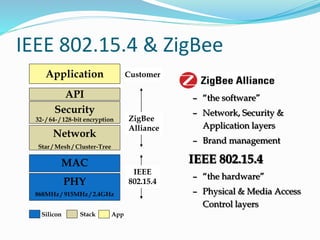
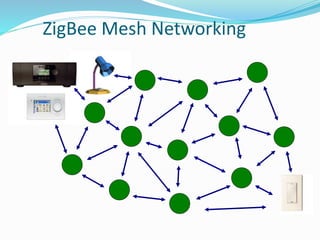
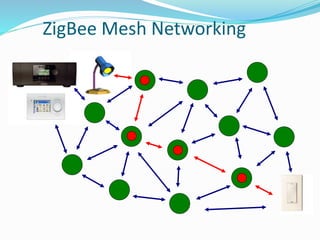
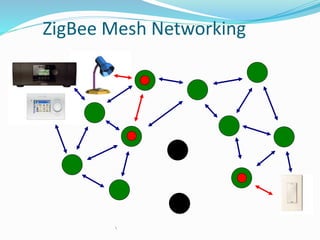
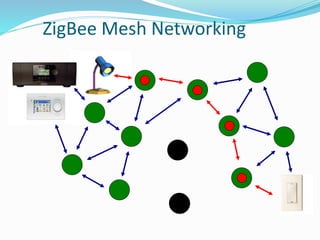
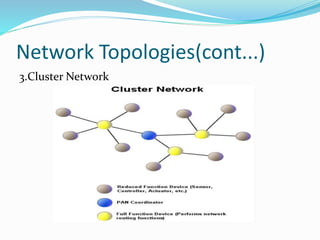
Zigbee is a wireless technology designed for control and sensor networks, based on the IEEE 802.15.4 standard, and developed by the Zigbee Alliance. It enables low power consumption, allowing devices to last for extended periods, and supports networked homes where all devices communicate and are controlled from a single unit. Zigbee's architecture includes different device types, network topologies, and features aimed at providing security and ease of implementation in applications across various markets.