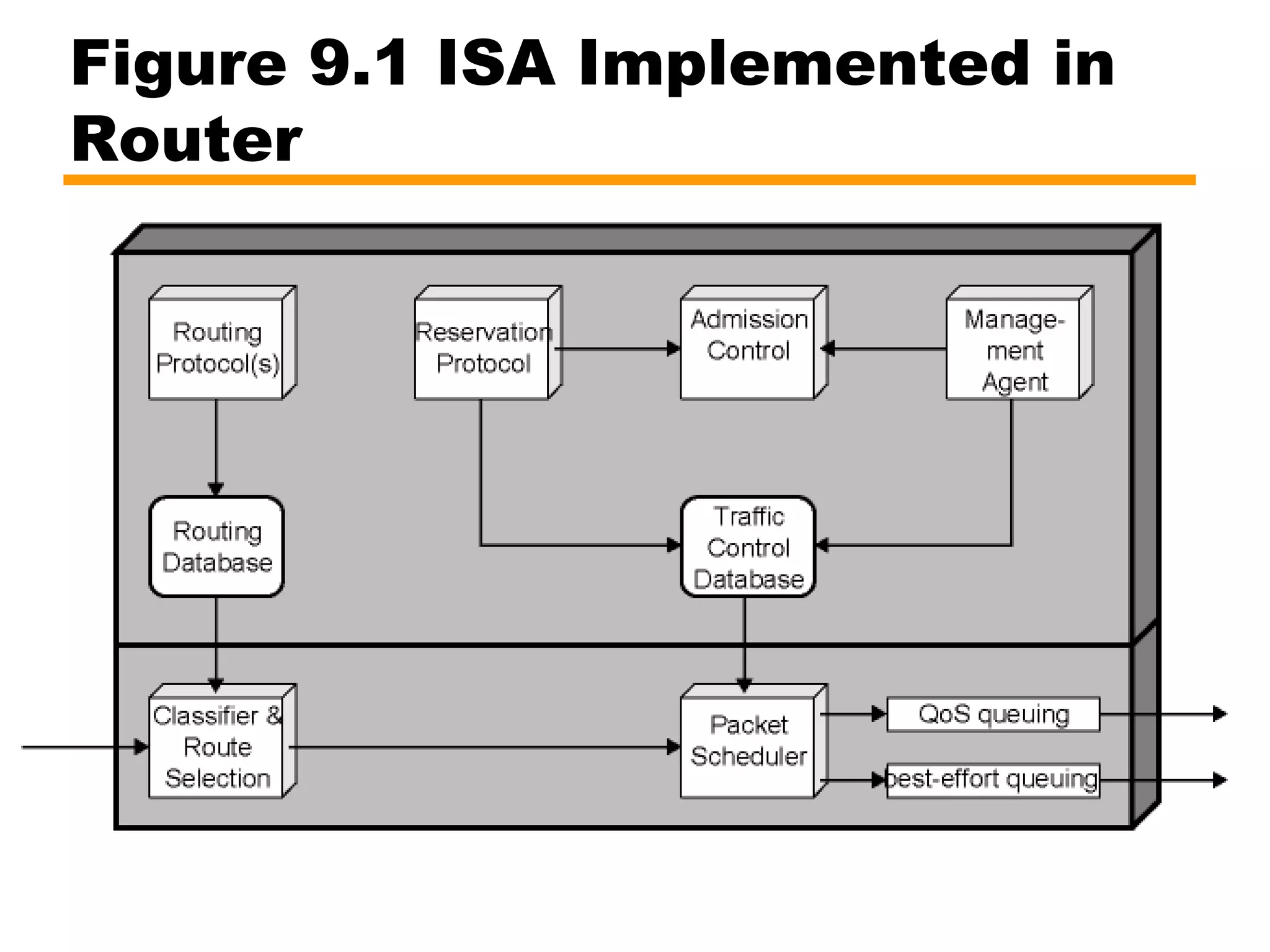
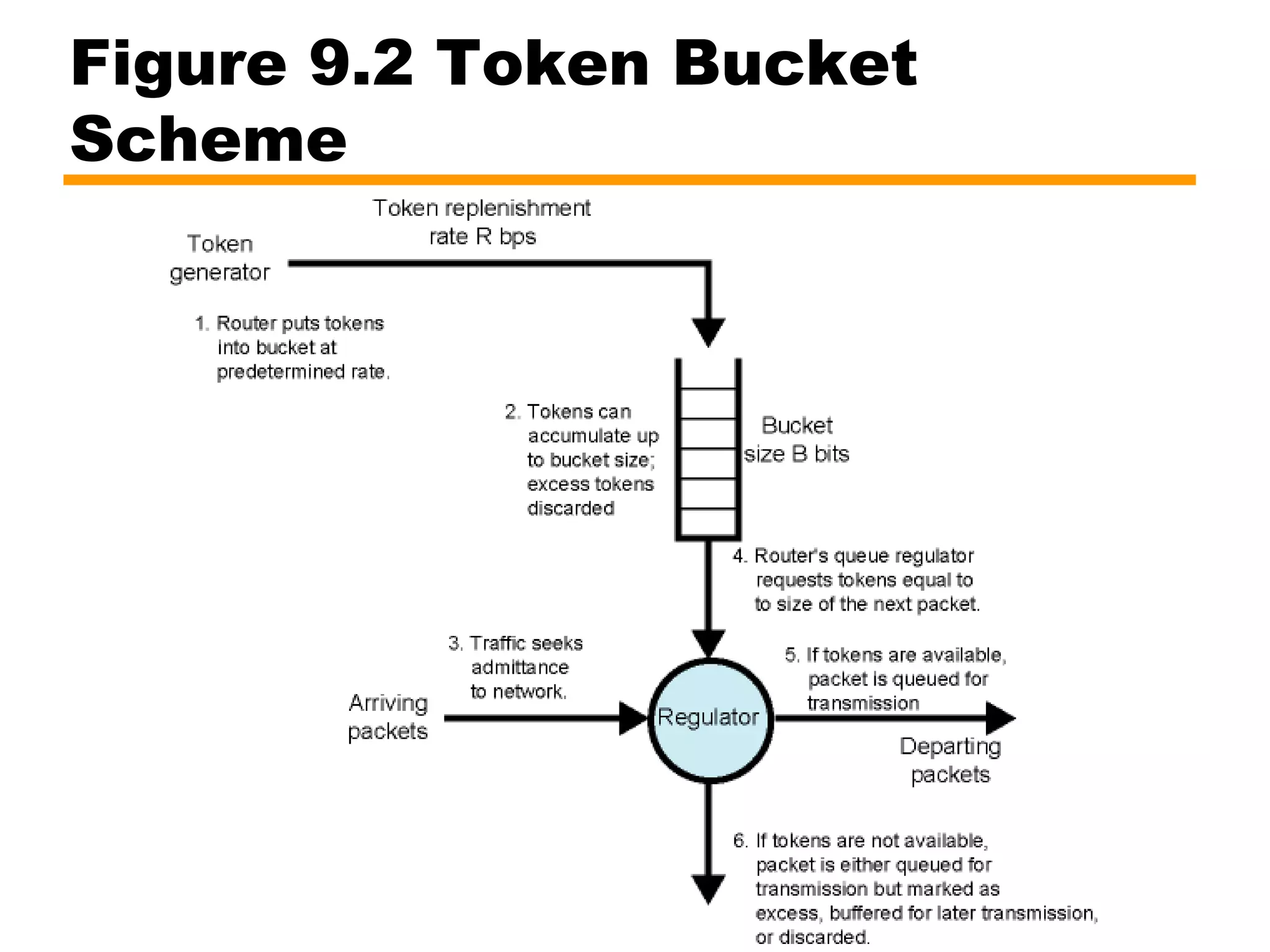
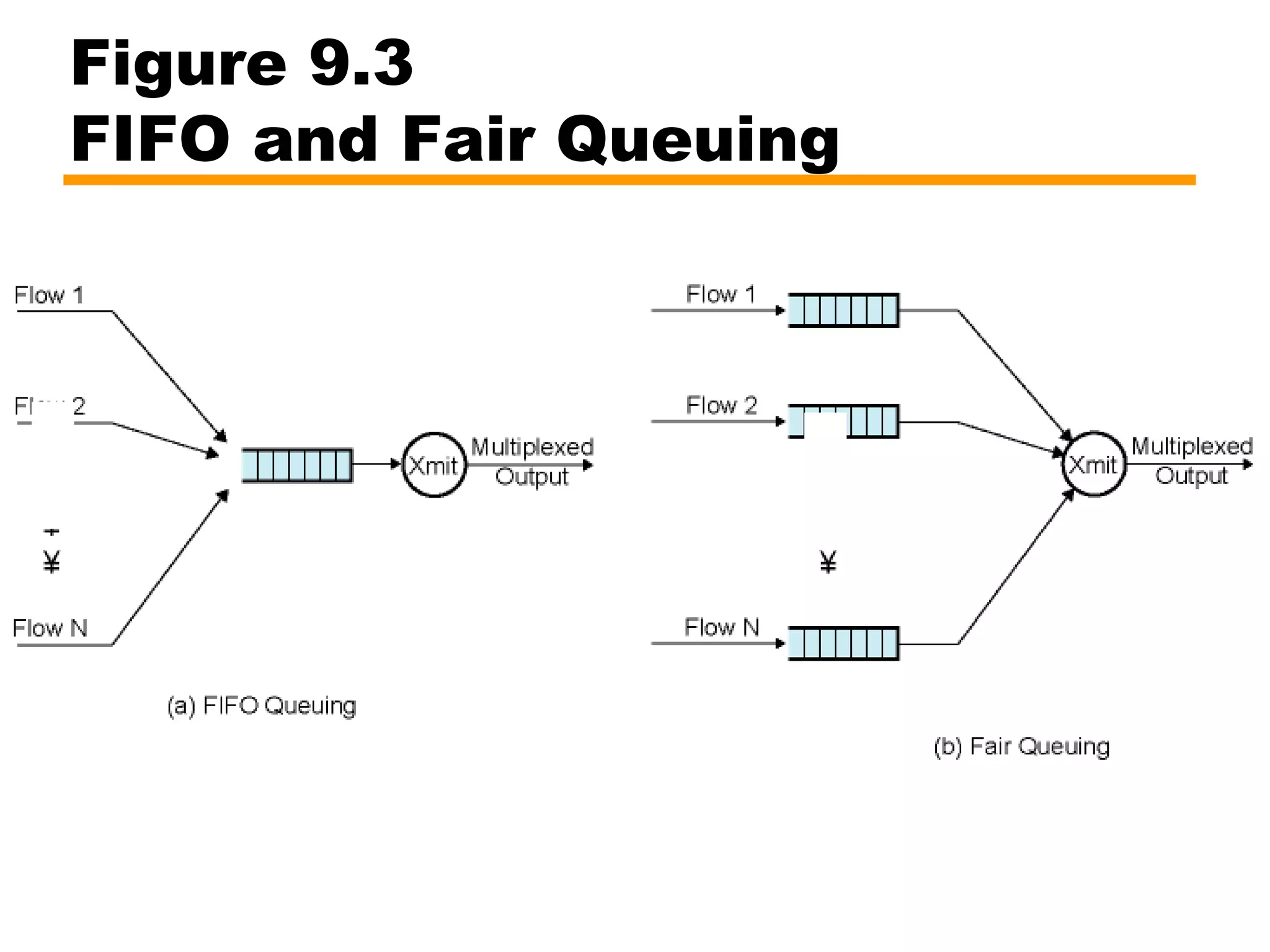
