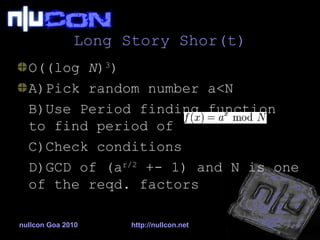
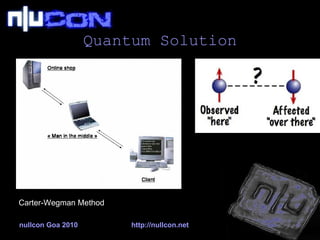
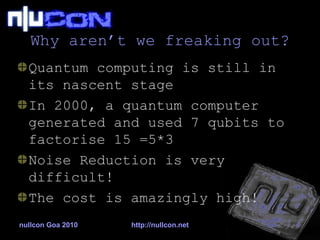
The document discusses the challenges of security in quantum computing, highlighting how current encryption algorithms like RSA may be compromised by advancements in quantum factoring through Shor’s theorem. It mentions the McEliece encryption system as a proposed solution, although it has already faced vulnerabilities. The author emphasizes the need for a shift from mathematical to physical approaches in developing the next generation of cryptography.