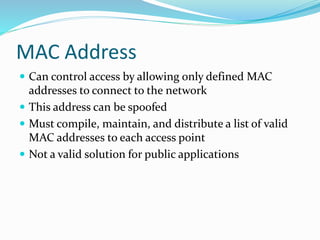
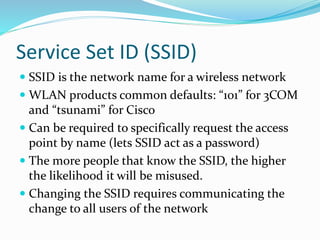
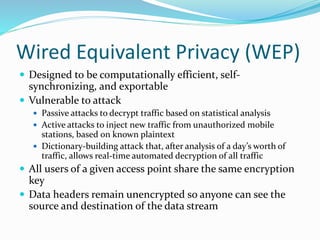
This document discusses wireless network security. It outlines uses and benefits of wireless networks, but also security issues like war driving and rogue networks. It evaluates potential security solutions like MAC address filtering, changing the SSID, and WEP encryption. However, it concludes that while wireless networks are convenient, current security measures are insufficient for sensitive environments given vulnerabilities like WEP attacks and the sharing of encryption keys across networks. Improved security is needed as wireless adoption increases.