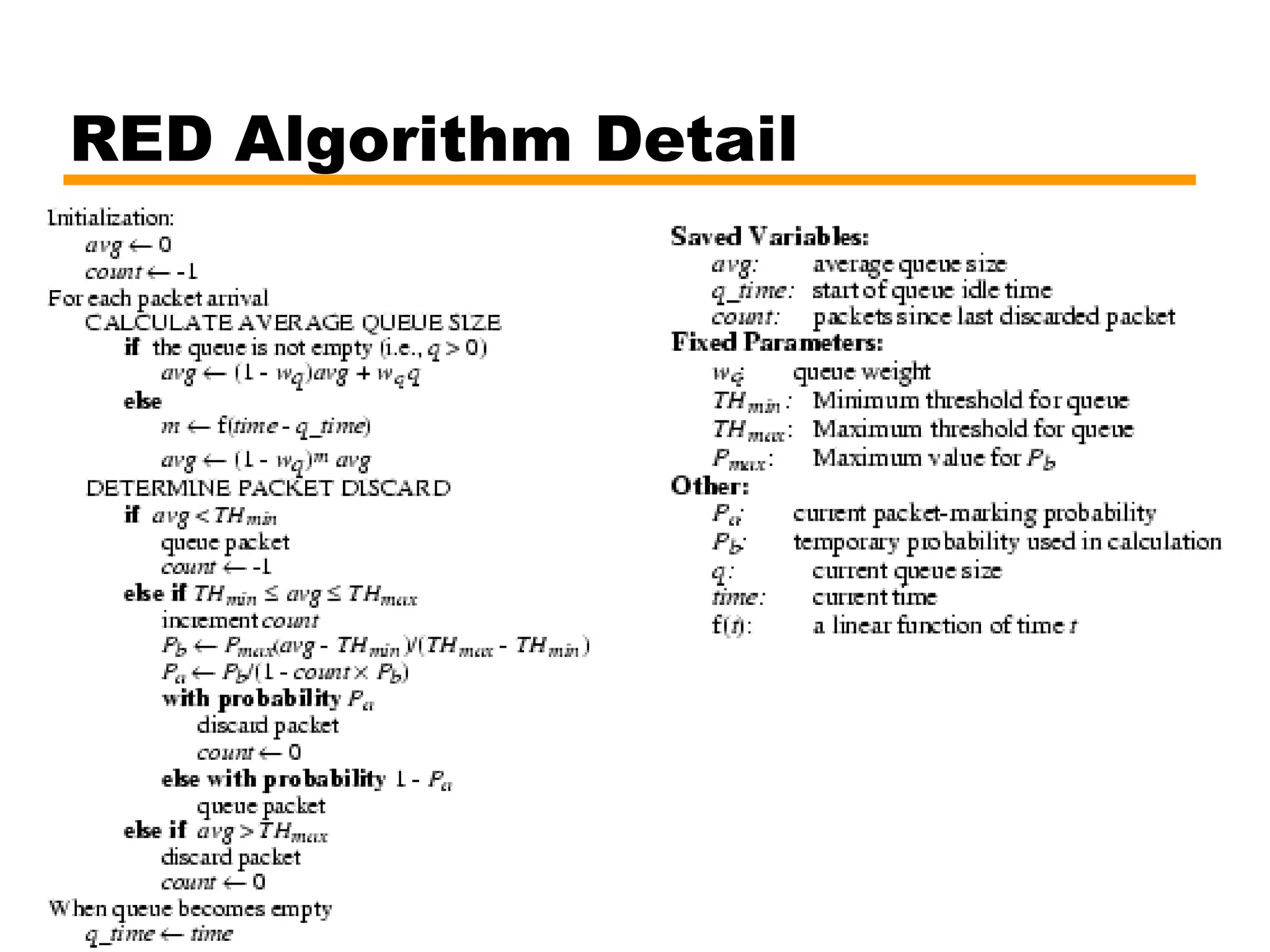
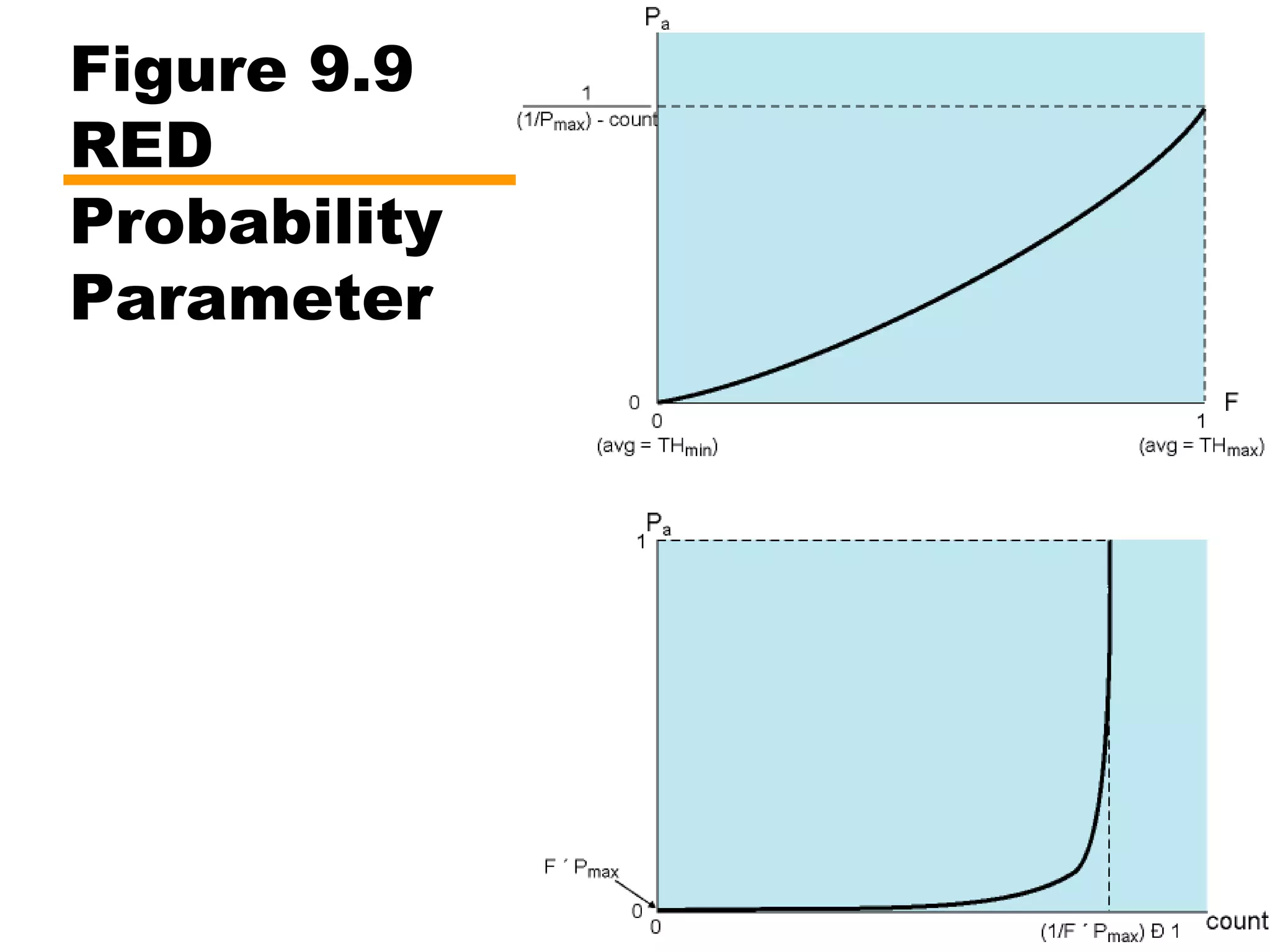
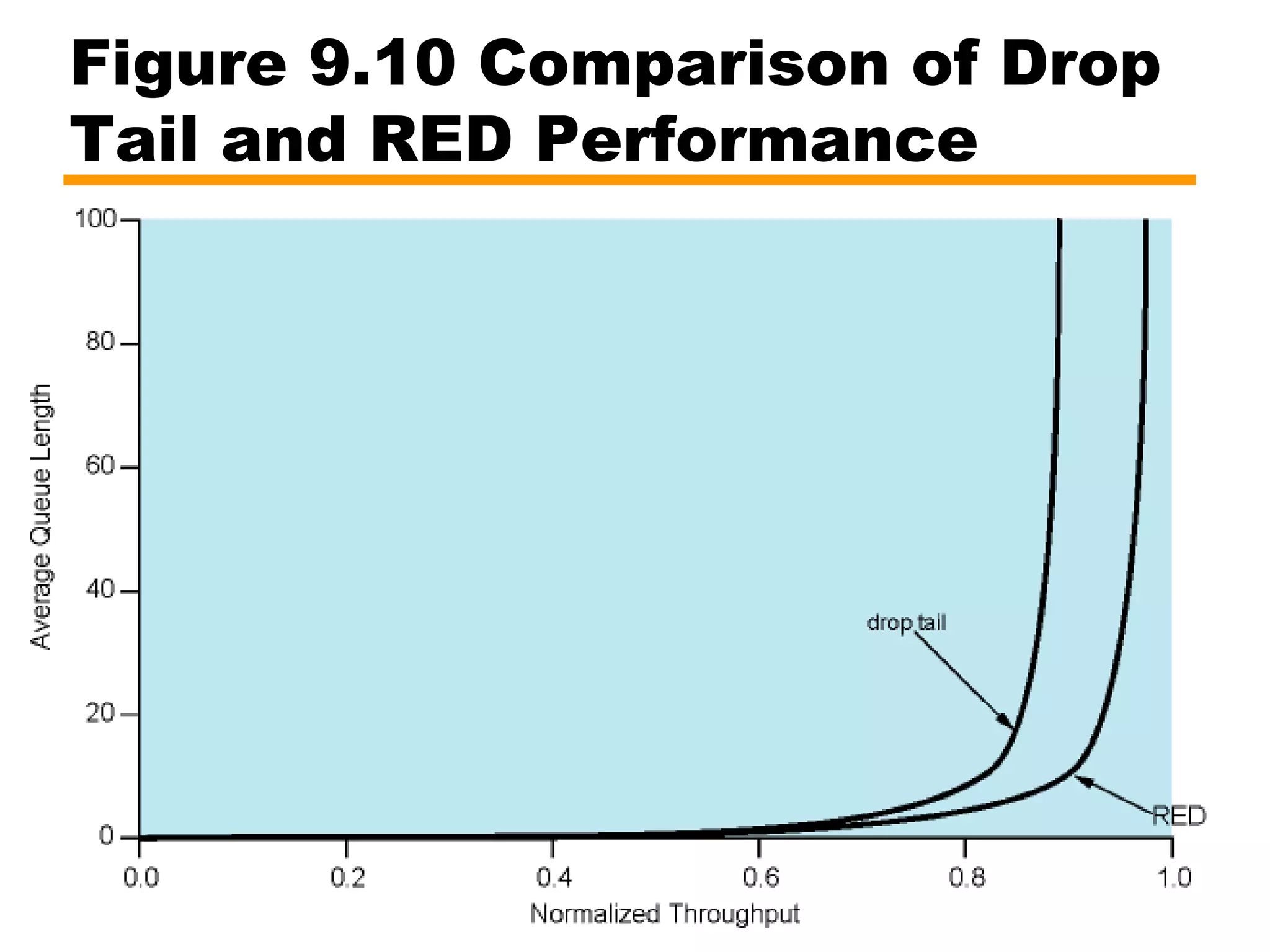
