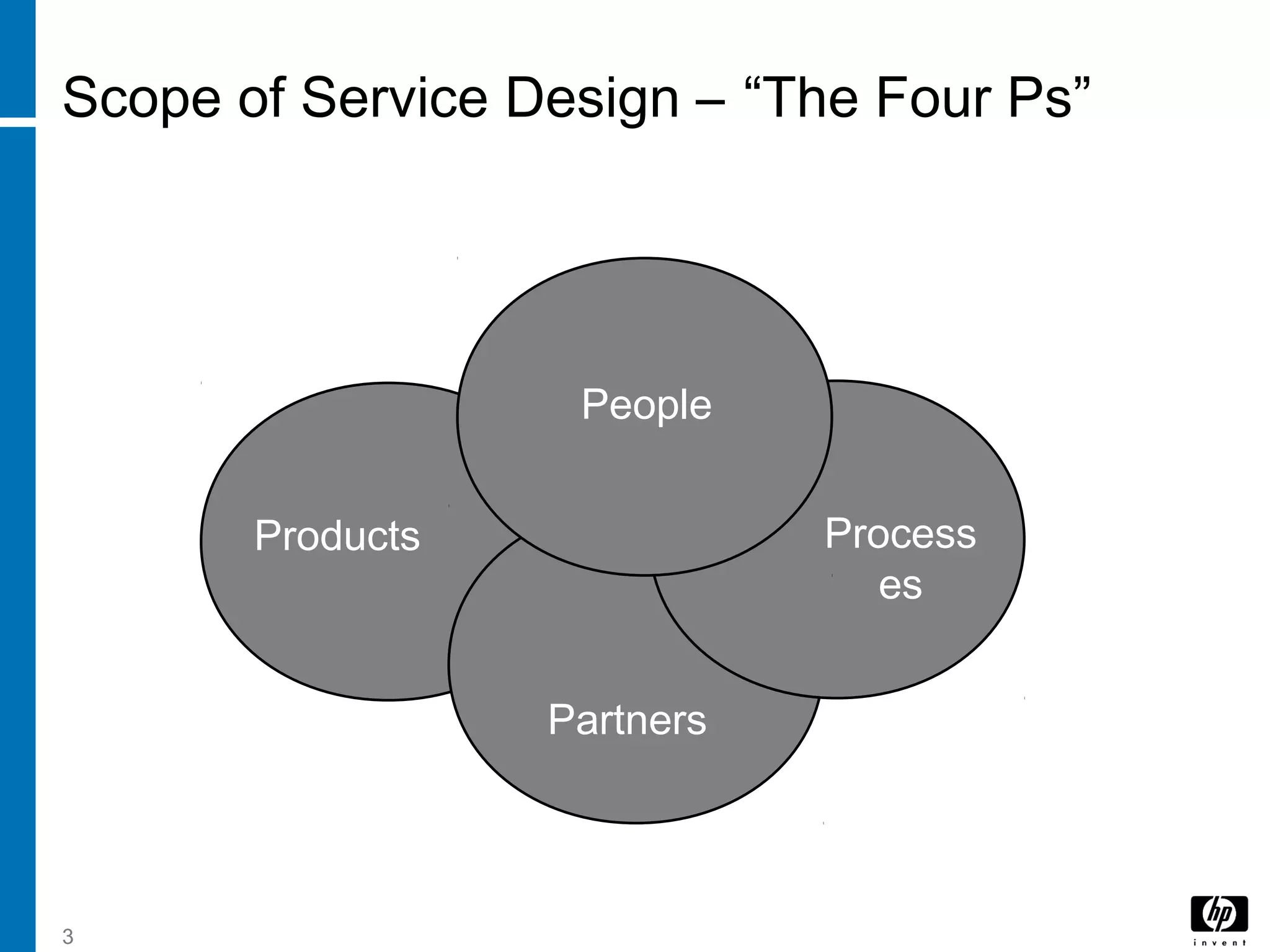
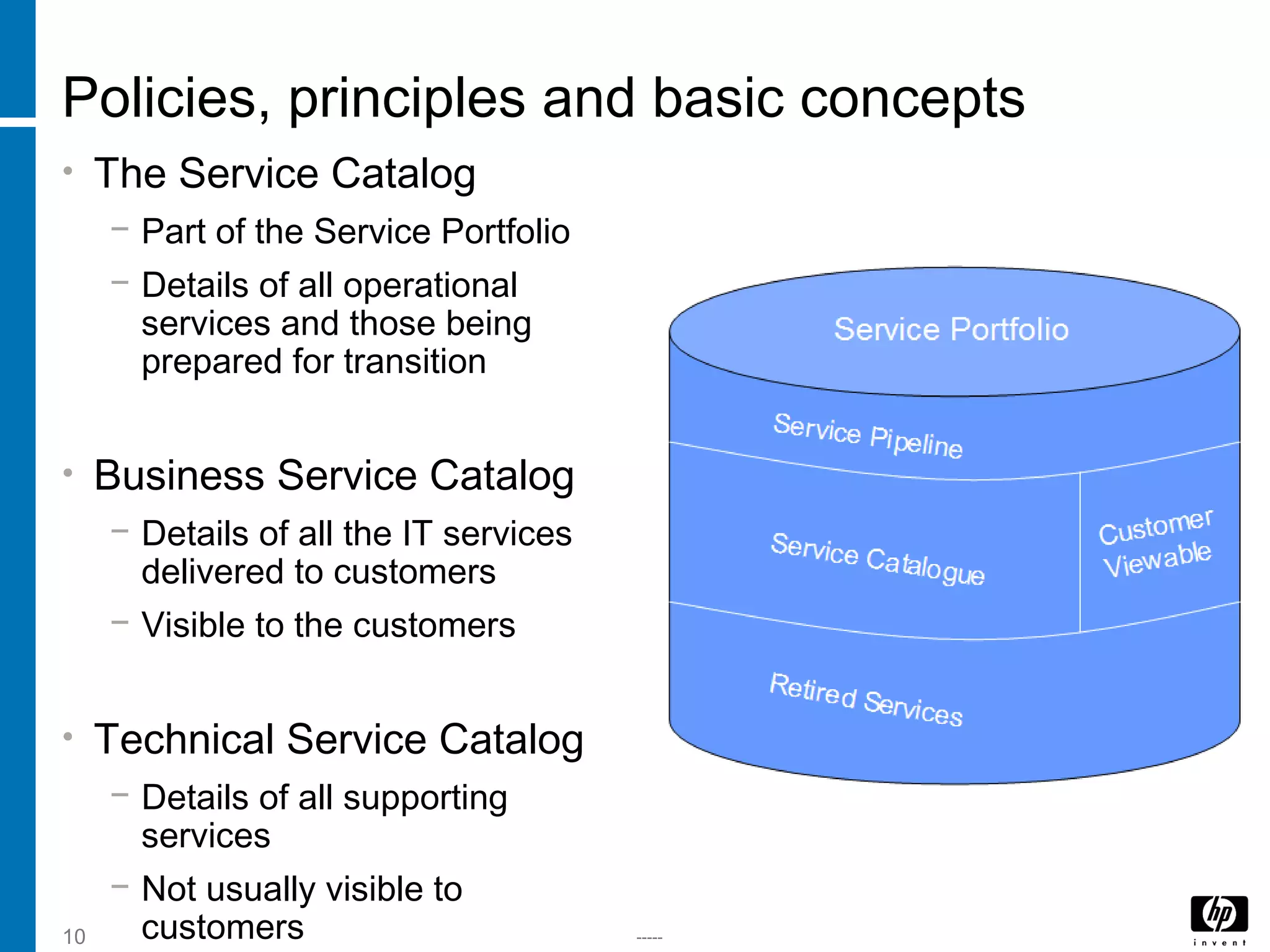
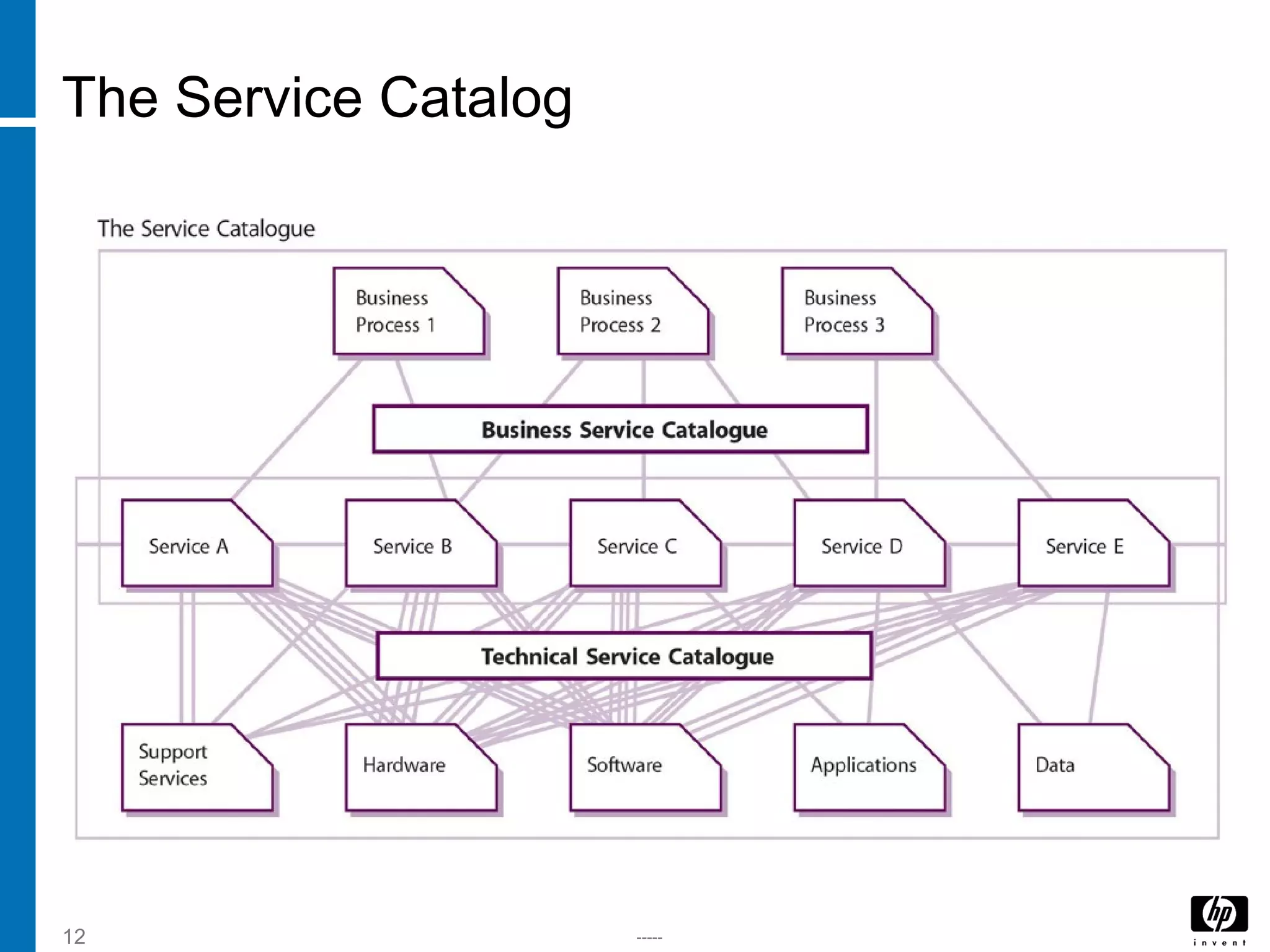
