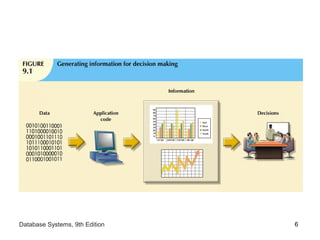
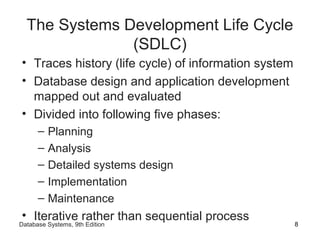
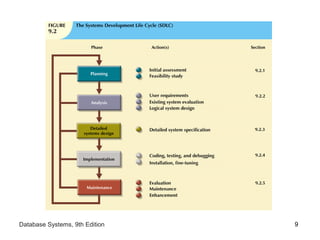
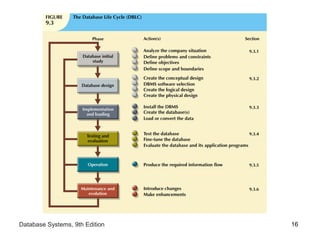
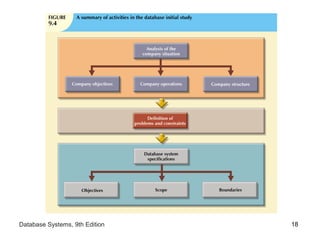
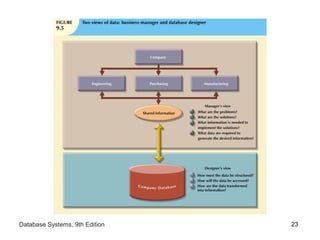
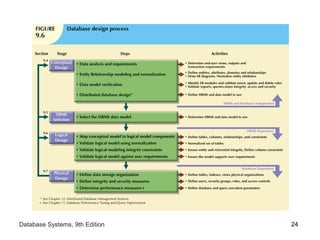
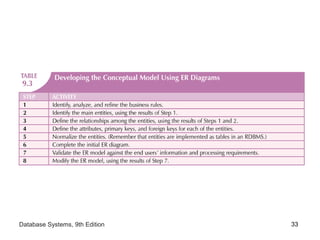
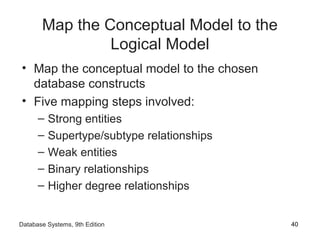
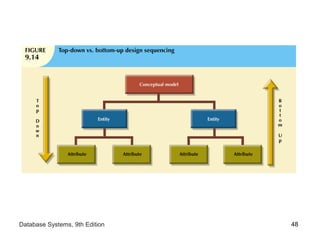
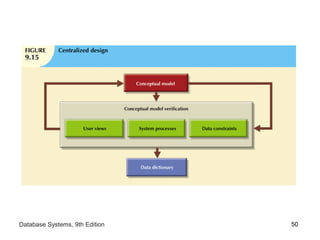
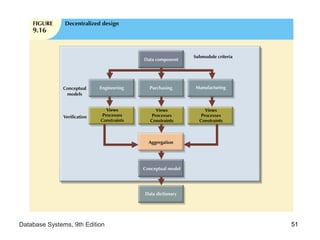
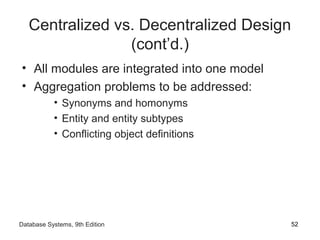
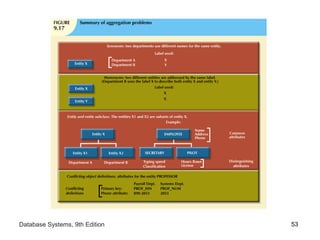
The document discusses database design within the context of information systems and their life cycles. It describes the systems development life cycle (SDLC) and database life cycle (DBLC) as frameworks for developing and maintaining databases and applications. The database design process involves conceptual, logical, and physical design stages to model data and map the design to a target database management system. Centralized and decentralized approaches as well as top-down and bottom-up strategies are discussed for database design.