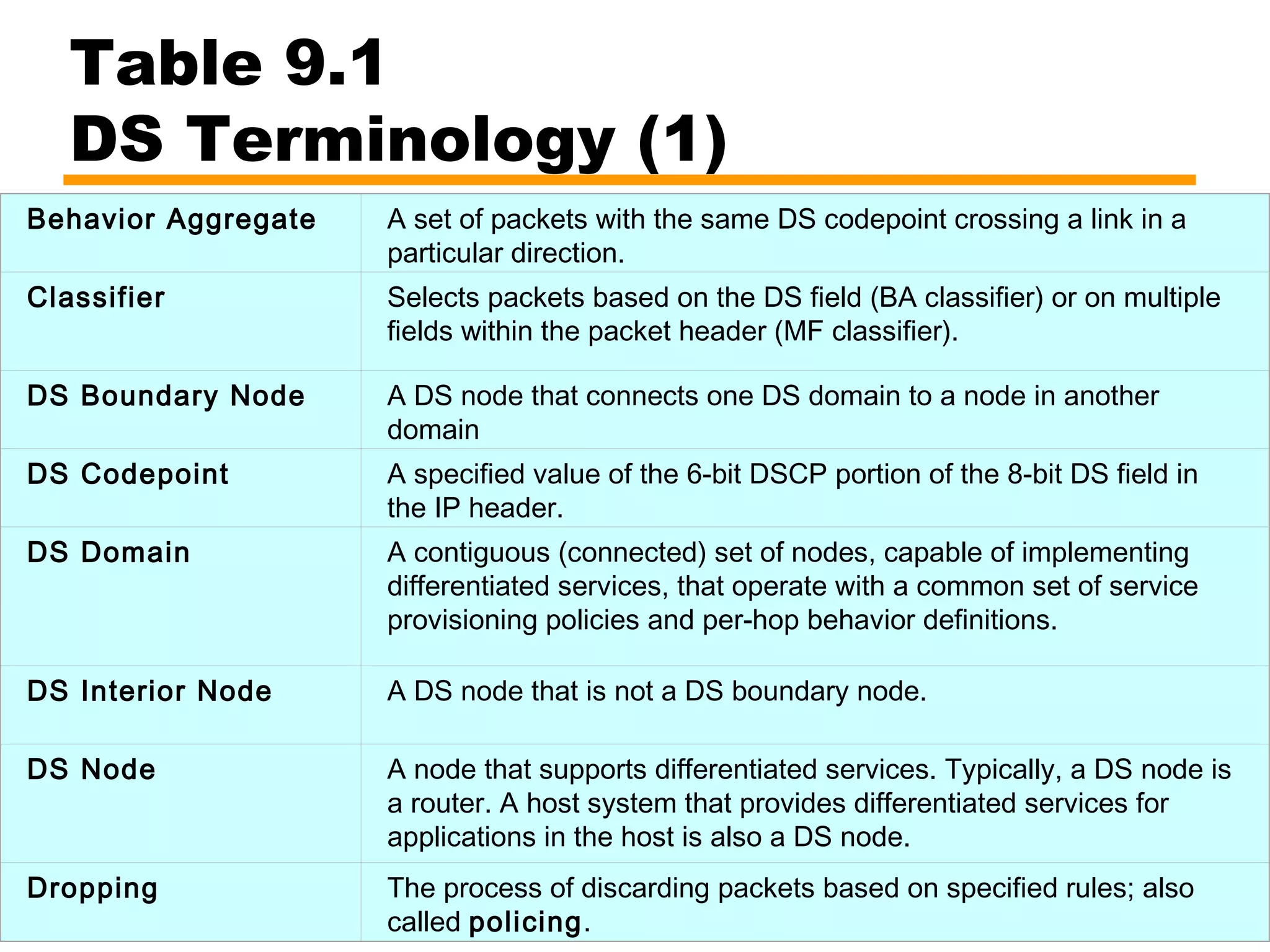
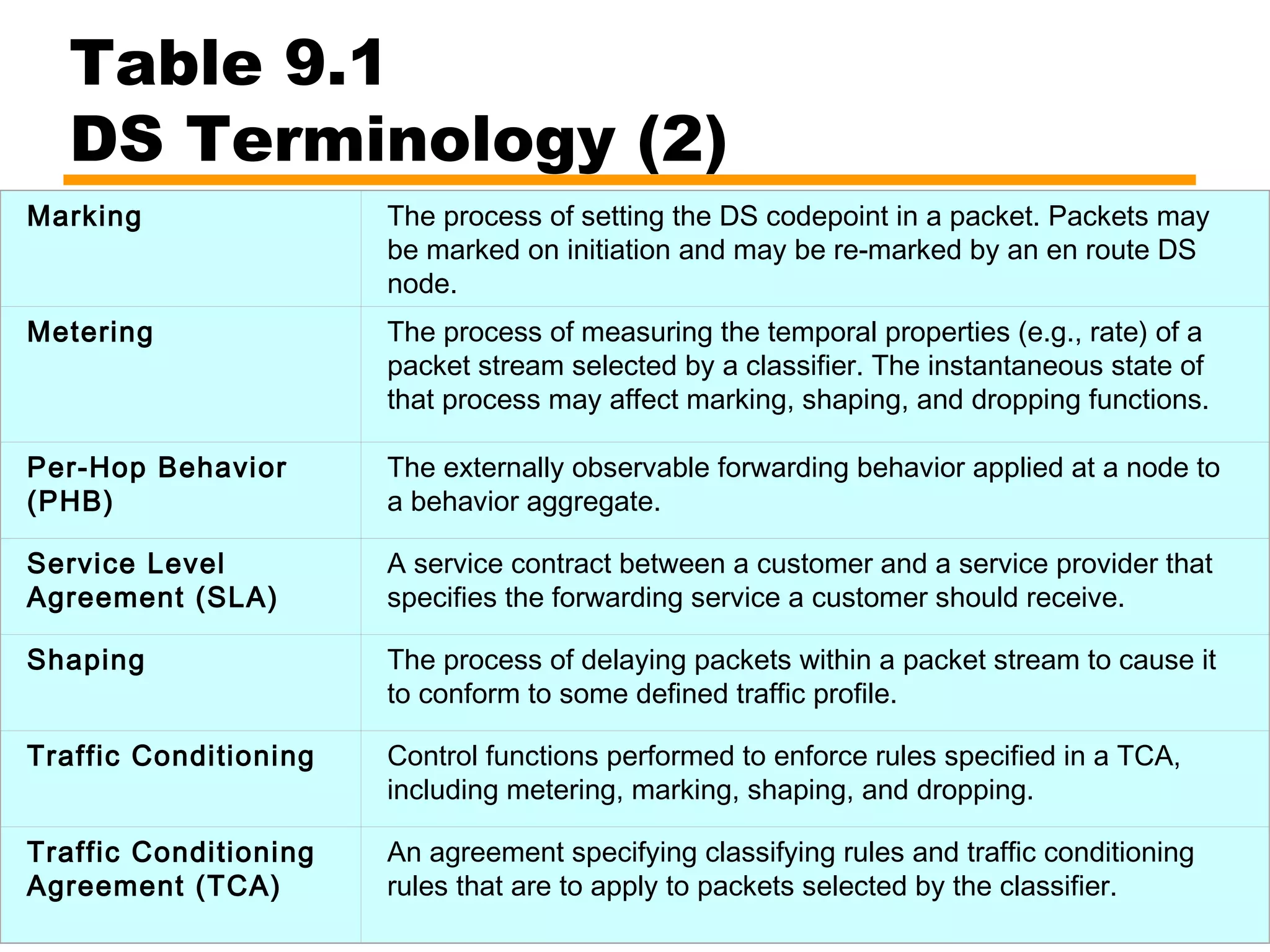
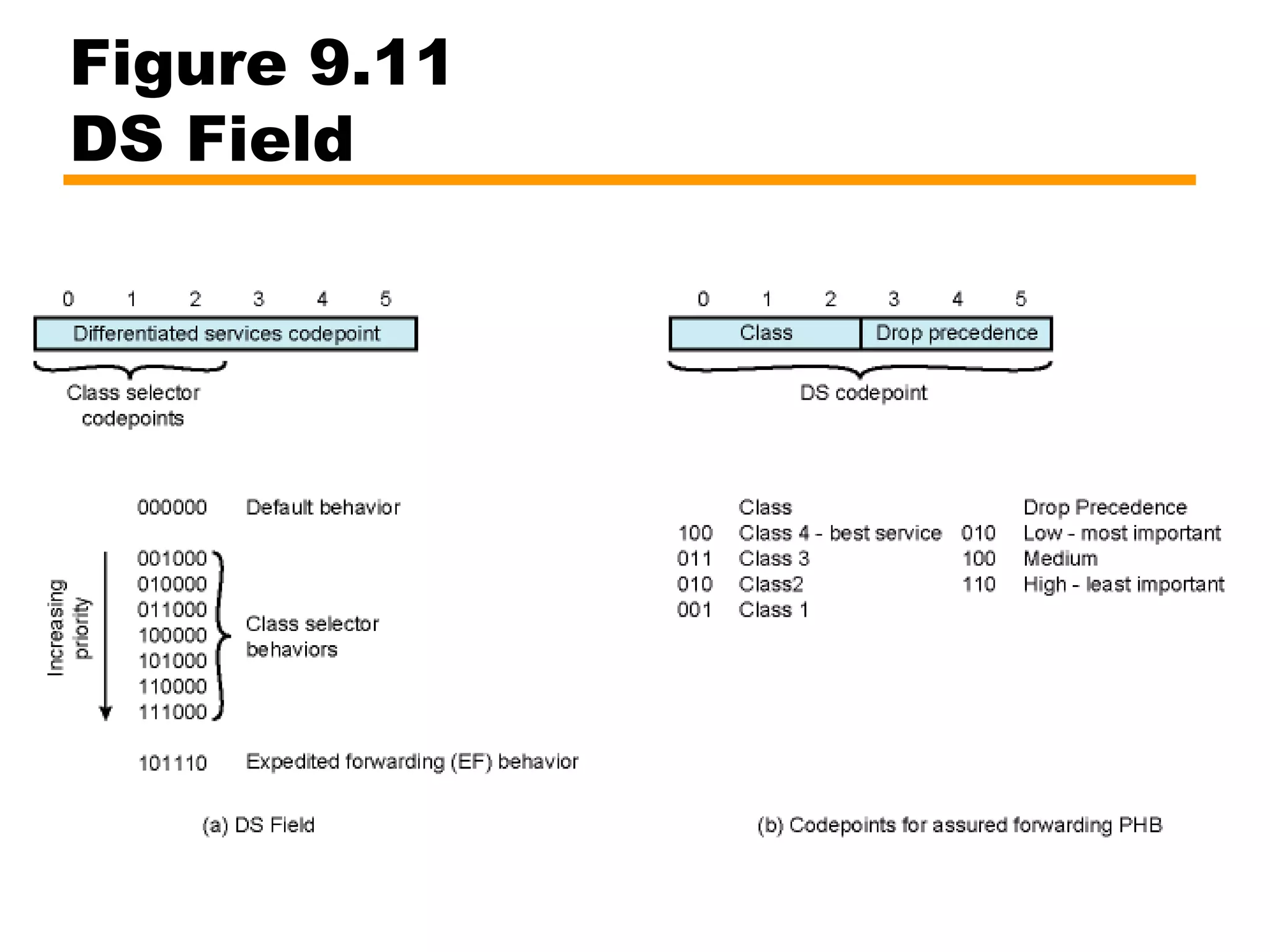