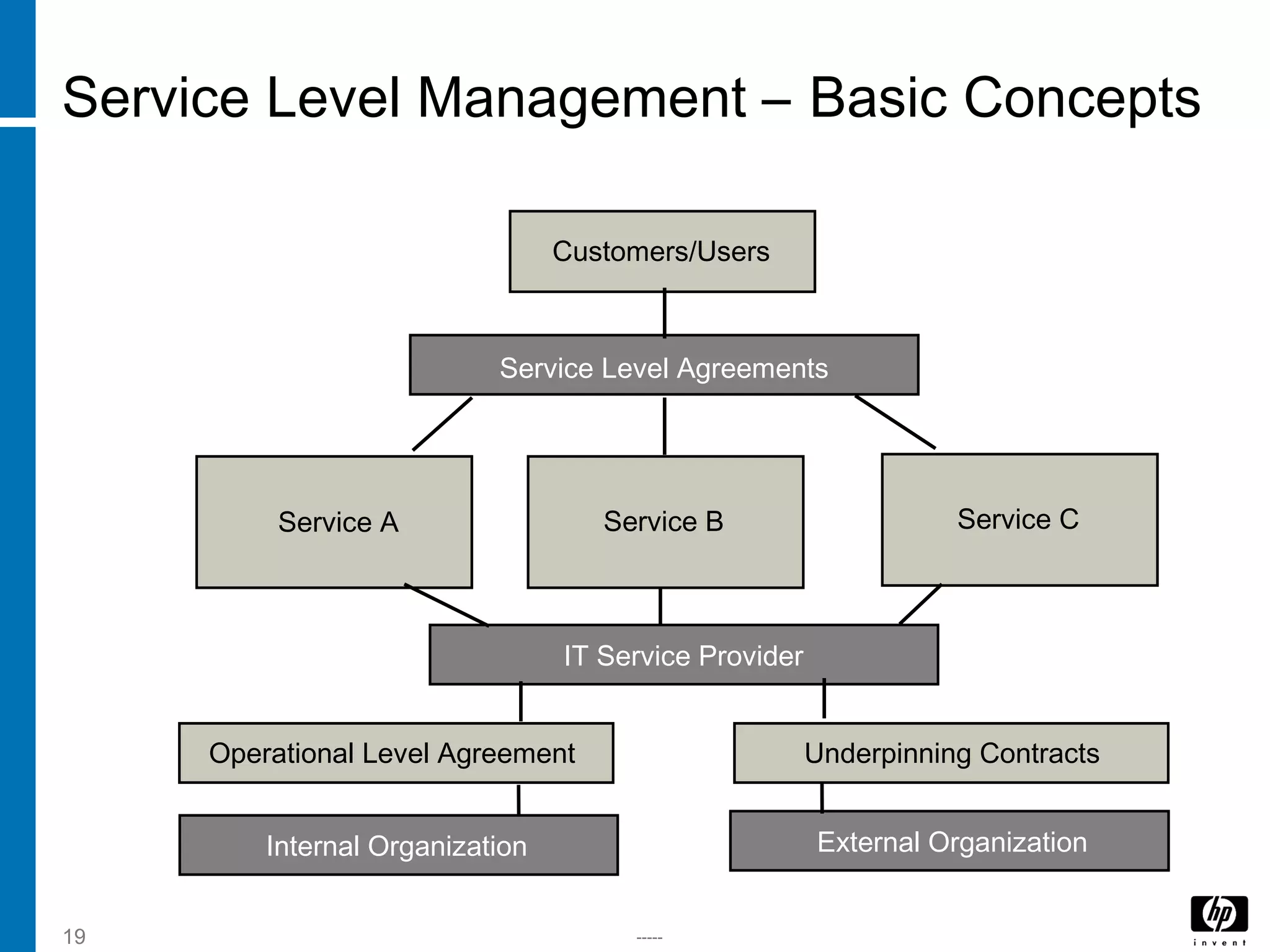
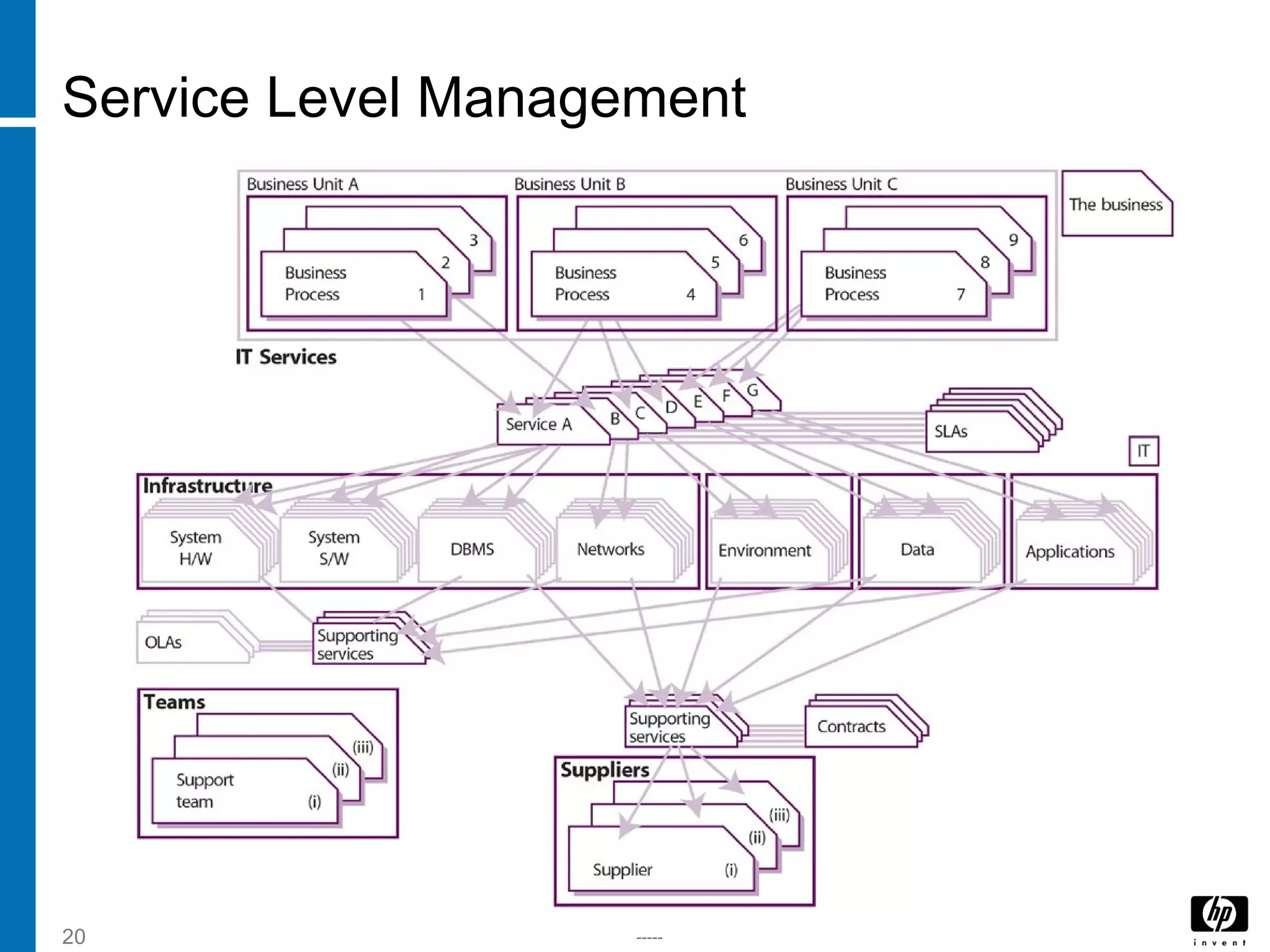
