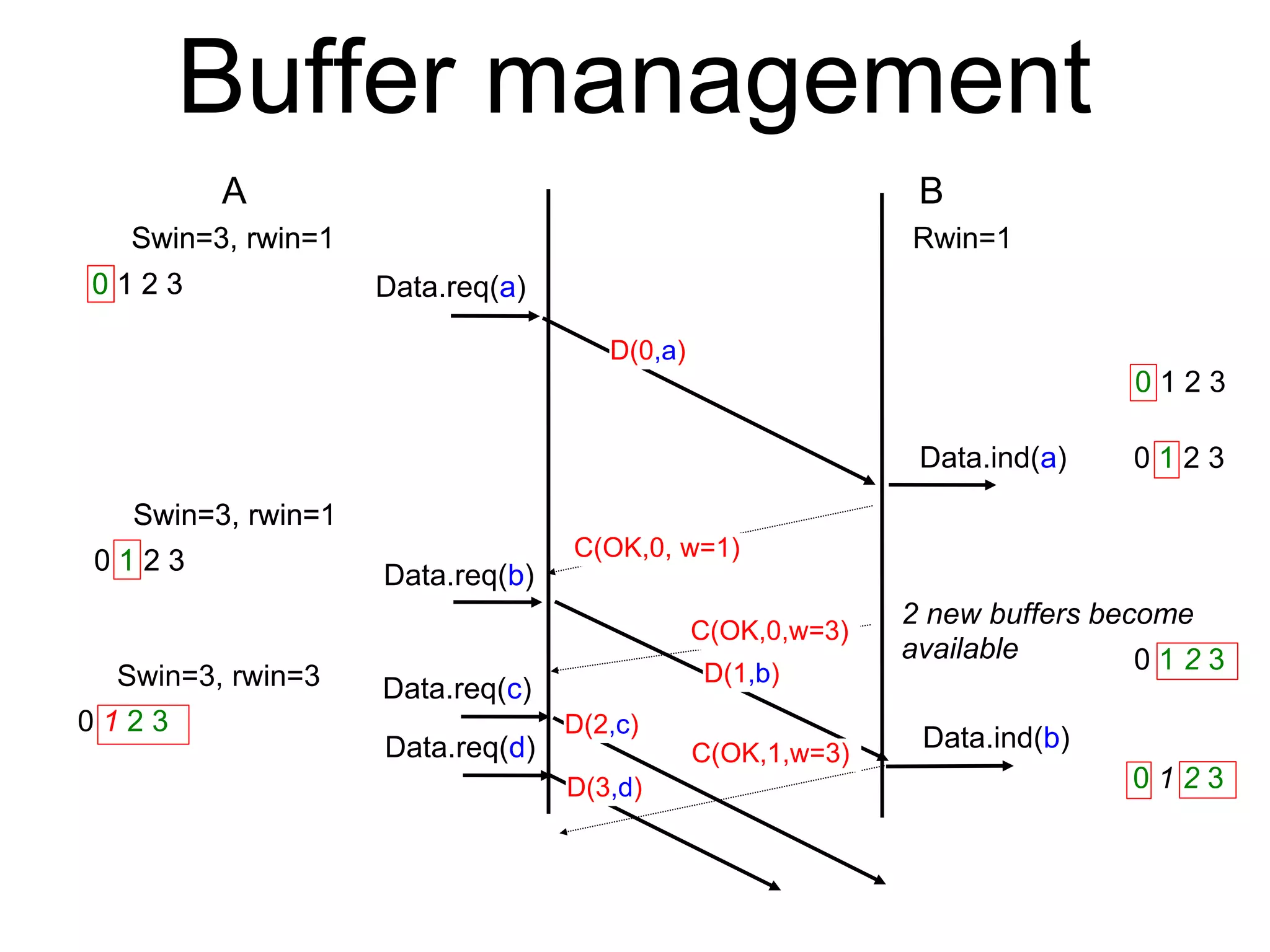
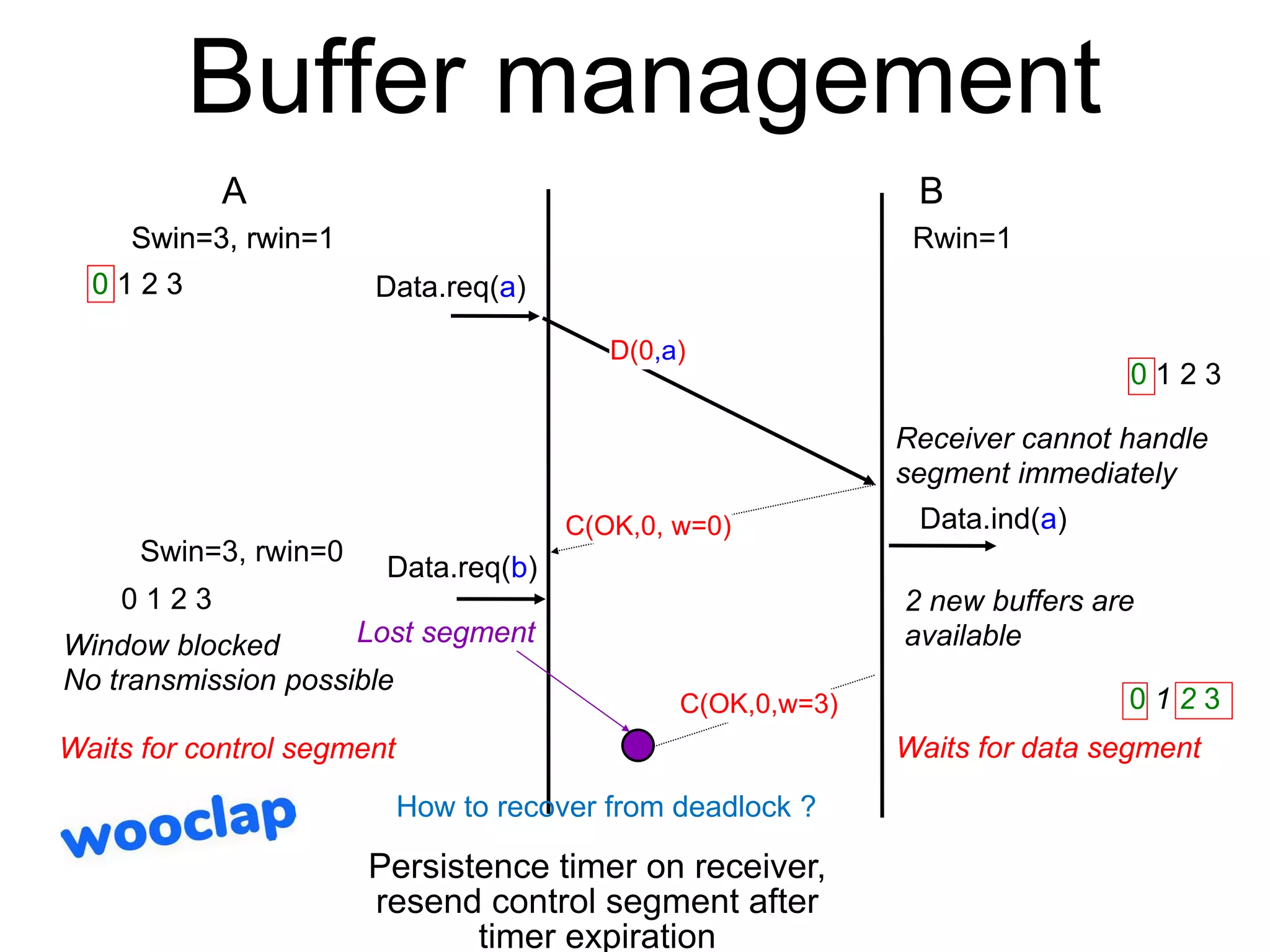
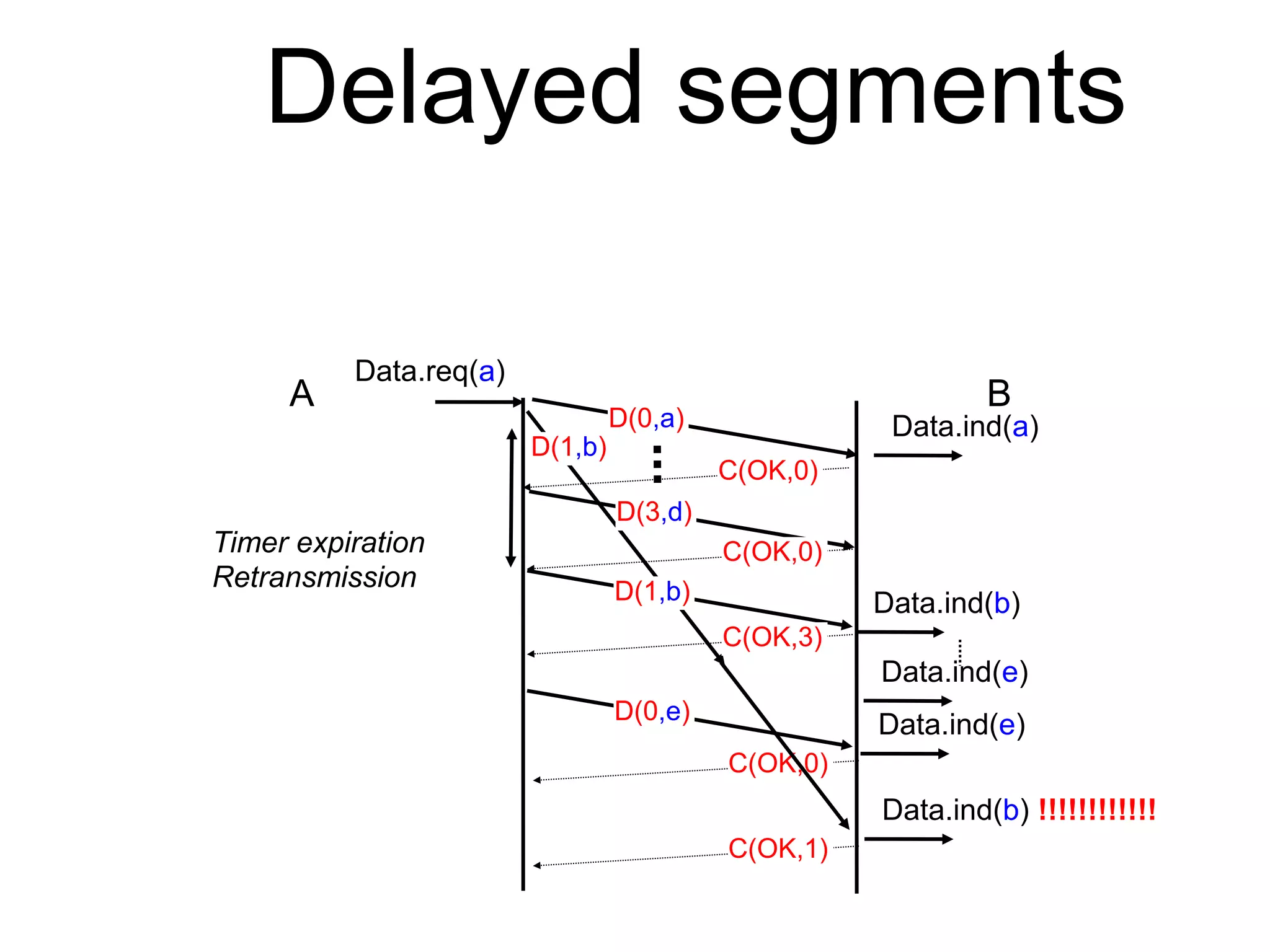
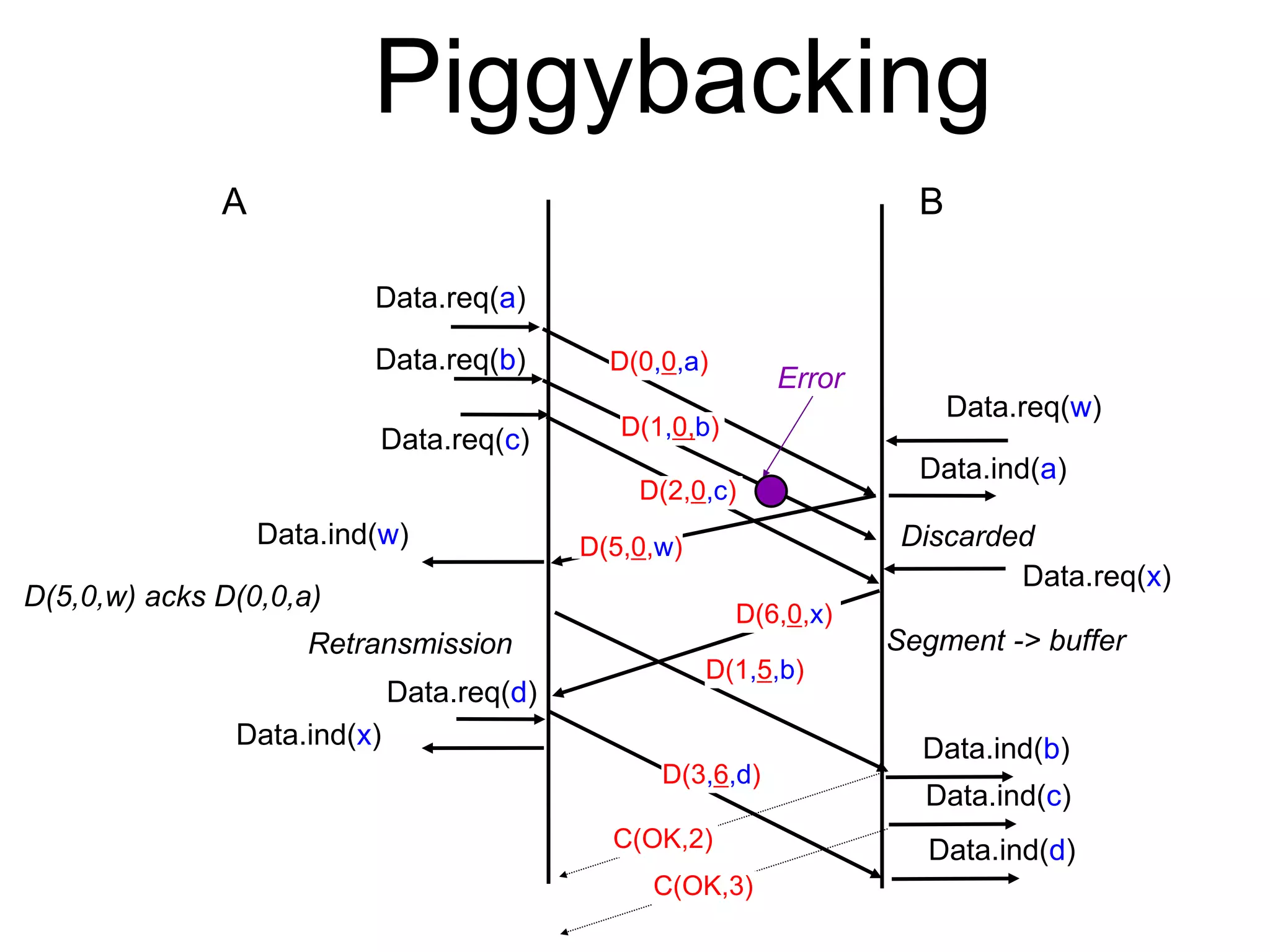