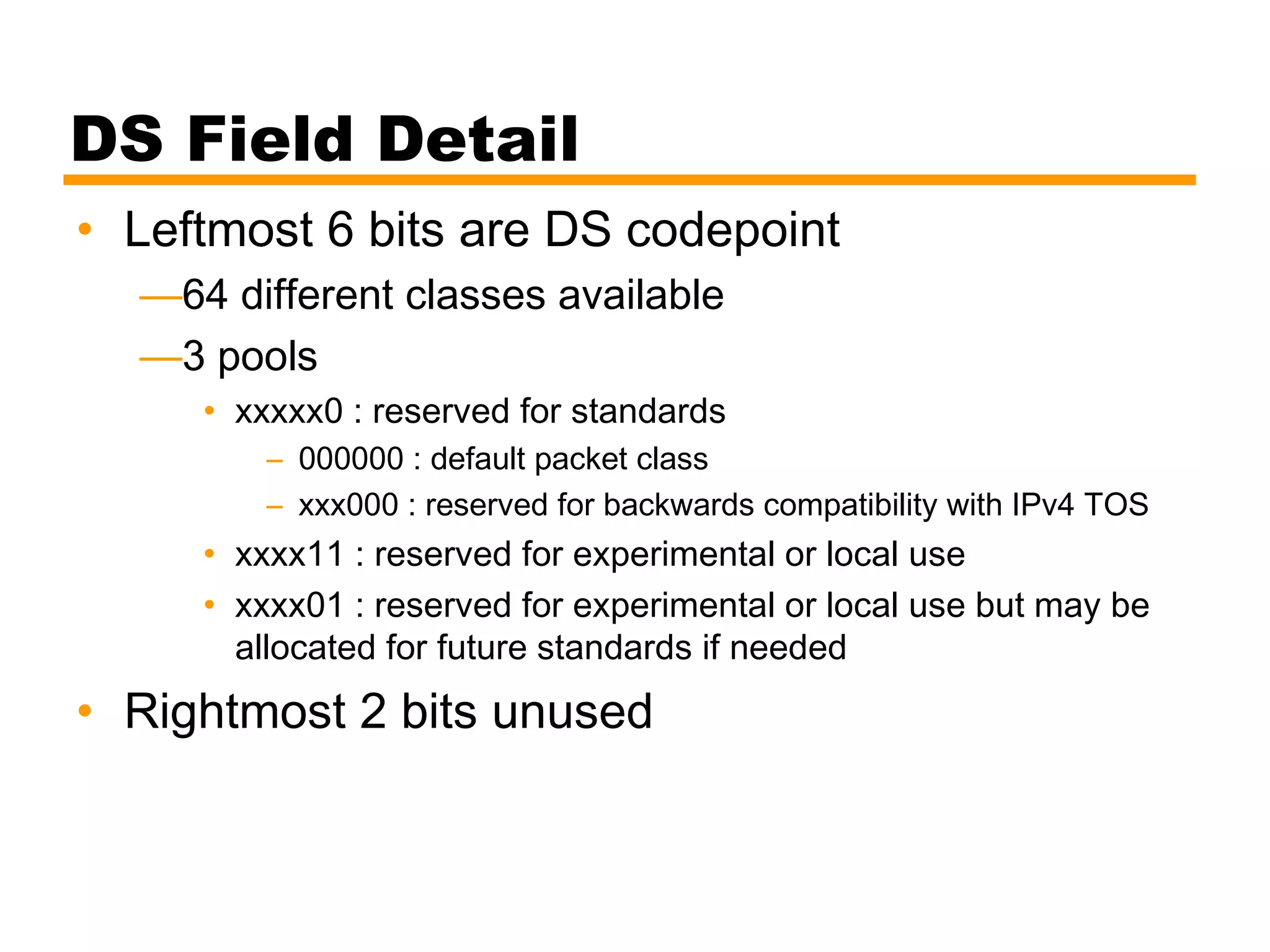
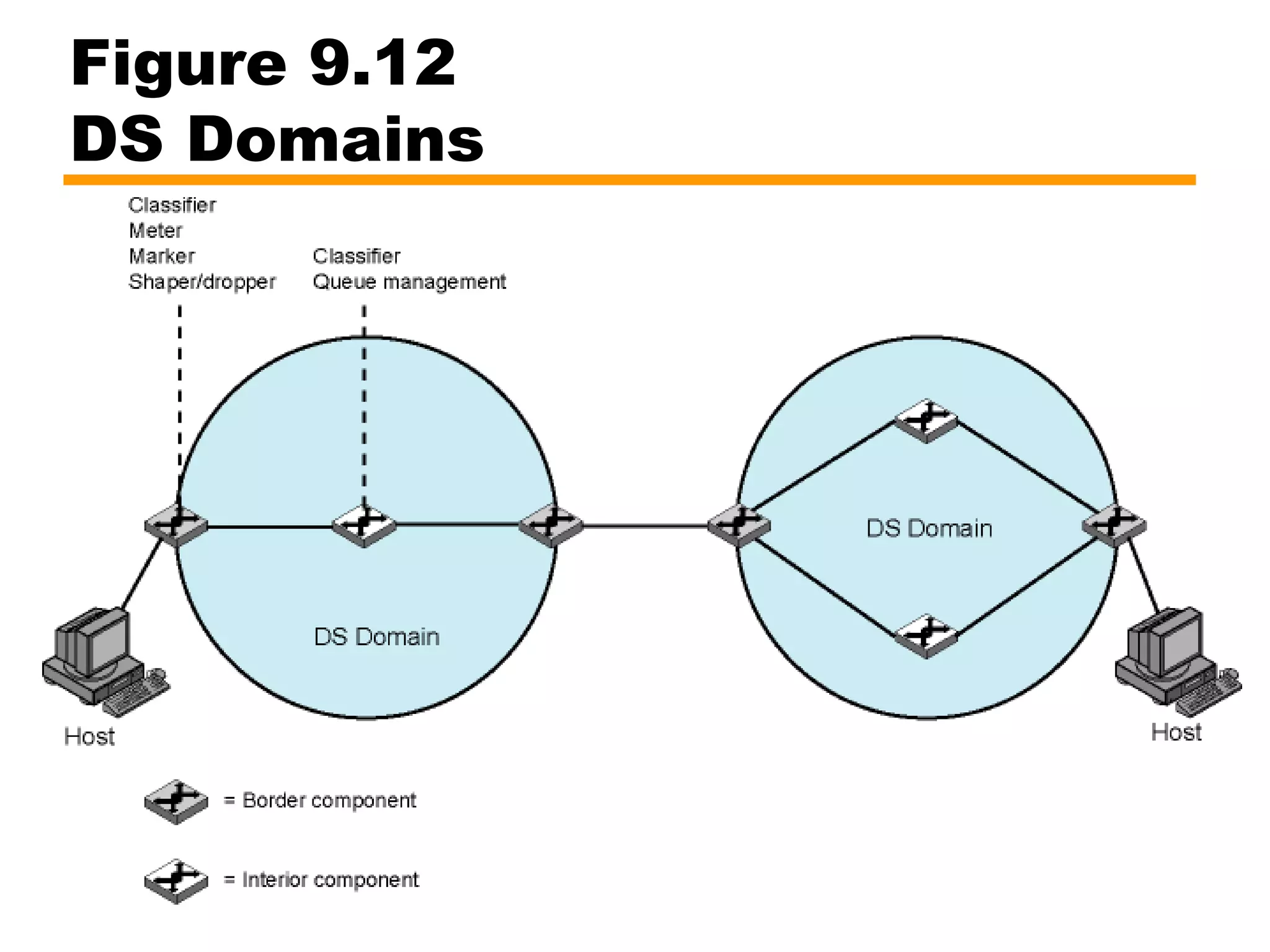
This document discusses integrated services and differentiated services for providing quality of service (QoS) on the internet. Integrated services uses resource reservation and traffic classification to provide guaranteed, controlled load, and best effort services. It requires per-flow state maintenance in routers. Differentiated services provides a simpler approach using traffic conditioning and per-hop behavior based on DS codepoints, without per-flow state. It aggregates traffic into behavior aggregates for forwarding.