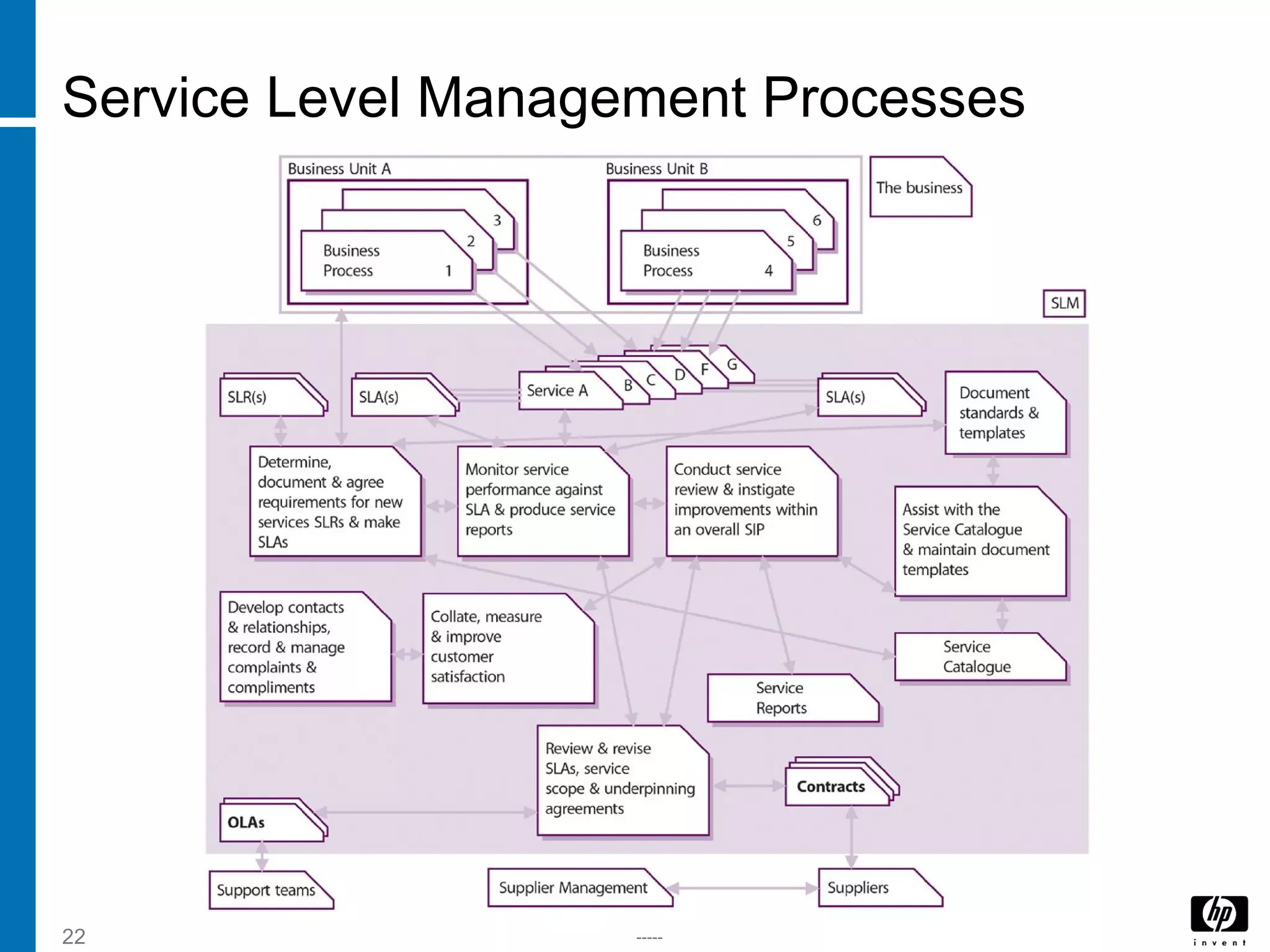
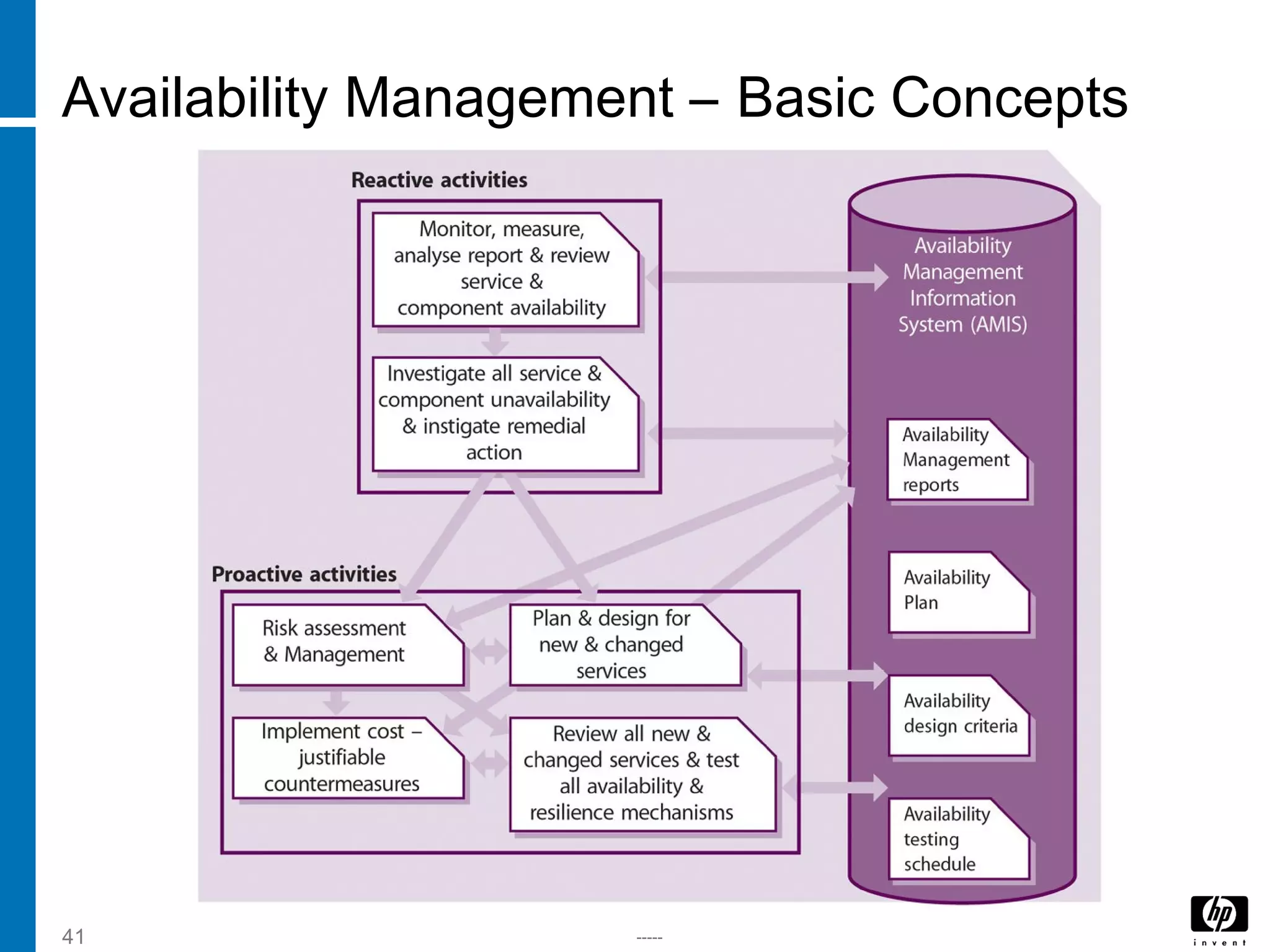
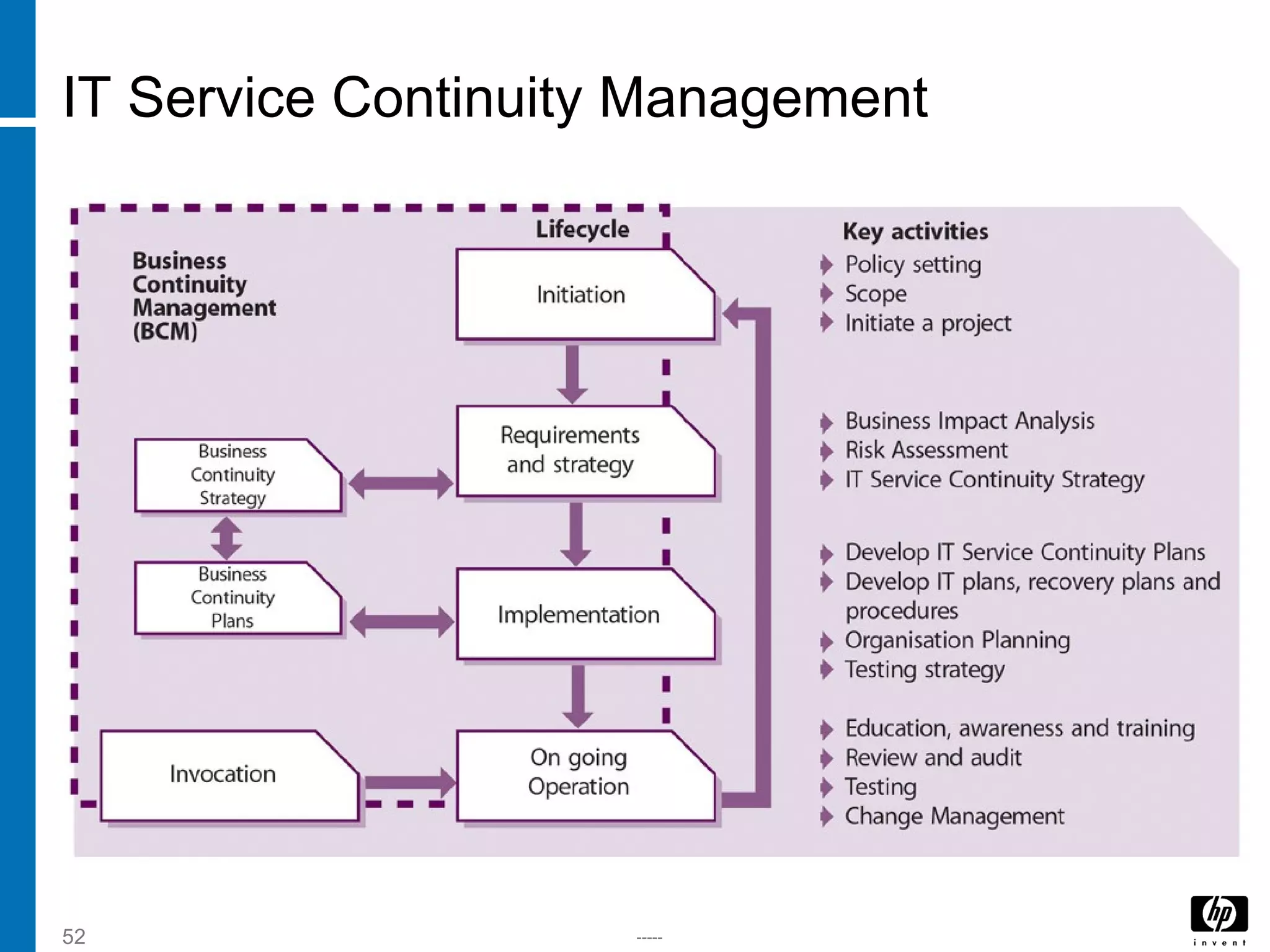
