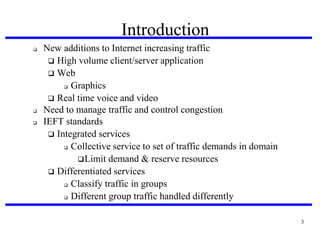
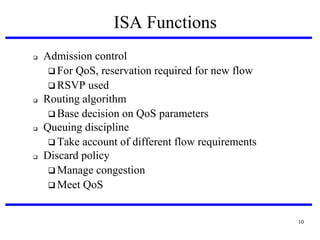
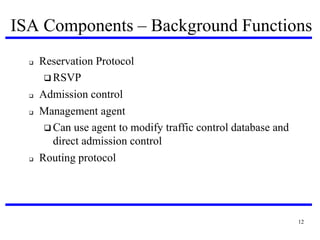
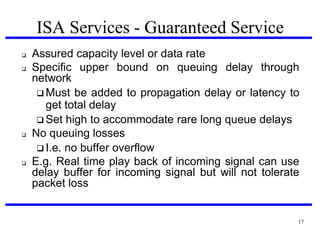
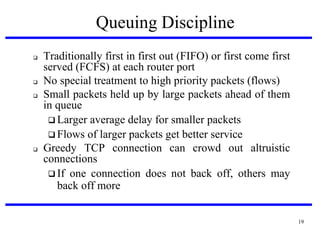
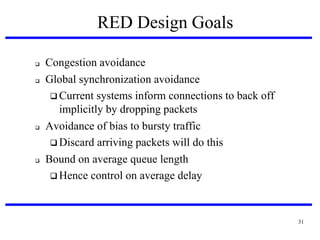
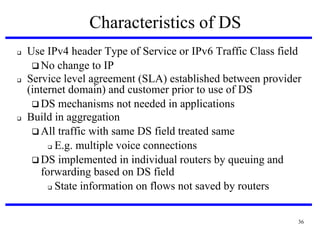
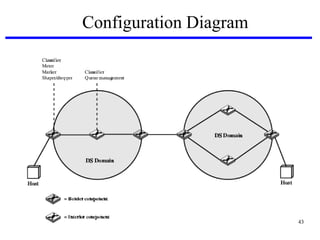
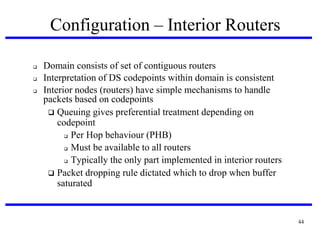
This document discusses integrated services architecture (ISA) and differentiated services (DS) for providing quality of service (QoS) in computer networks. It describes the components and functions of ISA, including reservation protocol, admission control, routing, queuing disciplines, and services. It also covers traffic classification, scheduling, and dropping policies implemented in routers. Random early detection (RED) is presented as a proactive packet discard mechanism for congestion management. Differentiated services is introduced as a simpler alternative to ISA that uses traffic classes in packet headers to provide different performance levels.