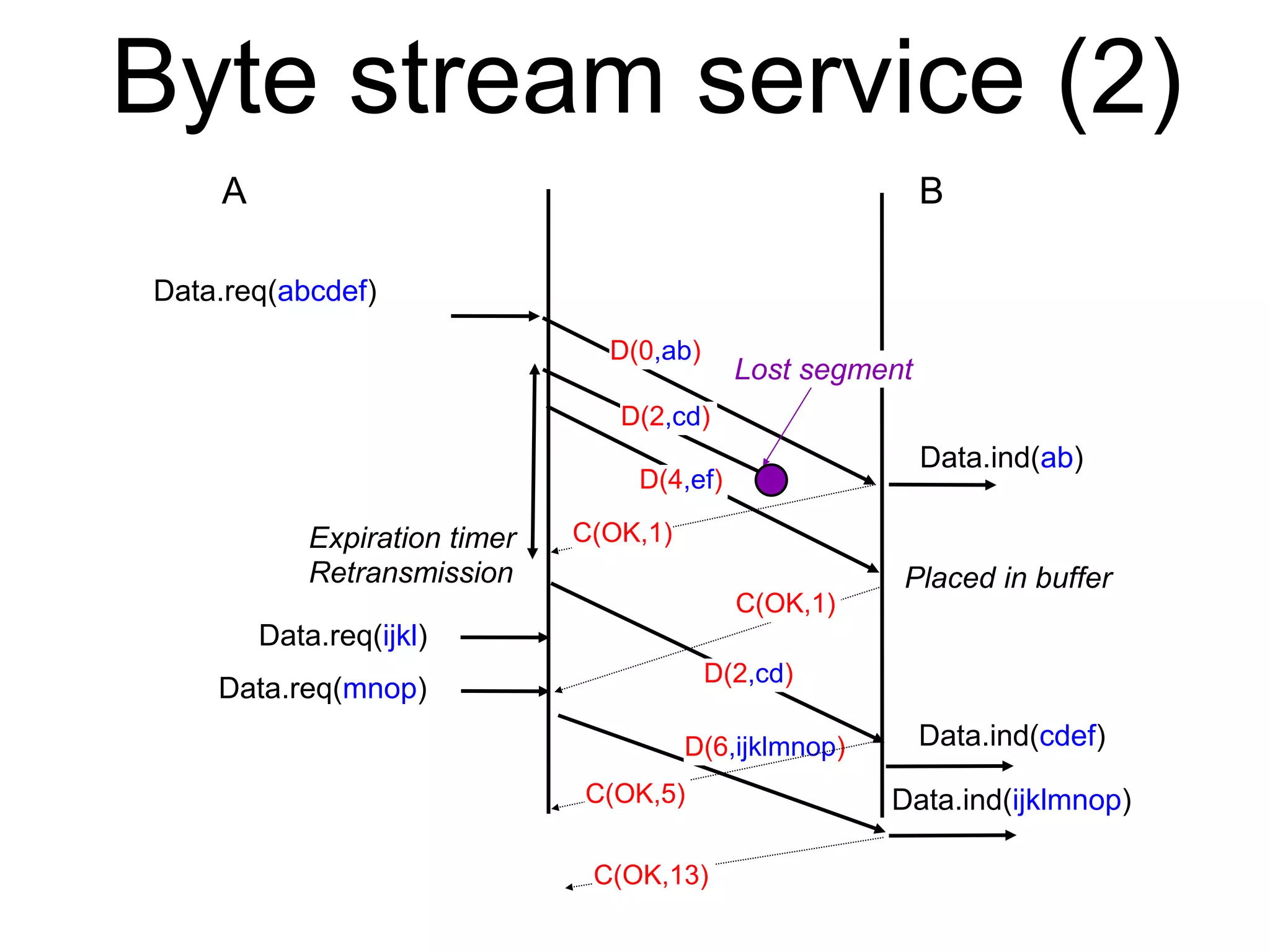
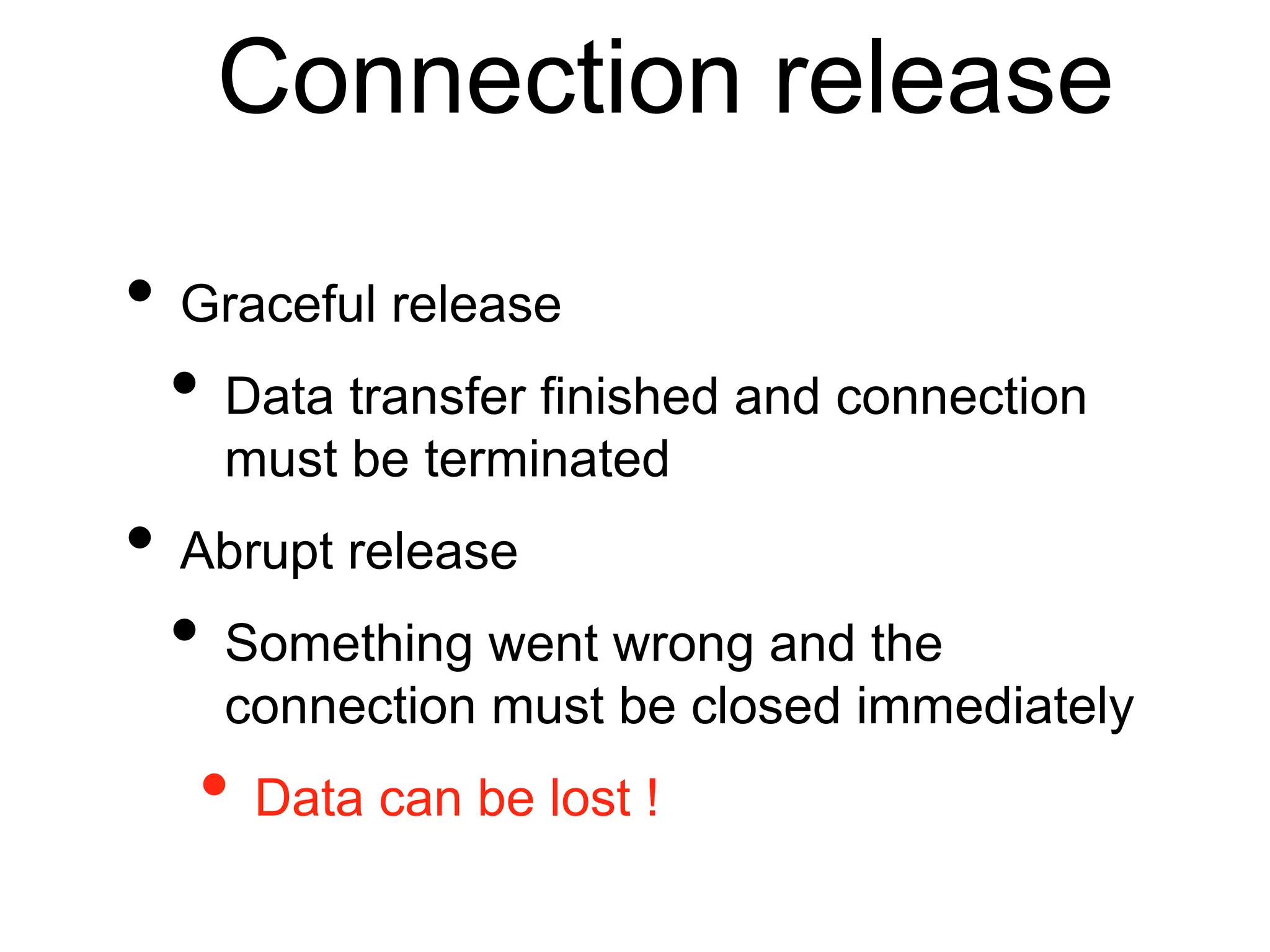
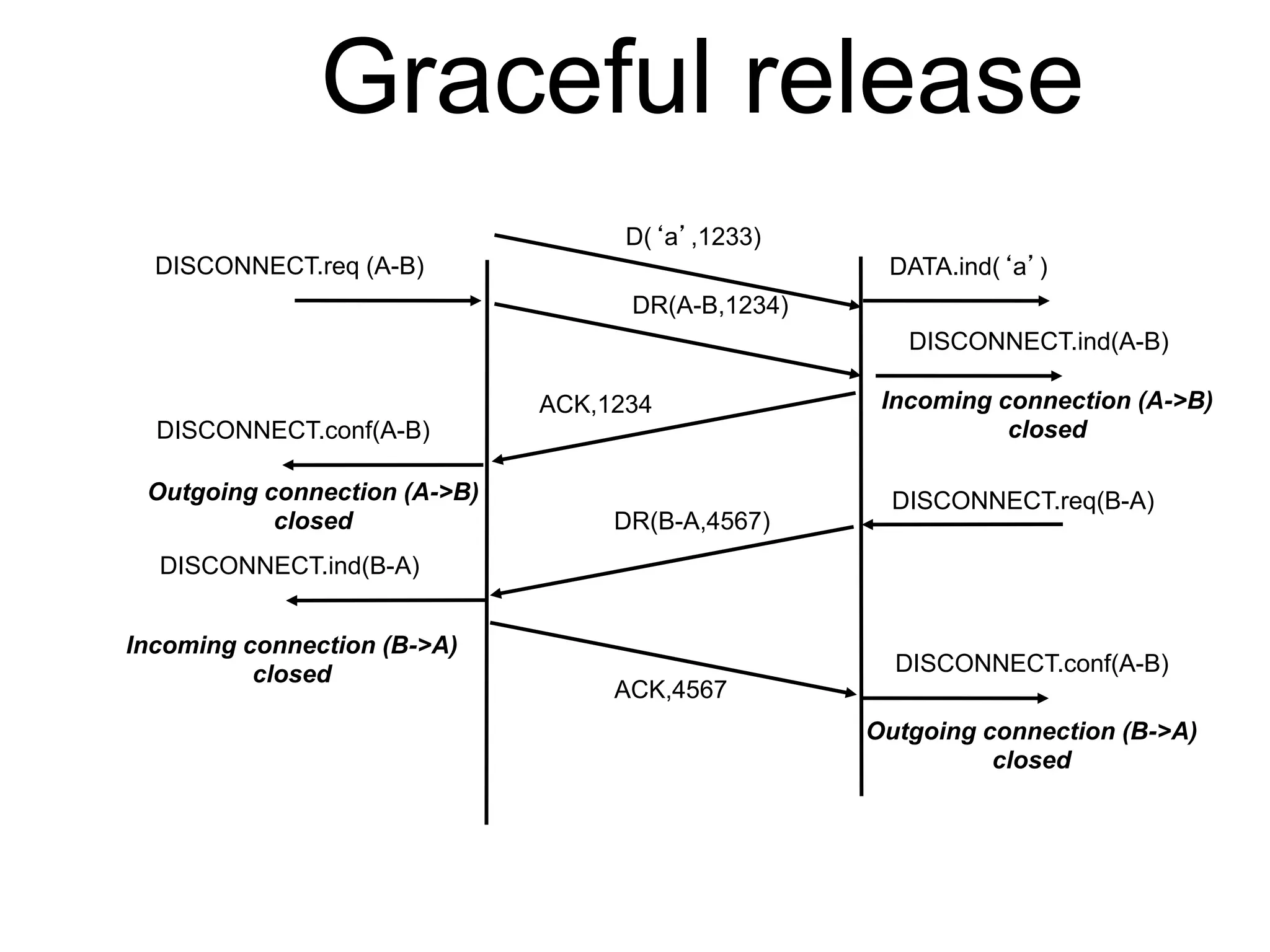
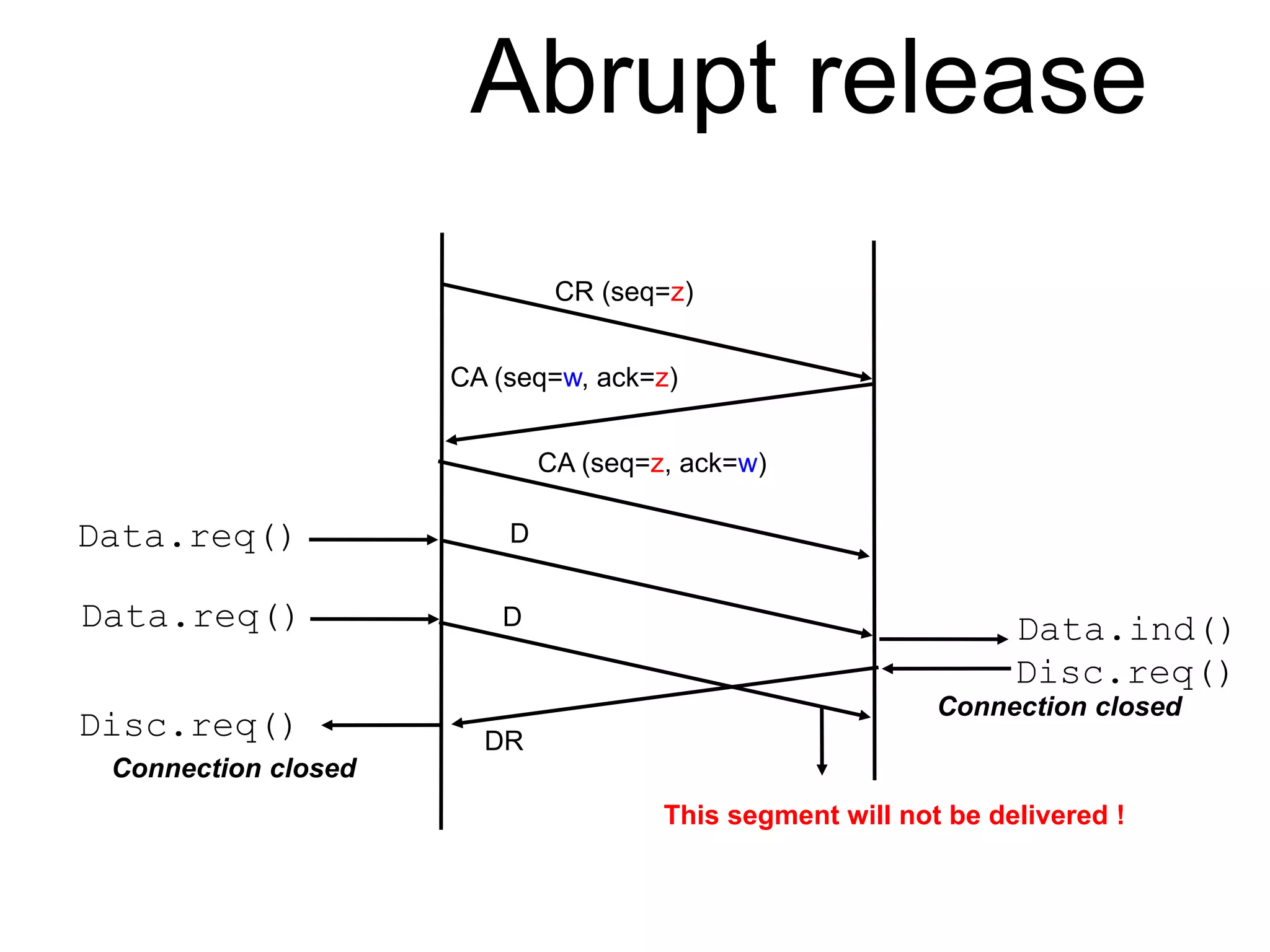
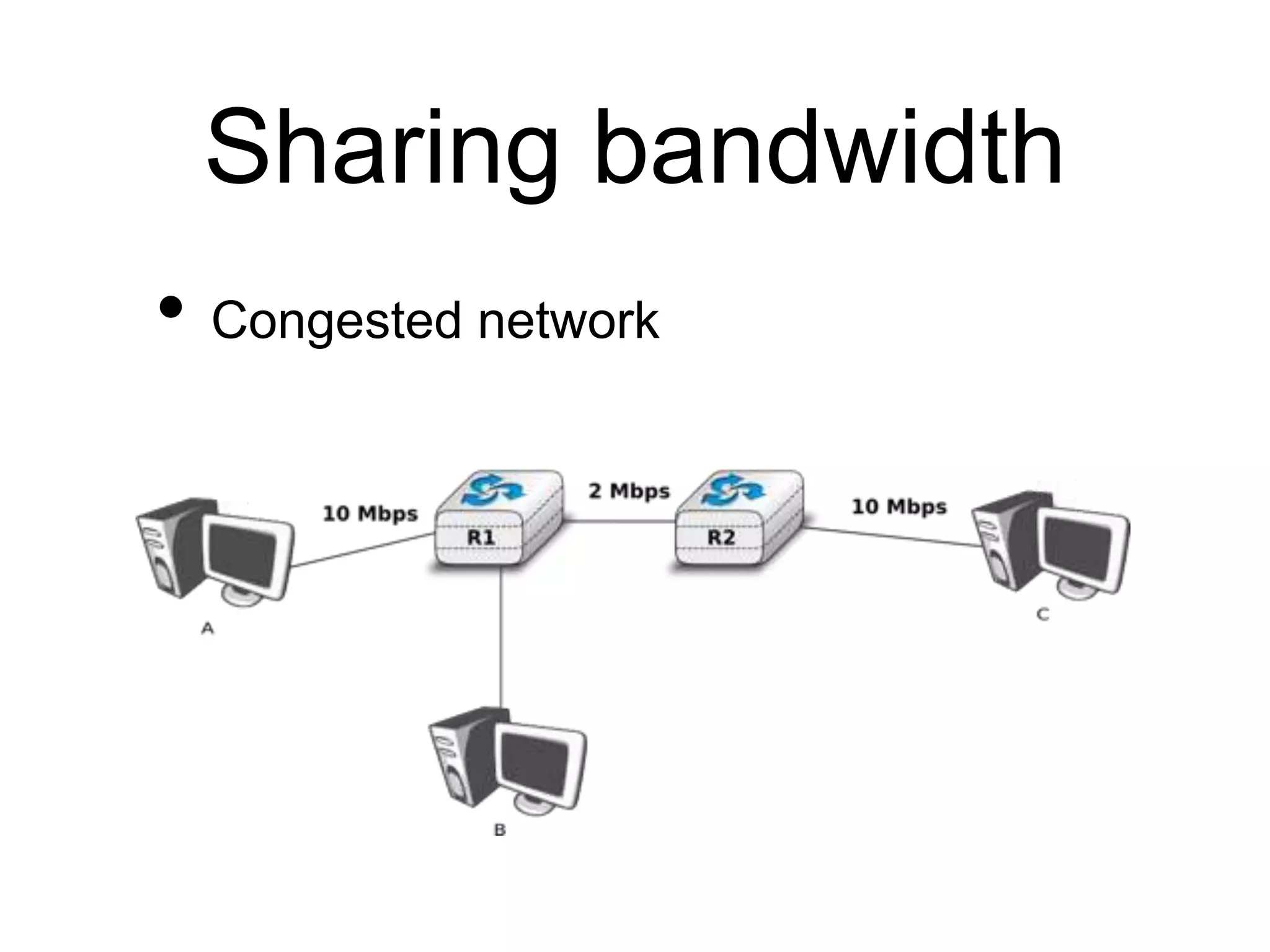