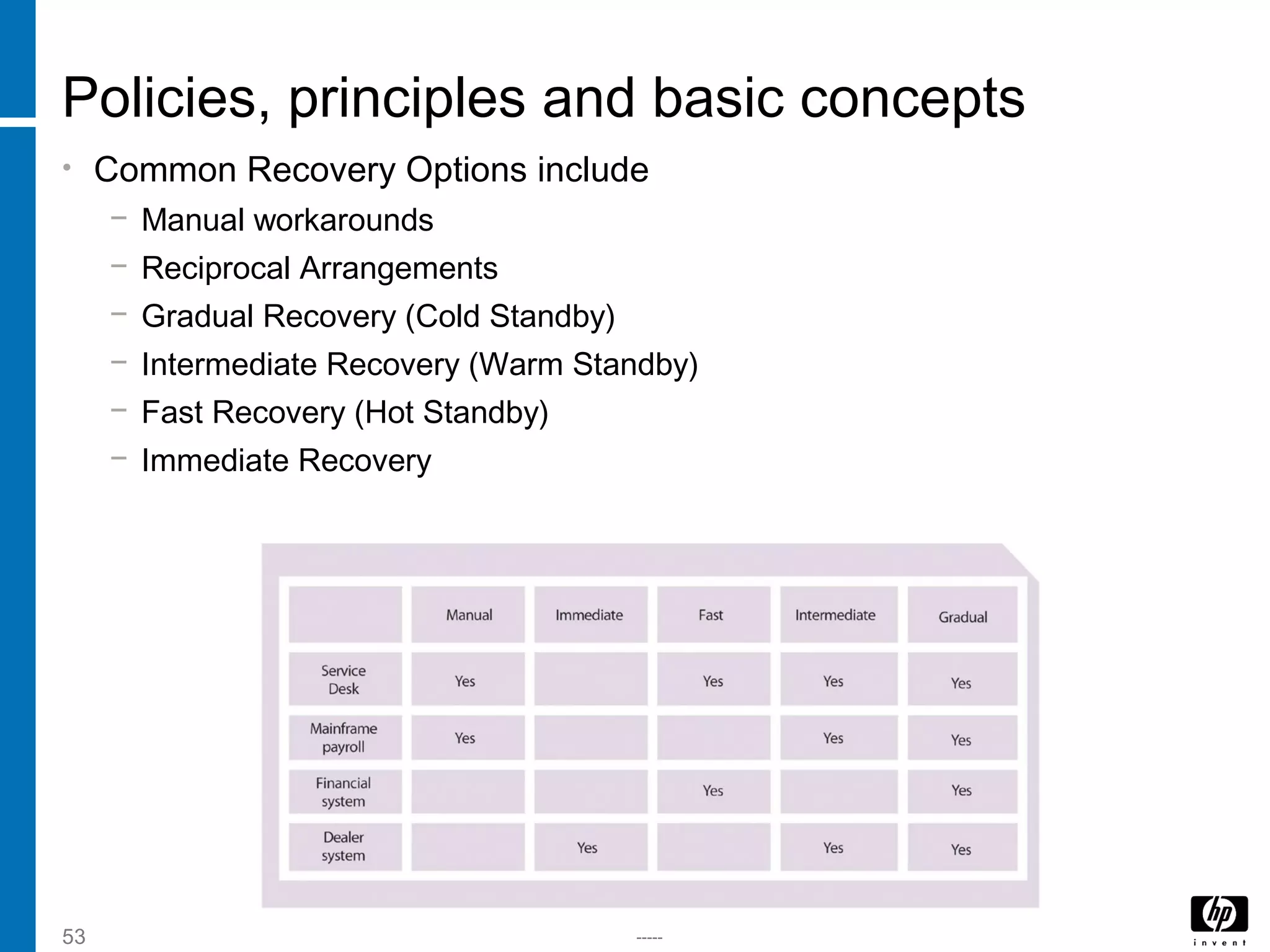
This document provides an overview of IT service design and several key IT service management processes. It discusses the purpose, objectives, scope, value and basic concepts of service design, service catalog management, service level management, capacity management, availability management, and IT service continuity management. For each process, it describes relevant activities, roles, metrics, challenges and interfaces. The document is intended to explain these important ITSM processes at a high level.