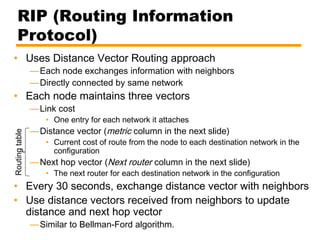
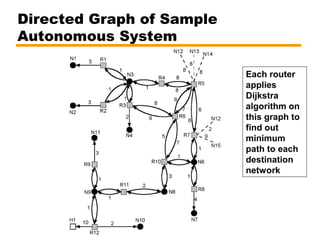
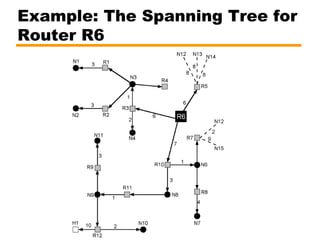
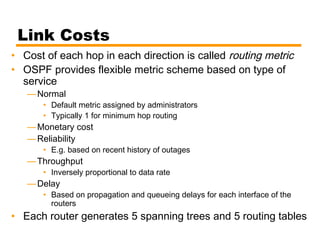
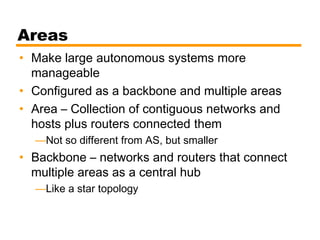
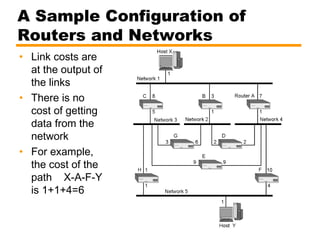
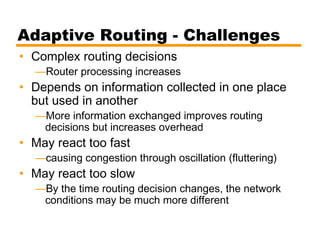
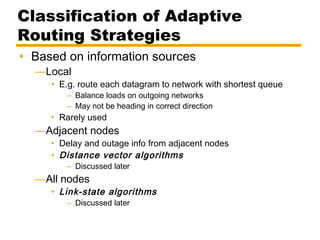
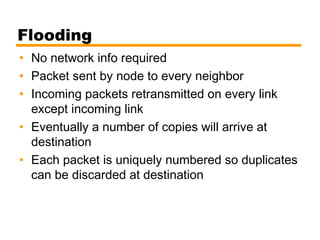
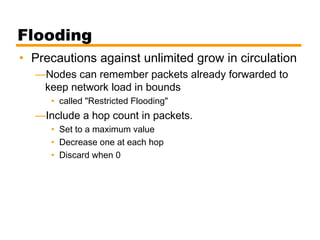
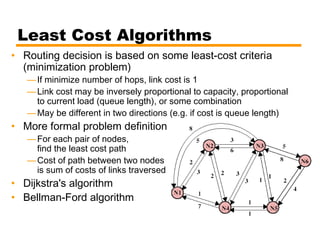
This document discusses routing in IP networks. It begins by introducing routing and routing protocols. Routers use routing protocols to decide the best path between networks based on metrics like link costs and current congestion. It then provides an example of router and network configurations with link costs. The document discusses routing tables, which contain the next hop for each destination network. It also covers different types of routing like fixed, adaptive, flooding and random routing. Adaptive routing aims to dynamically change paths in response to failures or congestion but faces challenges. The document classifies adaptive routing strategies and algorithms like distance-vector, link-state, and path-vector routing. It concludes by explaining the Dijkstra's and Bellman-Ford least cost







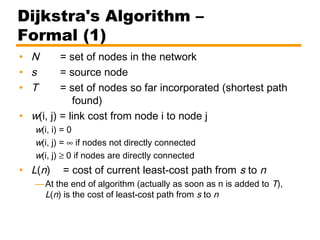
![[Initialization]
T = {s}
i.e. set of nodes so far incorporated consists of only source node
L(n) = w(s, n) for all n ≠ s
i.e. initial path costs to neighboring nodes are link costs
Dijkstra's Algorithm –
Formal (2)](https://image.slidesharecdn.com/11-routing-140526020007-phpapp01/85/11-routing-26-320.jpg)
![Repeat
[Get Next Node]
Find neighboring node not in T with least-cost path from s
Find x ∉ T such that
Add x to T. L(x) is the shortest path from s to x.
[Update Least-Cost Paths]
L(n) = min[L(n), L(x) + w(x, n)] for all n ∉ T
If the latter term is the minimum, the path from s to n is now
the path from s to x concatenated with the edge from x to n.
Until all nodes are in T
Dijkstra's Algorithm –
Formal (3)
Lx( )=
min
j∉T
L j()](https://image.slidesharecdn.com/11-routing-140526020007-phpapp01/85/11-routing-27-320.jpg)
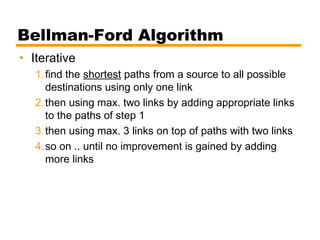
![Bellman-Ford Algorithm –
Formal (2)
[Initialization]
L0(n) = ∞, for all n ≠ s
h=0](https://image.slidesharecdn.com/11-routing-140526020007-phpapp01/85/11-routing-31-320.jpg)
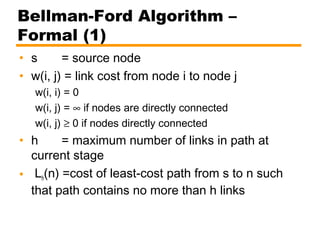
![Bellman-Ford Algorithm –
Formal (3)
[Update]
Loop until no more improvements
For each n ≠ s, compute
If s-to-n cost reduced, then path also
changes to s -…- j - n
h=h+1
Lh+1 n( )=
min
j
Lh j( )+ w j, n( )[ ]](https://image.slidesharecdn.com/11-routing-140526020007-phpapp01/85/11-routing-32-320.jpg)