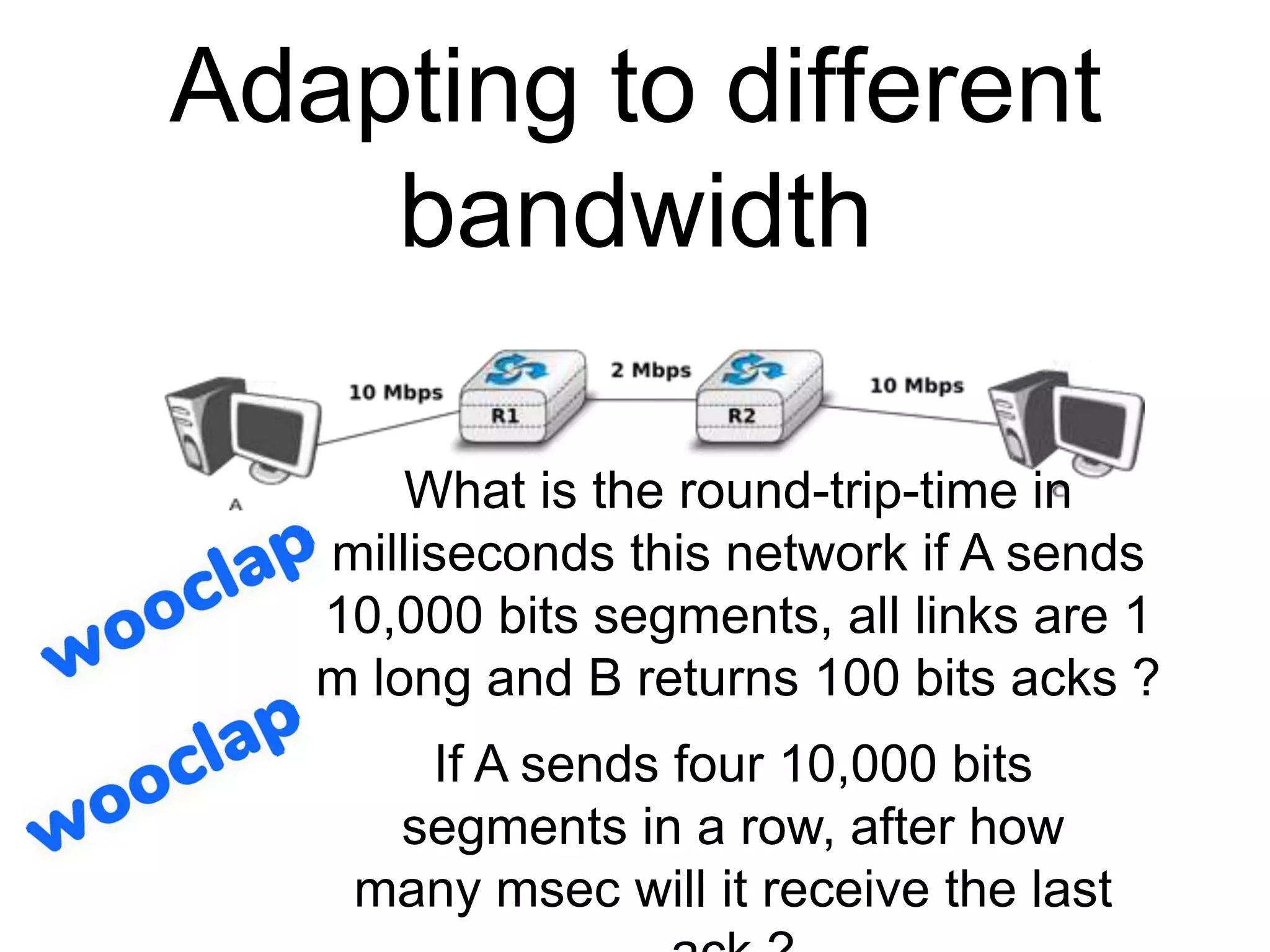
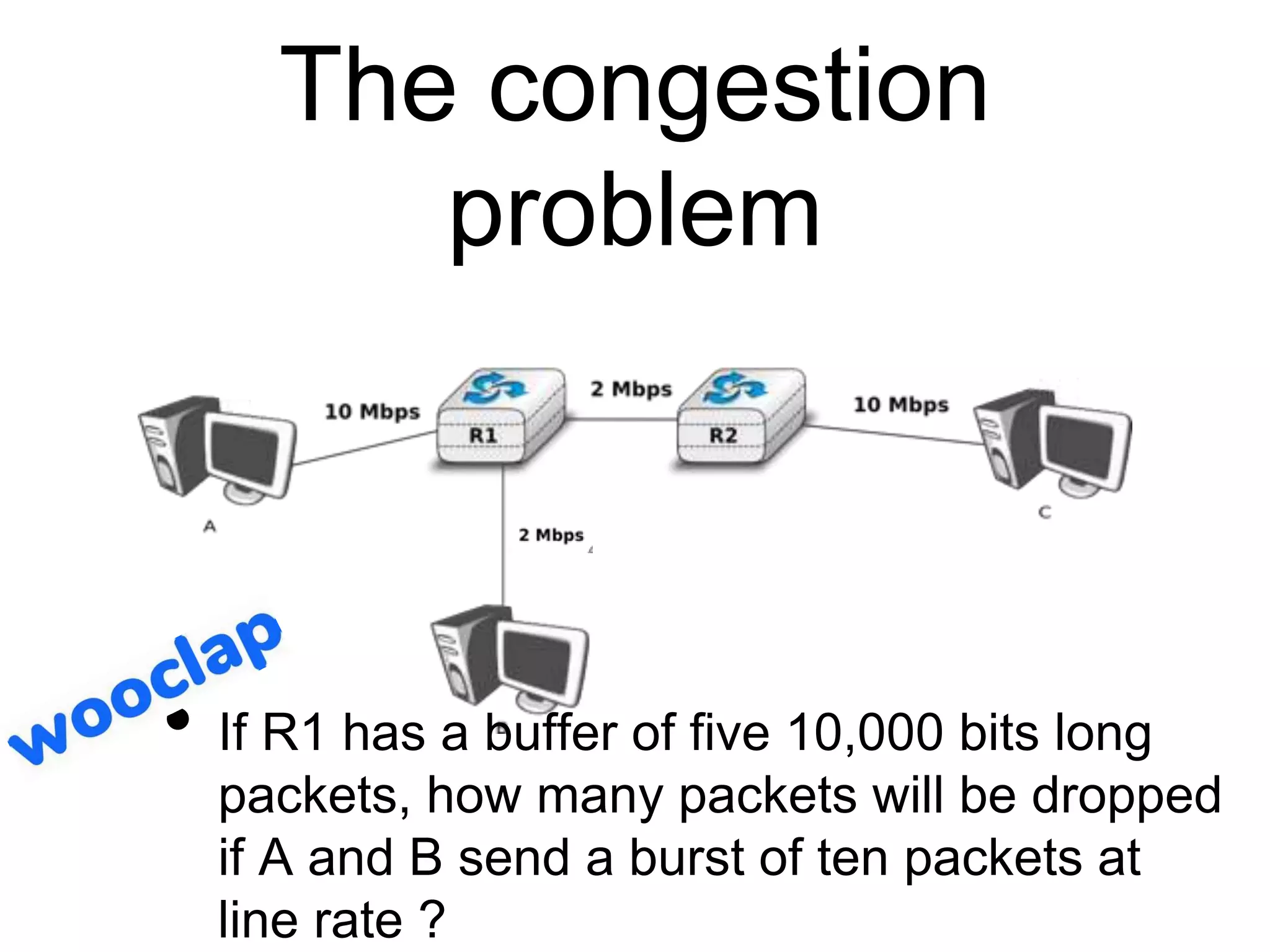
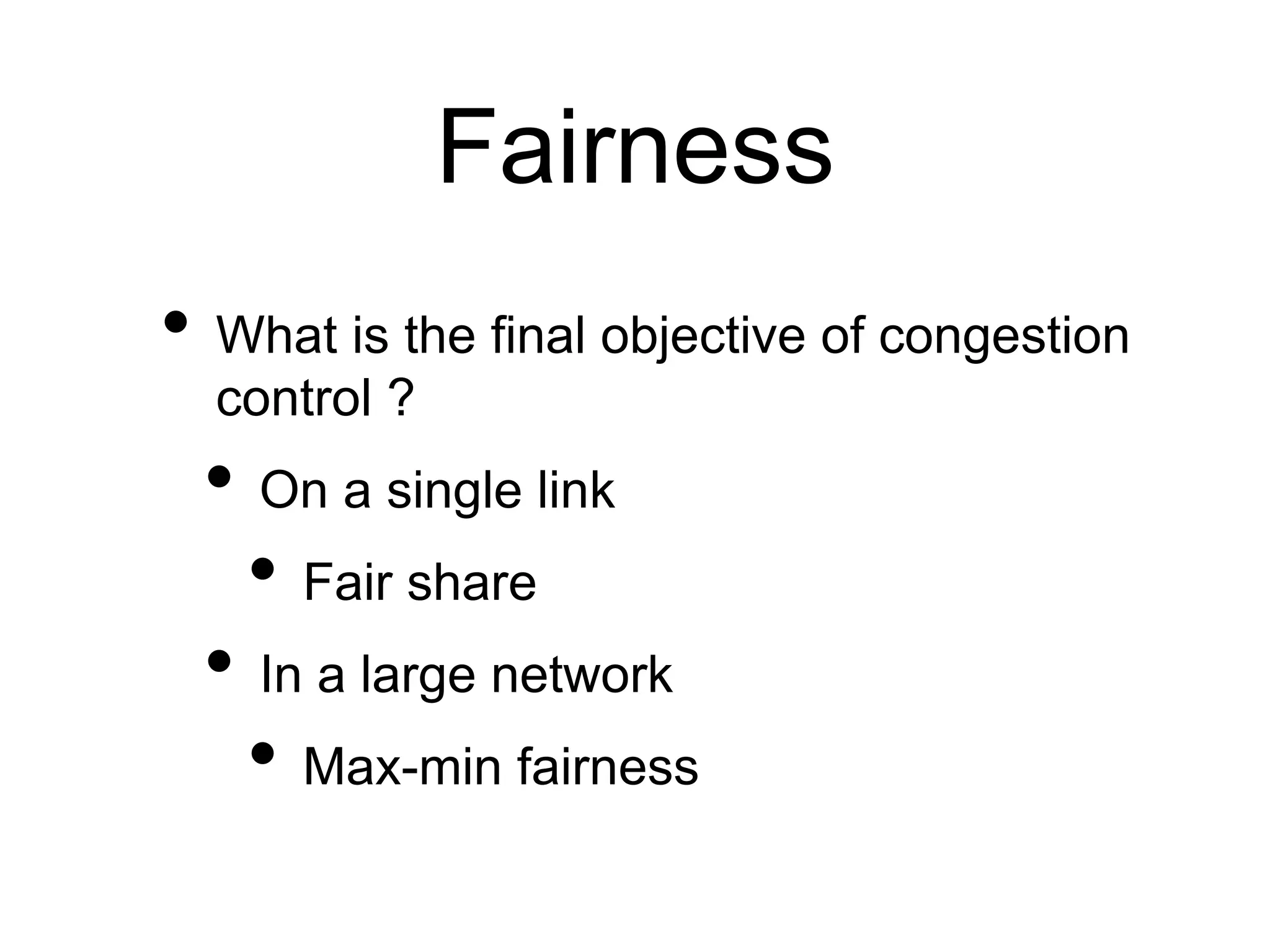
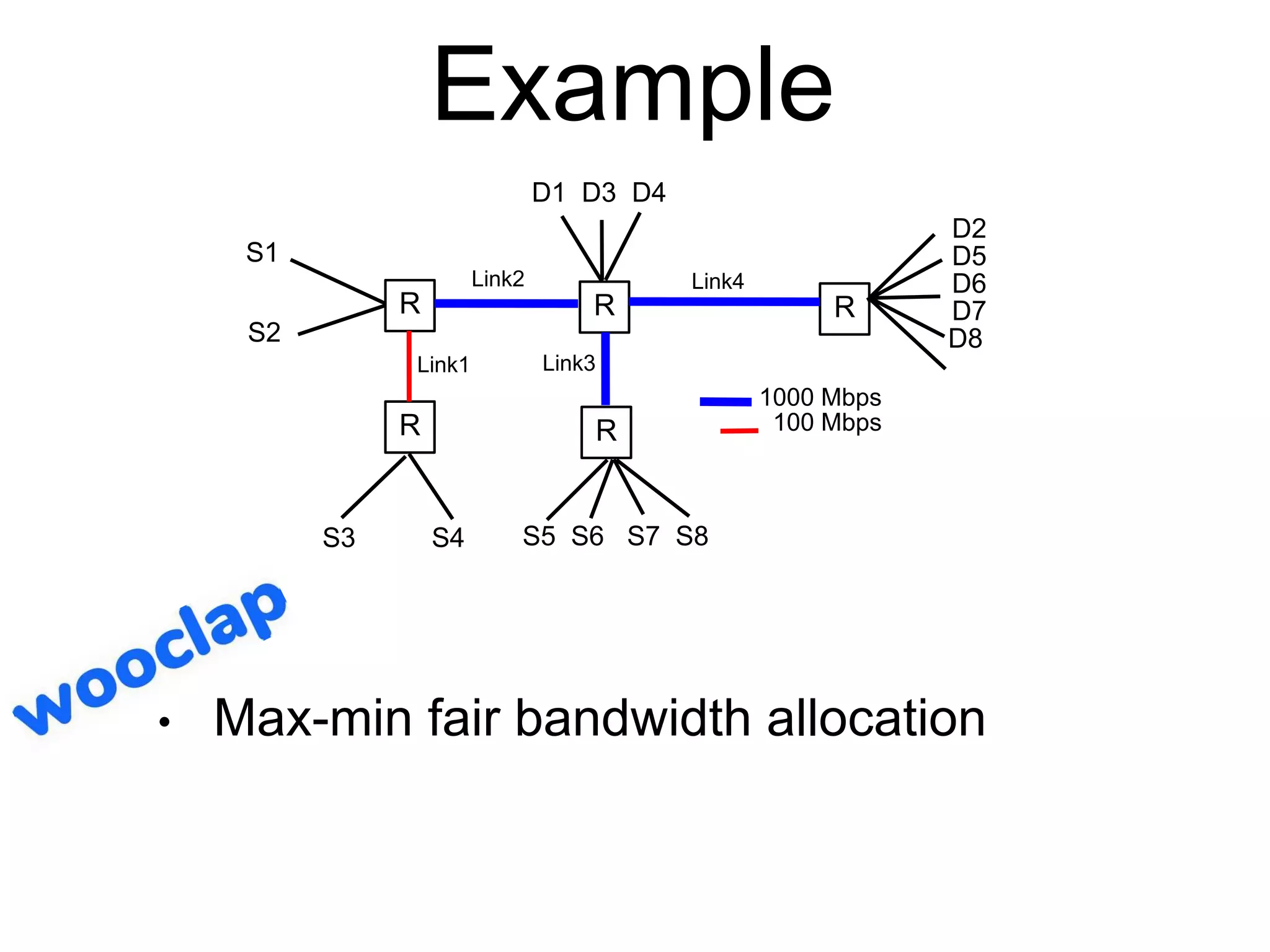
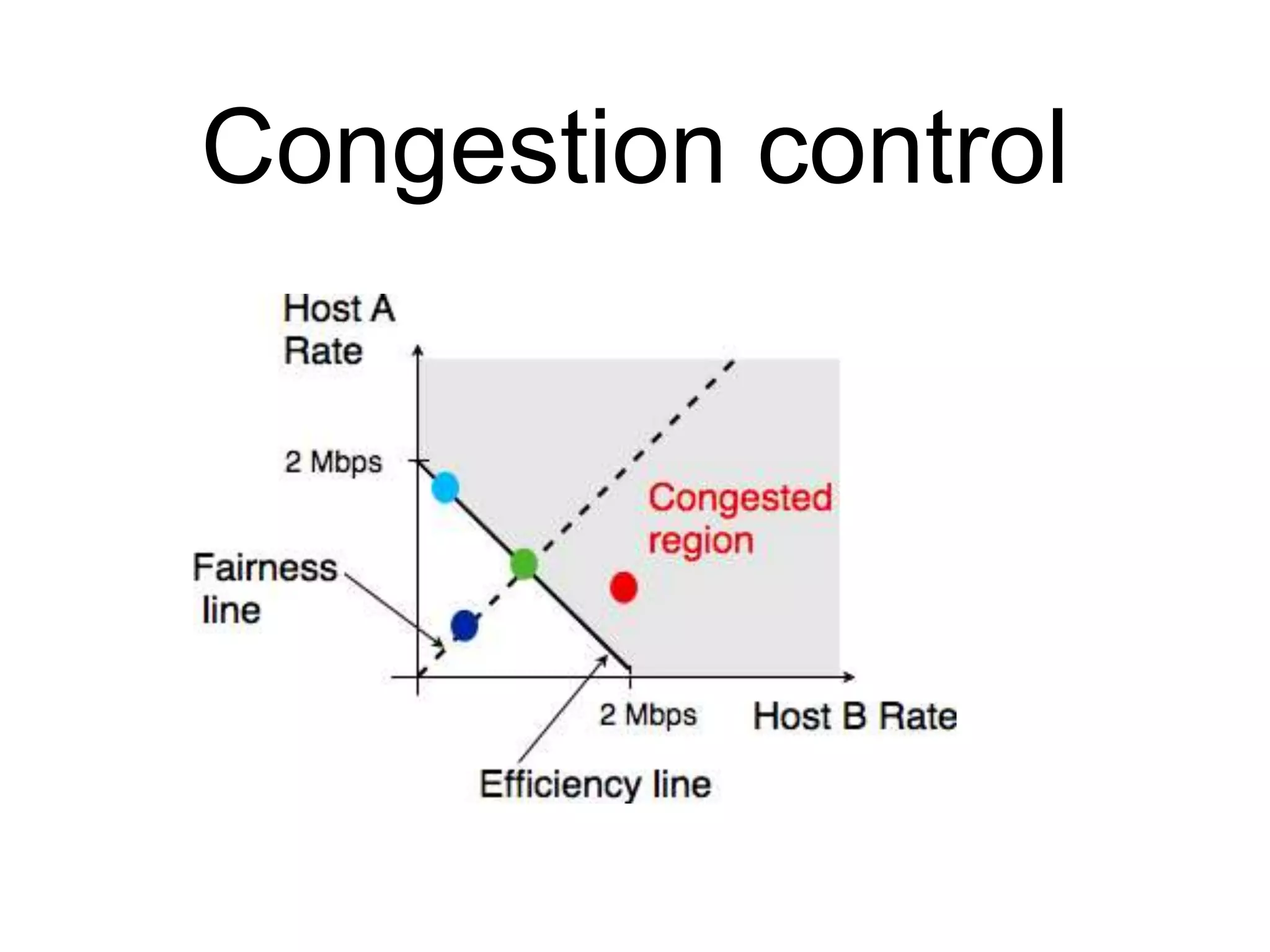
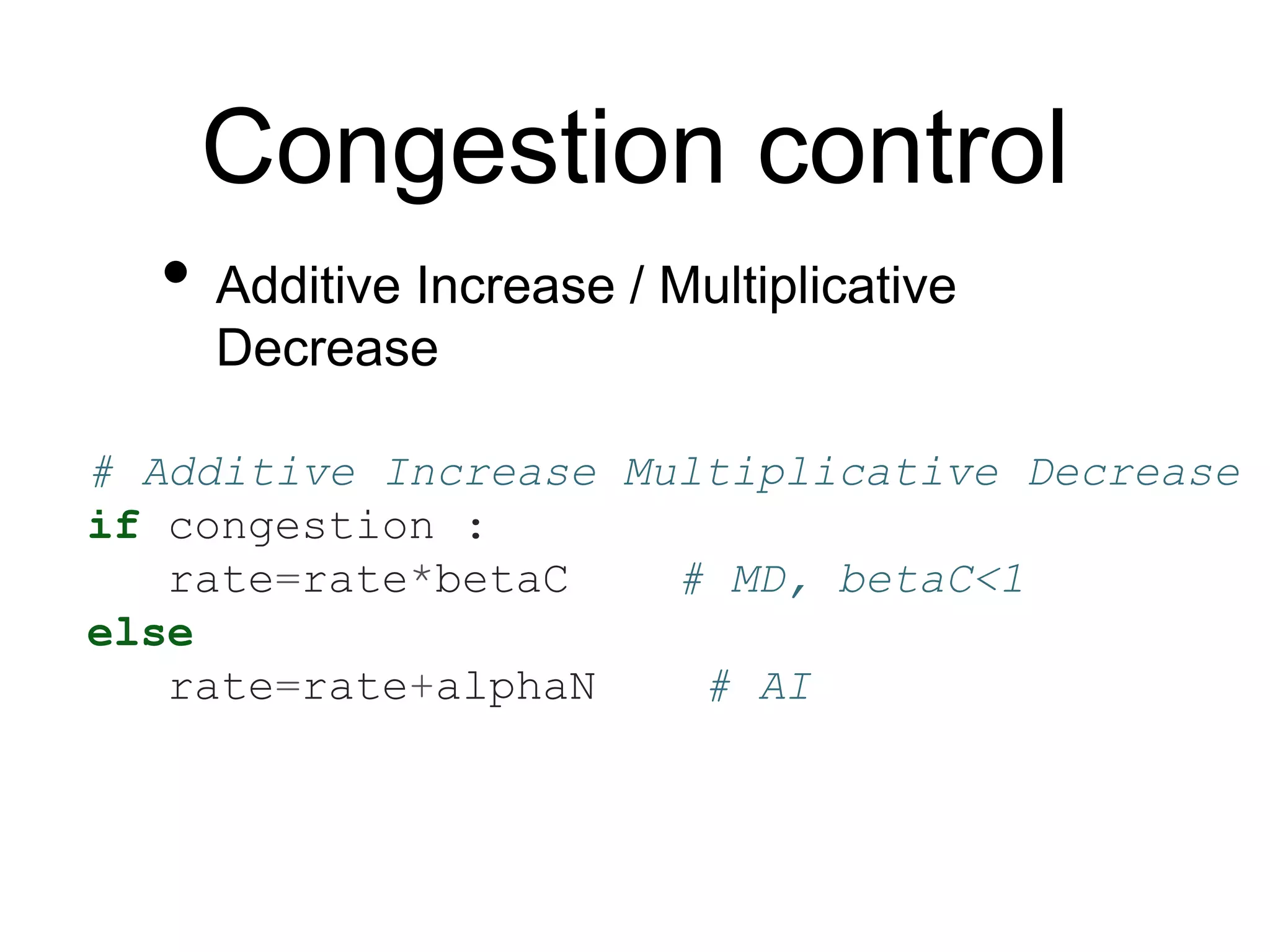
The document discusses concepts of reliable transport, including multiplexing, connection establishment, data transfer, connection release, and resource sharing. It outlines the importance of managing connections through a connection table and describes techniques for dealing with delayed segments and congestion control. The document also emphasizes max-min fairness in bandwidth allocation and methods to detect and manage congestion in network systems.

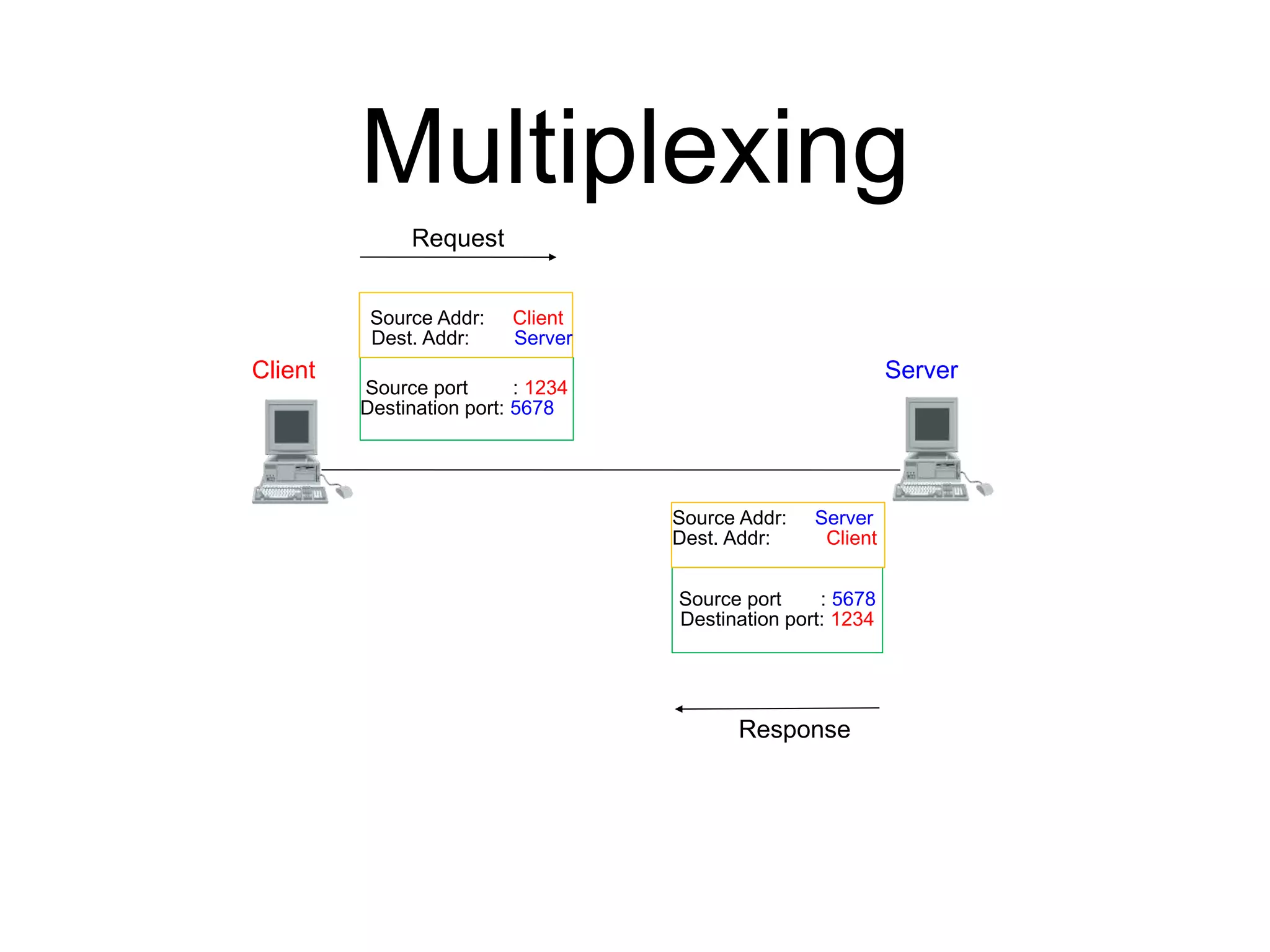
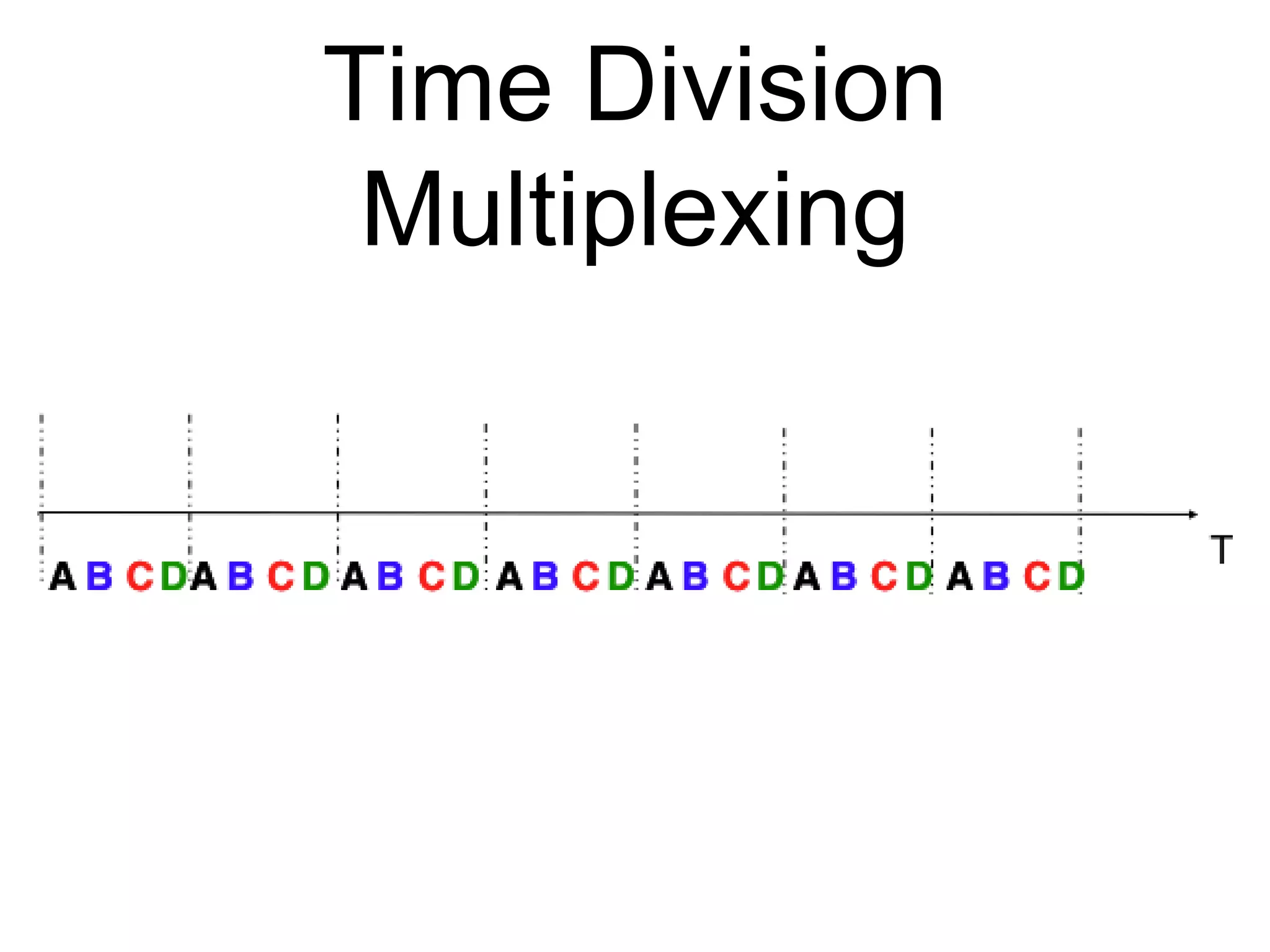
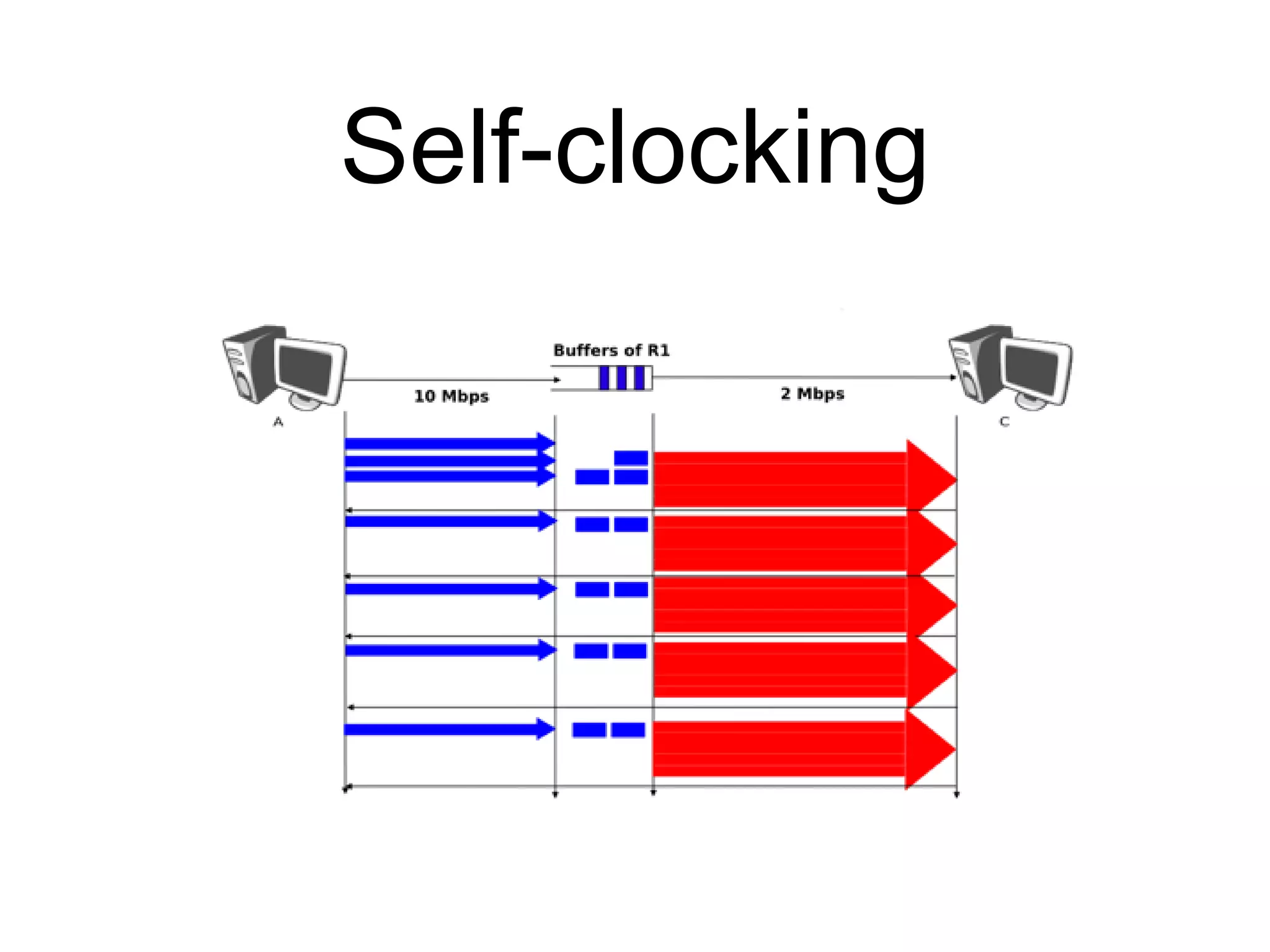
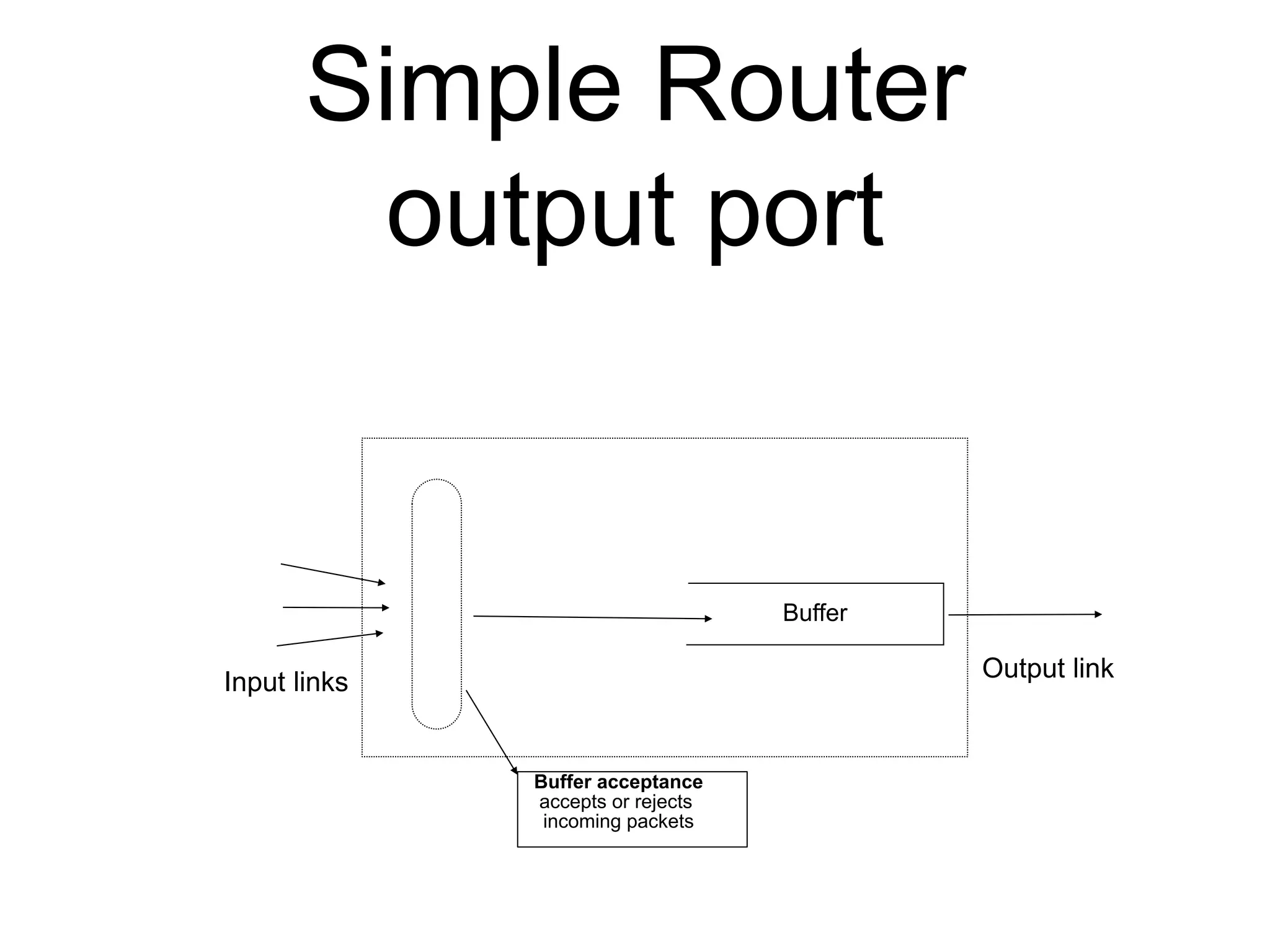
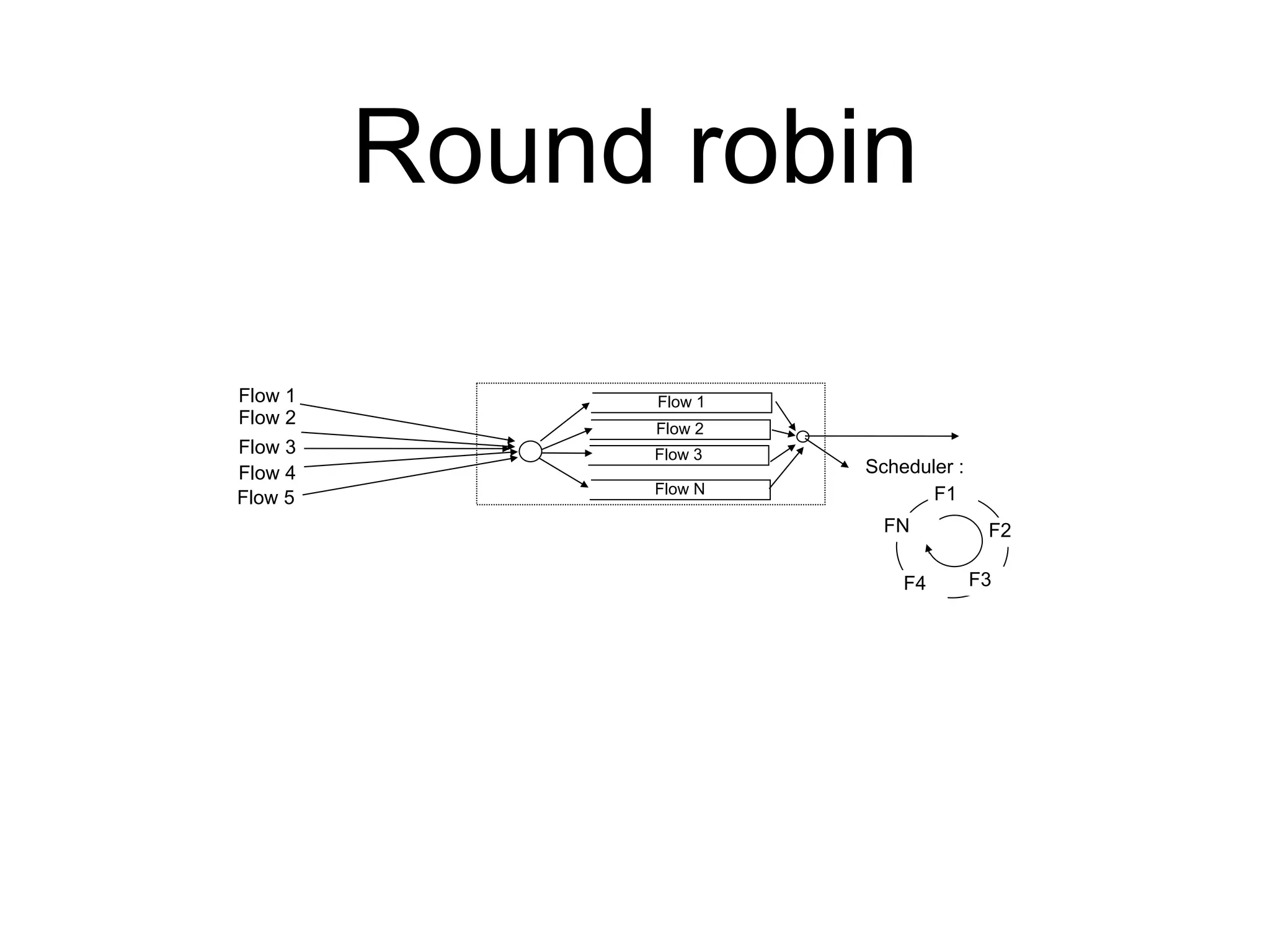
![Router output port
Q[1]
Q[2]
Q[3]
Q[N]
Flow identification
Input links
Output link
Flow identification
Identifies the TCP/UDP flow
to which the arriving packet
belongs
Buffer acceptance
accepts or rejects
incoming packets
Queuing strategy
Logical organization of the
router's buffers
Scheduler
Chooses the packet to
be transmitted first on
the output link](https://image.slidesharecdn.com/4-transport-sharing-210507084522/75/Part-4-reliable-transport-and-sharing-resources-50-2048.jpg)